

Guide for Configuring PowerStore with an SSL Certificate
Tue, 30 Aug 2022 14:11:47 -0000
|Read Time: 0 minutes
SSL certificates are commonly used when browsing the internet. Even corporate intranet pages are usually protected with an encrypted SSL connection. The two major security improvements when using SSL certificates are:
- Authenticity to prove a trusted server
- Encryption to protect (sensitive) data
Let’s start with some quick basics. I guess everyone has seen the nice error message about expired or invalid certificates in a browser. Some browsers even don’t allow you to continue when hitting a page with an expired certificate.
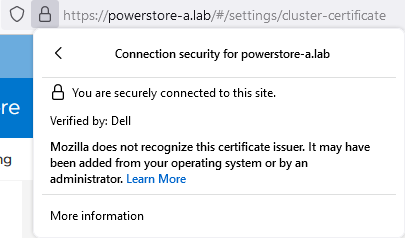
When Dell PowerStore is installed, it internally generates a self-signed certificate to allow data encryption between browser and PowerStore. Because the signed certificate is not trusted by the browser, a warning indicates that the page is not trusted. To mitigate the warning, PowerStoreOS allows the administrator to change the out-of-the box self-signed certificate with a trusted SSL certificate, ideally signed by a trusted certification authority (CA).
Besides the major commercial and public CAs, some companies run their own company-wide certificate authority. A private CA is usually part of a Private Key Infrastructure (PKI) and can provide certificates for different purposes. To allow the browser to validate certificates, the certificate of the private CA needs to be installed as a trusted Certificate Authority in the browser.
A certificate always consists of at least two parts:
- A secret key which is used to sign other certificates or to encrypt data
- A public key which is included in a certificate
When a certificate or data is signed or encrypted with a private key, the public shared key can be used to decrypt the information. Fingerprints within the certificate file help verify whether the shared key and decrypted information can be trusted.
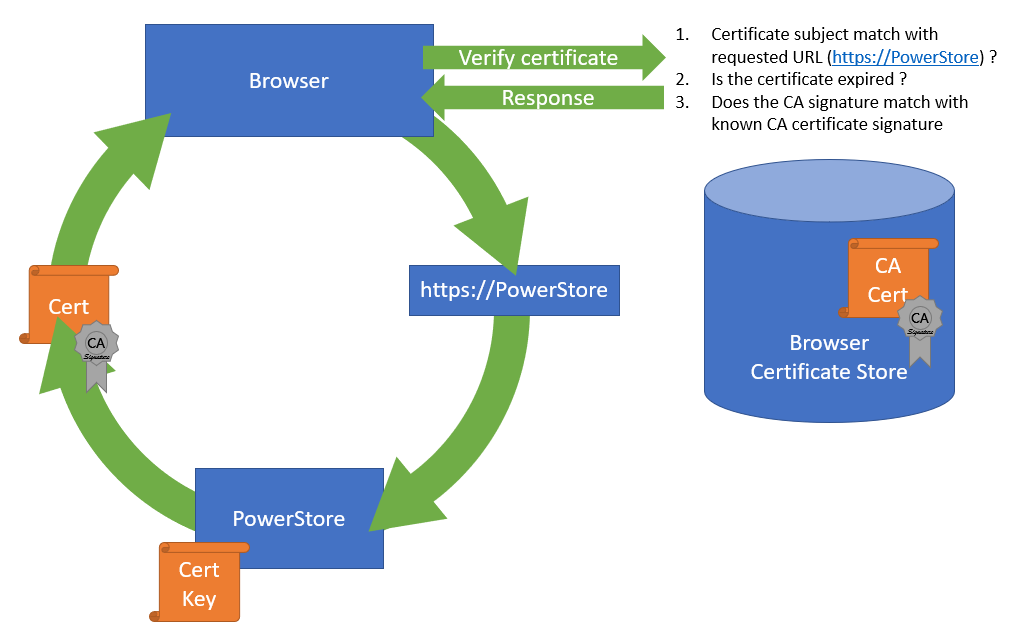
The structure of trusted certificates is always hierarchical and based on a Root CA certificate, which is at the top of the trust chain. A Root CA can have one or more Intermediate CAs, which are usually used to sign a server certificate by a certificate authority. In the same way when a client requests data from an SSL protected site, the server uses the certificate key to sign and encrypt the data and sends the response with the public certificate to the client. The client uses the response to check and validate the certificate attributes. These important attributes are the “valid from” and “valid to” timestamps, whether the URL matches the subject of the certificate, and whether the certificate is signed by a trusted CA certificate in the client certificate store. The check against a trusted CA certificate proves the authenticity. When all checks are passed, the browser indicates that the page can be trusted.
SSL certificates involve some different files:
Certificate | Description |
Certificate “key” file | Contains the key to encrypt and sign data. The key file should be kept safe. |
Certificate Sign Request (CSR) | The certificate sign request is generated with information from the key file and contains the information for a CA to issue a certificate file. Included information for a CSR generated with PowerStore: Subject: Concatenated string containing Organization, Organizational Unit, Location, State, and Common Name as given in PowerStore Manager when creating the CSR. SAN: A X509v2 extension called “Subject Alternate Names” which is the DNS and IP information as entered Public-Key: The public part of the private key file |
Certificate file | This could be either a single certificate or a certificate chain. A certificate chain is a set of concatenated certificates that allows clients to validate a certificate down to a trusted (CA) certificate. There are different file formats possible: PEM: “Privacy-Enhanced Mail” is commonly used to exchange certificates DER: “Distinguished Encoding Rules” is a binary encoding for PEM files PFX/PKCS: Another type called personal information exchange format When dealing with SSL certificates for Dell PowerStore, the PEM format is used. |
CA Certificate / | This is the public certificate of the issuer CA of a certificate. A PowerStore does not know anything of the issuer and needs the CA certificate to build the whole chain of trust for the certificate. Sometimes the file includes the whole certificate chain that consists of concatenated PEM certificates CA -> [Intermediate CA] -> PowerStore The included certificates in a chain depend on the issuer of a certificate. For PowerStore, we require the chain of certificates in following order:
|
Since PowerStoreOS 2.0, it’s possible to install 3rd party / signed server certificates for PowerStore T models in a block only deployment using PowerStore REST API or PowerStore CLI. PowerStoreOS 3.0 adds support for PowerStore T unified deployments and a GUI in PowerStore Manager for SSL import. This provides a comfortable way to generate a certificate sign request (CSR) and install the certificate. The certificate key file is stored in PowerStore and cannot be exported.
The next sections describe how to use PowerStore Manager and the PowerStore CLI to install a third party SSL certificate.
Installing a third party SSL certificate (PowerStore Manager)
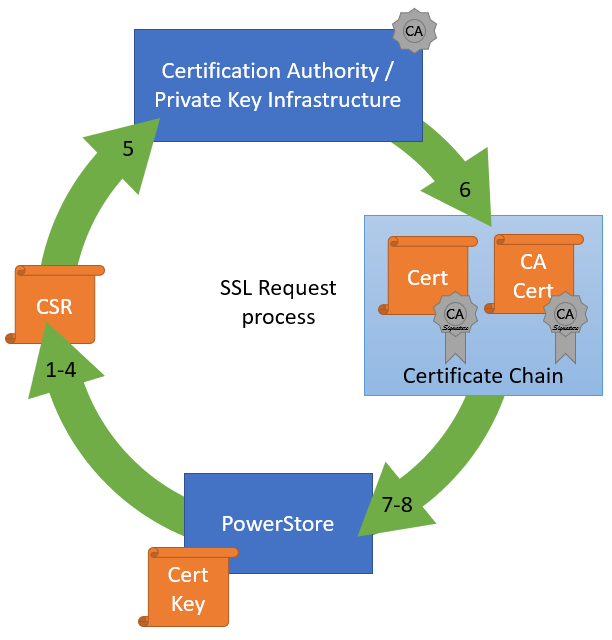
The following figure illustrates the steps required to deploy the certificate in PowerStore Manager:
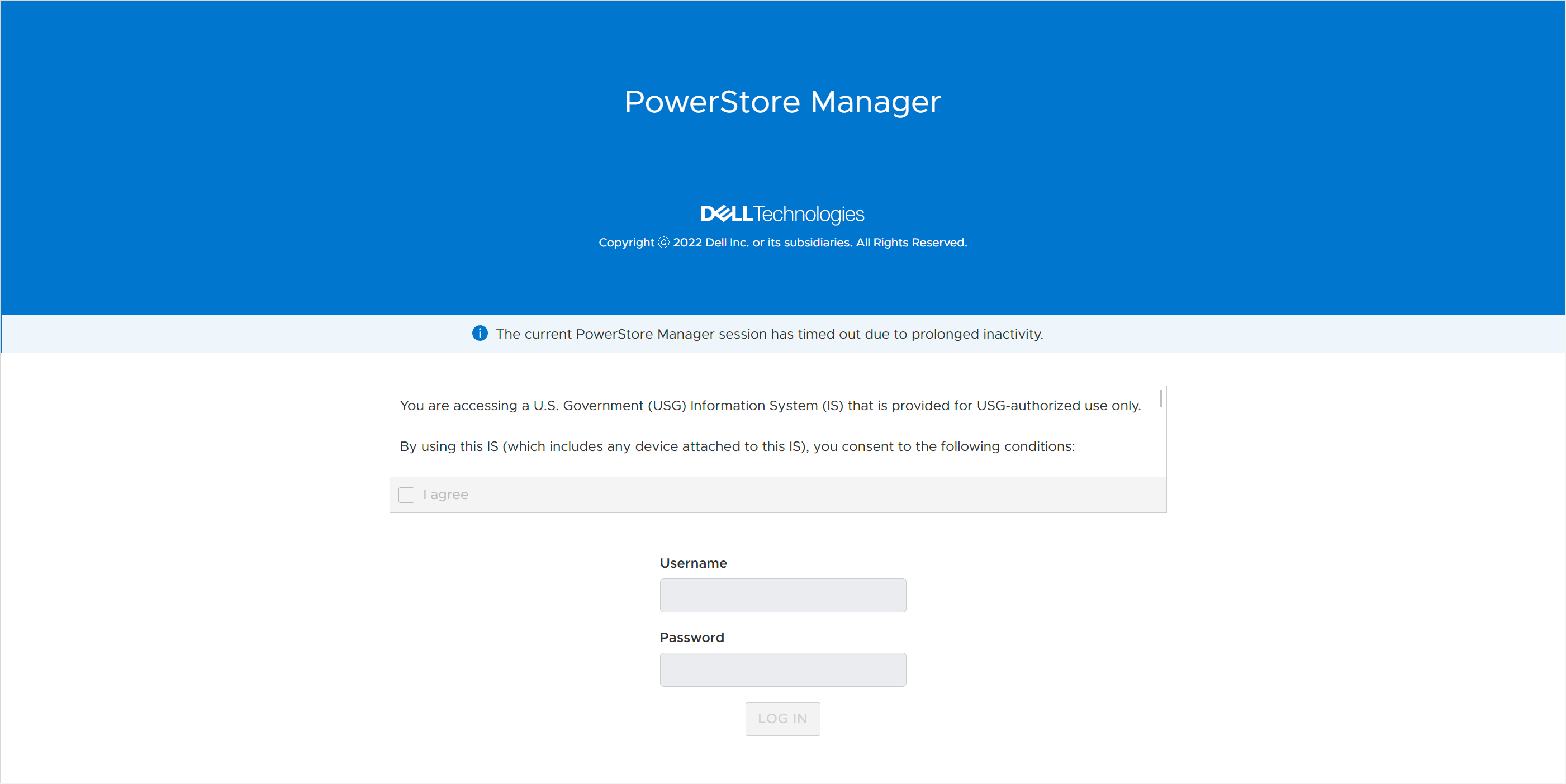
- Log into PowerStore Manager.
Note that your browser shows that the connection is not secure: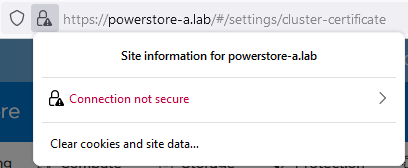
- Go to PowerStore Settings > Security > Signed Cluster Certificate.
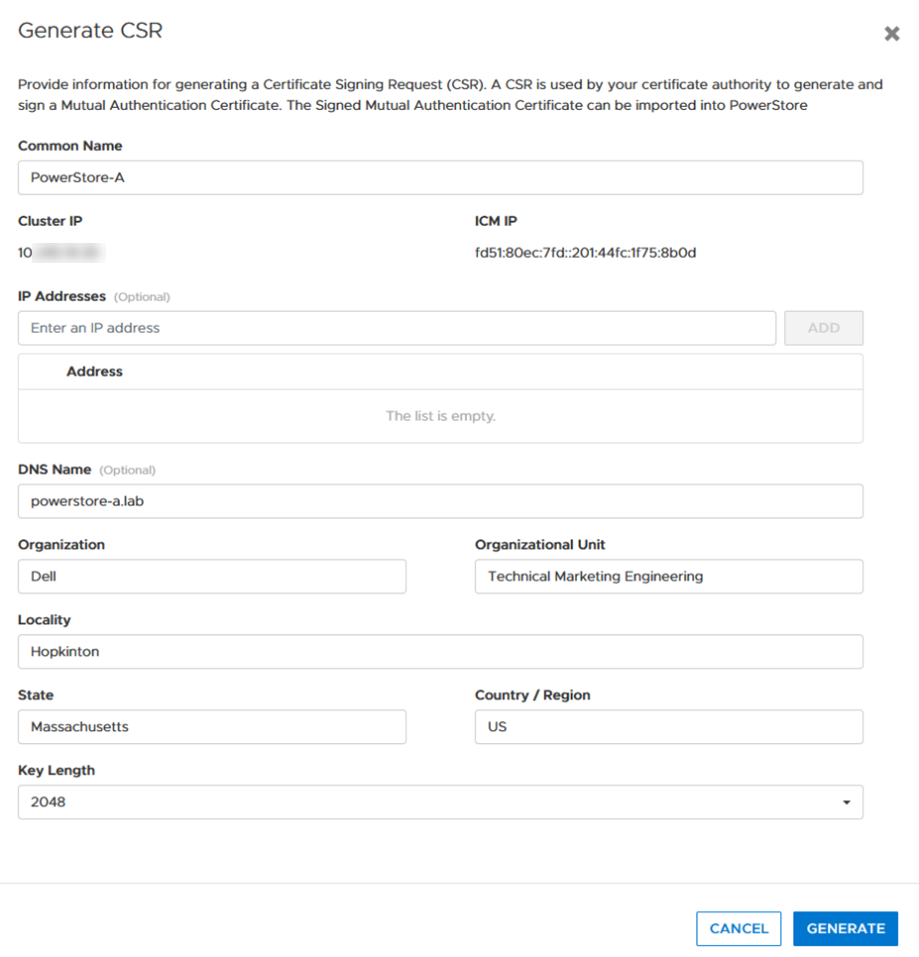
- Click the Generate CSR button and enter the required information to request a certificate.
a. Common Name Name of the certificate – usually the PowerStore cluster name
b. Cluster and ICM IP Mandatory for the Certificate and can’t be changed
c. IP Addresses Alternate IP Addresses which should appear in the certificate.
d. DNS name PowerStore FQDN
e. Organization Company Name
f. Organizational Unit Team / Organization
g. Locality Town
h. State State
i. Country/Region Two-letter country code
j. Key Length 2048 or 4096
4. When the CSR is created, click copy to clipboard and export the CSR content to a file -> for example, PowerStore.CSR
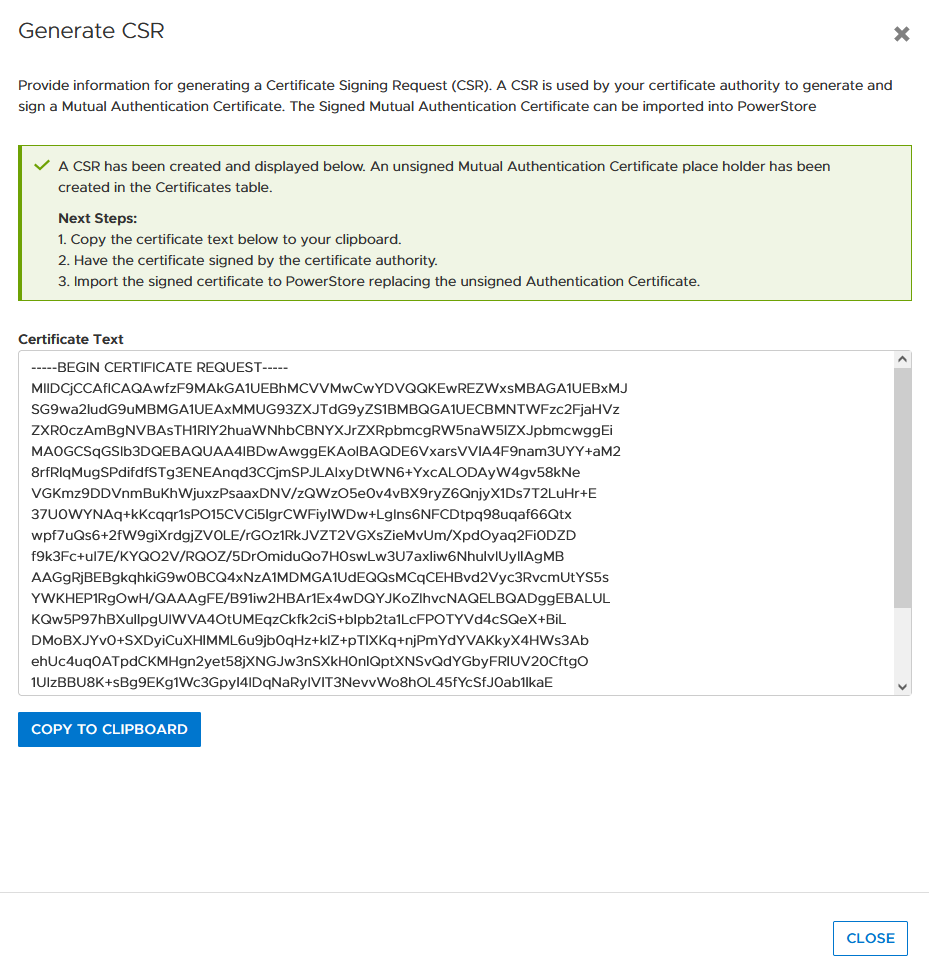
Optional: you can use the openssl tool to extract the contents of the CSR in a human readable format:
# openssl req -noout -text -in PowerStore.CSR
5. Send the CSR to your Certification Authority / PKI.
When there is an option to specify the format of the response, choose “PEM” format for the PowerStore and CA certificate. These files can be easily concatenated to a single certificate chain file (using the Linux CLI or a text editor) for import:
# cat powerstore.crt CA.crt > chain.crt
6. If not completed already, import the CA Certificate into your browser.
7. In PowerStore Manager, import the certificate chain in same screen where the CSR was generated.
Important: Sometimes the certificate file is in blocks. PowerStore expects the certificate in single lines, as in the following example with a PowerStore- and CA certificate:
-----BEGIN CERTIFICATE----- [...Single line PowerStore certificate content...] -----END CERTIFICATE----- -----BEGIN CERTIFICATE----- [...Single line CA Certificate certificate content...] -----END CERTIFICATE-----
If the individual certificates are not on a single line, the import will fail with the error “Failed to update certificate in credential store. Please verify your certificate chain. (0xE09010010013)”. You can use the openssl tool to verify that the file is ok:
# openssl x509 -in powerstore-chain.crt -noout -text
8. Start using PowerStore with a trusted HTTPS connection.
Installing a third party SSL certificate (PowerStore CLI)
Follow these steps to generate a certificate with PowerStore CLI for PowerStore-A. Be sure to format the CSR and certificate file correctly.
1. Generate CSR:
cli> x509_certificate csr -type Server -service Management_HTTP -scope External -key_length 2048 -common_name PowerStore-A -dns_name powerstore-a.lab -organizational_unit "Technical Marketing Engineering" -organization Dell -locality Hopkinton -state Massachusetts -country US
The response shows an ID and the CSR in a block. Keep the ID noted somewhere as it will be required for import. Also, use a text editor to make sure BEGIN- and END CERTIFICATE REQUEST are each on their own line when requesting the certificate:
-----BEGIN CERTIFICATE REQUEST----- [... a nice formatted block or single line ...] -----END CERTIFICATE REQUEST-----
2. Use CSR content to request the certificate.
3. Ensure that the issued certificate file is a single line string as required for import in PowerStore Manager. Note that the required line breaks need to be “\n”.
4. Import the certificate by using the ID and the certificate string:
cli> x509_certificate -id f842d778-0b28-4012-b8d5-66ead64d38e4 set -is_current yes -certificate “-----BEGIN CERTIFICATE-----\n[...Single line PowerStore certificate content...]\n-----END CERTIFICATE-----\n-----BEGIN CERTIFICATE-----\n[...Single line CA Certificate certificate content...] \n-----END CERTIFICATE-----"
Terms used:
CA Certification Authority
CN Common Name
CSR Certificate Sign Request
chain Single “chain” file with concatenated certificates
key Private certificate key
PEM Privacy-Enhanced Mail and commonly used to exchange certificates
SAN Subject Alternate Name
Resources
Author: Robert Weilhammer, Principal Engineering Technologist
Related Blog Posts

Enhancing your Data Center Security with VxRail
Fri, 28 Jul 2023 22:16:57 -0000
|Read Time: 0 minutes
In addition to providing operational efficiency, VxRail fundamentally sets up a secure foundation for your organization’s data center. This blog post provides a high-level overview of VxRail security. For a complete understanding of VxRail security features, read the VxRail Comprehensive Security by Design white paper or view the three-part video series VxRail Security: A Secure Foundation for your Data Center:
The white paper and videos provide a complete picture of how security begins with VxRail design and extends through VxRail deployment in your IT infrastructure.
As an introduction to what you can expect to learn from the videos, here’s the first of the three:
The integrated components of VxRail are designed to help secure your data center, starting from the PowerEdge server layer running on Intel or AMD processors, to the VMware vSphere (ESXi) layer integrated with vSAN for virtual storage, to the VxRail HCI system software layer that provides life cycle management through VxRail Manager (which is accessed through the vCenter plug-in), and to other add-ons from Dell and VMware, such as RecoverPoint for Virtual Machines. The video series and security by design white paper provide information about data protection and how VxRail creates a stable environment to ensure business continuity.
VxRail is engineered to employ functions of the NIST framework: protect, detect, and recover to boost cyber resiliency. VxRail includes integrated features to protect VxRail BIOS, firmware, and your organization’s data stored in vSAN. The VxRail system built on the PowerEdge server has a system lockdown feature that prevents configuration changes that may lead to security vulnerabilities. The PowerEdge hardware of the VxRail system verifies the integrity of software update files moving through the integrated stack through the embedded UEFI Secure Boot feature, which ensures that the files are from vetted sources.
Furthermore, the VxRail nodes are protected through Intel’s Trusted Execution Technology (TXT). The TXT prevents the introduction of malware into the VxRail nodes is prevented by the TXT by verifying the cryptographically signed PowerEdge server firmware, BIOS, and hypervisor version. Also, VxRail devices deployed in open environments are protected using bezel locks, preventing the introduction of malware-infected USB drives. With the bezel locks, the ports can be disabled and enabled. In addition to using bezel locks on VxRail in an open environment, VxRail satellite nodes are protected from theft and the compromise of data privacy by self-encrypting drives (SEDs).
To secure your organization’s workloads, VxRail is designed to protect data and VMs using the VxRail Manager, VMware vSphere, and vSAN. FIPS 140-2 Level 1 encrypts data in use, data at rest, and data in transit. These keys are carefully stored using Dell BSAFE Crypto-C Micro Edition and two FIPS-validated cryptographic modules using AES 256-bit.
Dell provides hardening packages for your VxRail using the Security Requirement Guide published by the Defense Information Systems Agency (DISA) for customers seeking additional security that meets their industry or sector requirements. For more information about hardening your IT infrastructure, see the resource links at the end of this post.
If you have not already watched the VxRail security video series or read the white paper, I hope this short summary of features gives you some insight into the tremendous features of VxRail security. To learn more about how VxRail provides a secure foundation for your data center through a carefully vetted supply chain, secure development life cycle, and many other features provided by VxRail, see the following resources:
- Dell VxRail: Comprehensive Security by Design
- Dell VxRail Documentation Quick Reference List—For links to the Product Security Configuration Guide, STIG Hardening Guides, and other useful support documentation)
- VxRail Info Hub—For additional technical guides, white papers, blogs, and videos
- Dell VxRail Hyperconverged Infrastructure (Dell Technologies product page)
Author:
Olatunji Adeyeye, Product Manager

What's New in PowerStore OS 3.5?
Fri, 19 May 2023 16:56:13 -0000
|Read Time: 0 minutes
Dell PowerStoreOS 3.5 is the latest software release for the Dell PowerStore platform. In this release, there has been a large focus on data protection and security for PowerStore T as well as File networking, scalability, and more. We’ll cover all of these in this blog!
The following list highlights the major features to expect in this software release followed by additional details for each category.
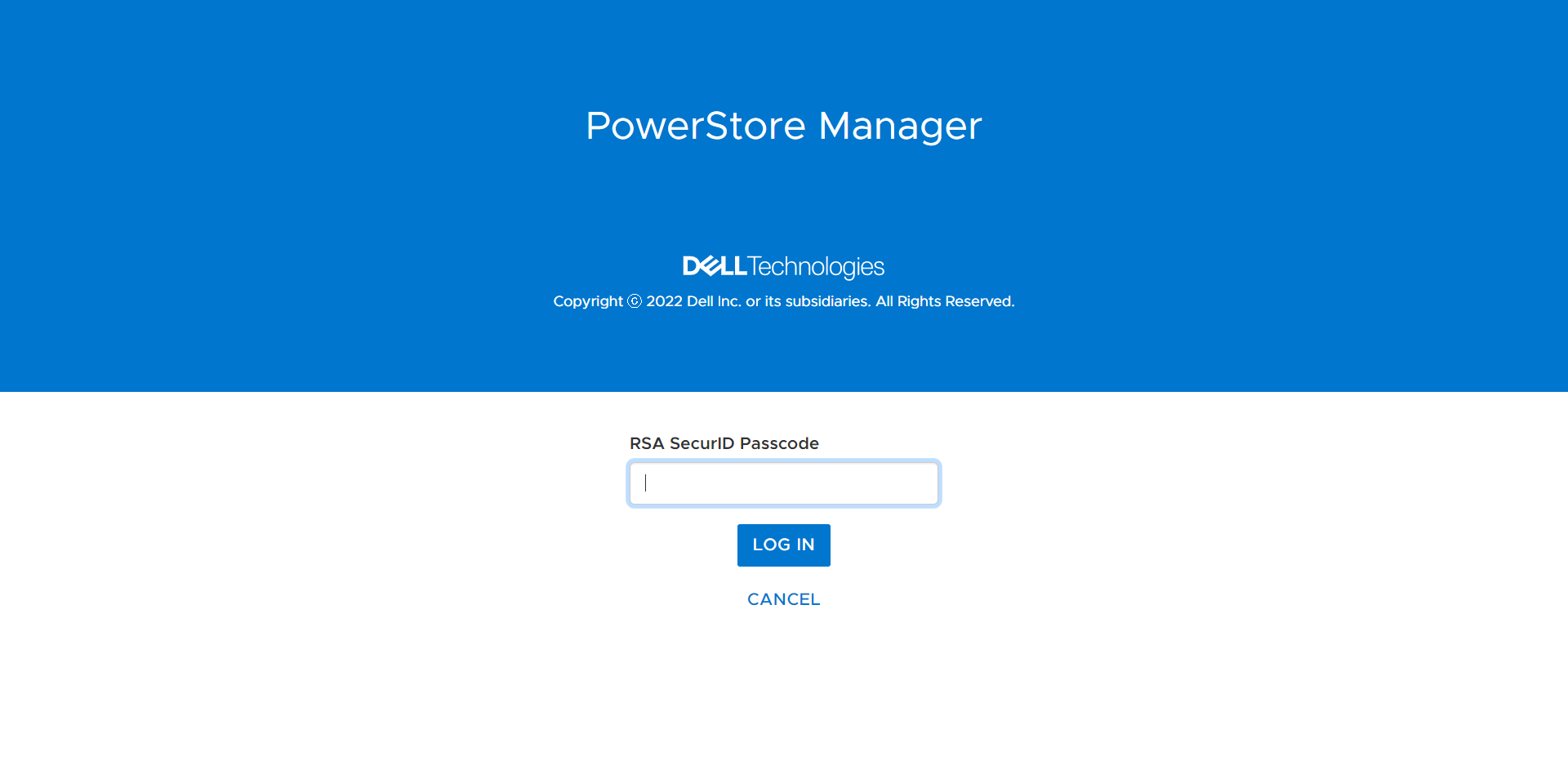
- Security: On the security side of the house, we’ve implemented support for Multi-Factor Authentication (MFA) for PowerStore Manager and REST API using RSA SecurID. Following the US Federal Security Technical Guide conditions, PowerStore now complies with STIG requirements. Also, users can now import a 3rd party certificate for the VMware VASA provider.
- Data Protection: We’ve added a few different enhancements to our data protection capabilities: the largest feature is a native backup solution that integrates with Dell PowerProtect DD series appliances. Metro Volume has seen some UI enhancements to help guide customers on selecting appropriate host connectivity options. The new secure snapshot setting protects snapshots from being accidentally or maliciously deleted.
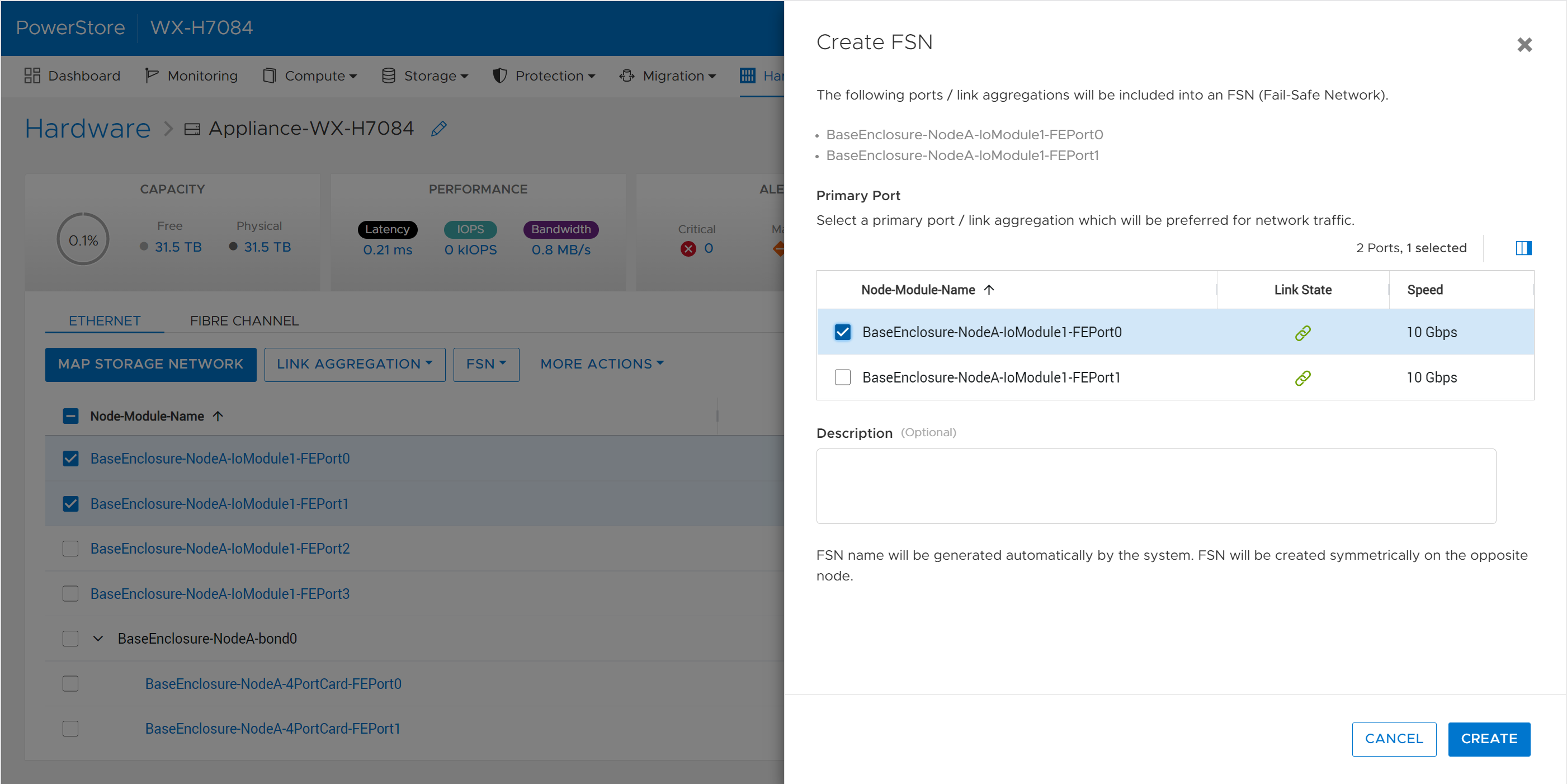
- File Enhancements: Through PowerStore Manager and REST, users can now manage file share permissions (ACLs). Fail-Safe Networking (FSN) can be created for NAS server interfaces, a lightweight and switch-agnostic form of link redundancy that complements link aggregation.
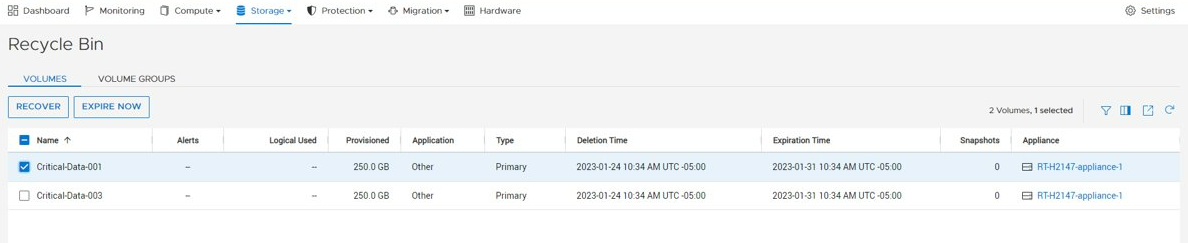
- Scaling & Capacity: We’ve improved scalability limits for file systems, volumes, and vVols. We’ve also added a Recycle Bin for retrieving deleted volumes, volume groups, and snapshots within an expiration period.
Security
Multi-Factor Authentication
Multi-Factor Authentication (MFA), also known as two-factor authentication, has become a modern-day standard not only in the datacenter, but in our everyday lives. In PowerStoreOS 3.5 and later, users can now enable MFA for PowerStore Manager and REST API. Once configured using your existing RSA Authentication Manager, users have two-factor authentication with LDAP users or PowerStore manager users using their RSA SecurID token.
Security Technical Implementation Guides (STIG compliance)
STIG mode is an optional setting that implements security configuration changes to harden the existing appliance all the way down to PowerStore’s base OS and containers. Having STIG compliance is typically a requirement for US Federal customers and dark sites alike. STIG compliance is also a prerequisite for the Approved Product List (APL) certification which is a standard for Department of Defense (DoD) organizations.
With Multi-Factor Authentication, Secure Snapshots, and STIG compliance, PowerStore is hardened to accommodate the security requirements of the US Federal Government and Zero Trust security environments.
Data Protection
Native PowerProtect DD Backup Integration
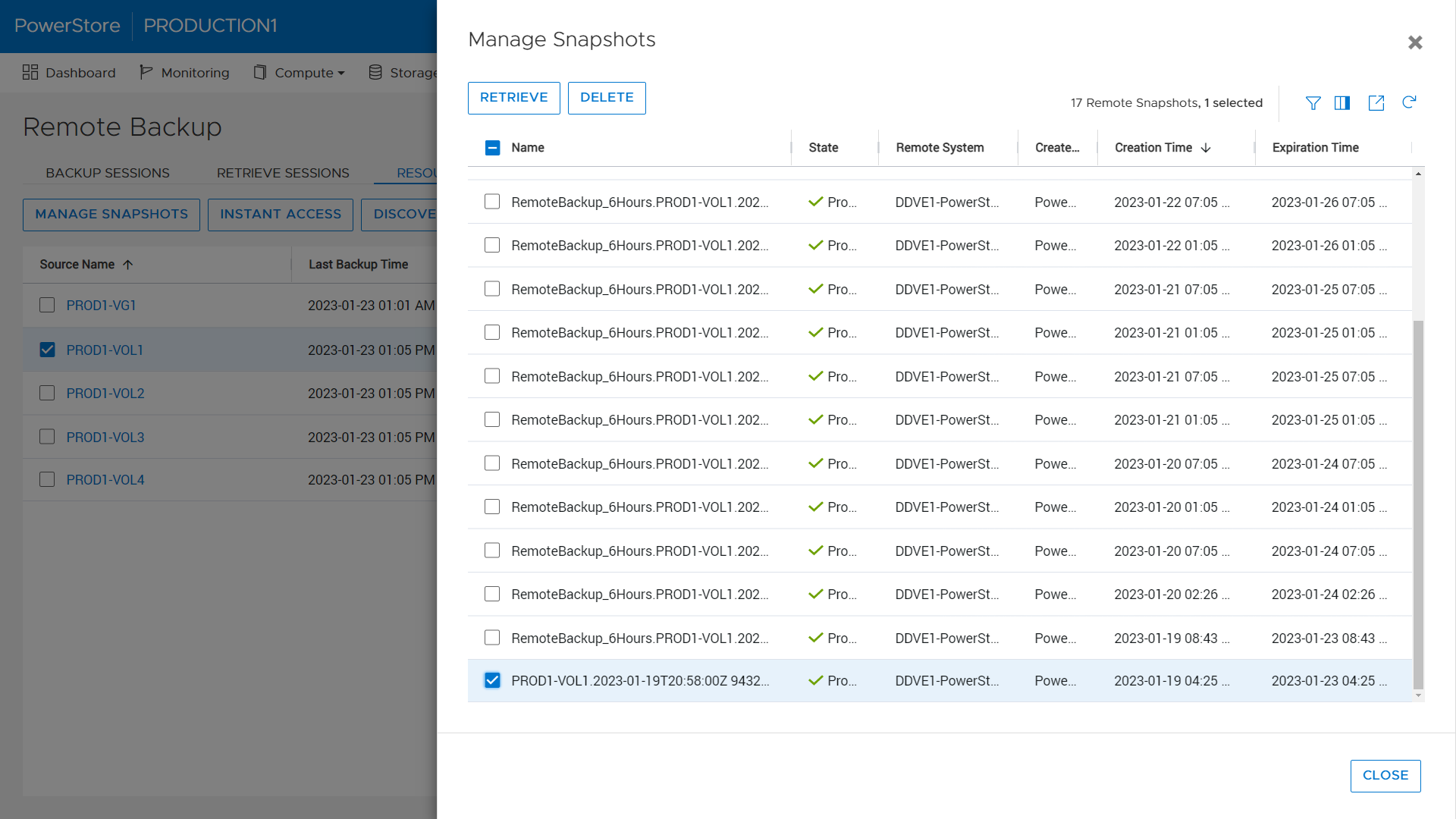
Studies show that using a backup and storage solution from a single vendor can reduce data protection administration costs by up to 22%. Using PowerStore’s native PowerProtect integration, backups in the form of remote snapshots can be initiated directly from PowerStore Manager using a remote connection to the PowerProtect DD appliance (physical or virtual edition). Users can set up cloud or on-prem backup in just 90 seconds natively within PowerStore Manager. PowerStore enables faster backups through tight integration with PowerProtect DD Appliances, enabling the ability to back up to 150TB daily.
Backups can be initiated manually or through a new protection rule called a Remote Backup Rule. Users can create remote backup sessions, retrieve snapshots, recover deleted or corrupted resources, and provide hosts with access to snapshots directly on the PowerProtect appliance. This host access, called Instant Access, provides access to data from a remote PowerProtect appliance in just seven clicks from a single UI.
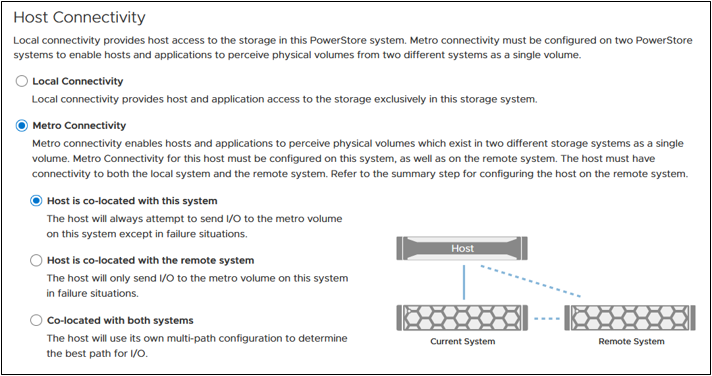
Metro Volume
Native Metro Volume, PowerStore’s synchronous active/active block replication technology introduced in PowerStoreOS 3.0, has been updated to include graphical representation of the host’s connectivity during setup to help users pick the right configuration. These configurations are Local Connectivity (also known as non-uniform), where the host is only connected to the local PowerStore appliance, and Metro Connectivity (known as uniform), where the host has connections to both local and remote PowerStore appliances. When selecting metro connectivity, the UI helps guide the user through the different connectivity options:
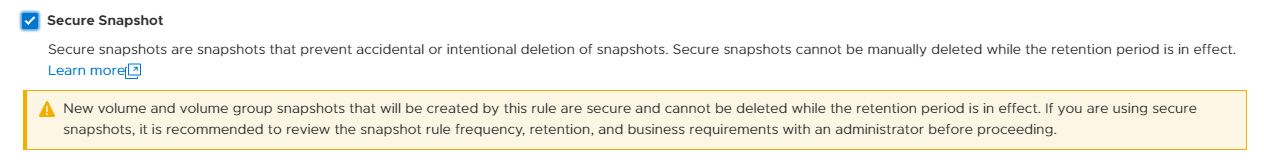
Secure Snapshots
The Secure Snapshot setting is an optional setting for volume and volume group snapshots. When the Secure Snapshot setting is enabled, the snapshot is protected from deletion until the retention period expires. The Secure Snapshot option also cannot be disabled on a snapshot after it is enabled. This provides a cost-effective line of defense against ransom attacks and accidental deletion of snapshots, volumes, or volume groups. Secure snapshots can also be created automatically using a Protection Policy containing a Snapshot Rule with the Secure Snapshot option enabled. The Secure Snapshot option within the Snapshot Rule can be enabled or disabled at any time. Changing this setting only affects future snapshot creations.
File enhancements
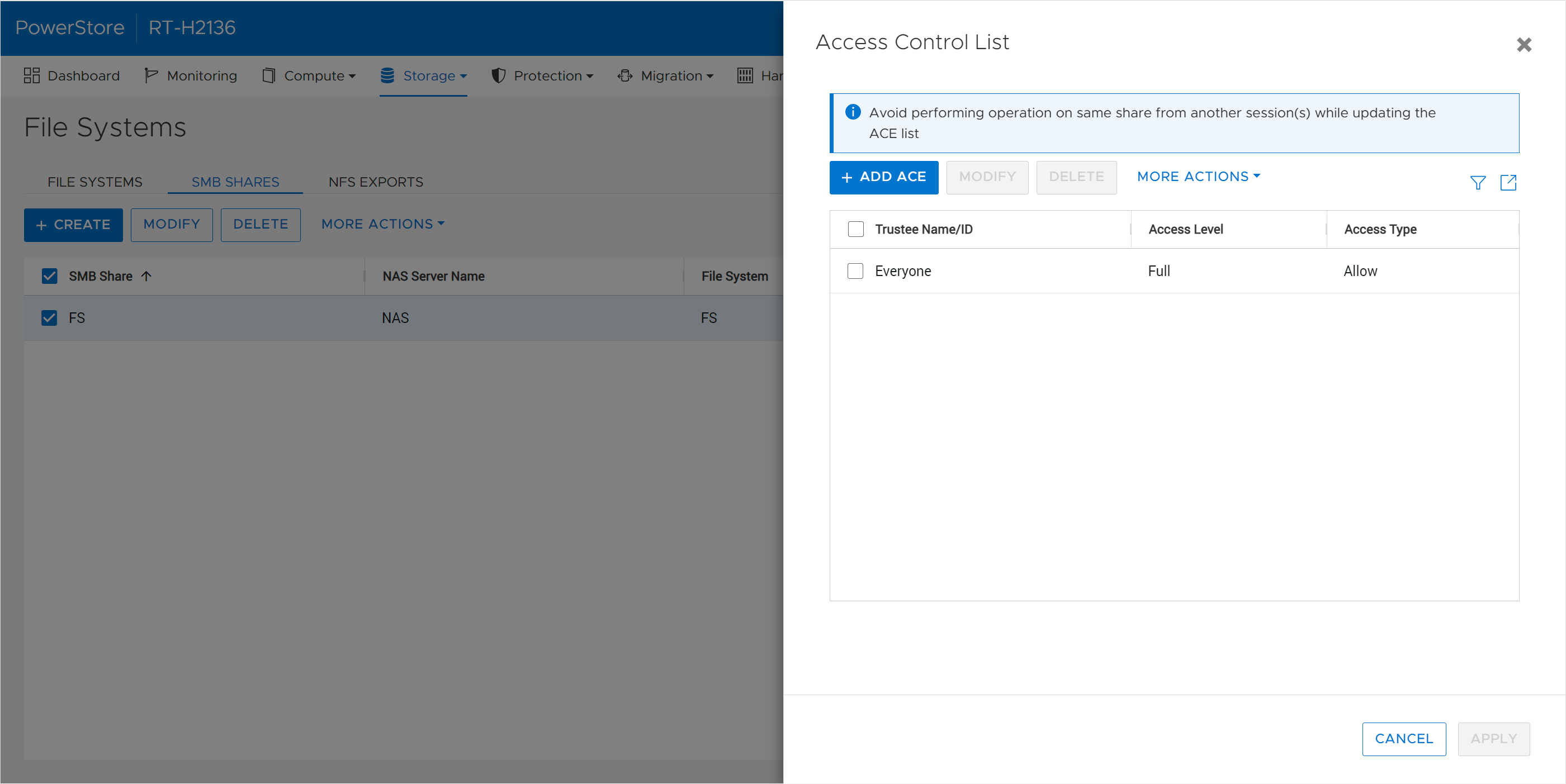
SMB share permissions (ACLs)
When provisioning a NAS share usingthe SMB protocol, the share permissions are managed from the client within an Access Control List (ACL). With PowerStoreOS 3.5, these permissions within the ACL can be managed directly from PowerStore Manager or REST API. Leveraging this feature, PowerStore users can define and manage existing share permissions without requiring access to the client-side environment.
Fail-Safe Networking (FSN)
Fail-Safe Networking is a well-known feature used in other products across the Dell portfolio, such as Unity XT, which provides a mechanism for switch-level redundancy. You may ask if this is needed since PowerStore already supports Link Aggregation (LA). Fail-Safe Networking provides a high availability solution that is switch agnostic for NAS interfaces. With FSN, users can eliminate single points of failure (ports, cables, switches, and so on) by linking ports together in an active/passive configuration. An FSN can consist of individual ports, Link Aggregations, or a combination of both. When used in conjunction with LA, multiple ports can be used as part of the active or backup part of the FSN.
Scalability and Capacity
File, volume, and vVol limit increase
Across the board, PowerStoreOS 3.5 brings increased limits to the number to file systems, volumes, and vVols that can be provisioned. The amount that the limits have increased for each of these resources depends on the PowerStore model. A few examples: the number of NAS servers for the PowerStore 3200 and higher is increased from 50 to 250 NAS servers per appliance. On a PowerStore 9200, the combined max number of volumes, vVols, and file systems is now 16,600 per appliance. There are also up to 4x the number of .snapshot files and file systems that can be provisioned. For a full list of resource limits on PowerStore, check out the support matrix.
Recycle bin
Research indicates that human error proves to be the most common cause of data loss - typically in the form of accidental deletion of data, unorganized data, or administrative errors. In the PowerStoreOS 3.5 release, we’ve introduced a recycle bin feature to combat accidental deletion of block storage resources. If a block resource is deleted, it will enter the recycle bin by default. The recycle bin is located in the Storage > Recycle Bin section of PowerStore Manager. In there, users can view, restore, and permanently expire volumes, volume groups, and their corresponding snapshots. Users can also customize the expiration period from 0-30 days depending on their requirements.
Conclusion
The PowerStoreOS 3.5 release offers a multitude of enhancements across the board for the PowerStore product. In the modern data center, PowerStore continues to deliver on security, data protection, and scalability with the performance of an end-to-end NVMe platform. It’s no wonder that PowerStore is deployed in over 90% of Fortune 500 vertical sectors and rated #1[1] in customer satisfaction!
Resources
For additional information about the features above, along with other information about the PowerStoreOS 3.5 release, consult the whitepaper and solution documents found below:
- Data Protection for PowerStore with PowerProtect DD Series Appliances
- Dell PowerStore Native Integration with Dell PowerProtect DD Series Appliances for DP in Oracle Environments
- Time to Rethink your SQL Backup Strategy – Part 2
- Dell PowerStore: Snapshots and Thin Clones
- Dell PowerStore: Cybersecurity
- Dell PowerStore: File Capabilities
- Dell PowerStore: Persistent Data Availability
- Dell PowerStore: Metro Volume
- Dell PowerStore: Microsoft SQL Server Best Practices
- Dell PowerStore: Oracle Best Practices
- Dell PowerStore: Microsoft Hyper-V Best Practices
- Dell PowerStore: MongoDB Solution Guide
- Dell PowerStore: VMware vSphere Best Practices
- Dell PowerStore: VMware vSphere with Tanzu and TKG Clusters
- Dell VxRail and Dell PowerStore: Better Together Through Dynamic AppsON
Other Resources
- What’s New In PowerStoreOS 3.2?
- PowerStore Simple Support Matrix
- PowerStore: Info Hub - Product Documentation & Videos
- Dell Technologies PowerStore Info Hub
Authors: Ryan Meyer and Ryan Poulin
[1] Based on Dell analysis in January 2022 comparing among Top 3 storage providers globally, using double-blinded, competitive benchmark Net Promoter Score (NPS) data gathered by third-party commissioned by Dell for 2H FY22.



