Home > Networking Solutions > Enterprise/Data Center Networking Solutions > Enterprise SONiC Networking Solutions > Guides > Dell Technologies Enterprise SONiC Edge with Cisco ISE > RADIUS Complete logs from ISE
RADIUS Complete logs from ISE
-
Figure 178.
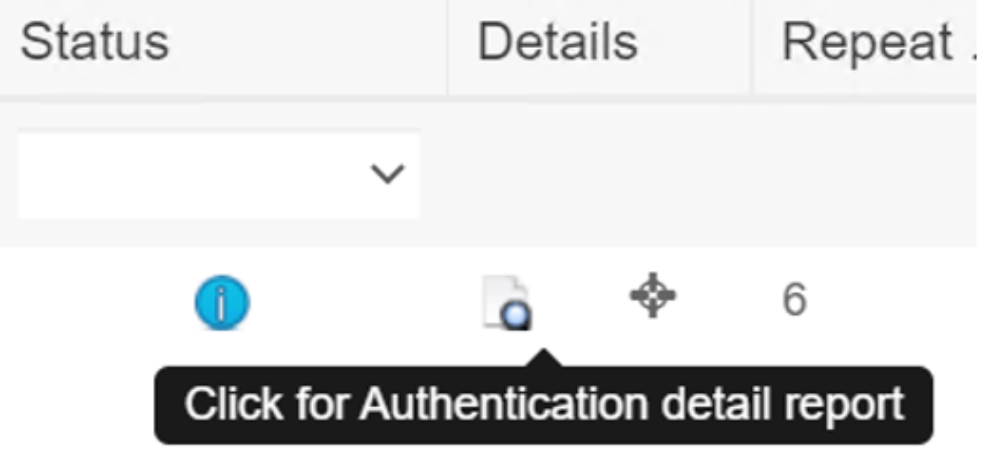
One clickable button in RADIUS Live Log to open the complete RADIUS mesage logThe following list defines the complete logs for all the four endpoints we deployed in this setup:
- Dot1x Windows OS
- Dot1x Cisco IP phone
- MAB IP camera
- Dell Switch access
Overview of Windows OS dot1x endpoint log information
Event 5200 Authentication succeeded
Username Administrator (EAP passed the Windows username to ISE)
Endpoint Id 24:6E:96:44:03:9C
Endpoint Profile Dell-Device (see Figure XXX for Dell-Device Profiling Policy)
Authentication Policy Dell-SONiC-Edge-Switch-dot1x >> Wired dot1x
Authorization Policy Dell-SONiC-Edge-Switch-dot1x >> Windows OS Authorization Rule
Authorization Result Dell-SONIC-Dot1x,PermitAccess,Employees (See Authentication/Authorization Policy in Figure 138 and Figure 139)
Authentication details
Source Timestamp 2023-01-11 04:44:41.814
…
Policy Server dot1x-tme-lab
Event 5200 Authentication succeeded
Username Administrator
User Type User
Endpoint Id 24:6E:96:44:03:9C
Calling Station Id 24-6E-96-44-03-9C
Endpoint Profile Dell-Device
Authentication Identity Store Internal Users
Identity Group User Identity Groups:MARKETING,User Identity Groups:Employee,Profiled
Authentication Method dot1x
Authentication Protocol PEAP (EAP-MSCHAPv2)
Service Type Framed
Network Device Leaf12
Device Type All Device Types#Dell S-Z-N-series and Ent. SONiC
Location All Locations#Dell-RR-Lab_N_Series_RACK
NAS Port Type Ethernet
…
Other attributes
ConfigVersionId 227
…
DTLSSupport Unknown
HostIdentityGroup Endpoint Identity Groups:Profiled
Model Name N3248PXE-ON (This is defined in Network Device Entry, Leaf12, see Figure 106)
Software Version 4.0
Network Device Profile DELL-Switch-DOT1X
Location Location#All Locations#Dell-RR-Lab_N_Series_RACK
Device Type Device Type#All Device Types#Dell S-Z-N-series and Ent. SONiC (These attributes are part of Network Device definition)
IPSEC IPSEC#Is IPSEC Device#No
EndPointPolicy 21a2e0f0-8c00-11e6-996c-525400b48521
EnableFlag Enabled
RADIUS Username Administrator
Device IP Address 100.67.152.30 (This is Dell Switch IP address, See Figure 106 )
CPMSessionID 6443973aRjP0sVHo9ZmARqR0Q0QZKwbJrByF6QlHiiFaIT
Called-Station-ID E8-B5-D0-5C-8F-BF:
Result
Class CACS:6443973aRjP0sVHo9ZmARqR0Q0QZKwbJrByF6QlHiiFaIT_r_kw:dot1xtme-
…
Tunnel-Medium-Type (tag=1) 802
Tunnel-Private-Group-ID (tag=1) 338 (VLAN assigned to Windows endpoint See Figure 145)
cisco-av-pair cts:security-group-tag=0004-00
…
LicenseTypes Base and Plus license consumed
Steps
11001 Received RADIUS Access-Request
…
11015 An Access-Request MUST contain at least a NAS-IP-Address, NAS-IPv6-Address, or a NAS-Identifier; Continue processing
12302 Extracted EAP-Response containing PEAP challenge-response andaccepting PEAP as negotiated
…
12805 Extracted TLS ClientHello message
12806 Prepared TLS ServerHello message
12807 Prepared TLS Certificate message
12808 Prepared TLS ServerKeyExchange message
12810 Prepared TLS ServerDone message (First use TLS certificate to authenticate)
12811 Extracted TLS Certificate message containing client certificate
…
22072 Selected identity source sequence - All_User_ID_Stores
15013 Selected Identity Source - Internal Users
24210 Looking up User in Internal Users IDStore – Administrator (Then use Windows username/password to authenticate)
24212 Found User in Internal Users IDStore
22037 Authentication Passed
…
15036 Evaluating Authorization Policy
24209 Looking up Endpoint in Internal Endpoints IDStore – Administrator (It’s authenticated through certificate and Windows login username/password)
24211 Found Endpoint in Internal Endpoints IDStore
…
11002 Returned RADIUS Access-Accept
Cisco IP Phone Dot1x Endpoint Log
Overview
Event 5200 Authentication succeeded
Username CP-8841-SEPF0B2E58FC22F
…
Authentication details
Source Timestamp 2023-01-11 04:44:42.035
Received Timestamp 2023-01-11 04:44:42.035
Policy Server dot1x-tme-lab
Event 5200 Authentication succeeded
Username CP-8841-SEPF0B2E58FC22F
Endpoint Id F0:B2:E5:8F:C2:2F
Calling Station Id F0-B2-E5-8F-C2-2F
Endpoint Profile Cisco-Device
Identity Group Profiled
…
Other attributes
ConfigVersionId 227
…
Serial Number 40 5C 60 06 00 00 00 26 EE 17
Subject - Common Name CP-8841-SEPF0B2E58FC22F
Subject Alternative Name CP-8841-SEPF0B2E58FC22F
Subject - Organization Cisco Systems Inc.
…
IdentitySelectionMatchedRule Wired dot1x
TLSCipher ECDHE-RSA-AES256-GCM-SHA384 (It’s Elliptic Curve Digital Signature Algorithm with SHA384 encryption)
TLSVersion TLSv1.2
DTLSSupport Unknown
Subject CN=CP-8841-SEPF0B2E58FC22F,OU=CTG,O=Cisco Systems
Inc.,SERIALNUMBER=PID:CP-8841 SN:FCH19278RZG (This is the identity name for authentication)
…
EndPointPolicy 0eba7c50-8c00-11e6-996c-525400b48521
RADIUS Username CP-8841-SEPF0B2E58FC22F (ISE has this identity entry for the phone, see Figure 173)
Device IP Address 100.67.152.30
…
Result
Filter-ID deny_ping
…
Tunnel-Private-Group-ID (tag=1) 688 (VLAN assigned to this endpoint see Figure 170)
cisco-av-pair cts:security-group-tag=0004-00
…
Steps
11001 Received RADIUS Access-Request
…
12800 Extracted first TLS record; TLS handshake started
12805 Extracted TLS ClientHello message
12806 Prepared TLS ServerHello message
12807 Prepared TLS Certificate message
12808 Prepared TLS ServerKeyExchange message
12809 Prepared TLS CertificateRequest message (TLS certificate and handshake)
12505 Prepared EAP-Request with another EAP-TLS challenge
…
12571 ISE will continue to CRL verification if it is configured for specific CA -
certificate for CP-8841-SEPF0B2E58FC22F
12571 ISE will continue to CRL verification if it is configured for specific CA -
…
15036 Evaluating Authorization Policy
24209 Looking up Endpoint in Internal Endpoints IDStore - CP-8841-
SEPF0B2E58FC22F (Use certificate subject to get an identity)
24211 Found Endpoint in Internal Endpoints IDStore
…
11002 Returned RADIUS Access-Accept
Note:
The 'client hello' message: The client starts the handshake by sending a "hello" message to the server. The message will include which TLS version the client supports, the cipher suites supported, and a string of random bytes known as the "client random."
The 'server hello' message: In reply to the client hello message, the server sends a message having the server's SSL certificate, the server's chosen cipher suite, and the "server random," another random string of bytes that's generated by the server.
IP Camera MAB Endpoint Log
Overview
Event 5200 Authentication succeeded
Username D0:21:F9:93:F7:58 (MAB use MAC address as username)
…
Authentication details
Source Timestamp 2023-01-11 04:44:43.988
…
Authentication Method mab
Authentication Protocol EAP-MD5 (MAB use EAP-MD5, no certificate/PKI)
Service Type Call Check
…
Other attributes
ConfigVersionId 227
…
Called-Station-ID 00:00:00:00:00:00
Result
Class CACS:6443973a1i9n7JPKP1HP_j1lRovXoZcSfPkr3xLyOj2ky/rQD2A:dot1x-tme-lab/456286262/6017
Tunnel-Type (tag=1) VLAN
Tunnel-Medium-Type (tag=1) 802
Tunnel-Private-Group-ID (tag=1) 588 (this is the VLAN assigned to MAP endpoint, see Figure 183)
cisco-av-pair cts:security-group-tag=0004-00
Steps
11001 Received RADIUS Access-Request
…
11028 Detected Host Lookup UseCase (UserName = Calling-Station-ID)
15041 Evaluating Identity Policy
…
15013 Selected Identity Source - Internal Endpoints
24209 Looking up Endpoint in Internal Endpoints IDStore - D0:21:F9:93:F7:58
24211 Found Endpoint in Internal Endpoints IDStore
…
Note: EAP-MD5: EAP-MD5 is the base security requirement in the EAP standard and uses username and passwords as the authentication credentials. EAP-MD5 protects the message exchange by creating a unique “fingerprint” to digitally sign each packet to ensure that the EAP messages are authentic. EAP-MD5 is very “light weight” and performs its operations very quickly, making it easy to implement and configure. EAP-MD5 does not use any PKI certificates to confirm the client or supply strong encryption to protect the authentication messages between the client and the authentication server.
Switch Access Log
Overview
Event 5200 Authentication succeeded
Username labadmin
Endpoint Id 100.94.224.42
Endpoint Profile
Authentication Policy Dell-SONiC-Edge-Switch Access >> Network Device Authentication
Authorization Policy Dell-SONiC-Edge-Switch Access >> Network Device Authorization Rule
Authorization Result Network_Services,PermitAccess
Authentication details
Source Timestamp 2023-01-11 04:52:32.64
…
Identity Group User Identity Groups:ALL_ACCOUNTS (default)
Authentication Method PAP_ASCII (use PAP to authenticate user through password)
Authentication Protocol PAP_ASCII
…
Other attributes
ConfigVersionId 227
…
EnableFlag Enabled
RADIUS Username labadmin
NAS-Identifier Leaf12
Device IP Address 100.67.152.30
CPMSessionID 6443973amuIPuGM61_Ui59qT8QOnoJ7dtnW7Folfl1isI087ahY
Result
Class CACS:6443973amuIPuGM61_Ui59qT8QOnoJ7dtnW7Folfl1isI087ahY:dot1x-tmelab/
456286262/6018
cisco-av-pair cts:security-group-tag=0003-00
Steps
11001 Received RADIUS Access-Request
…
15013 Selected Identity Source - Internal Users
24210 Looking up User in Internal Users IDStore - labadmin
24212 Found User in Internal Users IDStore (No EAP involved in switch access authentication)
22037 Authentication Passed
…
