Dell SONiC Edge bundle switch configuration for Cisco ISE
Home > Networking Solutions > Enterprise/Data Center Networking Solutions > Enterprise SONiC Networking Solutions > Guides > Dell Technologies Enterprise SONiC Edge with Cisco ISE > Dell SONiC Edge bundle switch configuration for Cisco ISE
Dell SONiC Edge bundle switch configuration for Cisco ISE
-
AAA/RADIUS server configuration for Cisco ISE
The following chapters provide detail descriptions on how to configure Dell SONiC Edge switch, how to create network device, profile, group, and policy in Cisco ISE RADIUS server, and integrate them together for AAA, dot1x, and MAB authentication and authorization.
Here are the configuration commands for Dell SONiC Edge switch (NAS) to send authentication and authorization requests to AAA/RADIUS server are:
aaa authentication login default local group radius
aaa authentication failthrough enable
aaa authentication login default can be local or radius. To configure radius as the first authentication, use the following CLI:
aaa authentication login default group radius local
Every authentication request will go to RADIUS server first, then local. The default SONiC operating system username admin is not supported in Cisco ISE because it is reserved for ISE default administrator username. Any usernames that are not configured in ISE will be rejected and the login will use the local switch username list for authentication.
The “aaa authentication failthrough enable” CLI ensures that if the first authentication failed, it will take the next authentication method in the order.
RADIUS configuration commands for RADIUS server (Cisco ISE)
The configuration commands to specify AAA/RADIUS server connection parameters are:
radius-server timeout 5
radius-server auth-type pap
radius-server host 100.67.151.58 auth-port 1812 key <intended key/shared secret for RADIUS network device entry> source-interface Management 0
radius-server auth-type by default is Password Authentication Protocol (PAP). With PAP, switch log has been authenticated with username password, not through security certificates or other authentication methods.
100.67.151.58 is Cisco ISE IP address and the default RADIUS UDP port is 1812, the key is the shared secret between switch and Cisco ISE. This shared key must match the one in Cisco ISE network device. See Figure 105 for more details.
The source-interface keyword is to specify where the RADIUS access request is coming from. This source interface IP address will be used in Cisco ISE network device configuration. In our example, the management 0 IP address is, 100.67.152.30. See Figure 104 Detail of a Network Device (Device Profile and Group) for more information.
show running-configuration interface Management 0
!
interface Management 0
description Management0
mtu 1500
autoneg on
speed 1000
ip address 100.67.152.30/24 gwaddr 100.67.152.254
Network device (Dell SONiC Edge bundle switch) access control with Cisco ISE
Using the switch network and the corresponding configuration in Cisco ISE (username/password, network device, etc.), login to switch using these usernames are authenticated through local first, then to Cisco ISE username/password databased. Once authenticated, it can supply authorized access based on Cisco ISE policy for that user.
Dot1x and MAB (MAC address Authentication Bypass) network interface configuration for Cisco ISE
Dot1x configuration for Windows OS, Ethernet 1/22
Here are the configuration commands to enter in Dell SONiC switch to enable dot1x authentication for Windows OS endpoint.
interface Eth1/22
description "windows server dot1x"
mtu 9100
speed auto
no shutdown
authentication max-users 3
authentication host-mode multi-auth
authentication port-control auto
authentication event fail action authorize vlan 30
dot1x pae authenticator
authentication periodic
Dot1x configuration for Cisco IP phone, Ethernet 1/23
Here are the configuration commands to enter in Dell SONiC switch to enable dot1x authentication for Cisco IP phone endpoint.
interface Eth1/23
description "Cisco IP CP-8841 attached"
mtu 9100
speed auto
no shutdown
switchport trunk allowed Vlan 688
network-policy 10
authentication max-users 3
authentication host-mode multi-auth
authentication port-control auto
authentication event fail action authorize vlan 30
dot1x pae authenticator
authentication periodic
We configured both these dot1x ports to use dot1x as the first authentication order (does not show in the running configuration). If dot1x failed, we want the ports to stay locked, no MAB bypass. Another choice is to add mab in the configuration to use it as an alternative authentication method.
MAB configuration for PoE IP camera, Ethernet 1/24
Here are the configuration commands to enter in Dell SONiC switch to enable dot1x/MAB authentication for PoE camera endpoint.
interface Eth1/24
description "PoE Camera on this port"
mtu 9100
speed 1000
no shutdown
authentication max-users 3
authentication host-mode single-host
authentication port-control auto
authentication order mab
authentication event fail action authorize vlan 30
dot1x pae authenticator
authentication periodic
mab
We specify MAB as the first authentication method since we know the endpoint (IP camera) does not have dot1x authentication capability.
Cisco ISE configuration for Dell SONiC Edge Bundle Switch
Create network device for Dell Switch
- Create a Leaf12 Network Device for our Dell SONiC Edge Bundle switch.
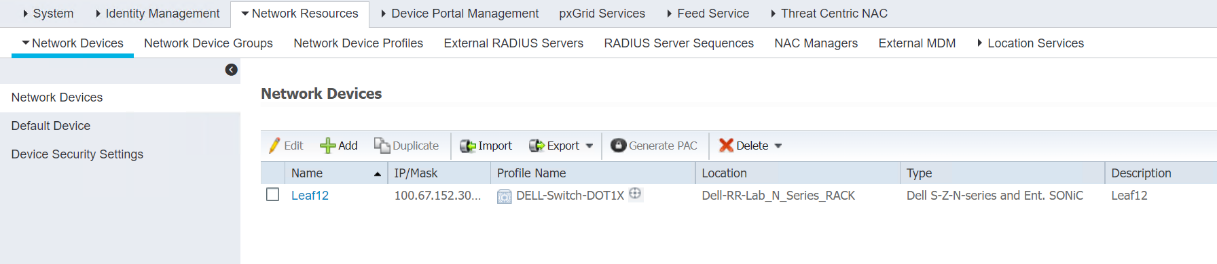 Figure 102. List of Network Devices
Figure 102. List of Network Devices
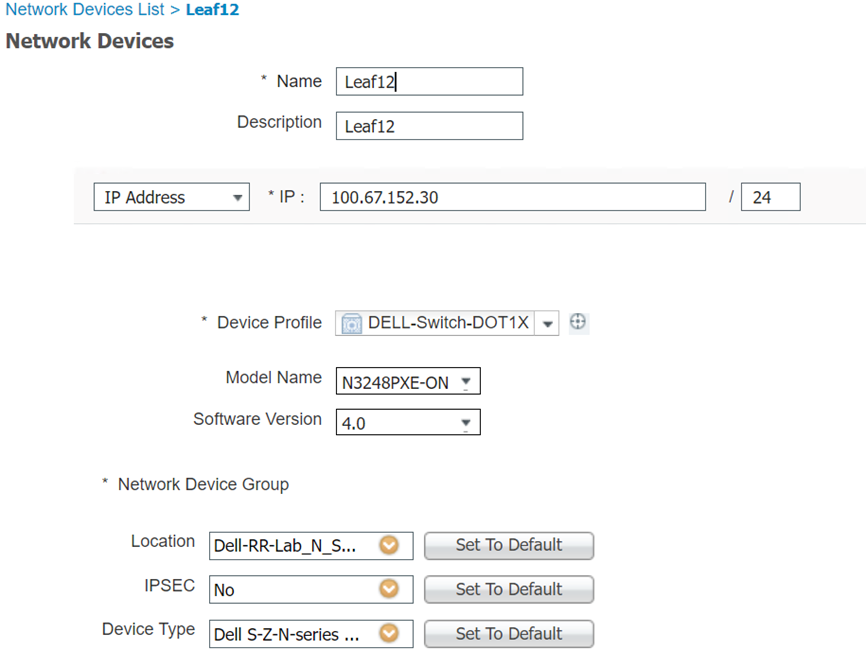
Figure 103. Detail of a Network Device (Device Profile and Group)
The Network Device IP address is from the Dell Edge switch.
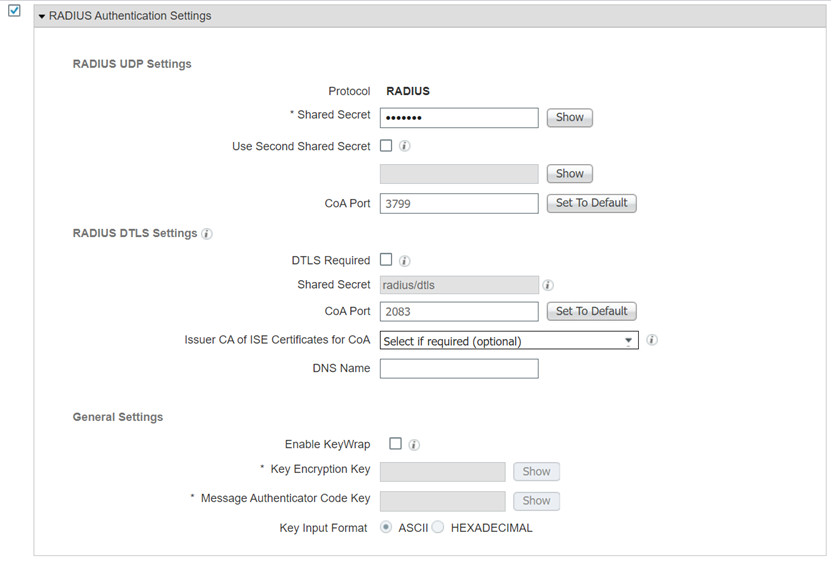
Figure 104. Detail of a Network Device (shared secret)
The RADIUS key shared secret is configured in Dell switch. When a RADIUS access request comes to ISE, it uses the IP address and shared secret to match the network devices defined in this page. Once matched, the device profile and group attributes used in this device are being used in ISE Policy Sets conditions.
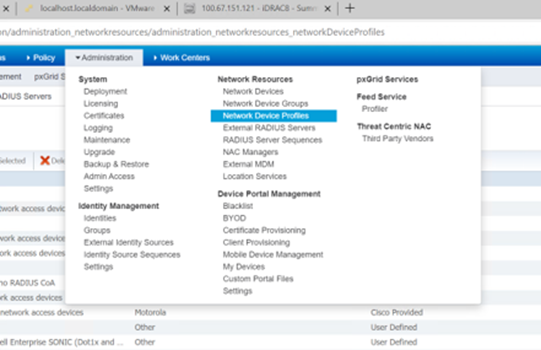
Figure 105. Drop down menu for Network Device profile
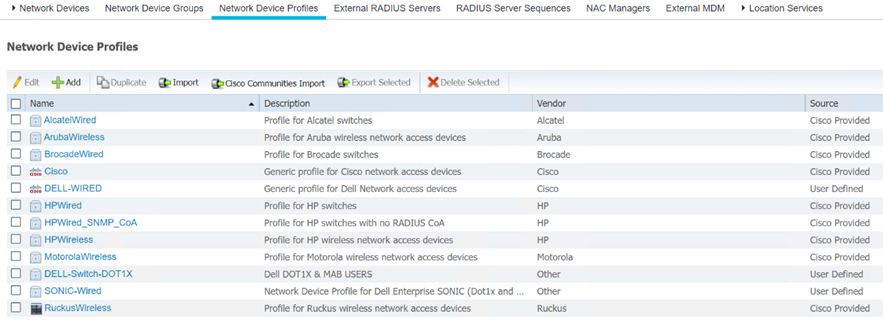
Figure 106. List Network Device profiles
The Source column shows what is included with the Cisco ISE package (Cisco Provided) and what is created by user (User Defined).
2. Click Add to create a new device profile, check the box next to the device profile, and click Edit to bring this device profile page.
3. Check the box next to the profile name and click Edit to view the profile detail page.
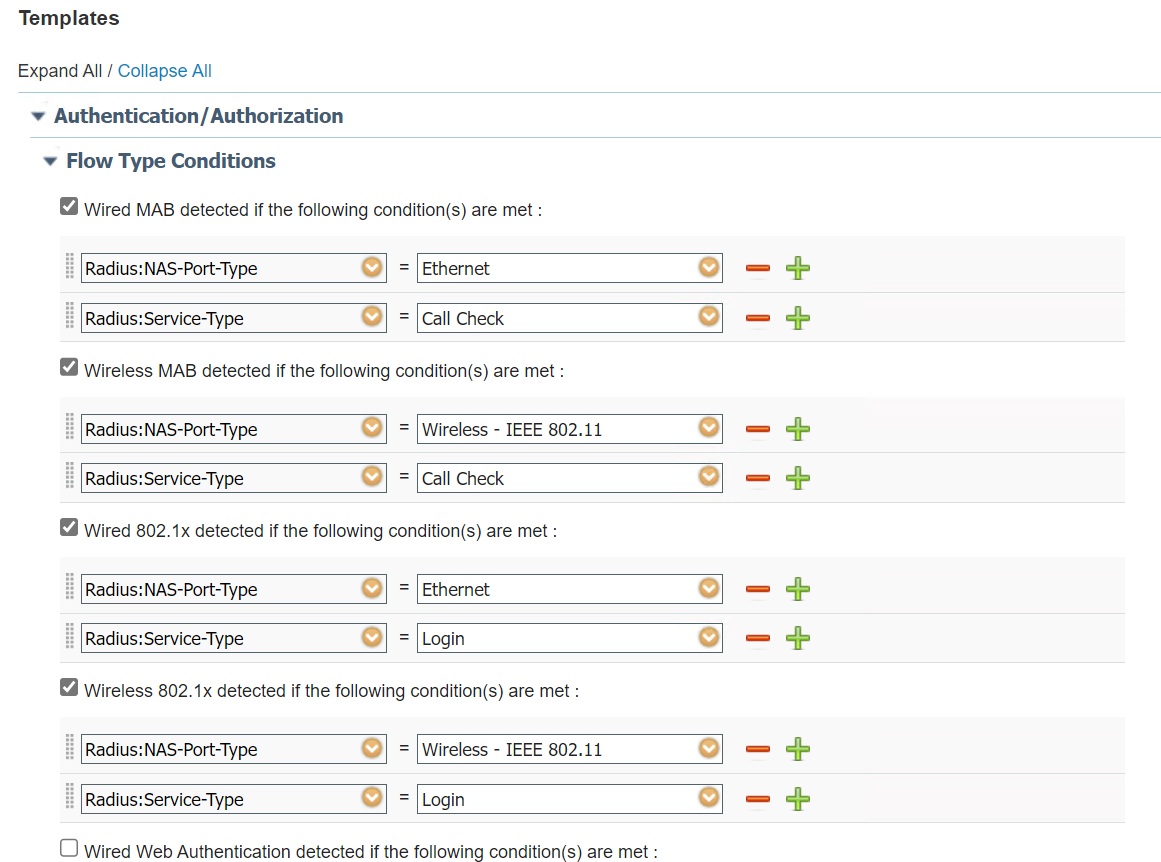
Figure 107. Detail of a network device profile (RADIUS dictionary)
4. Click Expand All and Collapse All toggle button to view authentication/authorization templates.
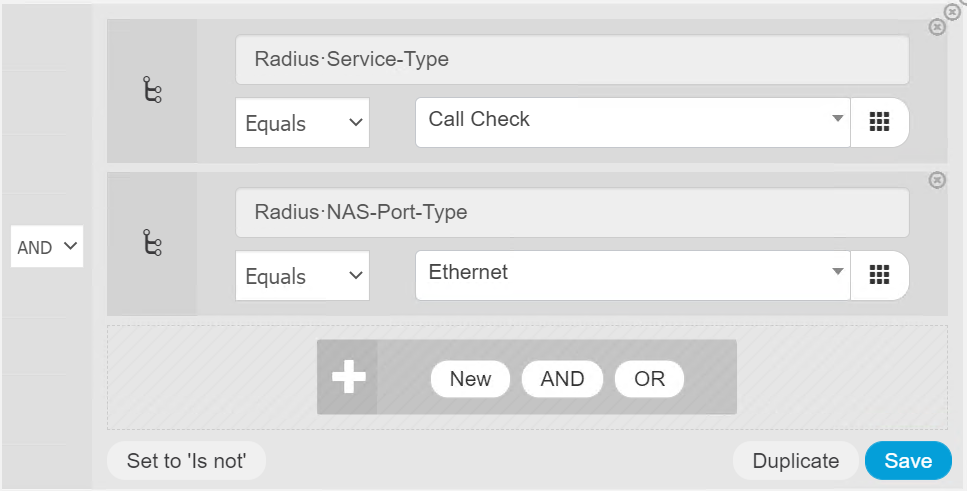
For this Dell-Switch-DOT1X device profile, create four RADIUS dictionary attributes to profile the Dell switch that can support wired and wireless Dot1x and MAB endpoints. Dot1x and MAB are differentiated through the RADIUS: Service-Type attribute. Wired and wireless are differentiated by the RADIUS: NAS-Port-Type attribute.
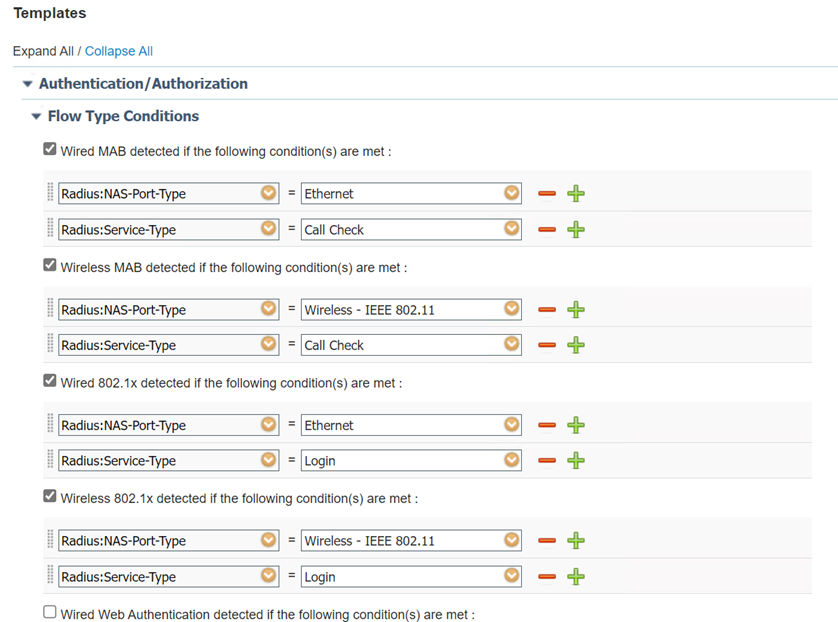
Figure 108. Detail of a network device profile (authentication and authorization attributes)
5. Click – to remove the attribute next to it.
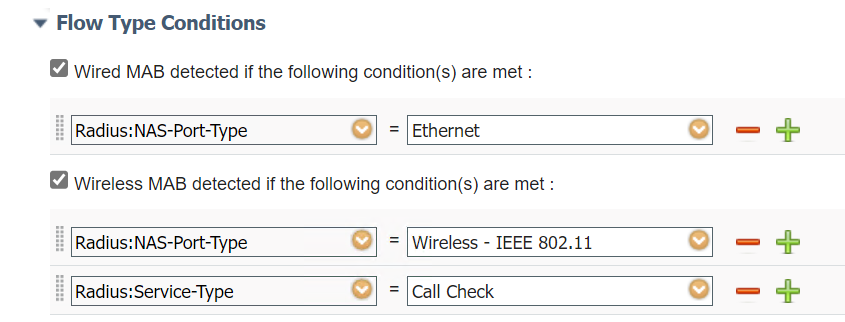 Figure 109. RADIUS attribute used in MAB authentication
Figure 109. RADIUS attribute used in MAB authentication6. Scroll down to display MAB Host lookup and permission settings. Check and select all fields for MAB authentication.
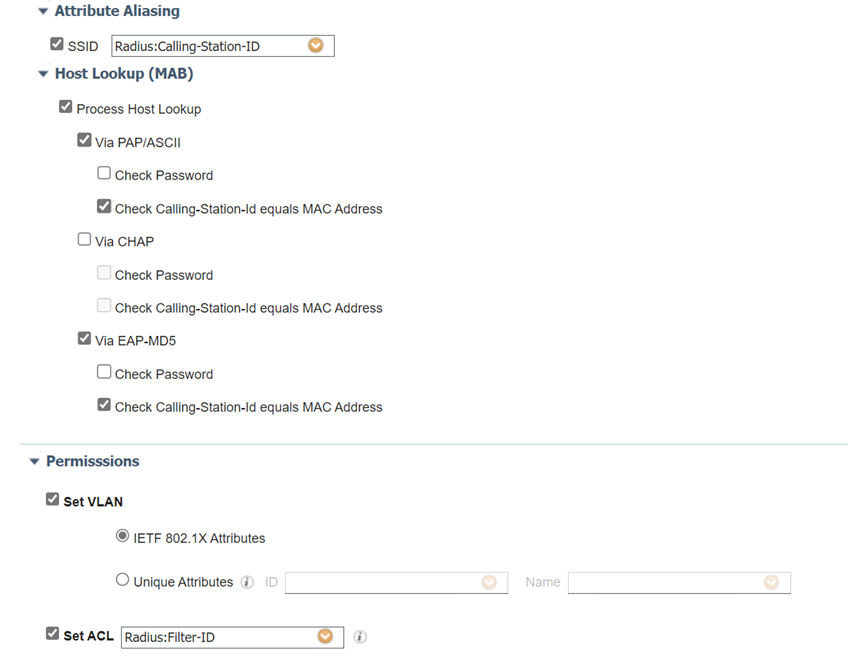
Figure 110. Detail of a network device profile (host lookup for MAB)
7. Once configured, scroll down to the bottom to save and submit the changes.
- Once configured, scroll down to the bottom to save and submit the changes.
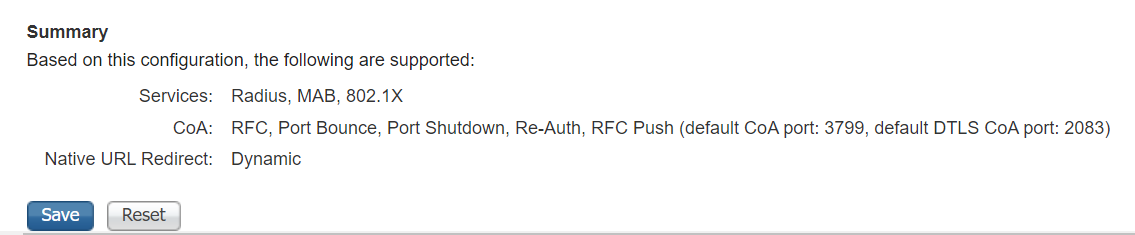
Figure 111. Save a modified network device profile
Network Device Groups configuration for Dell Switch
- The three Network Device Groups used in the “Leaf12” Network Device are created and displayed in Administration > Network Resources > Network Device Groups.
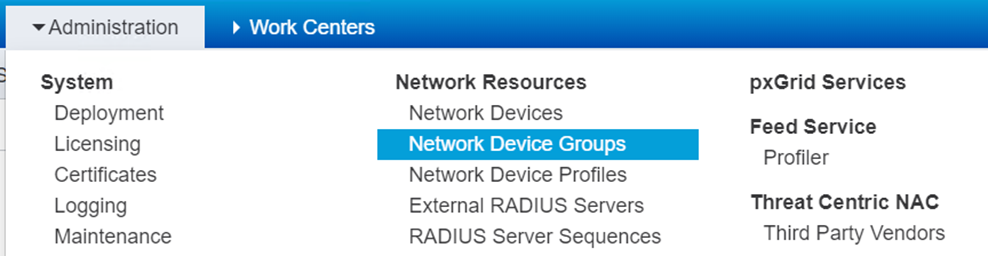
Figure 112. Drop down menu for Network Device Groups
2. Click the drop down menu to view the Network Device Groups page.
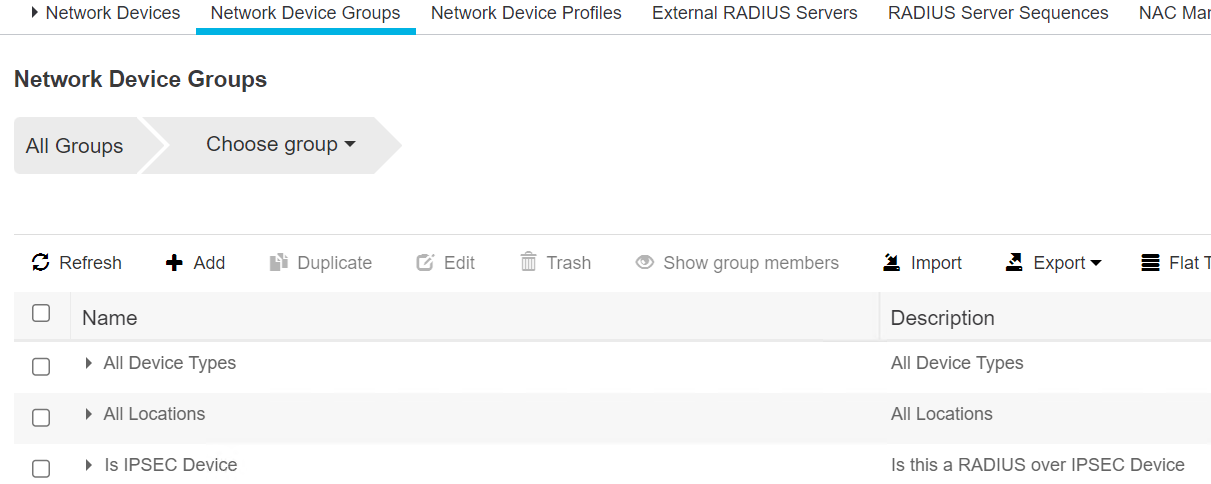
Figure 113. List of network device groups (collapsed view)
3. Click the caret next to each group to view the subgroups.
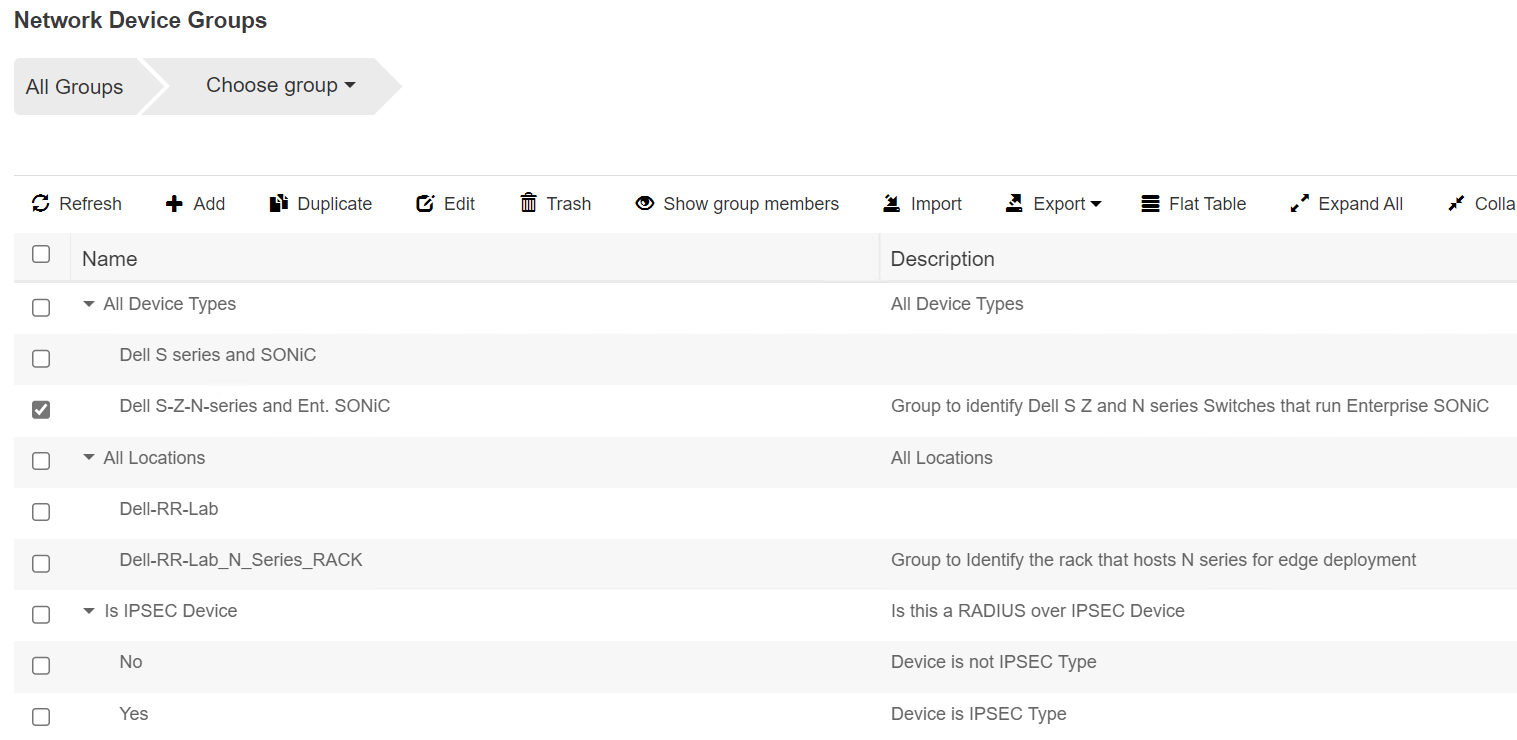
Figure 114. List of network device groups (expanded view)
User Configuration for Dell Switch
In this setup we created two identities, Administrator and labadmin. Administrator is used for Windows OS endpoint authentication. We enabled dot1x authentication in Windows OS with this username, Administrator. Use the following steps to create these identities.
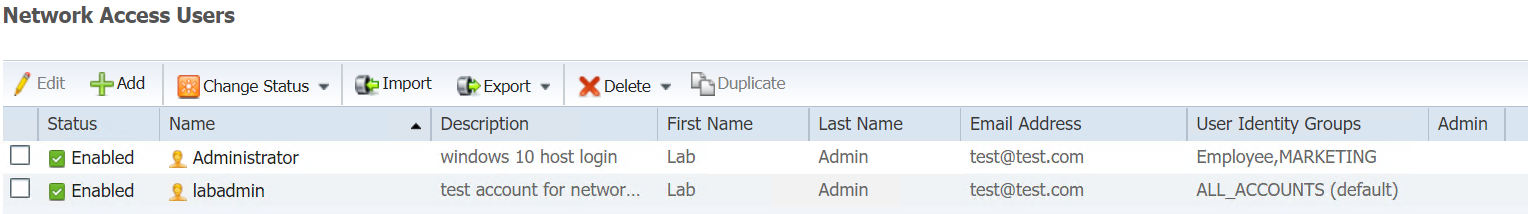
Figure 115. List of Identities
The Administrator username/password will be authenticated against RADIUS username/password database through the EAP MSCHAPv2 method.
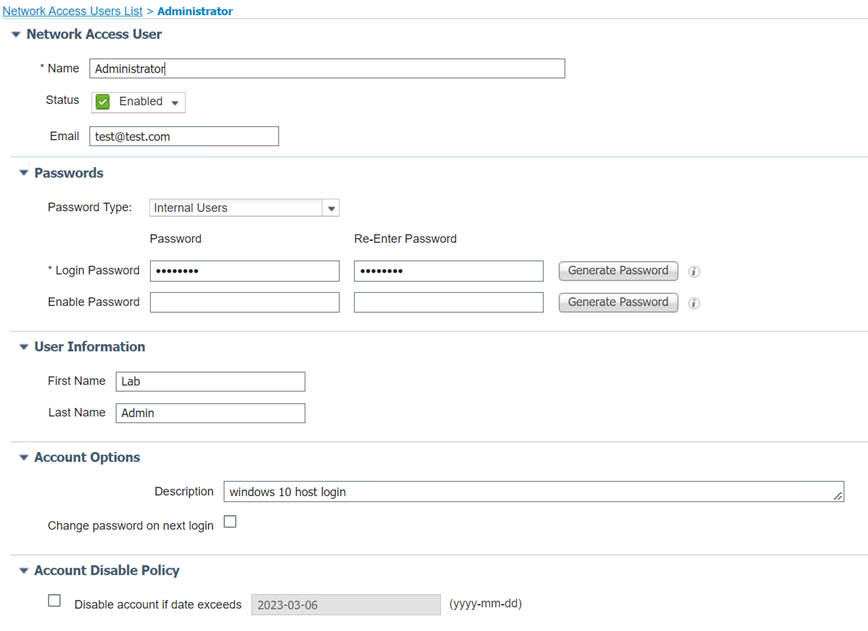
Figure 116. Administrator edit page
The login password is the same password that is used to log on to Windows OS through a monitor.
The labadmin identityis for Dell switch login access. To log on to the switch through console or ssh sessions, the user can enter labadmin username and the password stored in this entity. The RADIUS access request passes username/password to RADIUS server(Cisco ISE) and authenticates them against this labadmin identity.
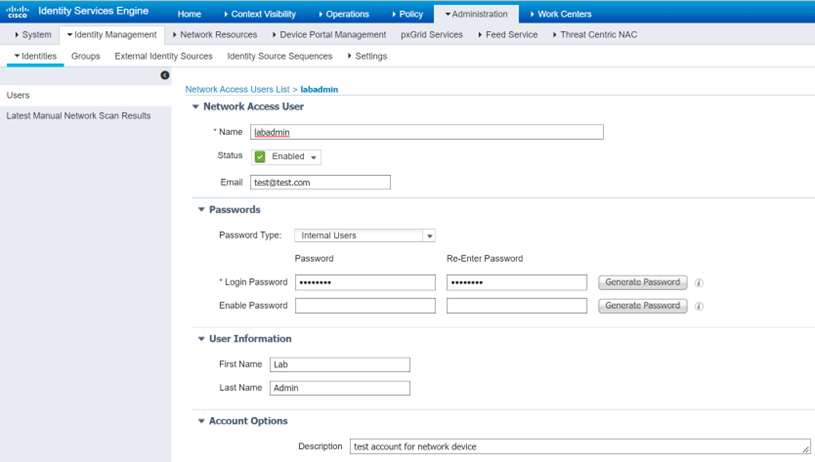
Figure 117. Detail of an Identity admin (labadmin)
Policy Sets Configuration for Dell Switch
In the policy sets tab, we created these three policies:
- Dell-SONiC-Edge-Switch-MAB (for MAB endpoints, i.e., PoE IP camera)
- Dell-SONiC-Edge-Switch-dot1x (for dot1x endpoints, i.e., Cisco IP phone and Windows PC)
- Dell-SONiC-Edge-Switch Access (for Dell switch access)
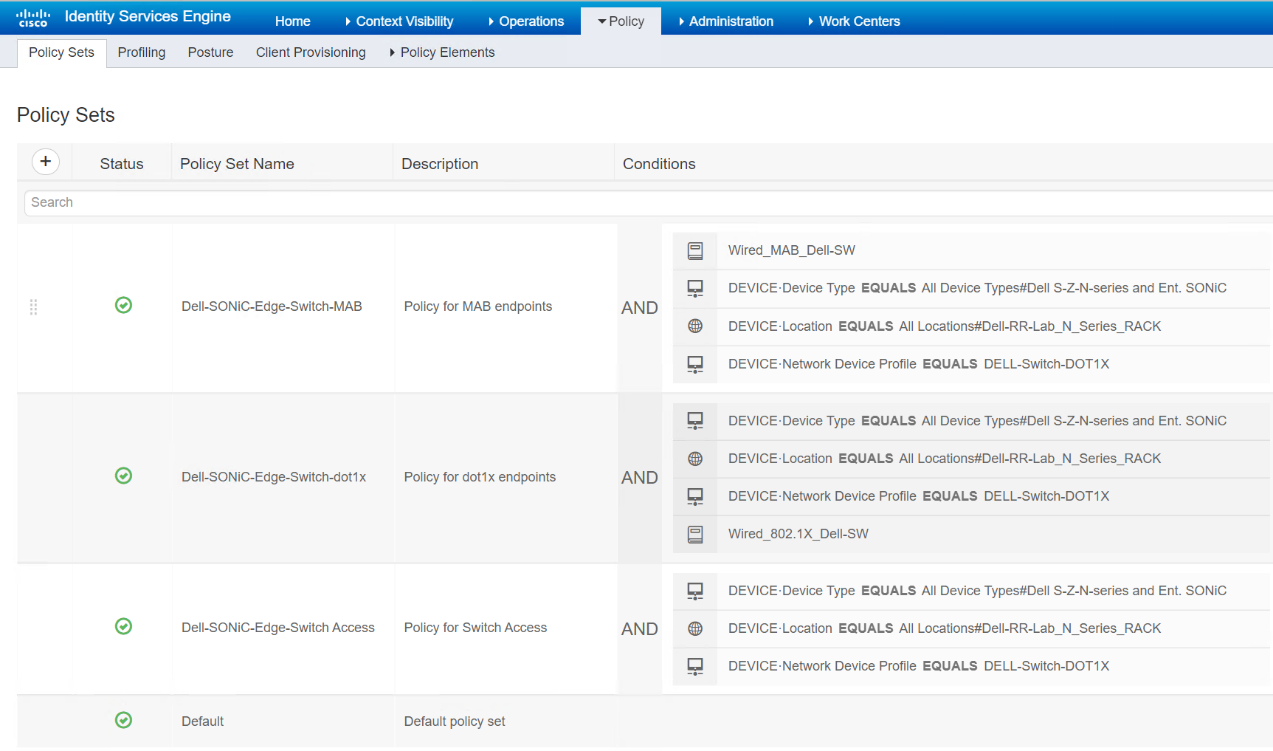 Figure 118. List of Policy Sets for the setup
Figure 118. List of Policy Sets for the setup
When a RADIUS access request comes in, ISE applies these policies sequentially in the top-down order (policy 1 first and policy 3 last). If the access request matches one of them, it will then get into that policy for authentication/authorization. If none of them match, it will go to the last one in the bottom, the default policy which on rules andconditions are defined.
Policy for Wired MAB ports in Dell Switch (Dell-SONiC-Edge-Switch-MAB)
- Click the center of the to Dell-SONiC-Edge-Switch-MAB to open the Policy Edit Studio.
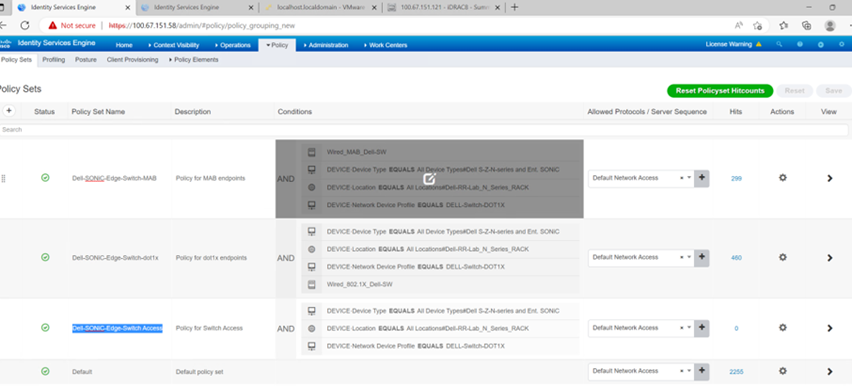
Figure 119. Place editor for Policy Sets
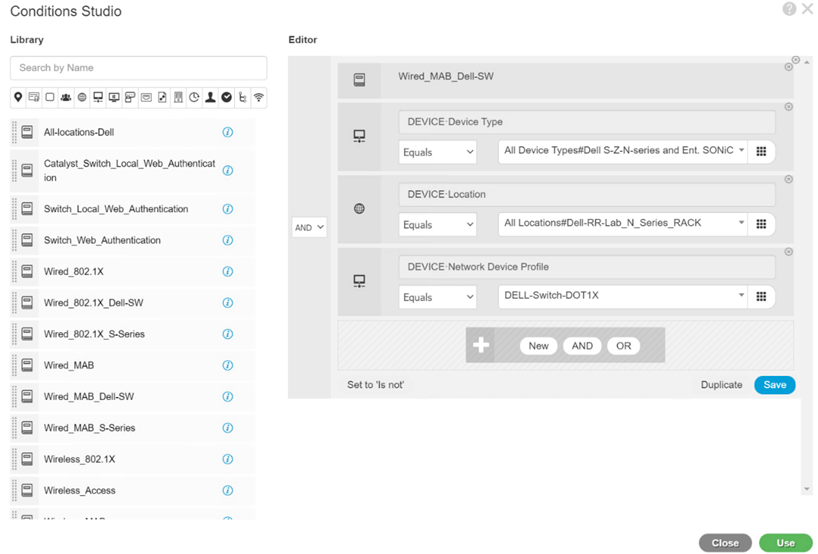
Figure 120. Dell Switch MAB Policy Set
The four conditions used in the Dell-SONiC-Edge-Switch-MAB policy include:
- One library condition, Wired_MAB_Dell-SW
- Two network device attributes, network device type and profile
- One location attribute, Device location
2. Go to Wired_MAB_Dell-SW library condition to open Duplicate and Edit.
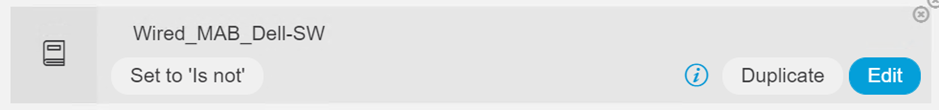
Figure 121. Edit button for Wired_MAB_Dell-SW Condition
3. Click Edit to open the condition edit page.
The edit page is the “AND” logical expression of these two RADIUS attributes, service-type and NAS-Port-Type.
 Go to the attribute areas, the Duplicate and Save buttons are popped up automatically.
Go to the attribute areas, the Duplicate and Save buttons are popped up automatically.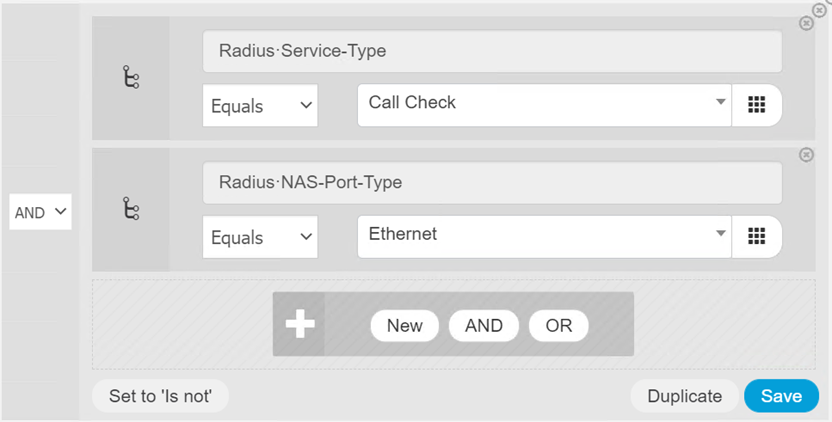
Figure 122. Save button for an attribute
The general characterization for wired MAB endpoints is RADIUS: Service-Type is Call Check “AND” RADIUS: NAS-Port-Type is Ethernet.
For Dell Switch with wired MAB ports, we added three more attributes:
- Dell Device type
- Dell Device location
- Device Profile: DELL-Switch-DOT1X
These attributes are included in the Leaf12 Network Device.. When a RADIUS access request comes to ISE, it matches to the “Leaf12” device by checking NAS IP address and shared secret, then it comes to this policy set for wired MAB port, if the access request is from a wired MAB port endpoint (port with the PoE IP camera attached), it will be applied to this policy.
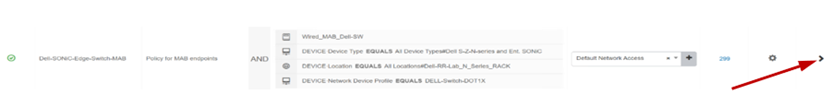
Figure 123. Detail view of Dell Switch MAB Policy Set
4. Click > on the right side to view a complete list of this Policy Set.
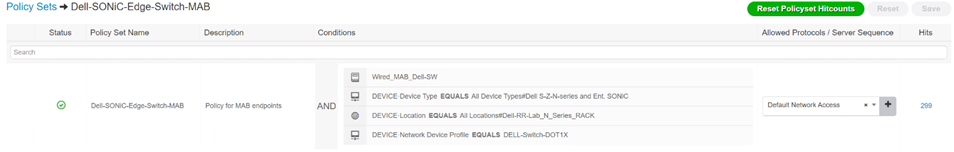
Figure 124. Dell Wired MAB Policy Set (top view)
This grants the Default Network Access as Allowed Protocols.
5. Expand the section using the caret to view the Allowed Protocols (Policy > Policy Elements > Results > Authentication > Allowed Protocols).
6. Drop down menu for Allowed Protocols
7. Click X to remove the current Allowed Protocol in the text field.
8. Expand Authentication Policy to view the policy.
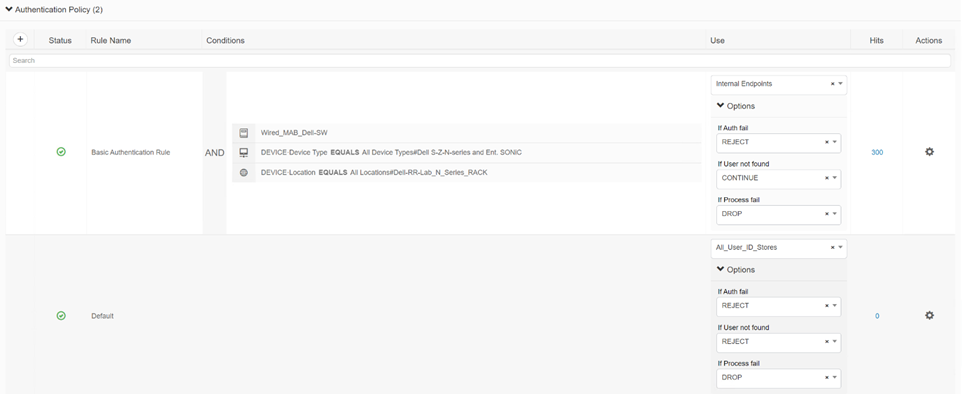
Figure 125. Expanded Authentication Policy in a Policy Set
9. Click the Condition column in the center of the page to view the Conditions Studio.
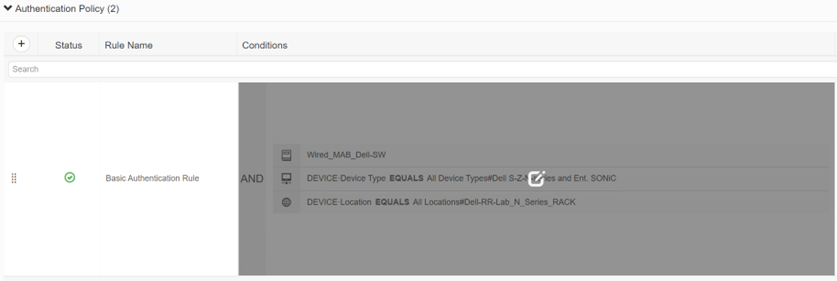
Figure 126. In place editor for authentication policy condition
If default authentication policy does not contain conditions defined to check the action items are rejected and dropped. If the authentication rule before this default rule is not met, the default rule will reject the access request.
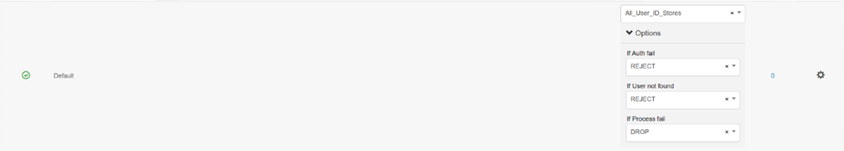
Figure 127. Default Authentication Policy
10. After completing the authentication policy, expand the authorization policy.
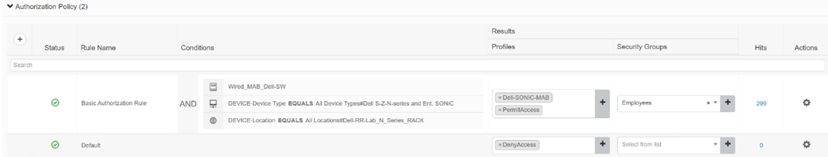
Figure 128. Expanded View of Authorization Policy in a Policy Set
The supported authorization results, MAB endpoints, are Dell-SONIC-MAB and PermitAccess. These are defined in Policy > Policy Elements> Results> Authorization > Authorization Profiles. The Security Groups are Employees and these groups are defined in Work Centers > TrustSec > Components > Security Groups.
If the authorization rule is not met, access will be denied.
Policy for Wired DOT1x endpoints in Dell Switch
Use the following steps to create and edit policy for wired dot1x endpoints.
- Open the Wired_802.1X_Dell-SW library condition UI.
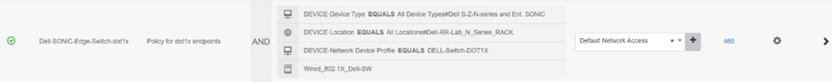
Figure 129. Dell Switch dot1x Policy Set
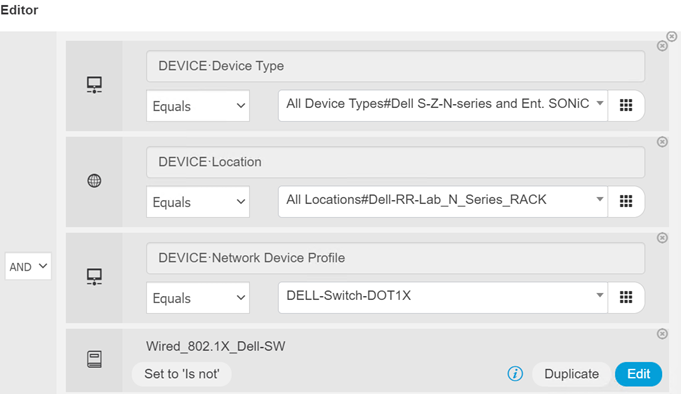 Figure 130. Detail View of Dot1X condition
Figure 130. Detail View of Dot1X condition2. Click Edit to display the detail of this condition.
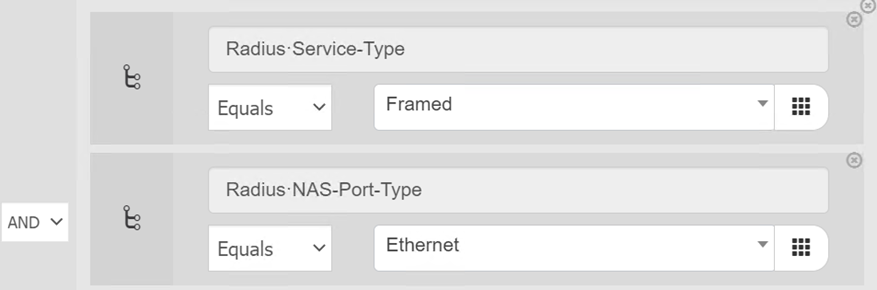
Figure 131. Detail of Wired_802.1X_Dell-SW Library Condition
Note: The RADIUS service type for 802.1x is Framed. The authentication policy is similar to Wired MAB policy.

Figure 132. Expanded Authentication Policy for dot1x policy set
3. Open the authorization policy. Apply different results to Windows and Cisco IP phone endpoints and use endpoint profiling policy to distinguish Dell and Cisco devices. The complete list of endpoint profiling policy is available at Policy > Profiling > Profiling Policies.
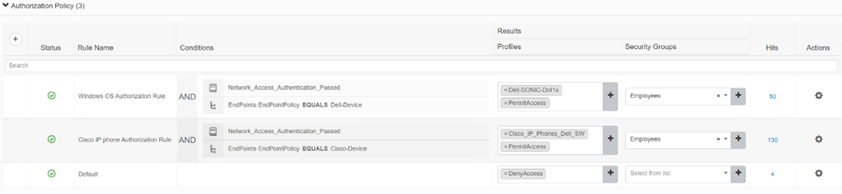
Figure 133. Expanded Authorization Policy for dot1x policy set
The main difference between the Dell-SONiC-Dot1x and Cisco_IP_Phone_Dell_SW results is the different VLANs assigned to IP phone and Windows PC.
Policy Set for Dell Switch Access
The last policy we created is “Dell-SONiC-Edge-Switch Access” to process switch access requests. We do not use any library conditions. Once the RADIUS access request reaches ISE, it matches to the “Leaf12” network device, and all the device attributes and profile are sufficient to characterize it as the network device itself. Please note that this policy must be placed after the dot1x and MAB policies as the conditions used in these policies are the superset of network access policy. The policies are checked in the top-down order.
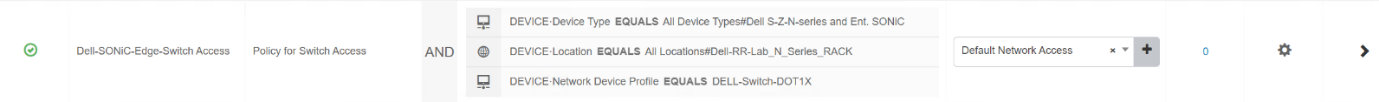
Figure 134. Dell Switch Access Policy Set
- Create a Leaf12 Network Device for our Dell SONiC Edge Bundle switch.
