Home > Networking Solutions > Enterprise/Data Center Networking Solutions > Enterprise SONiC Networking Solutions > Guides > Dell Technologies Enterprise SONiC Edge with Cisco ISE > Introduction
Introduction
-
Network administrators can use Cisco ISE to control who can access their network and ensure that authorized policy-compliant devices are being used. IT administrators can use ISE for policy enforcement, visibility, granting guest access to the network, threat containment, tool integrations, device administration, and bring-your-own-device (BYOD) management. Cisco ISE can authenticate wired, wireless, and virtual private network (VPN) users. Authorized and unauthorized users are logged in so administrators can view who and which devices are connected to their network at any time. It supports both IPv4 and IPv6 IP address schemas.
AAA protocols were initially designed as remote access control mechanisms and network service providers through modem pool and dial-in services, but they continue to be presently implemented in multiple architectures.
Remote Authentication Dial-In User Service (RADIUS) is one of the implementation platforms of AAA protocols.
A typical RADIUS deployment scenario for service providers has an intermediate element, the Network Access Server (NAS), which runs like a RADIUS client, a modem dial in user connected to NAS through modem poll or other devices, and a RADIUS server. The client sends the user’s information to the RADIUS server and acts on the response returned from it.
The RADIUS server receives the client’s request and authenticates the user based on the received data (generally against directory servers). The server returns the configuration with the necessary information so that the client can access the authenticated user service. During this Authentication and Authorization process the user’s validity and the resources it has authorized to access are verified. This procedure is complemented by the accounting process, registers the session’s relevant data that is typically used to generate rate-setting registration.
Authentication and authorization
The user requesting access makes the request by sending the necessary information and password to a NAS with a link level point to point communication (PPP). The NAS, which acts as a RADIUS client, resends the request to the RADIUS server. This request includes the end user’s information and password, encrypted with the one shared with the server (authenticator). The server confirms the authentication through any of the supported mechanisms: Password Authentication Protocol (PAP), Challenge-Handshake Authentication Protocol (CHAP), Extensible Authentication Protocol (EAP), Unix login, Lightweight Directory Access Protocol (LDAP) or others. Through these protocols, the serverobtains the relevant information related to the client.
If the RADIUS server authorizes the access, it sends an Access Accept message to the userwith a series of parameters attached that characterize the connection like the IP address and bandwidth. If the access is rejected, the Authentication/Authorization will be denied and the user will receive an Access Reject message which describes the purpose of the rejection.
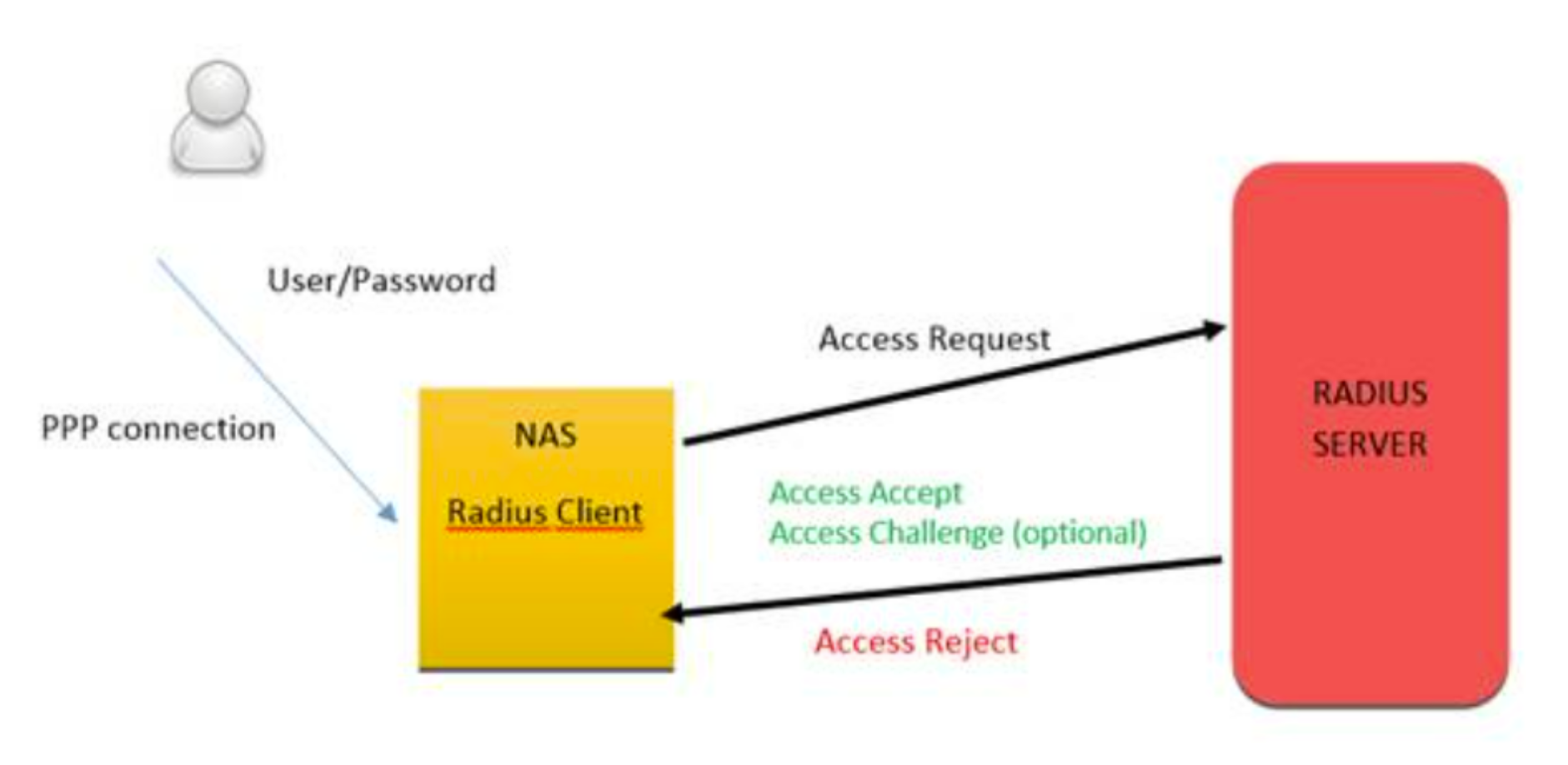
Figure 1. General RADIUS Protocol Diagram
Once the user has been authenticated and authorized the client can send an accounting request to start a session which the RADIUS server responds to, starting a connection registration with data about the start/end of the session, volume of transferred data, etc. The session ends with a request from the server or client (Accounting Stop).
RADIUS has the displays the following to control all the phases in the AAA process:
- Access-Request: Sent by a RADIUS client to request access Authentication and Authorization to a network.
- Access-Accept: Sent by the RADIUS server in response to an Access-Request message. This message notifies the client of the Authentication and Authorization which the user requested with the necessary RADIUS attributes.
- Access-Reject: Sent by the RADIUS server in response to an Access-Request message. This message informs the client that the request has been rejected.
- Access-Challenge: Sent by the RADIUS server in response to the Access-Request message. This message is sent to the client with a challenge that the client must respond to.
- Accounting-Request: Sent by a RADIUS client to specify information about the accepted connection. It can be start or stop type to start or stop the accounting.
- Accounting-Response: Sent by the RADIUS server in response to an Accounting-Request message. This message notifies about the correct reception of the request and starts the session’s process.
The Port Access Control (PAC) feature supplies validation of client and user credentials to prevent unauthorized access to a specific switch port. PAC uses the following methods for client authentication:
- 802.1X─IEEE 802.1X-2004 is an IEEE Standard for PAC that supplies an authentication mechanism to devices wishing to attach to a LAN. The standard defines Extensible Authentication Protocol Over LAN (EAPOL). The 802.1X standard describes an architectural framework in which authentication and consequent actions take place. It also establishes the requirements for a protocol between the authenticator and the supplicant and between the authenticator and the authentication server.
- MAB─An authenticator can make use of MAC Authentication Bypass (MAB) feature to authenticate simple devices like cameras or printers that do not support 802.1x. The MAB feature makes use of the device MAC address to authenticate the client.
These methods use RADIUS for client credential verification and receive the authorization attributes like VLANs, ACLs, and so on for the authenticated clients.
The PAC process includes the following components: the clients (supplicants), the port access entity authenticator (SONiC Switch) and the authentication server (RADIUS). The RADIUS server controls user profiles and access control. When a client authenticates itself initially on the network, the SONiC Leaf Switch acts as the authenticator to the clients on the network and forwards the authentication requests/messages to the RADIUS server in the network.
If the authentication succeeds, the client is placed in an authorized state and the client can send or receive traffic through the port.
RADIUS servers send a list of Authorization attributes like VLAN, ACLs, and others to be applied to the client traffic. This allows the flexibility of differential treatment to clients.
The PAC Port modes include:
- Auto Mode:This mode enforces authentication process on a port. The port state is unauthorized and blocked for traffic unless the client is authenticated.
- Force UnAuth: In this mode, the port is configured into an unauthorized state and blocks any client traffic.
- Force Auth:This mode is used to disable authentication on a port and all client traffic is allowed.
The Host modes find the number of hosts that have access and the type of host, either voice or data to allow access. The PC Host modes include:
- Single-Host:Only one data client can be authenticated on a port and the client is granted access to the port. Access is allowed only for this client.
- Multi-Host: Only one data client can be authenticated on a port. When authentication succeeds, access is granted to all clients connected to the port.
- Multi-Auth: One voice client and multiple data clients can be authenticated on a port and these clients are then granted access.
- Multi-Domain: One data client and one voice client can be authenticated on a port and these clients are then granted access.
Another part of Port Access Control is the special VLANs involved if the authentication method fails or times out. If the last authentication fails, the authentication manager can authorize the client to a special VLAN.
- UnAuth VLAN: This VLAN is used to authorize clients that fail authentication due to invalid credentials. It is used for 802.1X aware clients only. Any 802.1X aware clients failed the authentication will be redirected to this VLAN
- Guest VLAN: This VLAN is used to authorize 802.1X unaware clients. Any 802.1X unware clients will be redirected to this VLAN.
- Monitor Mode:If Monitor mode is enabled, PAC places the client in Monitor mode as applicable.
- Open VLAN: Open Authentication capability allows PAC to allow client traffic events before it authenticates
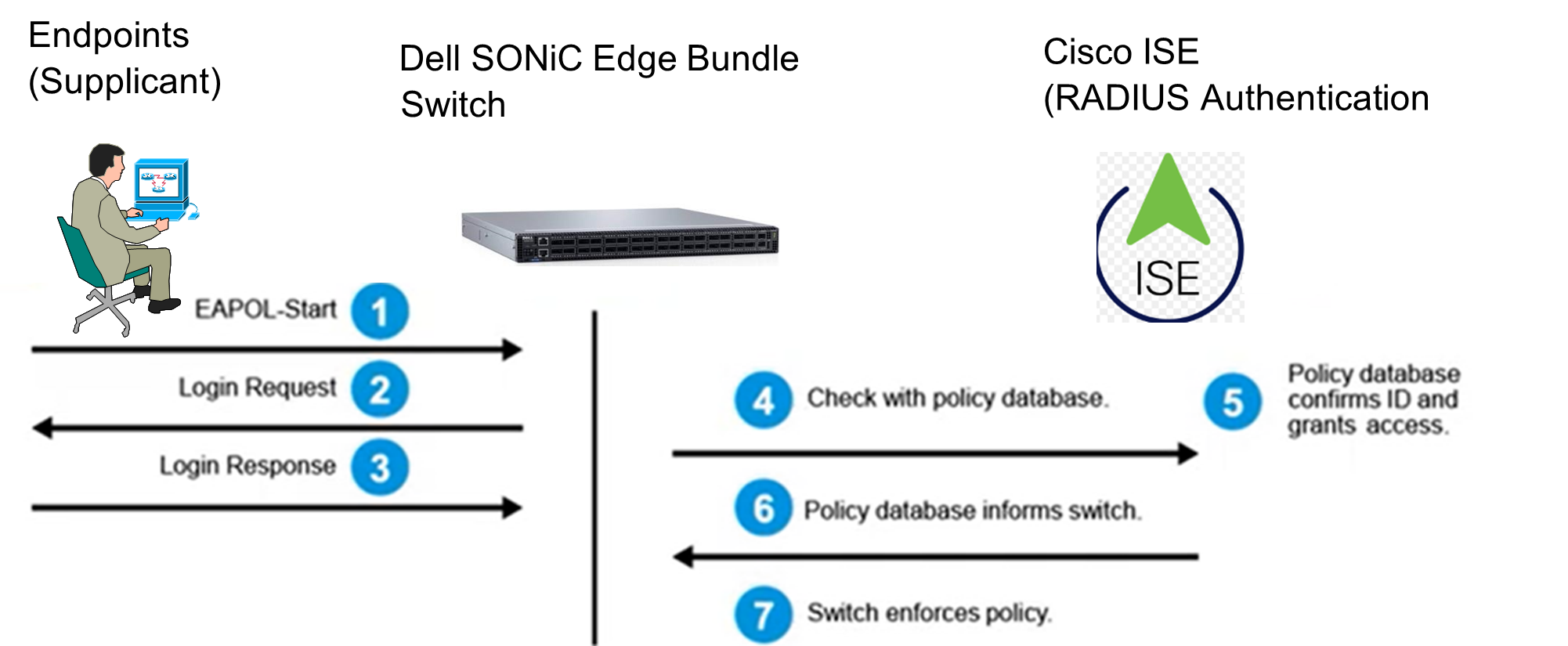 Figure 2. Dot1x EAPOL Authentication
Figure 2. Dot1x EAPOL AuthenticationEAPOL authentication involves three parties: the supplicant (user’s device), the authenticator (switch or controller), and the authentication server (RADIUS server). The authentication process can first be broken down into 4 broad categories: initialization, initiation, negotiation, and authentication.
- Initialization: the authenticator detects a supplicant seeking to authenticate to the secure network.
- Initiation: essentially a process of saying hello between the supplicant, authenticator, and authentication server.
- Negotiation: the supplicant and authentication server exchange identifying information to determine whether the user should be authenticated to the network.
- Authentication: the process is completed, opening a port for the confirmed user to connect to the 802.1X network and browse securely.
- RADIUS server (Cisco ISE) confirms ID and Grant Access: Cisco ISE can further define authorization policy to supply various authorization regulations-based endpoint properties, Windows computer, VoIP phone, or PoE IP camera, etc.
- Cisco ISE send the confirmation and granted policy back to Switch
- Switch enforces the policy based on Cisco ISE policy specification: placed endpoint to a designated VLAN, supply proper traffic engineering adjustment (QoS, ACL, etc.)
