Keep in mind that implementing security features, like encryption or proxying, can have an effect on system performance.
Home > Edge > Manufacturing Edge > Guides > Dell Validated Design for Manufacturing Edge - Design Guide with 5 Independent Software Vendors > Cybersecurity for Claroty
Cybersecurity for Claroty
-
Note: In addition to the application hardening test cases in the following sections, users should also consider OS hardening for Claroty-based deployments. Both SRA and CTD provide ClarotyOS, which is a restricted OS with built-in security and functionality, custom built to work with Claroty products. If not using ClarotyOS, Claroty provides custom hardening scripts for CTD and SRA to harden the CentOS or RHEL environment to help automate securing the host OS. More information about ClarotyOS and hardening scripts can be found in the CTD and SRA administration guides.
Note:
CTD hardening
The following settings have been validated on CTD version 4.6. Testing was done with CTD running on ClarotyOS. If users are deploying CTD software on existing RHEL or CentOS deployments, it is highly recommended to run the OS hardening scripts provided by Claroty. More information on this can be found in the Hardening section of the Claroty CTD Administration Guide.
Test 1: Load Certificate Authority signed certificates
- Ability to run openssl commands.
- Ability to sign CSRs.
Confirm that Certificate Authority (CA) signed certificates can be used by CTD Server, EMC, or CTD Sensor during operations. This adds a layer of trust for when communicating with CTD or EMC (for example, when accessing the HTTPS interface). The end user can be assured that the certificate was signed by a trusted party. - Create a CSR and key pair using the openssl command. Example command:
openssl req -newkey rsa:2048 -nodes -keyout <key-name>.key -out <csr-name>.csr - Sign the CSR with a trusted CA and obtain the signed certificate.
- Transfer the signed certificate and key file to a host with a web browser that can access the CTD component.
- Log in to CTD/EMC and browse to Settings > Management > OS Configuration. Note: For the CTD Sensor, browse to https:// <sensor-IP/FQDN>/platform to get to the Manage page.
- Select the option to Upload certificate and key.
- Click on Choose Certificate and select the signed certificate.
- Click Choose key and select the key associated with the signed certificate.
- Click Upload Certificates.
To verify, perform the following steps: - Refresh the web page.
- View the contents of the certificate being presented by CTD, EMC, and CTD Sensor.
- Validate that the information is correct, and that the issuer is the correct CA.
Test 2: Integrate with Active Directory over LDAPS
- The CTD/EMC under testing can resolve the FQDN of the AD server (if AD server is using FQDN as CN).
- AD is deployed and has users and groups configured and available for testing. The users have minimum attributes such as first name, last name, username, and email address.
Validate that CTD or EMC can integrate with an Active Directory (AD) server over Lightweight Directory Access Protocol (LDAP) using Transport Layer Security (TLS). This enables central management of users and protects the confidentiality of the authentication data when using LDAPS (LDAP over TLS) instead of regular LDAP. - Log in to the CTD or EMC and navigate to Settings > User Management > Domains.
- Click the + Create New button.
- Fill out the settings for the target AD server. Use the settings below as an example:
- PORT: 636 (for LDAPS)
- DOMAIN NAME: example.com
- SERVER: FQDN/IP Address
- BASE DN FOR USER LOOKUP: cn=users,dc=example,dc=com Note: A Distinguished Name (DN) is a string to help search for objects. Reference for more information: https://docs.microsoft.com/en-us/previous-versions/windows/desktop/ldap/distinguished-names
- BASE DN FOR GROUP LOOKUP: cn=users,dc=example,dc=com
- BIND DN: DN string for user for AD user with AD search privileges (ex: cn=adsearchuser,cn=users,dc=example,dc=com)
- PASSWORD: Password of above user
- Leave CONNECT USING SSL, and VERIFY SSL CERTIFICATE enabled.
- Click on Choose File under SSL CA CERTIFICATE and select the CA certificate of the AD server. Note: The uploaded CA Certificate should be in ASCII format.
- (Optional) Leave USER E-MAIL ADDRESS FROM ACTIVE DIRECTORY to On.
Figure 171. Example of CTD configuration settings to connect to AD over LDAPS 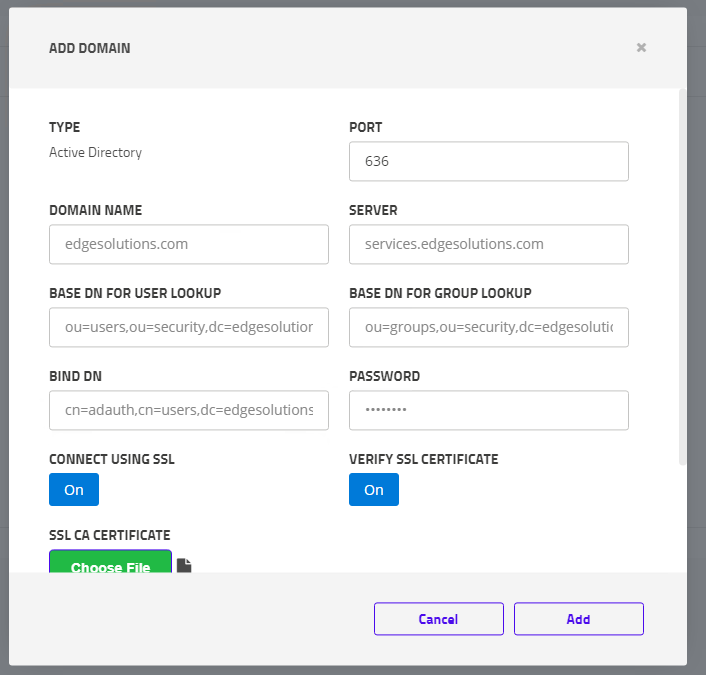
- Click Add.
- Confirm that the entry is displayed in the RESULTS table on the Domains page.
- Go to Settings > User Management > Groups and click the + Create New button.
- Use the following settings for guidance and as an example:
- Group Name: Unique group name (does not have to be the same as the AD group)
Figure 172. Associating AD group with CTD group 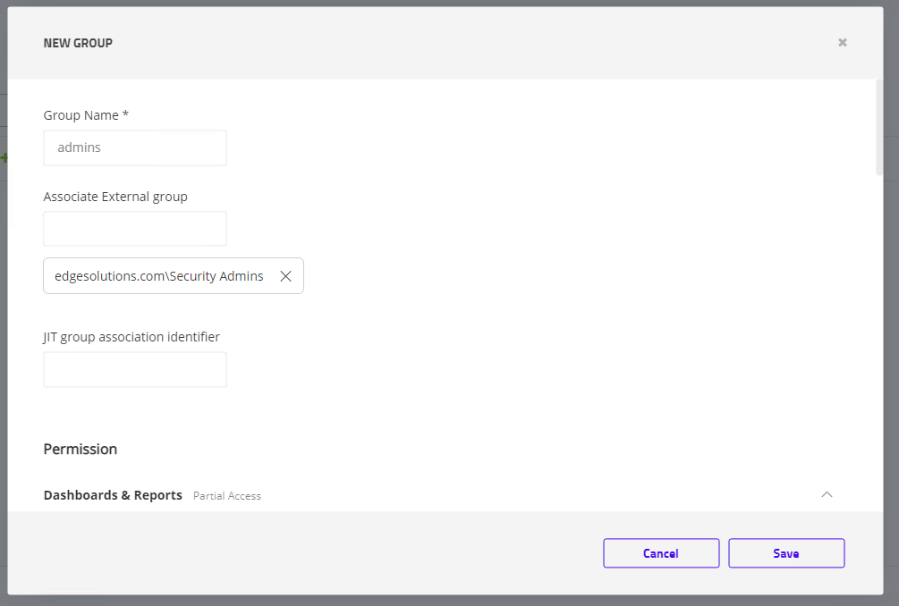
- Associate External Group: Choose AD group - when selecting this text box, a list of the AD groups appears below. Not all groups appear. Begin typing the AD group to see more options.
- JIT group association identifier: Leave blank for this test.
- Select custom permission settings. Can leave as default.
- Leave all other settings default for this test.
- Group Name: Unique group name (does not have to be the same as the AD group)
- Click Save.
To verify, perform the following steps: - Log out of the CTD/EMC.
- Log in with the user created in the configuration steps using the AD username and password.
- Validate the user can log in.
- Log in with a user who can view system settings and go to Settings > User and Management > Users.
- Confirm that the AD user was automatically added and that they are part of the GROUP that was created in this test case.
Test 3: Configure password settings
There is at least one user created on CTD/EMC that can be used for testing. Confirm that CTD/EMC allow users to configure robust password settings for locally created user accounts. Defining stronger password settings helps to reduce the risk of compromised accounts. - Log in to CTD/EMC and navigate to Settings > User Management > Security & Authentication > General Settings.
- Set/confirm the following settings under Password:
- Minimum length: 10
- Lowercase (a-Z): Yes
- Uppercase (A-Z): Yes
- Digits (0-9): Yes
- Non Alphanumeric (!,@, #): Yes
- Doesn't contain username: Yes
- Prohibit password re-use: Yes
- Click Apply.
To verify, perform the following steps: - Log out and log back in with the test user account.
- Click the username at the top-right side of the menu and select Change Password.
- Enter the CURRENT PASSWORD of the test user.
- Enter the following passwords, click Save, and confirm that they are denied:
- Password: P@s5word Output: Password must contain at least 10 characters.
- Password: P@S5WORD123 Output: Password must contain at least one lowercase letter.
- Password: p@s5word123 Output: Password must contain at least one uppercase letter.
- Password: P@ssworddd Output: Password must contain at least one digit.
- Password: Password123 Output: Password must contain non-alphanumeric letter.
- Password: <username>P@s5worddd Output: Password must not contain the username.
- Password: <current password> Output: The new password cannot be the same as the old one.
- Enter in a password that satisfies the requirement (example: P@s5worddd) and verify that it is successfully saved.
Note: Spaces count as alphanumeric characters, so be careful when entering the test strings.
Test 4: Control excessive authentication attempts
There is at least one user created on CTD/EMC that can be used for testing. Confirm the ability to limit the number of log in attempts to a user account on CTD/EMC. This is critical in protecting against attacks that attempt to guess legitimate user account credentials. - Log in to CTD/EMC and go to Settings > User Management > Security & Authentication > General Settings.
- Under the User setting change Disable User After Unsuccessful Login Attempts to the value of 3.
- Click Apply and then Yes.
To verify, perform the following steps: - Log out of the CTD/EMC instance.
- Attempt three failed logins with a test user.
- On the fourth attempt, enter the correct password for the test user.
- Confirm the system outputs the following message, "User is disabled, contact system administrator."
- Log back in to CTD/EMC as an admin user.
- Navigate to Settings > User Management > Users.
- Confirm that the test user's STATUS is set to Disabled.
Test 5: Configure RBAC settings
- There is at least one user created on CTD/EMC that can be used for testing.
- CTD has been populated with multiple assets and at least two different vendor types.
Confirm that CTD can define groups with specified permissions. Validate that the configured permissions are working correctly. Note that this test does not validate every set of permission settings but rather tests the overall functionality. - Log in to CTD/EMC and navigate to Settings > User Management > Groups.
- Click the + Create New button.
- Fill out the settings per the example below:
- Group Name: Unique group name (example: Read-only)
- Dashboards & Reports: View
- Visibility: View
- Threat Detection: View
- Risks and Vulnerabilities: View
- Investigation: View
- Settings: No Access
- Users: Select test user
- Click Save.
To verify, perform the following steps: - Log out of the CTD/EMC.
- Log in with the test user added to the group created in this test procedure.
- Confirm there is no Settings menu displayed.
- Go to Threat Detection > Alerts.
- Confirm the user is missing capabilities to make changes, such as deletion capability.
- Go to Visibility > Assets.
- Observe the assets and choose a Vendor, such as Dell.
- Click an asset with the chosen Vendor
- Scroll down to TIMELINE, enter a comment in the box and submit it. Confirm that permission is denied.
- Log out of the test user and log back in with an admin user.
- Go to Settings > User Management > Groups.
- Click Edit to the right of the test group.
- Edit the following settings:
- Visibility: Admin
- Threat Detection: Admin
- Settings: Admin
- Resource Access > Add Permission: Asset, Vendor, <Vendor name (example: Dell)>.
- Click Save.
- Log out and log back in with the test user.
- Confirm that the Settings option is present, and user can navigate there. There should be no Data Sources option available on the left-side menu.
- Click Back to Main Menu > Visibility > Assets.
- Click an asset with the chosen Vendor.
- Scroll down to TIMELINE, enter a comment in the box and submit it. Confirm that the comment is accepted.
- Go back to the list of assets. Click on the asset with a different Vendor value.
- Scroll down to TIMELINE, enter a comment in the box and submit it. Confirm that permission is denied.
- Go to Threat Detection > Alerts.
- Confirm the user now has capabilities such as Accept and Archive (icons above the RESULTS table).
Test 6: View applications logs
- There is a test user with permissions to be able to view logs/events and modify system settings.
- There is another user that can be used for testing purposes.
Validate the capability of CTD/EMC to audit/log actions taken on the system such as successful or failed login attempts or system configuration changes. This is critical in keeping users accountable for their actions and for any potential investigations into suspicious activity. - Browse to the CTD/EMC logon page.
- Attempt a failed log in with the test user 1.
- Successfully log in with the test user 1.
- Log out and log in with an admin account.
- Navigate to Settings > User Management > Users.
- Click the + Create New button.
- Fill out the information to create a test user 2 and click Add.
To verify, perform the following steps: - Log in to the CTD/EMC's ClarotyOS to get to the command-line interface.
- Enter the command:
ctd logs search-all <test user 1 username> - Confirm that there are both log messages for failed and successful authentication attempts.
- Enter the command:
ctd logs search-all<test user 2 username> - Confirm there is a log file for the creation of user 2. For example, Adding user <test user 2 username, first_name…>
Test 7: Integrate with centralized logging server
- Splunk server deployed and reachable over the network from CTD component.
- Splunk is configured with a Syslog input as an endpoint to ingest Syslog messages over UDP port 514.
Validate the capability for CTD/EMC to integrate with a central logging server using Syslog to be able to aggregate logs and to help secure them. Splunk was used as the Syslog server endpoint and SIEM for this test. - Log in to CTD/EMC and go to Settings > Integrations > SIEM Syslog.
- Click the + Create New button.
- Uncheck the LOCAL box.
- Enter or select the following settings:
- VENDOR NAME: Splunk
- MESSAGE CONTENT: Health Monitoring
- MESSAGE FORMAT: RFC5424
- Interval: 1 Hour
- SERVER: <IP/FQDN of syslog server>
- PORT: 514
- PROTOCOL: UDP
- SYSTEM URL: Leave default
Figure 173. Example of configuring a Syslog server in CTD 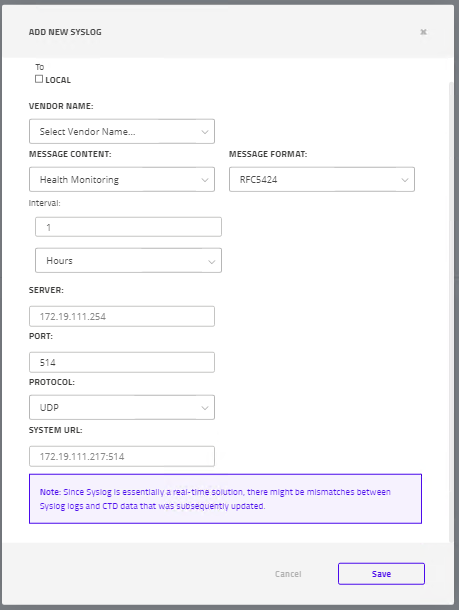
- Click Save.
To verify, perform the following steps: - Click Send a test message on the new entry for the Syslog server on the SIEM Syslog screen.
- Confirm that the screen outputs Test Message Sent.
- Go to the Syslog server and look for the source IP of the CTD/EMC server.
- Confirm that there are test messages delivered to the Syslog/SIEM server from the CTD/EMC source IP/FQDN.
Test 8: Connect to NTP server
NTP server is deployed on the network and reachable from the CTD component. Part of an effective audit/logging system is to have time synchronized across devices on the network. This helps when correlating events across a range of device logs. Validate that CTD/EMC can successfully connect to an NTP server. - Log in and go to Settings > Management > OS Configuration > Manage. Note: For the CTD Sensor, browse to https:// <sensor-IP/FQDN>/platform to get to the Manage page.
- Under the System Time, select NTP server hostname and enter in the IP address or FQDN of the target NTP server.
To verify, perform the following steps: - Click Test NTP.
- Validate a Success message appears.
- Click Update and confirm that Current Server Time is accurate.
- Log in to the host OS (example: ClarotyOS) and run a command to get the system time. For example, on ClarotyOS, type and enter:
time show local. - Confirm operating system time is accurate.
Test 9: Upgrade CTD components
Validate upgrading the CTD/EMC/Sensor hosting ClarotyOS as it is important to keep up to date on any security patches or to update or fix functionality. This procedure uses the web user interface. To use the CLI, or when using RHEL instead of ClarotyOS, reference official Claroty documentation. Note: In a connected scenario, when updating or upgrading CTD Server or CTD Sensor, the EMC must be the first to be updated or upgraded to the newest version before updating or upgrading connected CTD sites. For instance, EMC must be version 4.6 before CTD can be upgraded to version 4.6.
- Log in to EMC or CTD and go to Settings > Management > OS Configuration > Upgrade. Note: For the CTD Sensor, go to https:// <sensor-IP>/platform to get to the OS Configuration > Upgrade settings.
- Click the Choose Bundle button and select the .bni upgrade file.
- Click Upload file. Wait for the upload to complete (this may take several minutes).
- (Optional) Select to save PCAPS (CTD) and create a local backup before upgrading.
- Click Upgrade. Output is shown on the log screen as the system performs the upgrade. The system also requires a restart. Note: The system may require to re-authenticate. If that occurs, navigate back to the Upgrade page to monitor the upgrade logs.
- Confirm the Upgrade page displays Bundle execution finished successfully.
To verify, perform the following steps: - Log back into the EMC or CTD.
- Click the Username on the upper-right of the user interface.
- Validate that the version number under CTD Version reflects the correct version.
Test 10: Manually updating EMC
Updating the Enterprise Management Console (EMC) is important to keep up to date on any security patches or to update or fix functionality. This procedure uses the web user interface. Note: Updates can only be applied to the CTD if EMC has been upgraded to the appropriate version (example: from 4.5 to 4.6). After that, both CTD and EMC can be updated (example: from 4.6.0 to 4.6.0 Update 1).
- Log in to EMC and go to Settings > Management > Site Management.
- To the right of Update EMC by manually uploading and update file, select the update icon.
- Click UPLOAD UPDATE FILE and select the update file.
- Click Update EMC.
- The user is taken to a new page. The system may restart or may be taken back to the Site Management page.
To verify, perform the following steps: - If necessary, log back into the EMC and go to Settings > Management > Site Management.
- Under Update EMC by manually updating an update file, validate that the version listed is reflects the version that was uploaded.
Upgrade and update EMC first, prior to CTD, in a connected scenario.
Test 11: Upgrade/update CTD from EMC
EMC has already been updated or upgraded to the correct version. This update or upgrade has not yet been applied to the test CTD instance. Validate the capability of EMC to automatically update connected CTD components. This scenario is important to help automate the upgrade and update process in larger environments, and it provides an easier way to ensure that all connected CTD instances are at the correct version. - Log in to the EMC and go to Settings > Management > Site Management.
- Click the checkbox next to the CTDs to upgrade and click the upgrade button.
- In the UPGRADE SITES window, verify the correct Version to download is displayed (it should match what EMC has been upgraded to).
- (Optional) Leave setting enabled to Save system backup.
- Click the Download & Install button.
- Back on the Site Management page, the UPGRADE STATUS for the CTDs being upgraded should list Downloading and will change to different states such as Installing and Migrating.
- Restart the CTD.
- Confirm that upgrade is completed. The status should indicate the date of the last upgrade.
- Back on the Site Management page, select the CTDs to update and click the update button under ACTIONS.
- Click the Update site button. Note: Upgrading and updating the CTD site or sites should kick off automatic updates to the CTD connected CTD Sensors.
To verify, perform the following steps: - Log in to the CTD that was upgraded from the EMC.
- Click the username on the upper-right of the screen.
- Confirm that the correct version is displayed under CTD Version.
SRA hardening
The following settings have been validated on SRA version 3.5. Testing was done with SRA running on CentOS 7.9. It is highly recommended to run the OS hardening scripts provided by Claroty. More information on this can be found in the Appendix: Hardening section of the Claroty SRA Installation Guide.
Test 1: Load CA signed certificates
- Access to a system that can run openssl commands. Test 2: Integrate with AD over LDAPS
- Ability to get certificates signed by a CA.
Confirm that CA signed certificates can be used by SRA during operations. Using a signed certificates adds trust between hosts during communications such as accessing the SRA web interface or when connecting to other SRA components. - SSH to the SRA host and create a new temporary directory to store the certificate files:
mkdir -p /tmp/ssl - Generate a key pair:
openssl genrsa -out ssl.key 4096 - Create a certificate request (CSR) with a SAN as the CN:
openssl req -new -key ssl.key -out ssl.csr -sha256 -days 1095 -reqexts
SAN -config <(cat /etc/pki/tls/openssl.cnf; printf
"[SAN]\nsubjectAltName=DNS:Subject Alternative Name")Note: When filling out the CSR prompts, it is advised to specify the Common Name (CN) value as the FQDN/hostname of the system hosting SRA.
Note: The openssl request command adds a SAN attribute to the CSR, this should specify the DNS name of the SRA host (FQDN/hostname).
- After entering the values, transfer the ssl.csr file to the organization's CA to get it signed.
- Return the signed certificate to the SRA host's /tmp/ssl directory.
- Replace the existing ssl.crt and ssl.key files in the /etc/icsra/workers/web/ directory:
cp /tmp/ssl/ssl.crt /tmp/ssl/ssl.key /etc/icsra/workers/web/ - Restart the SRA service:
Systemctl restart icsra
Note: Remove the temporary key and certificate after completing this procedure.To verify, perform the following steps:
- Browse to the SRA SAC web interface.
- Using the browser settings, view the certificate presented by the SRA SAC.
- Confirm that the information is correct, and that the issuer is the correct CA.
Test 2: Integrate with AD over LDAPS
- The SRA host can resolve the FQDN of the AD server (if AD server is using FQDN as CN).
- AD is deployed and has users and groups configured and available for testing. The users have minimum attributes such as first name, last name, username, and email address.
Validate that SRA can integrate with an Active Directory server over LDAP using TLS. This enables central management of users and protects the confidentiality of the authentication data when using LDAPS instead of regular LDAP. - Log in to the SRA SAC and navigate to System Management> Domains.
- Click Add domain.
- Fill out the settings according to the target AD server:
- Type: Active Directory
- Domain name: <Org. domain name. Ex: example.com>
- Server address: <FQDN of AD server. Ex: ad.example.com>
- Bind DN: <DN string for user for AD user with AD search privileges (ex: cn=adsearchuser,cn=users,dc=example,dc=com)>
- Password: <Password of Bind DN user>
- Base DN for user lookup: <DN query string for users to integrate with SRA. Ex: ou=users,ou=engineering,dc=example,dc=com>
- Base DN for group lookup: <DN query string for groups to integrate with SRA. Ex: ou=groups,ou=engineering,dc=example,dc=com >
- Connect using SSL: On
- Verify SSL certificate: On
- SSL CA Certificate: <Browse for org. CA cert>
- Port: 636 (default)
Figure 174. Example of LDAPS configuration in SRA 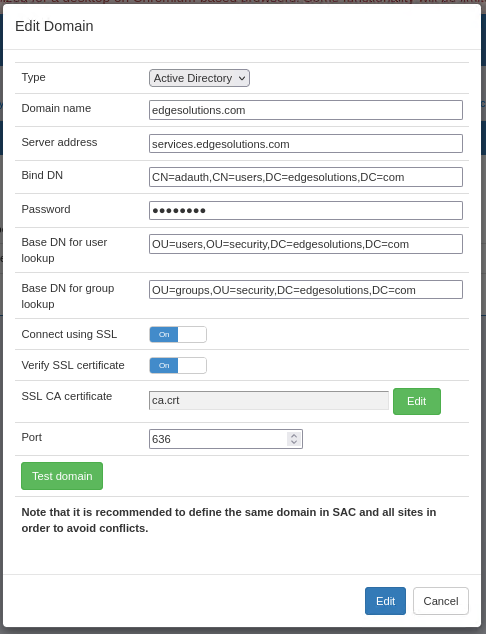
- Click Test domain and confirm Success is displayed.
- Click Add.
- Go to User Management > Groups.
- Click Active Directory associations.
- In the Edit Group External Associations appear, under Search External Groups, add one of the AD groups listed for the AD domain.
- Confirm the AD group changed to Added, and then click Close.
To verify, perform the following steps: - Log out of SRA.
- Log in with an AD user that is part of the group added in the Configuration steps (Example: user@example.com).
- Confirm that the user successfully logs in.
- Navigate to User Management and confirm that the logged on user is listed with Type: Active Directory.
Test 3: Integrate with SSO
- There is an identity provider configured to use SAML 2.0.
- The identity provider is configured with users and groups to test with.
Verify the ability of SRA to integrate with a Single Sign-On (SSO) solution using the SAML 2.0 protocol. Using SSO enables more effective management of credentials on the network and reduces issues such as account sprawl. This also allows users to not have to enter account credentials after prior successful authentication with the identity provider (IdP). This specific test was validated using Active Directory Federation Services (AD FS) as the IdP. For guidance on how to configure AD FS to integrate with SRA over SAML 2.0, see the Configure AD FS to support SSO over SAML 2.0 section.
- Log in to SRA and go to System Management > Security and scroll down to SAML Authentication.
- Next to SAML auth policy, select the drop-down and choose Enable for web access.
- Fill out the SAML settings according to the target AD FS server:
- ACS URL: https://<FQDN of SRA>
- Entity ID: https://<FQDN of SRA> Note: The following examples use AD FS as the IdP. Modify accordingly if using a different solution.
- Single Sign-On URL: Ex: https://<ADFS-FQDN>/adfs/ls
- Entity ID: https://<ADFS-FQDN>/adfs/services/trust
- Certificate: Paste in the AD FS certificate.
- Under SAML Authorization turn on the setting: Enable Just-In-Time (JIT) provisioning.
- Under SAML JIT Parameter Mapping, add the SAML parameters from AD FS for SRA to use to create users if they do not exist. Fill this out for all three parameters. Note: It may be helpful to look at the AD FS configuration to see which attributes are being sent. There are also tools that can debug SAML attributes being sent across to help identify the attribute statement being used. If using AD FS, users can view the outgoing claim rules (which can be mapped to the SMAL JIT Parameter Mapping values in SRA). Go to AD FS Management > Relying Party Trusts and right-click the Relying Party to edit the claim issuance policy. Select the appropriate claim issuance policy, then click View Rule Language.
- Click Apply SAML settings.
- Go to User Management > Groups.
- Edit an existing group or add a new group.
- For JIT group association identifier, enter in the group identifier to associate to from the IdP. For example, if IdP is using AD groups, and then put the name of the AD group to associate to the SRA group.
Figure 175. Configuration example for SRA SAML Authentication for SSO with AD FS 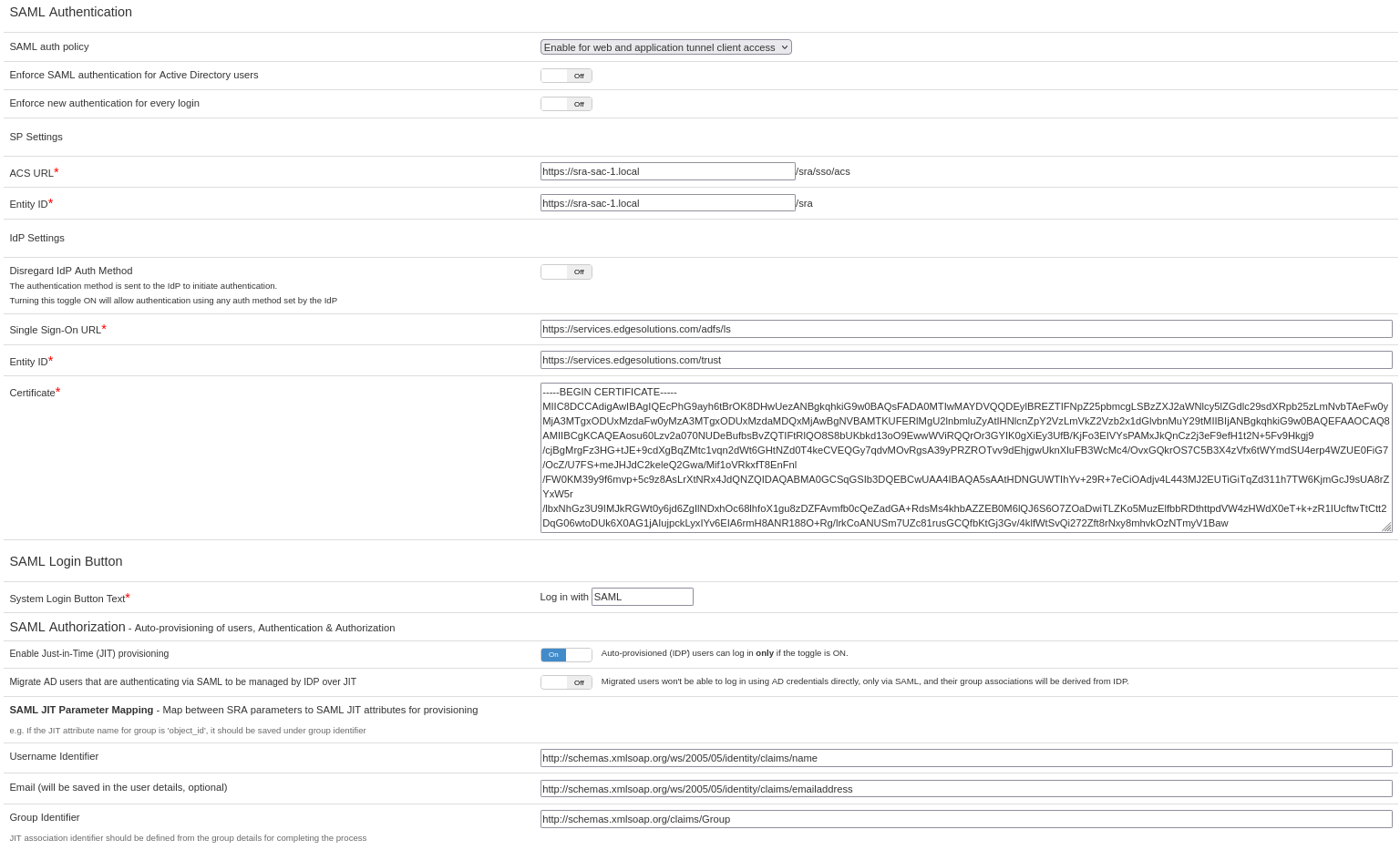
To verify, perform the following steps: - Log out of SRA.
- Click the Login with SSO button.
- Verify that the user is automatically logged in. Note: This step assumes the user has not been previously created within SRA.
- Once logged in, go to User Management.
- Confirm that the SSO user is present, and their Type is listed as Identity Provider.
Helpful tip: Information on the IdP can be found in the XML metadata file. For example, this metadata file can be obtained from AD FS by browsing to https://<FQDN>/federationmetadata/2007-06/federationmetadata.xml.
Test 4: Configure password settings
Confirm that SRA can configure robust password settings for locally created user accounts. Defining stronger password settings helps to reduce the risk of compromised accounts. - Log in to SRA and go to User Management.
- Click New user to create a temporary test user. Enter the details for a test user, at least adding a username and password.
- Navigate to System Management > Security.
- Set or confirm the following settings under Password Policy:
- Allowed failed log in attempts: 3
- Disable inactive users: 1
- Force change password in first login: On
- Minimum Length: 10
- Leave all the other settings as default.
- Click Apply Password Policy settings.
To verify, perform the following steps: - Log out and log back in as the test user account.
- Confirm that the user is forced to create a new password.
- Enter the following passwords, click Login, and confirm they are denied with the following messages:
- Password: <Current password>: "The new password cannot be the same as the old password."
- Password: P@s5word Output: "Your password does not meet the administratively configured strength policy: Not long enough"
- Password: P@S5WORD123 Output: "Your password does not meet the administratively configured strength policy: Does not contain any lower case letters."
- Password: p@s5word123 Output: "Your password does not meet the administratively configured strength policy: Does notcontain any upper case letters."
- Password: P@ssworddd Output: "Your password does not meet the administratively configured strength policy: Does notcontain any digits."
- Password: Password123 Output: "Your password does not meet the administratively configured strength policy: Does notcontain any symbols."
- Password: <username>P@s5worddd Output: "Your password does not meet the administratively configured strength policy: Contains your username."
- Enter in a password that satisfies the requirement (example: P@s5worddd) and verify that is successfully saved.
- Log out and attempt three failed logins.
- Log in with a different user, such as admin, and go to User Management.
- Confirm that the test user is Disabled.
Test 5: Configure multifactor authentication
- User has an OTP/Token authenticator app such as FreeOTP.
- SRA is configured with the correct time.
Validate the capability of SRA to be able to enable two factor authentication for user logins. This test uses FreeOTP as the token application, but there are other options available to the user as well. This test also uses only one account type, but it is recommended to implement two factor authentication on all logins if possible. CAUTION: Be careful not to be locked out of the local user account. The test setting forces two factor authentication for all local accounts.- Log in to the SRA SAC and go to System Management > Security.
- Scroll down to TOTP Authentication and set the TOTP authentication policy to Enable only for local users.
- Click Apply TOTP settings.
To verify, perform the following steps: - Log out of SRA and log back in with a local user.
- Confirm that the user is presented with a screen for two-factor authentication.
- Using FreeOTP, open the application and open the barcode scanner.
- On the SRA screen, press Show me the barcode.
- Scan the code on the FreeOTP app. Confirm that a new token is added to the home screen.
- Click on the new tile and enter in the token on the SRA screen.
- Confirm that the user successfully logs in.
Test 6: App Tunnel secure authentication
- There is a host with the App Tunnel client.
- SAML has been enabled. See Test 3: Integrate with SSO.
- AD/LDAP integration has been enabled. See Test 2: Integrate with AD over LDAPS.
- TOTP has been enabled.
This test procedure validates that the SRA App Tunnel application works with SAML, AD, and two factor authentication functionality. The prerequisites must be met to carry out this test. - Carry out the prerequisites and open the App Tunnel on the test host.
- Ensure that the Application Tunnel Config includes the groups that are tied to the AD and SSO (SAML) users.
To verify, perform the following steps: - Local user login with two factor authentication:
- On the App Tunnel, click Edit within the authentication box.
- Select Username and Password.
- Enter in the local user credentials and click the connect button.
- Verify that the 2-Step Verification prompt appears.
- Use the OTP/Token application to enter in the token and press CONTINUE.
- Confirm that the application is Connected.
- LDAP login:
- On the App Tunnel, click Edit within the authentication box.
- Select Username and Password.
- Enter in credentials for an AD (LDAP) user and click the connect button.
- SAML SSO login:
- One the App Tunnel, click Edit with the authentication box.
- Click SAML.
- Click the connect button.
- Confirm that either user is logged in or a prompt for the SSO login appears.
Test 7: Configure RBAC settings
Confirm that SRA can define groups with specified permissions. Validate that the configured permissions are working correctly. Note that this test does not validate every set of permission settings but rather tests the overall functionality. - Log in to SRA SAC and go to User Management and click New user.
- Follow the steps below to create each type of user. Repeat step 1 after creating each type of user to create another user.
- Configure client user:
- Username: client
- Password:<password>
- Role: Client
- Configure operator user:
- Username: operator
- Password:<password>
- Role: Operator
- Site (file management):<Site>
- Configure administrator user:
- Username: administrator
- Password: <password>
- Role: Administrator
- SFTP enabled: on
- Navigate to User Management > Groups.
- Click New group, and create the following groups:
- Permissions group:
- Group name: permissions
- Group type: Permissions
- Operators group:
- Group name: operators
- Group type: Operators management
- Site management for: <None/Empty>
- After creating the groups, click Members for the permissions group.
- Click Add for the client user.
- Click the permissions group name.
- Allow access to one session and no access to another. Click OK.
- Click Membership for the operator group.
- Click Add for the operator user.
- Go to File Management and click Upload File.
- Click Browse and select a file (create a blank .txt file) named test.txt.
- Click Sync for the listed Site.
- Under Share this file with others, select the group operators and Permission Read.
- Click Add and then Upload.
To verify, perform the following steps: - Verify correct permissions for each of the following users and groups:
- Client user and group:
- Log in with user: client
- Confirm that the Dashboard is only present and only the servers with Allowed access appear.
- Click Connect next to the available server.
- Confirm that the session successfully connects.
- Operator user and group:
- Log in with user: operator
- Confirm that the following links are available: Dashboard, Sessions, Server Management, File Management.
- Open a new tab and log in with user operator to the SRA site.
- Confirm user can log in and has the same links available.
- Go to Files and confirm test.txt file is present.
- Administrator user and group:
- Log in with user: administrator
- Confirm the administrator can view all the links and servers on the dashboard.
- Go to File Management and confirm that the file uploaded earlier is present.
- Log in to the site with user administrator and repeat steps b and c.
Test 8: View application logs
There is an admin user available for testing. Validate the capability of CTD/EMC to audit and log actions taken on the system such as successful or failed login attempts or system configuration changes. This is critical in keeping users accountable for their actions and for any potential investigations into suspicious activity. - Browse to the SRA log in page.
- Attempt a failed logon with an existing user.
- Log out and log in with an admin account.
- Go to User Management.
- Click New user.
- Fill out the information to create a new test user and click OK.
To verify, perform the following steps: - Within SRA, navigate to Activities.
- Click Activities.
- Confirm presence of the following logs:
- User:<username from Configure steps step 2>, Action: Log in to SRA failed
- User: <admin user>, Action: Create user
Test 9: Integrate with centralized logging server
Splunk (or other Syslog endpoint) is deployed on the network and accepts messages on UDP port 514. Confirm that SRA has the capability to integrate with a central logging server to help aggregate and secure logs. Specifically, SRA uses Syslog to send logs and Splunk was used as the target server. - Log in to SRA and go to System Management > Syslog server.
- Click Add syslog server.
- Fill out the Syslog server details.
- IP: <Syslog server IP>
- Protocol: UDP
- Port: 514 (default)
- Click Test server. Confirm that Success is displayed.
- Click Add.
- Go to User Management and click New user.
- Fill out information for a test user and click OK.
- Open a new tab and attempt to log in with the new user but using the wrong password.
To verify, perform the following steps: - Go to the target Syslog server and search for the IP address of the SRA server.
- Confirm that logs appear with content similar to the following:
- User '<username>', type 'Local', failed to log in the system on site '<Site>' using IP address '['<IP address>']'. Reason: Invalid username or password. Contact your administrator.
- User '<username>' created a new user: '<username>', type: 'Local'
Test 10: Connect to NTP server
NTP server is deployed on the network and reachable from the CTD component. Part of an effective audit/logging system is to have time synchronized across devices on the network. This helps when correlating events across a range of device logs. Validate that SRA can successfully connect to an NTP server. - SSH to the SRA host.
- Edit the chronyc file:
- Open the file with editor of choice, for example: vi /etc/chrony.conf
- Edit the file and insert a line above the default server entries for the organization's NTP server of choice:
server <IP/FQDN of NTP server> iburst prefer - Save and quit out of the file.
- Restart the chrony service:
systemctl restart chronyd - Run the command below to confirm that NTP is synchronized to the NTP server. The Reference ID should be set to the NTP server.
chronyc tracking
To verify, perform the following steps: - Run the command date on the SRA host and take note of the time.
- Log in to the SRA web user interface.
- Go to Activities.
- Confirm that the entry for Login to SRA succeeded has the correct time listed under the Date column.
xDome hardening
The following settings have been validated on the xDome analysis server dashboard.
Test 1: Configure RBAC Settings
There is a user provisioned by Claroty that can be used to change settings on the organization's Analysis Server instance. Confirm that the xDome analysis server can define groups with specified permissions. Validate that the configured permissions are working correctly. This test does not validate every set of permission settings, but rather tests the overall functionality. - Log in to xDome with a user who has administrative permissions to change site settings.
- Go to Settings > System Settings > Role-Based Permissions.
- Click the + Add Role button.
- Enter the name Test and click Add.
- Verify a column with name, "Test" appears on the RBAC table (far right).
- Under the Test column, and on the Home row, click the box for the setting: View Sites Overview Page.
- Click the checkmark button to Save Changes.
- Go to Settings > System Settings > User Management.
- Click the + Add User button.
- Enter the following settings:
- USER TYPE: Claroty Dashboard User
- First Name: Test
- Last Name: User
- Username: test.user
- Title: Tester
- Email: <email where Claroty will send account registration to>
- Site Permissions: Select All
- Role: Test
- Click Create User.
To verify, perform the following steps: - Custom Role Verification:
- Go to the specified email for when the test user was created.
- Click the link to register the user, set the password, and log in.
- Navigate to Home > Reports. Confirm that the left side states No Matching Graphs and that the Generate Report button is missing.
- Navigate to Devices > All Devices and click on a device in the list. Confirm that only basic information is listed and there are no details such as RISK & ALERTS.
- Log back into Claroty as an admin user and Settings > System Settings > User Management.
- Click the Edit User button for user Test (pencil icon).
- Edit the Role to Read-Only User and click Save User.
- Predefined Role Verification:
- Log back in with the test user.
- Go to Home > Reports. Confirm that the left side of the screen lists options to add to the report and that the Generate Report button is present.
- Go to Devices > All Devices and click a device in the list. Confirm that all details are visible such as RISK & ALERS. Hover over + Add Notes, confirm that the user does not have permission to add notes.
Test 2: View application logs
There is an existing test user on the system. Validate the capability of the xDome analysis server to audit and log actions taken on the system such as successful or failed login attempts or system configuration changes. This is critical in holding users accountable for their actions and for investigating suspicious activity. - Log in as the test user.
- Log out as the test user.
- Log in with an admin account.
- Navigate to Settings > System Settings > User Management.
- Click the Edit User button (pencil icon) for the test user.
- Change the user's role (can change it back after test) and click Save User.
To verify, perform the following steps: - Navigate to Settings > System Settings > System Audit Log.
- Verify the log output looks similar to the following table.
Table 13. Claroty xDome System Audit Log results verification CATEGORY ACTION DETAILS USER Dashboard Users User Logged In Ser logged in <username> Dashboard Users User’s Role Changed User <username> was changed to role <Role name> <admin username>
Test 3: Configure multifactor authentication
There is a test user account available with access to that user's email account to obtain the multifactor authentication code. Validate the capability of xDome to be able to enable two factor authentication for user logins to the analysis server dashboard. This test uses email as the second form of authentication in addition to the default username and password authentication. - Log in to the xDome analysis server dashboard is an admin user and go to Settings > System Settings > Login Management.
- Toggle on the Multi-factor Authentication setting.
- Click the Email box.
- Press Ok on the following prompt. Note: The settings may take up to an hour to apply.
To verify, perform the following steps: - Log out and log in again.
- After entering in the correct username and password, confirm that the user is prompted to enter a code.
- Go to the user's associated email address, obtain the code, and enter it into the xDome login page.
- Press Login and confirm that the code works and the user successfully logs in.
CTD IDMZ architecture and validation
The following Claroty IDMZ architecture and security validation have been tested on CTD version 4.6.
Use case: EMC to CTD connection
EMC is used to manage multiple CTD Server and CTD Sensors connections. For the DVD security architecture, EMC is validated to run on the enterprise/IT and manages CTD instances residing in the IDMZ network while CTD Sensors are hosted on the OT network to collect OT data closer to the edge. CTD Sensors connect and send data to the CTD Server in the IDMZ and then the CTD Server connects to and sends its data to be aggregated at the EMC on the IT network.
Figure 176. CTD IDMZ security architecture example in the Purdue Model 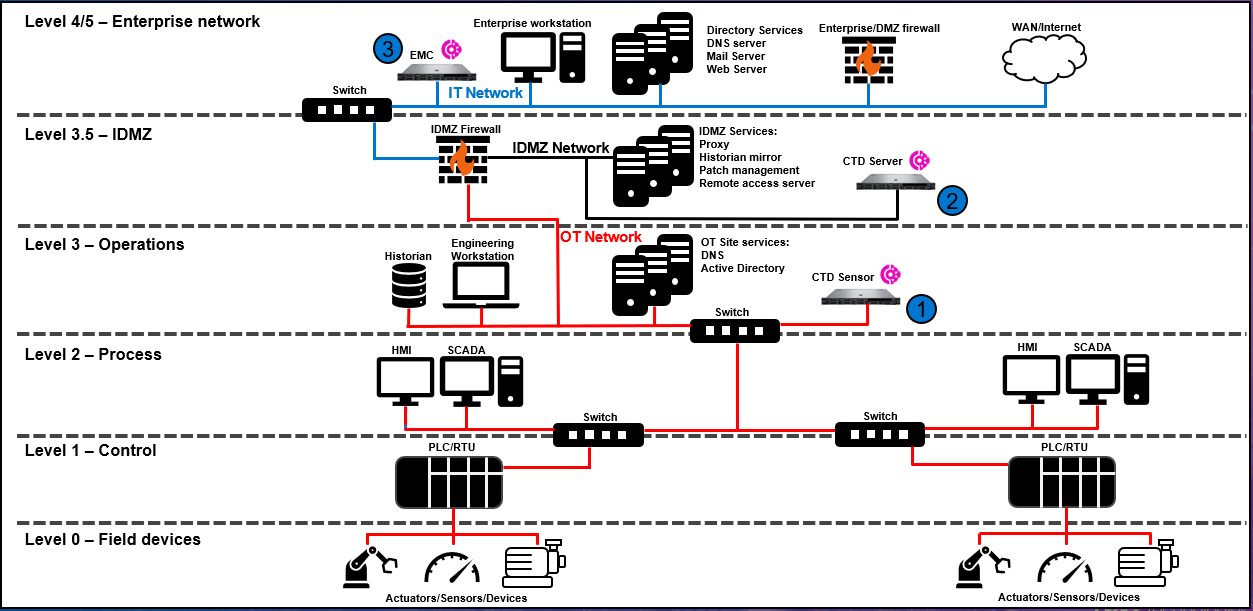
Table 14. CTD validated firewall rules Description Source network Source device Destination network Destination device Port Application Allow CTD Sensor on OT network to connect and send OT data to CTD in the IDMZ. OT CTD Sensor (1) IDMZ CTD Server (2) TCP 22 SSH Allow CTD Server within IDMZ to connect to EMC on the IT network. IDMZ CTD Server (2) IT EMC (3) TCP 443 SSL/TLS Note: These firewall rules assume that the SSL/TLS option was selected when connecting CTD Servers to EMC. If the option was not selected, and then SSH would be used for the connection between CTD and EMC.
SRA IDMZ architecture and validation
The following Claroty SRA architecture and security validation have been tested with SRA version 3.5.
Use case: SRA Site to SRA SAC connection
SRA SAC connects to SRA Sites. SRA SAC uses SRA Sites to establish connections to target servers on the OT network. For the DVD recommended security architecture, the SRA Site is hosted in the IDMZ network. This creates a proxied connection between the SRA SAC and the target server in the OT network. These rules validate the initial connection and registration process between SRA SAC and SRA Site followed by the rules required to allow continued communications.
Figure 177. SRA IDMZ security architecture example in the Purdue Model 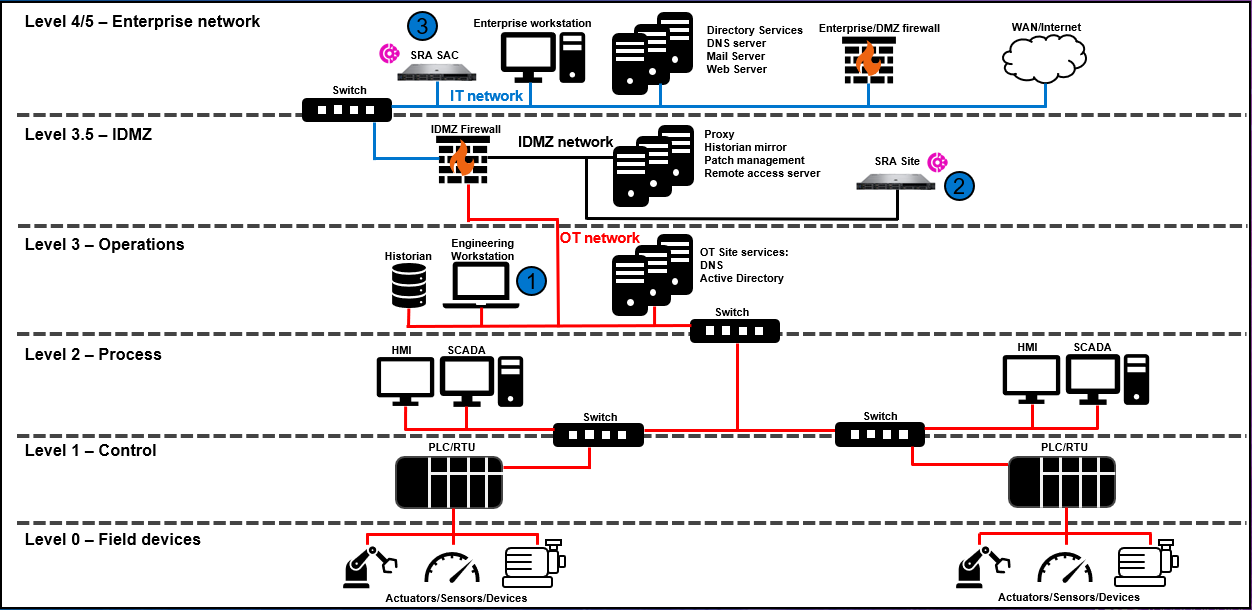
Table 15. Validated firewall rules Description Source network Source device Destination network Destination device Port Application SRA Site registration to the SRA SAC hosted in the IT network.1 IDMZ SRA Site (2) IT SRA SAC (3) TCP 9301,TCP 22 SSH, Web browsing SRA Site to SRA SAC connection for continued communications. IDMZ SRA Site (2) IT SRA SAC (3) TCP 22 SSH 1 This rule can be deleted or disabled after the initial registration of SRA Site to SRA SAC is completed.
Use case SRA Site and OT device connections
The actual connection to the OT devices is done from the SRA Site. To securely implement this, the IDMZ firewall should only allow the required ports and protocols for the remote session type (example: RDP) between OT device and SRA Site. Also, SRA Sites allow SFTP connections to upload files. These rules validate OT devices uploading files securely using SFTP to SRA Site on the IDMZ network. Lastly, there may be use cases where OT devices will also access the SRA Site.
Figure 178. SRA IDMZ security architecture example in the Purdue Model 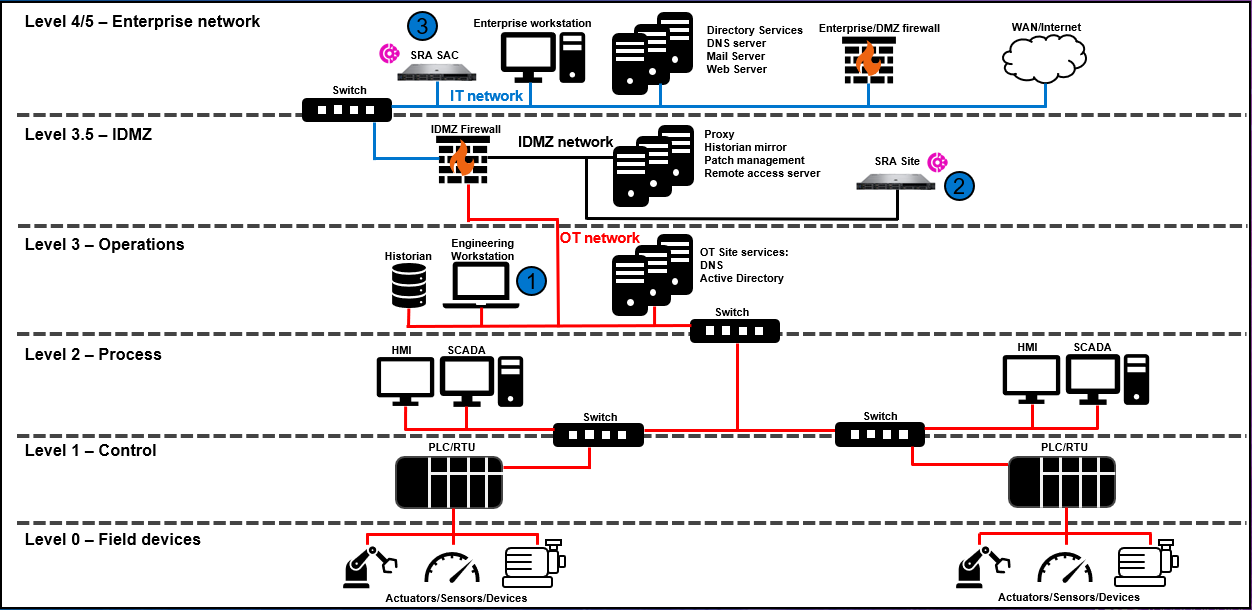
Table 16. Validated firewall rules Description Source network Source device Destination network Destination device Port Application SRA Site to target OT device using supported remote session protocols.1 IDMZ SRA Site (2) OT OT Device (example: Engineering workstation) (1) - TCP 22
- TCP 23
- TCP 3389
- TCP 59002
- TCP 80
- TCP 443
- SSH
- Telnet
- RDP
- VNC
- Web browsing
- SSL
Allow OT device to upload files to SRA Site. OT OT Device (1) IT SRA Site (2) TCP 2222 SSH Allow OT devices to access SRA Site web user interface. OT OT Device (1) IDMZ SRA Site (2) TCP 443 SSL 1 Only allow port and associated protocol based on what the target device is using. For example, if the target OT device only requires RDP and then only allow port 3389 and application RDP.2 VNC ports can often be 5900 + n (for example 5901) where n represents the connection number on the target server.xDome IDMZ architecture and validation
The following Claroty xDome architecture and security validation have been tested with xDome Collector and Analysis Server.
Use case: xDome component connections
xDome is made up of two main components. One component is the Collector, which resides on the plant floor and collects data about the network and assets through means such as passively collecting network traffic or integrating with on-premises devices. Within this recommended architecture, another collector server acts as a proxy to securely route traffic from OT, to the IDMZ, and then to the analysis server hosted in the cloud. The analysis server is also known as the dashboard where users see the processed plant floor data translated into assets, risks, vulnerabilities, threats, and so on. Lastly, the Claroty Edge component is another method to collect data on the plant floor and is designed to securely send data directly to the Cloud instance. Communications between components is done through secure tunnels.
Figure 179. xDome IDMZ security architecture example in the Purdue Model 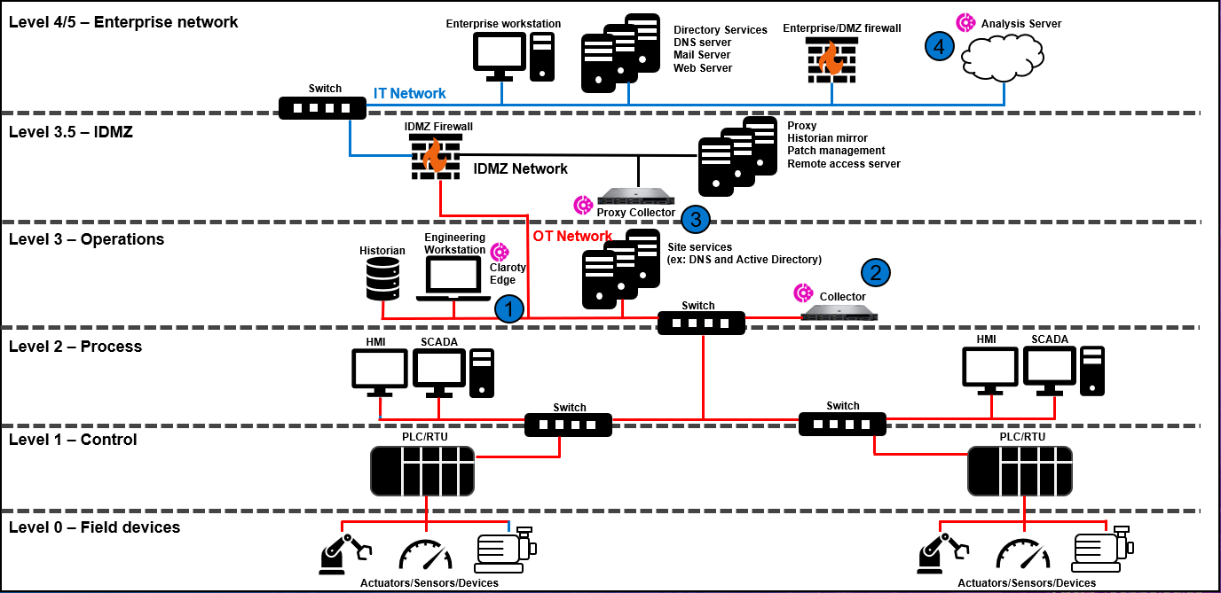
Table 17. Validated firewall rules Description Source network Source device Destination network Destination device Port Application Allow OT Collector to send traffic to Proxy Collector hosted in the IDMZ network. OT Collector (2) IDMZ Proxy Collector (3) TCP 8443, TCP 8444 HTTP-Proxy, Web-browsing, SSL Allow Proxy Collector to connect to and send data up to the Analysis Server hosted in the cloud. IDMZ Proxy Collector (3) External1 Analysis Server (4)2 TCP 443 SSL Allow Claroty Edge to send data to to proxy server hosted in the IDMZ network.3 OT Claroty Edge IDMZ Proxy TCP 3128 HTTP-proxy, SSL/TLS, Web-Browsing Allow proxy server to forward connection from Claroty Edge to analysis server. IDMZ Proxy External Analysis server 443 SSL/TLS 1 Destination network depends on the network configuration and how data is routed from the organization to external networks.2 Analysis Server IP addresses are dependent on the region.3 This test assumes that default proxy port 3128 is used. Proxy settings were configured in the browser, but Claroty Edge also allows the user to specify a proxy IP in the configuration settings.
