Home > Edge > Manufacturing Edge > Guides > Dell Validated Design for Manufacturing Edge - Design Guide with 5 Independent Software Vendors > Cybersecurity for Telit Cinterion
Cybersecurity for Telit Cinterion
-
Overview
Note: Throughout the following sections, keep in mind that anytime a configuration change is to be made, it is best practice to make a backup of the node prior. For more information, see the Backup and restore with Workbench section.
Note: Keep in mind that implementing security features, like encryption or proxying, can affect system performance.
Application hardening
Authentication
Test case: Create unique local user
Ensure that the new local users can be configured and that users must be unique. To configure, perform the following steps: - Open Workbench and connect to the deviceWISE Edge node.
- Expand the node’s menu, and go to Administration > Security > Users.
- Click New.
- In the pop-up window, Name the user and assign roles as needed. See Test case: RBAC with local Role for more information about roles. Click OK to save.
- Confirm that the new user appears in the list on the Users tab.
To verify, perform the following steps: - Repeat the above steps, attempting to use the same Name for the user.
- The user cannot be saved, and an error message will appear in a pop-up window: “The username already exists. Please enter a unique value in the Name field.”
Test case: Delete local user
An existing local user to delete
To maintain proper access control, users that no longer require access should be deleted. This test case confirms that users can be deleted, and that those credentials can no longer be used to access a node.
- Open Workbench and connect to the deviceWISE Edge node.
- Expand the node’s menu, and go to Administration > Security > Users.
- Select the user in the list and click the Delete button.
- Confirm the deletion in the pop-up window. The user should no longer be in the list of users.
To verify, perform the following steps: Attempt to log in as the deleted user:
- Right-click on the node and select Use Alternate Credentials.
- Log in as the deleted user.
- Confirm that node is inaccessible.
Test case: Change default logins
A second instance of Workbench
It is imperative to change the default logins on each deviceWISE Edge node. Since all nodes have the users preconfigured, the credentials can be considered public knowledge. Also, when a Workbench instance connects to a node, it tries the default admin login automatically, so one is not required to know what the default credentials are to connect to a node. Furthermore, the admin user is given unbridled access to the node by default, and this cannot be changed. It is vital to change default logins to prevent both malicious and unwitting unauthorized access.
Note: An admin user can change the password of other users, but there is no way to recover the password of the admin user once logged out. It is imperative that changed passwords are retained in a secure manner, or the node may become inaccessible.
- Open Workbench and connect to the deviceWISE Edge node.
- Log in as the admin user, if not done already.
- Expand the node’s menu, and navigate to Administration > Security > Users.
- Select the admin user from the list and click Edit.
- In the Edit User pop-up window, enter a password, and re-enter the new password to confirm. Click OK to save.
- Upon the password save, the node is immediately inaccessible.
To verify, perform the following steps: Log in with the new credentials:- Right-click on the node and select Use Alternate Credentials.
- Log in as the admin user with the new password. Access to the node should be granted.
- Open the second Workbench instance, and scan for the deviceWISE Edge node.
- Confirm that node is inaccessible by default, and that valid credentials must be applied before access is granted.
Test case: Workbench session management
Non-default login credentials, per Test case: Change default logins.
When interacting with a deviceWISE Edge node, a user’s session is managed by the Workbench instance they are using. Sessions are separate per node, so a user requires valid credentials for each node, although it is not a requirement that they be the same credentials. Sessions are maintained by the Workbench instance and last until Workbench is closed or a new user is logged in.
As described in Test case: Change default logins, when starting Workbench, it attempts to use the default credentials, so the default credentials must be changed in order for closing Workbench to effectively limit access to an unauthorized person. This test case explores closing Workbench as a way to end a user session, given that the default node credentials have already been changed.
- Open Workbench and connect to the deviceWISE Edge node.
- Right-click on the node and select Use Alternate Credentials. Log in as any valid user. Note: The Workbench session shows the logged in user in the top of the pane, unless the Workbench instance logged into the node with default credentials automatically.
To verify, perform the following steps: - Close the Workbench window.
- Relaunch Workbench.
- Confirm that the node is inaccessible by default, requiring a user to enter credentials for access.
Test case: Integrate with AD over LDAP
- The LDAP package is installed on the deviceWISE Edge node.
- AD is deployed and has users and groups configured and available for testing.
Note: At the time of writing, there is a conflict between the LDAP and OAuth packages—the OAuth package must not be installed on the node for the LDAP package to work properly.
LDAP (Lightweight Directory Access Protocol) is a protocol used to interact with directory servers. In this test case, the deviceWISE LDAP integration supports integration with a Microsoft AD (Active Directory) server for user management and Role-Based Access Control (RBAC).
- Open Workbench and connect to the deviceWISE Edge node.
- To configure LDAP settings on the deviceWISE Edge node, perform the following steps:
- Expand the node’s menu and navigate to Administration > LDAP. Configure the settings as follows:
- LDAP Primary Server: <hostname or IP address> of AD server
- LDAP Secondary Server: <hostname or IP address> of AD server to be used if the connection to the LDAP Primary Server fails.
- LDAP Port: 389
- Protocol: LDAP
- Query Username: <DN string for user for AD user with AD search privileges> (example: cn=adsearchuser,cn=users,dc=example,dc=com)
- Query Password: <password for user given in Query Username>
- Base Directory: <DN query string for users to integrate with deviceWISE> (example: ou=users,ou=dwusers,dc=example,dc=com)
- Filter: <additional attributes to filter users>
- Format for $(User): <specify the user domain format>
- Group Attribute: <attribute which contains a user’s group information>
- Click Save.
- Create Role and assign permissions—see Test case: RBAC with AD.
To verify, perform the following steps: Log in with the AD credentials:
- Right-click on the node and select Use Alternate Credentials.
- Log in as the AD user—ensure the format used matches the Format for $(User): specified in the LDAP configuration tab.
- Access to the node should be granted, with permissions as defined in the Policies tab for role matching the AD group.
Authorization
Test case: RBAC with local Role
RBAC is an approach to security where users are granted a set of permissions based on a role they have or a group they are in. The deviceWISE Edge Security functionality provides a locally administered option to create roles and define the permissions for those roles, which are inherited by the users who hold those roles. This test case examines how to create a role and assign permissions to that role. - Open Workbench and connect to the deviceWISE Edge node.
- Expand the node’s menu, and navigate to Administration > Security > Roles.
- Click New. Enter a Name for the role.
- Click Add to save. Confirm the new role is in the list.
- Go to Administration > Security > Policies.
- Select the Default Policy and click Edit.
- In the column under the new role, make selections for the permissions that should be applied. Click Save.
- On the popup window, click Yes to apply the policy changes.
To verify, perform the following steps: - Go to Administration > Security > Users.
- Assign the role to a user.
- To log in as that user, right-click on the node, and select Use Alternate Credentials.
- Confirm that the menu items are visible as expected.
Note: Some subcategories may be visible if their parent category is visible, even if permissions to the subcategory are not granted. In this case, the features may be disabled or a save may fail, indicating the user does not have access.
Note: At the time of writing, the Cloud Connectors page is visible to anyone who logs in with valid credentials if a related package is installed, regardless of assigned permissions.
Test case: RBAC with AD
deviceWISE AD integration with LDAP, as described in Test case: Integrate with AD over LDAP RBAC is an approach to security where users are granted a set of permissions based on a role they have or a group they are in. The deviceWISE Edge LDAP integration supports the mapping of AD groups to local roles, and permissions for those roles can be defined, which are inherited by the users who belong to the AD group. This test case examines how to create a role to match an AD group and assign permissions to that role. - Open Workbench and connect to the deviceWISE Edge node.
- Create a Role and assign permissions:
- Expand the node’s menu, and go to Administration > Security > Roles.
- Create a Role with a name identical to the AD group name, then click Save.
- Go to Administration > Security > Policies.
- Edit an existing policy or create a new policy and define the permissions that should be applied to the AD group.
- Repeat the above steps for each AD group.
- Right-click the node and select Use Alternate Credentials.
- Log in as the AD user.
To verify, confirm that the AD user has permissions as defined by the role matching the name of their AD’s group: - Log in as a user that has Administration viewing access, if the LDAP user does not have them.
- Go to Administration > Security > User.
- Confirm that a user was automatically generated with the name LDAP_<AD username>. For example, an entry for the AD user JohnS shows as LDAP_JohnS.
- Confirm that the user automatically has the AD role assigned.
Confidentiality
Test case: Encrypt data from far edge node to SDP
SDP deployed with MQTT broker. See the Configure SDP project/scope and prepare MQTT data ingest section. For a more secure OT system, traffic across a network should be encrypted to prevent an unauthorized party from accessing or compromising industrial data or processes. This test case examines the traffic over the MQTT protocol with TLS (MQTTS), from a far edge deviceWISE Edge node to SDP. - Prepare the deviceWISE Edge node for the MQTT connection, and configure the MQTT with TLS connection to SDP, as described in Prepare the Telit deviceWISE gateways for MQTT connection and Configure the device MQTT connection.
- Configure a trigger to send data to MQTT using the SDP MQTT device connection. Because the conditions, structure, and data required to build this trigger are application-specific, it is not covered here.
To verify, perform the following steps: - In SDP, confirm that data is being ingested, as described in the Streaming Data Platform chapter.
- Once it is confirmed that SDP is receiving data, use a packet capture tool, like WireShark, on the deviceWISE Edge node host machine to capture and analyze the network traffic. Confirm that payloads are encrypted.
Accounting
Test case: Audit log
An audit log is an important tool to track actions, which can be used to find the source of additions, changes, or deletions for a node’s configuration, whether intentional or unintentional. For each event, the following is captured: Date, Time, User, Component (action category), and Message (action description). This test case examines the capture of a selection of actions.
- Open Workbench and connect to the deviceWISE Edge node.
- Perform the following actions:
- Add, edit, and delete a user.
- Add and delete a role.
- Add, edit, and delete a policy.
- Log in as a different user.
- Add and remove a package.
- Add, edit, change state of, and delete a trigger.
- Add, edit, change state of, and delete a device.
- Export and import a project.
- Backup and restore the node.
To verify, perform the following steps: - Expand the node’s menu, and go to Logs & Reports > Audit Log.
- Verify that each of the above actions is captured as an event in the audit log. Some system entries may also be seen, such as the automatic node restart that occurs after adding or removing a package.
Note: At this time, entries for failed logins and license client settings are not captured.
Test case: Update deviceWISE Edge software
Take backup of node prior to update. Over time, it may become necessary, or at least advantageous, to update the deviceWISE Edge software. It is important that security settings remain in place after an update. This test case reviews select security settings before and after a minor version update.
To configure, perform the update as described in Updating deviceWISE Edge software.
To verify, perform the following steps: - Open Workbench and connect to the deviceWISE Edge node.
- Go to Administration > Security, and confirm that the settings for Users, Roles, and Policies are intact.
- If an LDAP integration is implemented, go to Administration > LDAP, and confirm that LDAP settings are intact.
Telit Cinterion IDMZ architecture and validation
Architecture
The IDMZ (Industrial Demilitarized Zone) provides distinct network segmentation between the industrial control network (OT network) on the plant floor and enterprise network (IT network). This interruption in network continuity prevents an IT attack from making its way to the OT network and compromising assets and processes. The IDMZ typically contains a proxy, where traffic coming into the IDMZ terminates and a firewall with rules to limit traffic to only expected connections and protocols.Figure 167. IDMZ architecture, incorporating a firewall and proxy between the control network and the enterprise network 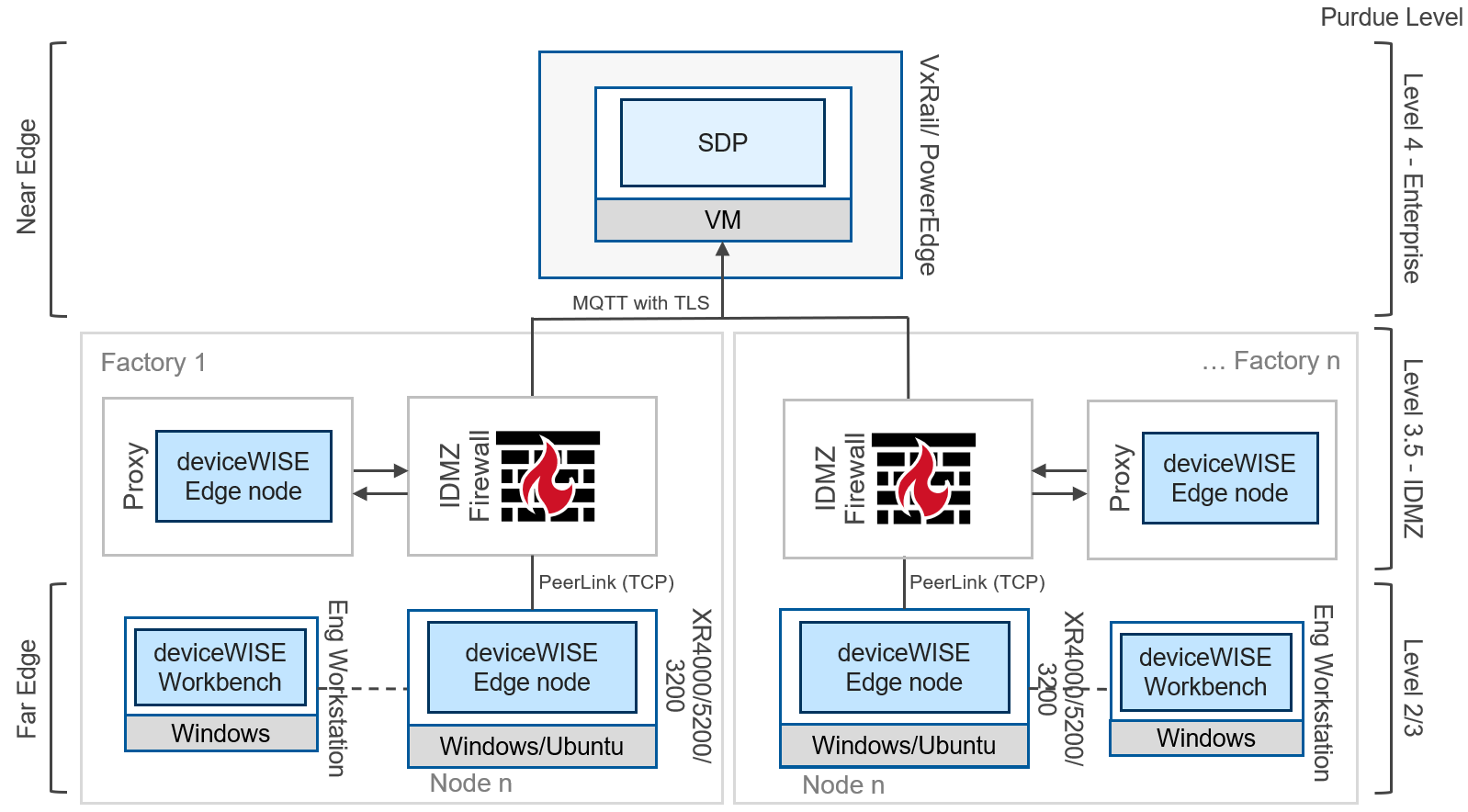
In this case, The IDMZ proxy function can be served by deploying a deviceWISE Edge node in the IDMZ network, which receives data from the far edge deviceWISE node and can send it onward to SDP to make it available for further analysis and visualization.
The test cases outlined below will explore the details of this IDMZ architecture further.
Validation
Test case: Encrypt data from far edge to IDMZ proxy
- A deviceWISE Edge node and Workbench deployed in the OT network (at the far edge)
- A deviceWISE Edge node and Workbench deployed in the IDMZ network
Traffic across the IDMZ boundaries should be encrypted for maximum security benefits. This test case examines the traffic moving from the far edge control network to the IDMZ proxy using deviceWISE Edge’s PeerLink connection type. In deviceWISE Edge v22.03, this proprietary protocol uses TCP with custom encryption. deviceWISE Edge v22.04 has an option to use TLS instead of the custom encryption, but this was not tested here.
The first part of this task is to create user credentials on the IDMZ node to allow the far edge node to establish communication. Alternatively, an AD (Active Directory) user can be used if LDAP (Lightweight Directory Access Protocol) is configured on the node, and this step can be skipped. See Test case: Integrate with AD over LDAP for more information about configuring LDAP.
- To create user credentials, perform the following sub-steps:
- Open Workbench on the IDMZ network, and connect to the IDMZ proxy node.
- Expand the node’s menu, and go to Administration > Security > Roles.
- Click New. In the popup window, name the new role Control-Node. Click Add to save.
- Go to the Policies tab under Administration > Security.
- Select the Default Policy and click Edit.
- In the Policy pop-up window, make permissions settings as wanted. At a minimum, ensure that there is a green check by the following:
- Triggers > Start
- Triggers > Stop
- Triggers > View
- Click Save to close the pop-up window.
- Go to the Users tab under Administration > Security.
- Click New. In the pop-up window, name the new user node1, assign a password, and select the checkbox by Control-Node in the Roles section. Click OK to save.
- To configure the PeerLink Connection to the IDMZ proxy node on the far edge deviceWISE node, perform the following sub-steps:
- Open Workbench on the OT network, and connect to the far edge node.
- Expand the node's menu, and go to Devices.
- Click New. In the Device pop-up window, apply the following configuration settings:
- Name: IDMZ-Proxy-PeerLink
- Type: Node Connection
- IP Address: <IP of IDMZ proxy node>
- Username: node1 (user created above)
- Password: <password> (of user created above)
- Click Save to close the pop-up window.
- Select the new device IDMZ-Proxy-PeerLink in the list, and click Start. The device's state should change to Started, if a connection can be established. If device does not start, check you network routing and IDMZ node credentials.
To verify, perform the following steps: - Ensure that data is being sent from the far edge deviceWISE Edge node to the IDMZ proxy node. The best way to accomplish this is application-specific, so it is not covered here.
- Once it is confirmed that the IDMZ proxy node is receiving data, use a packet capture tool, like WireShark, on the IDMZ proxy deviceWISE Edge node host machine to capture and analyze OT-to-IDMZ traffic. Confirm that payloads are encrypted (not human-readable).
Test case: Encrypt data from IDMZ proxy to SDP
- SDP deployed with MQTT broker (see section Configure SDP project/scope and prepare MQTT data ingest)
- A deviceWISE Edge node deployed in the IDMZ network
- A static route configured on the SDP host to route to the IDMZ network, if needed
Traffic across the IDMZ boundaries should be encrypted for maximum security benefits. This test case examines the traffic moving from the IDMZ proxy to SDP using the MQTT protocol with TLS, sometimes referred to as MQTTS. - Prepare the IDMZ node for the MQTT connection, and configure the MQTT with TLS connection to SDP, as described in Data ingest integration using Telit deviceWISE to SDP.
- Configure a trigger to send data to MQTT using the SDP MQTT device connection. Because the conditions, structure, and data required to build this trigger are application-specific, it is not covered here.
To verify, perform the following steps: - In SDP, confirm that data is being ingested, as described in the Streaming Data Platform chapter.
- Once it is confirmed that SDP is receiving data, use a packet capture tool, like WireShark, on the IDMZ proxy deviceWISE Edge node host machine to capture and analyze the IDMZ-to-IT traffic. Confirm that payloads are encrypted (not human-readable).
Test case: Validate IDMZ firewall rules
The following firewall rules were implemented and validated on the Telit Cinterion IDMZ architecture.
Table 10. Table of firewall rules to allow traffic required for Telit Cinterion IDMZ architecture Description Source Network Source Device Destination Network Destination Device Port Application1 Allow the far edge deviceWISE Edge node on OT network to connect and send OT data to IDMZ proxy deviceWISE Edge node in the IDMZ network. OT Far edge deviceWISE Edge node IDMZ IDMZ proxy deviceWISE Edge node TCP 4012 Unknown-TCP2 Allow the IDMZ proxy deviceWISE Edge node in the IDMZ network to connect to the SDP MQTT broker in the IT network. IDMZ IDMZ proxy deviceWISE Edge node IT SDP MQTT broker TCP 8883 SSL/TLS 1 The Application attributes correlate to Palo Alto Networks firewalls and may be different from other network firewalls. The port for MQTT over TLS is a default—part of defense-in-depth is to not use default ports.2 The PeerLink connection on the deviceWISE platform is used for node-to-node communication, and in v22.03.06 relies on a proprietary encryption method; therefore, it is not recognized as TLS.
