Home > Edge > Manufacturing Edge > Guides > Dell Validated Design for Manufacturing Edge - Design Guide with 5 Independent Software Vendors > Cybersecurity for Litmus
Cybersecurity for Litmus
-
Note: Keep in mind that implementing security features, like encryption or proxying, can have an effect on system performance.
Litmus Edge hardening
The following settings have been validated on Litmus Edge version 3.2 unless specifically stated otherwise.
Test 1: Load CA signed certificates
- Ability to run openssl commands.
- Ability to sign CSRs.
Confirm that CA signed certificates can be used by Litmus Edge during operations. This adds a layer of trust for when communicating with Litmus Edge (for example, when accessing the HTTPS interface). The end user can be assured that the certificate was signed by a trusted party.
- Start by creating a CSR and key pair using the openssl command which can be run on a Linux machine. Example command: openssl req -newkey rsa:2048 -nodes -keyout <key-name>.key -out <csr-name>.csrNote: To get the hostname of the Litmus Edge host for the CN value of the certificate, Go to System > Network > Overview.
- Sign the CSR with a trusted CA and obtain the signed certificate.
- Transfer the signed certificate, certificate key file, and CA signing certificate to a location with access to a web browser that can access Litmus Edge.
- Log in to Litmus Edge and go to System > Certificate > Device Certificate.
- Click the + Add Certificates button.
- For SSL certificate, upload the CA signed certificate. Note: When browsing for the certificate on Windows, you can select the option for, "All files" if your certificate extension is not .der or .pem and something like .crt but is in the correct format.
- For CA chain, upload the CA signed certificate/chain.
- For Private RSA Key, upload the signed certificate key.
- Click Submit. Note: If there is an error for parsing the key, try to convert it to the format Litmus Edge is looking for. For example, use openssl to convert keys: openssl rsa -in <current_key>.key -out <new-keyname>.key. Verify that the content of the key starts with "-----BEGIN RSA PRIVATE KEY-----".
To verify, perform the following steps: - Upon clicking Submit, confirm there are no errors and that the details under Device Certificates reflect the correct information pertaining to the Issuer.
- Refresh the web page.
- From the web browser, review the contents of the certificate and confirm it is the correct Issuer.
Test 2: Secure connections for MQTT
- MQTT broker deployed that can support TLS connections and use authentication.
- Litmus Edge is generating tag data.
- User can subscribe to MQTT broker topic to view data being published to the topic.
Validate LE can connect to MQTT brokers using TLS to secure the connection in addition to using username and password to authenticate the connection.
- Log in to Litmus Edge and go to Integrations.
- Click + to add a new connector.
- In the dropdown, select MQTT - Generic over SSL.
- Fill out the minimum information according to the target MQTT broker:
- Name: Descriptive name for the connection
- Hostname: FQDN/IP address of the MQTT broker
- Port: 8883 (Default)
- CA Certificate: Paste in MQTT broker's CA Certificate in Base64 format.
- Username: MQTT broker username
- Password: MQTT broker password
- Client ID: Random string
- Integration topic: MQTT broker topic data is being published on
- Click Add.
To verify, perform the following steps: - Click the toggle button to enable the connector.
- Confirm the integration shows Connected.
- Click within the tile and click on Topics.
- Click + Add a new subscription.
- Set Data Direction to Local to Remote - Outbound
- Choose a local tag to add as a Local Data Topic and toggle Enable to turn on.
- Click Yes and copy the Local Topic to use for later.
- Confirm that the MQTT broker is receiving the Litmus Edge tag data.
Test 3: Secure OPC UA connections
- Litmus Edge Version 3.3.1 or higher.
- OPC UA Server deployed on network and configured to accept connections for Basic256SHA256 Sign and Encrypt.
- Litmus Edge can resolve OPC UA server hostname if necessary.
Validate LE can connect to an OPC UA server and ingest data over a secured connection using encryption and authentication. This is recommended instead of using unsecure communications as that can compromise the confidentiality and integrity of the data. A custom CA signed certificate is used on Litmus to validate that users can load their own certificates instead of using default self-signed certificate.
- Log in to Litmus Edge and navigate to DeviceHub > Devices.
- Click the + to add a device.
- Under Device Type, select OPCUA, and for Driver Name select OPC UA Client Advanced.
- Fill in the settings according to the target OPC UA Server. Use the following settings as guidance for a secure OPC UA connection with a custom certificate (non-default). Make sure to enter all required parameters, beyond what is listed below.
- Server URL: <FQDN/IP of target OPC UA server that is an CN or SAN value in OPC UA server certificate>
- Security Policy: Basic256Sha256
- Security Mode: SignAndEncrypt
- Session Certificate: <Upload or copy/paste custom certificate in PEM format> Note: When creating a custom certificate for the OPC UA Client driver on Litmus Edge, make sure to add Subject Alternate Name (SAN) fields for the access URL and DNS. Use the self-signed client driver certificate as a template. View the LE OPC UA client driver self-signed certificate by exporting it when configuring the client driver settings.
- Session Private Key: <Upload certificate’s corresponding private key in PEM format>
- Auth Mode: UserName
- User Name:<Username for OPC UA server user>
- Password: <Password for OPC UA server user>
- Disable Error Certificate Host Name Invalid: false
- Click Add Device when finished configuring all settings. Note: Depending on the organization’s certificate setup, the OPC UA server may need import the signing CA certificate for the custom certificate uploaded to the Litmus Edge OPC UA Client driver.
To verify, perform the following steps: - Confirm that the status on DeviceHub > Devices for the OPC UA connection is displayed as Connected.
- Go to Tags and click the + button followed by Browse Tags.
- Under Select Device, choose the name of the Device connection added in this test case.
- Verify that the system is able to browse different tags.
Test 4: Integrate with Active Directory over LDAPS
Litmus Edge can resolve the FQDN of the AD server. Validate that Litmus Edge can integrate with an Active Directory server over LDAP using TLS (also known as LDAPS). This enables central management of users and protects the confidentiality of the authentication data when using LDAPS instead of regular LDAP. This test is done using a manual entry method. Using templates or loading features were not validated for this test.
Note: If DNS cannot resolve the FQDN of the AD server go to System > Network > DNS/NTP Servers and add an entry to the Hosts file section.
- Log in to Litmus Edge and go to System > LDAP/AD Auth.
- Click the + Add New button.
- Click Advanced.
- Give a descriptive Name and for Type leave as generic. Click Next.
- In the Connection settings, use the settings below as a guide:
- Host: FQDN of the AD server.
- Port: 636 (default LDAPS port).
- Use TLS: Select this option.
- TLS Root CA: CA signing certificate for the AD server.
- Bind DN: LDAP query for user who can authenticate to AD server for LDAP functionality Example: cn=administraotr,cn=users,dc=example,dc=com
- Bind DN Password: Password of above user.
- Click Next.
- In the Users settings reference the settings below as a guide:
- Users Search Base DN: Base DN string for users group Example: cn=users,dc=example,dc=com
- Search Scope: sub (depends on organization's deployment)
- User Search Filter: AD attributes to filter by for users Example: (&(objectCategory=person)(objectClass=user))
- Attribute for Unique UserID: Attribute in AD to uniquely identify user Example: sAMAccountName or uid
- Attribute for Username (for logging in): Attribute in AD that will be used for username Example: sAMAccountName or uid
- First Name: Attribute in AD that will be used as user's first name value Example: givenName
- Last Name: Attribute in AD that will be used as user's first name value Example: sn
- Users Search Base DN: Base DN string for users group
- Click Next.
- In the Groups settings, reference the settings below as a guide:
- Group Search Base DN: Base DN string for group to use in AD Example: cn=users,dc=example,dc=com
- Search Scope: sub (depends on organization's deployment)
- User Search Filter: AD attributes to filter by for groups Example: (objectCategory=group)
- Group Name Attribute: Attribute in AD that specifies group name Example: cn
- Group Membership Attribute: Attribute in AD that ties user to group(s) Example: member
- Member Value Type: Type of group member object Example: DN
- Group Search Base DN: Base DN string for group to use in AD
- Click Test.
- Verify that all of the status' report OK and that there is at least one result for each.
- Click Back from the test window and then click Update. Note: (Optional) Click Save to create a JSON configuration file of the settings.
- Within the Map Groups to Roles window, select a Role for the integrated AD group. For example, map AD group "admins" to Litmus Edge local group, "administrator".
- Click Save.
To verify, perform the following steps: - Log out of Litmus Edge.
- On the login screen, enter in the credentials for an AD user tied to the group that was mapped to the Litmus Edge group.
- Click Internal and select the AD LDAPS connection created in the configuration steps.
- Click Log In and confirm user can log in Litmus Edge successfully.
Additional information:
- Reference this article for more information about LDAP queries: https://confluence.atlassian.com/kb/how-to-write-ldap-search-filters-792496933.html
- When entering information for Users and Groups, users can also filter by entering in the DN value of the User Search Base DN from AD. For example, if there is an Organizational Unit (OU) with the name, "manufacturing" and domain example.com, then users can enter in OU=manufacturing,DC=example,DC=com. Leaving the User Search Base DN at the domain level (for example, DC=example,DC=com) may yield too many results.
- Use tools such as Apache Directory Studios or ldap-utils on Linux machines to help browse configuration information of the AD server to help set accurate configurations for the Litmus Edge integration.
Test 5: Configure robust passwords
Confirm that Litmus Edge can configure robust password settings for locally created user accounts. Defining stronger password settings helps to reduce the risk of compromised accounts.
- Log in to Litmus Edge and go to System > Policy Management.
- Under the Password Policy settings confirm the following configuration:
- Minimum password length: 10
- Maximum password length: 20
- Minimum uppercase characters: 2
- Minimum lowercase characters: 2
- Minimum number of digits: 2
- Special characters: !@#$
- Minimum special characters: 2
Note: These settings are for testing purposes only. These are not the recommended settings.
- Click Save Policy followed by Yes, change policy.
To verify, perform the following steps: - Navigate to System > Users and click the + Add New button.
- Enter the information for a test user.
- Under Enter Password type in the following passwords listed below.
- Password: password, and Output contains:
- "Should contain at least 2 capital letters."
- "Should contain at least 2 numbers. Your password contains 0"
- "Should be at least 10 characters long"
- "Should container at least 2 special characters"
- Password: PASSWOR12345678912345, and Output contains:
- "Should contain at least 2 lowercase letter."
- "Should be at most 20 characters long."
- Password: password, and Output contains:
- Enter in a password that satisfies the requirement (example: P@$dw0rD12) and verify that the password requirements are met so that the user can be created.
- Log out and log in as the test user.
- Click the user icon at the upper right and select Reset Password.
- Enter in the Current Password and the same password into the New Password field.
- Verify that the output states New password and current password must be different. Note: If attempting to change test user password with the current password in the Users settings, the update does not go through.
Test 6: Configure RBAC settings
There is an administrator account available to use and test with. Confirm that LE can define groups with specified permissions. Validate that the configured permissions are working correctly. Note that this test does not validate every set of permission settings but rather tests the overall functionality. LE comes with three predefined roles: administrator, developer, and observer.
- Log in to Litmus Edge and go to System > Users.
- Click the + Add User button.
- Enter in the settings below to create a user for the Observer role:
- First name: Test
- Last name: Observer
- Username: observer
- Enter Password/Confirm Password:<password>
- Role: Observer
- Click Add User.
- Click the + Add User button.
- Enter in the settings below to create a user for the Developer role:
- First name: Test
- Last name: Developer
- Username: developer
- Enter Password/Confirm Password: <password>
- Role: Developer
- Click Add User.
- Click the + Add User button.
- Enter in the settings below to create a user for the Administrator role:
- First name: Test
- Last name: Administrator
- Username: administrator
- Enter Password/Confirm Password: <password>
- Role: Developer
- Click Add User.
To verify, perform the following steps: - Log out and log in with user: observer.
- Accept the License Agreement and change the password if prompted.
- Confirm role functionality for Observer:
- Go to Device Hub. Confirm that user can see device but is not able to add a device.
- Go to System. Limited options are available to the user. For example, there is no Backup/Restore or LDAP/AD Auth option.
- Go to System > Network > Interfaces and click Update. User is denied access.
- Log out and log back in with user: developer
- Accept the License Agreement and change the password if prompted.
- Confirm role functionality for Developer:
- Navigate to Device Hub. User can see existing devices and is able to create a new device.
- Navigate to System. Limited options available to user. For example, there is no Backup/Restore or LDAP/AD Auth option.
- Navigate to System > Network > Interfaces and click Update. User is denied access.
- Log out and log back in with the admin user (for example: The account used to create the roles).
- Confirm role functionality for Administrator:
- Go to Device Hub. User can see existing devices and is able to create a new device.
- Go to System. All options displayed. For example, there are options for Backup/Restore or LDAP/AD Auth.
- Go to System > Network > Interfaces and click Update. Configuration prompt appears.
Note: When integrating with AD or another LDAP based server, map the three LE roles to the applicable AD/LDAP roles. To do this, navigate to System > LDAP/AD Auth. Click on the three-dot symbol next to the LDAP entry and click Map Groups to Roles. The left side is the LDAP group (for example, from AD) and on the right is the LE predefined roles.
Note: For a full list of permissions per LE predefined user roles, see https://docs.litmus.io/litmusedge/users (requires login).
Test 7: View application logs
There is an existing test user on the system. Validate the capability of LE to audit/log actions taken on the system such as successful or failed login attempts or system configuration changes. This is critical in keeping users accountable for their actions and for any potential investigations into suspicious activity.
- Log in to LE.
- Go to System > Users.
- Click the + Add User button.
- Enter in settings to create a test user and click Add User.
To verify, perform the following steps: - Go to System > Events > Event History.
- Validate there are at least two events:
- User created
- User logged in
Test 8: Sending logs to centralized logging server
- Splunk is deployed on the network with a HEC configured and using SSL.
- There is an active device added to Litmus Edge.
Validate the capability for LE to integrate with a central logging server. Specifically, Splunk will be used with the HTTP Event Collector (HEC) over an TLS-enabled connection using Litmus Edge's (LE) Splunk Integration. LE system events can also be sent over Syslog using UDP port 514. Splunk's HEC is the recommended method since the data is encrypted over the network.
- For HEC configuration, log in to LE and go to Integration.
- Click the + Add a connector button.
- Under Provider, select Splunk.
- Fill out the Splunk integration settings for the Splunk HEC.
- Name: <Descriptive name>
- Hostname:<FQDN/IP of Splunk>
- Port: 8088 (Default port)
- Use SSL: Leave enabled
- Endpoint: services/collector/event (Default)
- Token: <Splunk HEC Token>
Note: The HEC token can be found in Splunk by going to Settings > Data Inputs > HTTP Event Collector.
- Click Add.
- On the integration page, click the new Splunk integration tile.
- Go to Topics.
- Click the + Add a new subscription button.
- On the Data Integration page, fill out the settings per the example below:
- Local Data Topic: system.events
- Remote Data Topic: services/collector/event (default)
- Click Enable and then OK.
- Go back to the Integration page and click the toggle button on the Splunk integration tile to enable it.
- For Syslog configuration, log in to LE and navigate to Flows Manager.
- Click the Go to Flow Definition on a new or existing Flow.
- Add a udp out node on to the Flow.
- Add a Datahub Subscribe node on the Flow.
- Double-click in to the Datahub Subscribe node and edit the following settings:
- Datahub: <Select existing or create a new one with default settings>
- Topic: system.events
- Click Done.
- Double-click into the udp out node and edit the following settings:
- Send a: udp message
- To port: 514 (default Syslog)
- Address: <Splunk FQDN/IP>
- Click Done.
- Connect the Datahub Subscribe node to the udp out node and click Deploy.
To verify, perform the following steps: - In Litmus Edge, go to DeviceHub > Tags.
- Add a test tag or delete a test tag to generate a system event.
- Log in to Splunk and go to Search & Reporting.
- Enter in the filter: host="<IP address of LE>"
- Confirm messages are being received from Splunk with details about Tag events. Example: eventId: tags.added
Test 9: Connecting to NTP server
Part of an effective audit/logging system is to have time synchronized across devices on the network. This helps when correlating events across a range of device logs. Validate that Litmus Edge can successfully connect to an NTP server.
- Log in and go to System > Network > DNS/NTP Servers.
- Under the NTP Servers section, in the Add NTP Server field, enter in the NTP server IP address or FQDN and press Add.
- Click Yes to authorize the change.
Confirm that Device Time at the top of the page is accurately reflected. Note: If refreshing the browser does not update the time, try logging out and back into Litmus.
Test 10: Litmus Edge to Litmus edge Manager secure connection
- LE and LEM nodes are configured and deployed and able to communicate over the network.
- LEM's signing CA certificate is available to LE.
Validate a secure connection between Litmus Edge and Litmus Edge Manager using CA signed certificates, specifically on LEM. The secure connection is created using HTTPS. Other secure protocols such as WireGuard and MQTT over TLS are used for other functions such as data aggregation and remote UI access.
- Log in to LEM Web UI and go to the test Project.
- Go to Activation > Configuration and click +.
- Leave defaults and click SAVE.
- Scroll back to the top and copy the Activation Code.
- Log in to LE and go to System > Device Management.
- Click Edit and enter in the endpoint information under the activation code (https://<LEM-IP/FQDN).
- Click Set. User should be prompted with LEM's CA signed certificate. Click Yes.
- Paste in the Activation Code in the Cloud Activation box.
- Click Activate. Close the confirmation window.
To verify, perform the following steps: - Back on LEM, navigate to Activation > Requests.
- Under Action, click the three dot icon and click Approve.
- Go to Edge Devices and confirm the presence of the LE node.
- Click the name of the LE instance and then navigate to the DETAILS tab. Confirm details about the LE instance are accurately populated.
- Go back (press the < button) and click the Open Litmus Edge UI button. Confirm that a new tab is open to the LE login page and that the user can log on.
Test 11: Secure MQTT data transfer between Litmus Edge and Litmus Edge Manager
- LE and LEM are configured and deployed on the network and have been successfully connected. See the following test case for more information: Test 10: Litmus Edge to Litmus edge Manager secure connection.
- There is a Device in Litmus Edge that is actively generating data.
Validate that Litmus Edge nodes that are connected and managed by Litmus Edge Manager can securely send and aggregate data at LEM. Specifically, this test case validates that a MQTT over TLS connection can be used to transfer LE simulator data to LEM. Per the prerequisite, this requires that the testing LE instance has already been added to LEM which automates the creation of a MQTT over TLS integration on LE.
- Log in to the connected Litmus Edge (LE) host and go to Integration.
- Click the toggle button on the default-ssl integration tile to enable the connection (this is the integration automatically added to LE from the integration with LEM).
- Click somewhere within the tile to navigate to the Integration settings.
- Click Topics on the left side.
- Click the + Add a new subscription button.
- Select the local LE topic for the Device that is actively generating data (click the Search button or enter in the LE topic manually).
- Optionally enter a Description, select Enable, and click OK.
To verify, perform the following steps: - Log in to the LEM node, go to the appropriate company and project.
- Select Edge Devices and click the name of the test LE instance.
- Go to the MQTT tab. Confirm Connection state is listed as Connected.
- Click the Subscribe button.
- Confirm that LEM is receiving data from the LE node (messages start to appear with a timestamp and payload value).
LEM hardening
The following settings have been validated on LEM version 2.3.
Test 1: Load CA signed certificates
- Access to a system that can run openssl commands.
- Ability to get certificates signed by a CA.
Confirm that CA signed certificates can be used by Litmus Edge Manager during operations. This adds a layer of trust for when communicating with LEM (for example, when accessing the HTTPS interface). The end user can be assured that the certificate was signed by a trusted party. This test uses a custom testing CA to sing certificates. LEM supports other methods such as using Let's Encrypt certificates. - Start by creating a CSR and key pair using the openssl command which can be run on a Linux machine. Example command: openssl req -newkey rsa:2048 -nodes -keyout <key-name>.key -out <csr-name>.csrNote: It will be useful to change the hostname of LEM which can be done using Linux operating system commands such as using the hostnamectl command-line utility. The FQDN/hostname should be used as the CN value in the CSR prompts.
- Sign the CSR with a trusted CA and obtain the signed certificate.
- Transfer the signed certificate, certificate key file, and CA signing certificate to a location with access to a web browser that can access LEM.
- Log in to the LEM Admin Console (https://<LEM-IP>:8446) and navigate to Settings.
- Next to the SSL settings section choose User Defined.
- For SSL certificate click the three dots to upload the CA signed LEM certificate.
- For Key file click the three dots to upload the key for the LEM certificate.
- Click Save.
To verify, perform the following steps: - Reload the web page.
- Using the browser settings, view the contents of the certificate being used by LEM.
- Validate that the information is correct, especially the Issued By fields which should list the test CA.
Test 2: Integrate with AD over LDAPS
LEM's Keycloak instance trusts the issuer(s) of the AD server. Validate that Litmus Edge Manager can integrate with an Active Directory server over LDAP using TLS. This enables central management of users and protects the confidentiality of the authentication data when using LDAPS instead of regular LDAP.
- Log in to LEM's Keycloak (https://<LEM-IP>/auth/admin).
- Navigate to User Federation and select ldap.
- Set Vendor to Active Directory.
- Fill out the information according to the target AD server.
- Use tools such as AD Explorer (https://learn.microsoft.com/en-us/sysinternals/downloads/adexplorer) to help determine what attributes to use in the Keycloak settings.
- This test verifies LDAP over TLS. Set Connection URL to: ldaps://<AD-FQDN>:636 (636 is the default LDAPS port).
- Per the prerequisite, Keycloak must trust the issuer of the AD server's certificate. Run the command below to import the CA certificate into the Keycloak truststore. The service/LEM may need to be restarted afterwards.
sudo keytool -import -alias <alias> -cacerts
-storepass <truststore-password> -noprompt
-trustcacerts -file </path/filename.crt>
- Click Test connection and Test authentication to ensure that the parameters are entered in correctly.
- At the bottom of the page, click Synchronize all users. There should be a success message at the top with the number of importer users.
To verify, perform the following steps: - Within Keycloak, go to Users.
- Click View all users.
- Confirm that the table populates with the users from AD.
- Log in to the LEM Admin Console and go to Users.
- Confirm that the AD users are listed on the page.
- Choose one of the AD users and click the username.
- Under Company Level Teams, click the + button and select an existing company.
- Select a Team and click Save.
- Go to the LEM Web UI and attempt to log in with the AD user.
- Confirm they can log in using AD username/password and can view the assigned Company.
- Click the Project pane which takes the user to the Project Dashboard.
- Select Features and click on the Grafana tile.
- Confirm a new window is open for Grafana and that the logged in user is the AD user (click the avatar icon on the bottom left side of the Grafana UI).
- Back on the Features page on LEM clicks on Marketplace.
- Confirm the user is successfully able to access the Marketplace Catalog UI and navigate around.
Test 3: Configure multifactor authentication
- User has an OTP/Token authenticator app such as FreeOTP.
- LEM is configured with the correct time.
- Test user available on LEM.
Validate LEM's capability to use two-factor authentication. This enhances access control where users have to use something they know and something they have in order to authenticate into LEM.
- Log in to LEM as a test user.
- Select the user icon at the top and select Profile.
- Select Authenticator.
- Use test phone and install FreeOTP.
- On FreeOTP select the barcode icon to scan the barcode presented by LEM.
- Choose a custom icon and tap Next.
- Click Next until taken to the token. A six-digit icon should appear.
- Back on LEM, enter the code from FreeOTP in the One-time code field.
- Enter in a name for the device for Device Name and click Save.
To verify, perform the following steps: - Log out of the test user and attempt to log in again.
- Confirm the user is prompted for a One-time code after entering in the correct credentials.
- Enter in the FreeOTP code and press Log In.
- Confirm user successfully logs in.
Test 4: Configure RBAC settings
There is at least one test user. Confirm that LEM can define groups with specified permissions. Validate that the configured permissions are working correctly. Specifically for this test case, Teams for specific Companies will be created and tested with read/write permissions.
- Log in to the LEM Admin Console and go to Users.
- Click the + icon for the Company Teams section.
- Configure the settings below:
- Team Name: Observers
- Company: <select existing test company>
- Click Save.
- Click the + icon for the Project Teams section.
- Configure the following settings:
- Company:<select existing test company>
- Project: <select existing project>
- Team: Observers
- Role: Read
- Click Save.
- Repeat steps 3 to 7 but change the following values:
- Company Teams > Team Name: Writers
- Project Teams > Team: Writers
- Project Team > Role: Write
- Repeat steps 3 to 7 but change the following values:
- Company Teams > Team Name: No access
- Project Teams > Team: No access
- Project Team > Role: N/A
To verify, perform the following steps: - On the Users page, click an existing test user (or create one).
- Under Company Level Teams click the + icon.
- Configure the following settings:
- Company:<select existing test company>
- Team: Observers
- Click Save.
- Log out of LEM and log in to the LEM Web UI with the test user.
- Verify Observer user's authorization:
- User can log in.
- Go to Project List > Project > Sites > +ADD.
- Fill out information.
- Save.
- Confirm user is denied authorization.
- Repeat steps 1 to 6 for Writer permissions and replace the following values:
- User > Team: Writers
- Verify Writers user's authorization:
- User can log in.
- Go to Project List > Project > Sites > +ADD
- Fill out information.
- Save.
- Test site is created.
- Repeat steps 1 to 6 for No Access permissions and replace the following values:
- User > Team: No Access
- Verify Writers user's authorization:
- User cannot log in OR cannot navigate around (for example, If changed existing test user's permissions).
Test 5: View application logs
Validate the capability of LEM to log system events for actions taken on the LEM web UI. Examples of events are creating activation codes, adding or removing LE devices, and more.
- Log in to the LEM Web UI.
- Navigate Activation > Configuration.
- Click the + button.
- Click SAVE and then CLOSE.
- Confirm that the new activation code is listed in the Activation > Configuration page.
- Click the three dots next to the new activation code and select Remove.
- Click REMOVE on the prompt.
To verify, perform the following steps: - Go to Events.
- Confirm the following entries are listed in the system events:
- User: <user logged in with to carry out test case>. Event: Activation config update: code=null
- User: <user logged in with to carry out test case>. Event: Activation config deleted: code=<Code>
Test 6: Configure NTP server connection
Part of an effective audit/logging system is to have time synchronized across devices on the network. This helps when correlating events across a range of device logs. Validate that Litmus Edge can successfully connect to an NTP server.
- SSH into the LEM host.
- Run the following command to enable NTP:
#timedatectl set-ntp true - Edit the timedatectl file to specify the NTP server:
- Edit the file: /etc/systemd/timesync.conf
- Uncomment the "NTP" line and set it to the target NTP server.
NTP=<NTP server IP address/FQDN>
- Restart the timedatectl service.
#sudo systemctl restart systemd-timesyncd.service - Confirm that the timedatectl service is synchronized to the NTP server:
#systemctl status systemd-timesyncd.service - Confirm the output lists status as: Synchronized to time server 172.19.111.254:123 (172.19.111.254).
To verify, perform the following steps: - Log in LEM Web UI and navigate to a Company > Project.
- To generate an event, go to Activation > Configuration.
- Click + Add activation config button to add a new activation code.
- Click SAVE at the bottom.
- Navigate to Events.
- Confirm that there is an event created for the creation of the activation code.
- Take note of the time and compare to the time on the LEM host. Verify they align:
#timedatectl
Note: Ensure that both the LEM UI and host operating system are on the same time zone (for example, UTC).
Litmus Edge IDMZ architecture and validation
The following Litmus Edge IDMZ architecture and security validation use cases have been tested on Litmus Edge version 3.2 and Litmus Edge Manager version 2.3.
Use case: Connecting Litmus Edge to Litmus Edge Manager
LEM may be deployed outside the plan floor/control network for use cases such as aggregating LE data from different geographically located factories. These firewall rules validate secure LE to LEM connection through an IDMZ. In this scenario, an LE host is deployed in the IDMZ subnet as a proxy for plant floor LE hosts. The proxy LE aggregates data from the plant floor LE instances and then has a connection the LEM instance on the IT/Enterprise network. NATS is used as the protocol to transfer data between the OT and proxy LE instances.
Figure 180. Litmus Edge IDMZ security architecture in the Purdue Model 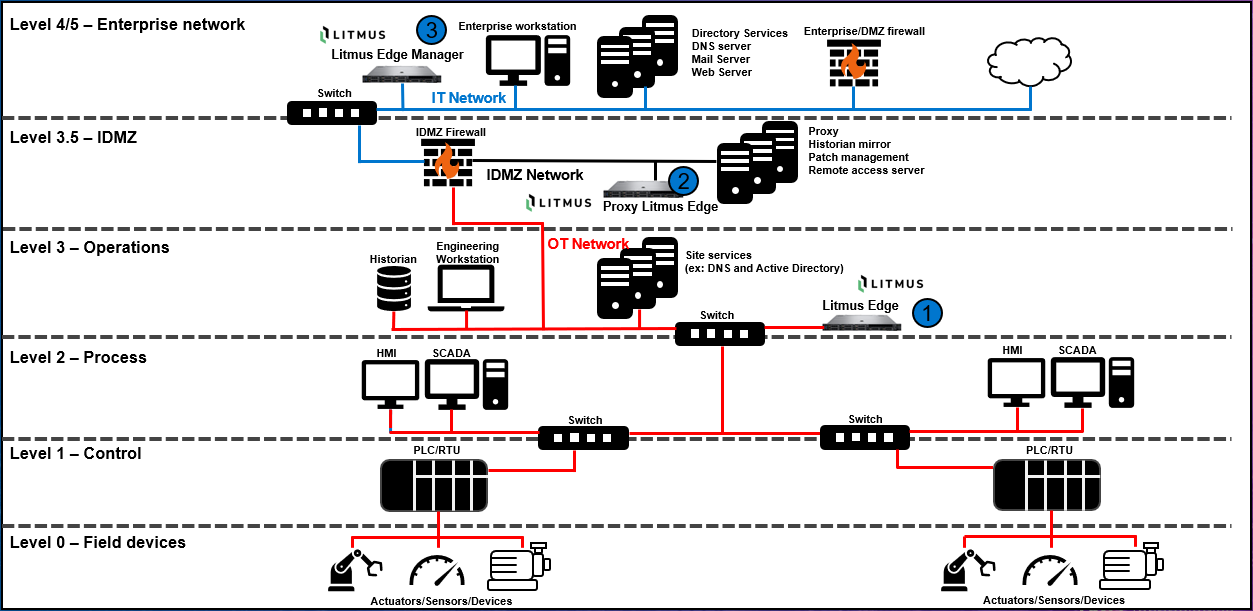
Table 18. Litmus to Litmus Edge Manager: Validated firewall rules Description Source network Source device Destination network Destination device Port Application Allow OT LE instance to send data to Proxy LE hosted on the IDMZ network using NATS. OT Plant Floor Litmus Edge (1) IDMZ Proxy Litmus Edge (2) TCP 4222 SSL, Unknown-TCP1 Allow Proxy LE to connect to LEM for sending data and for LEM remote control of LE host. IDMZ Proxy Litmus Edge (2) IT LEM (3) TCP 443, TCP 8883, TCP 8445, UDP 51820 SSL, Unknown-UDP2 1 At the time of this testing, the application signature was not fully recognized. NATS is used as part of this communication thread.2 At the time of this testing, the application signature was not fully recognized. WireGuard VPN and MinIO are some of the tools used in the communication threads. Consult official LEM documentation for more information.Use case: Connecting Litmus Edge to SDP deployed at the datacenter
SDP may be deployed on the IT network for data aggregation purposes. This use case provides validated guidance on how to securely transport LE data from the OT network to SDP hosted on the IT network. There are two LE instances in this use case, one that collects data on the OT network, and a proxy instance that aggregates LE data from the OT network and sends it to SDP. NATS is used as the protocol to transfer data between the OT and proxy LE instances.
For guidance on how to configure LE forwarding over NATS, reference Configure Litmus Edge to forward data to another Litmus Edge instance.
Figure 181. LEM and SDP IDMZ security architecture in the Purdue Model 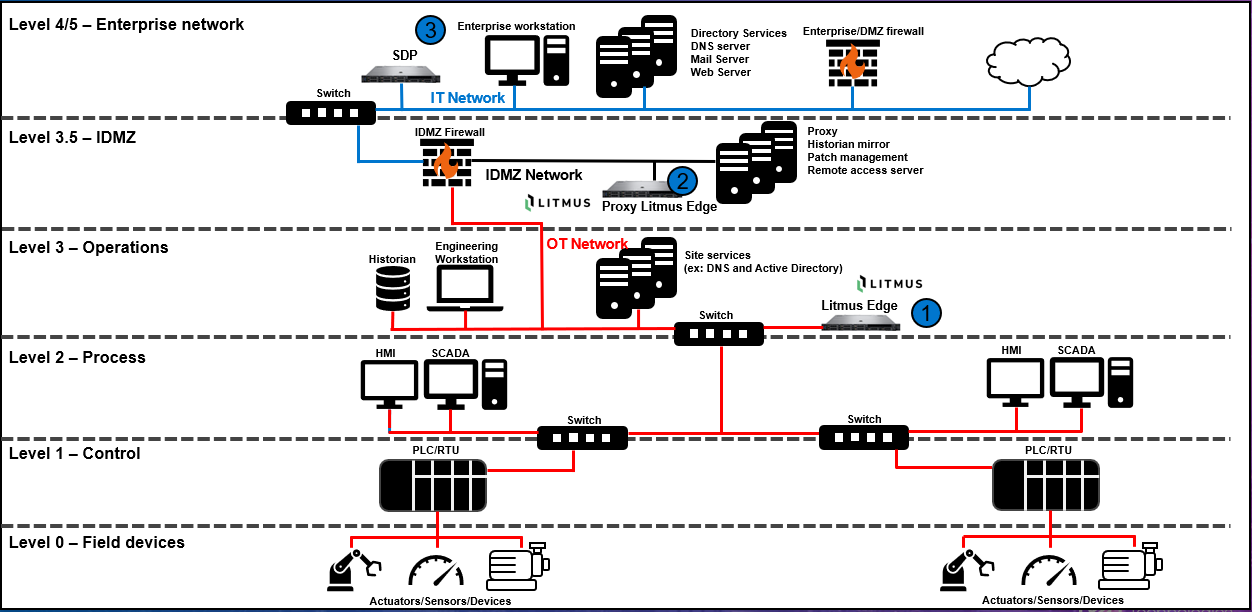
Table 19. Litmus to SDP: Validated firewall rules Description Source network Source device Destination network Destination device Port Application Allow OT LE instance to send data to Proxy LE hosted on the IDMZ network using NATS. OT Plant Floor Litmus Edge (1) IDMZ Proxy Litmus Edge (2) TCP 4222 SSL, Unknown-TCP1 Allow Proxy LE to connect to SDP MQTT broker using MQTT over TLS. IDMZ Proxy Litmus Edge (2) IT SDP (3) TCP 8883 SSL 1 At the time of this testing, the application signature was not fully recognized. NATS is used as part of this communication thread.
