

The power of cyber resiliency at your core
Thu, 26 Jan 2023 21:34:59 -0000
|Read Time: 0 minutes
At Dell Technologies, we often talk about how security is ingrained into our product DNA. What we mean is that security is never an afterthought — it’s never something that we build on after the product itself is complete.
Instead — and our Secure Development Lifecycle (SDL) is a key part of this — we continually design our products with past, current and future security threats in mind. And we supplement secure product development with external audits and continuous testing and evaluation to find and remedy vulnerabilities that do occur.
Dell’s commitment to customers
Attacks on the infrastructure layer, especially the firmware, are on rise. According to a Microsoft Security Signals report, more than 83% of enterprises have experienced at least one firmware attack in the past two years.
At Dell, we understand that securing the infrastructure layer is fundamental to protecting any IT environment against modern threats. Our cyber-resilient infrastructure has security built into every phase starting from the supply chain to the operation and eventual retirement of products. We are also committed to making sure any vulnerabilities or exposures found in the field, that could impact our products, get mitigated through rapid response on our end.
Let’s talk about how we secure our PowerEdge servers.
Cyber resiliency is key
Modern server platforms are highly complex, with hundreds of components — a lot of which require firmware for configuration and management of the component during the boot process and operation of the server.
Given the complexity of today’s platforms and the level of sophistication of cyberattacks, we recognize that it is not possible to prevent 100% of attacks. Some breaches are inevitable, especially when it comes to new devices and firmware, for example. Cyber resiliency — the ability to anticipate, withstand and recover from attacks — is therefore fundamental to surviving in this threat landscape.

At Dell, we use the NIST framework of Protect, Detect and Recover to guide our resiliency efforts. At the same time, the process of identifying and designing these capabilities is done through the zero-trust approach — with a focus on increasing the granularity of controls and checks in the systems — and by anticipating how our customers will want to use these capabilities while they are setting up their zero-trust IT environments and deployments.
Cyber resiliency built into PowerEdge
Dell PowerEdge servers offer cyber-resilient infrastructure by anchoring platform integrity to a silicon-based Root of Trust and using automated features to continuously protect the system during its operation.
Root of Trust: PowerEdge offers end-to-end boot resilience by enabling UEFI secure boot, which is anchored in our silicon-based platform Root of Trust. This immutable Root of Trust is the starting point of the chain of trust used to cryptographically authenticate the different pieces of firmware that get loaded on PowerEdge servers. Our secure boot helps to make sure that the firmware is coming from a trusted source and has not been tampered with in any way.
UEFI certificate customization: PowerEdge servers provide capabilities for complete customization of UEFI secure boot, giving system owners an option to avoid relying on third-party industry keys and industry certificate authorities. The NSA has recognized that fully customized UEFI secure boot offers the highest level of security and provides the best protection against threats. And it’s important to note that Dell was the first server vendor to provide these capabilities to customers.
CPU security
In addition to fully customizable UEFI secure boot, PowerEdge servers offer a complementary layer of protection against things like sleep attacks by enabling Intel Boot Guard and AMD Platform Secure Boot features. These features add robustness to the chain of trust process by verifying the firmware before it gets executed on the processor and eliminating attacks between time of check by UEFI secure boot and time of use of the firmware on the processor.
Drift detection: Beyond assuring boot integrity, PowerEdge can also lock down the system configuration and automatically detect drift in firmware versions and the configuration of the system. If drift is detected, PowerEdge can respond by automatically initiating rollback of the firmware and OS to a “known good” version.
Through these features, PowerEdge servers offer end-to-end boot resilience by protecting against attacks on the firmware, detecting any ongoing attack on firmware and/or system configuration, and automatically recovering from attacks by rolling the system configuration and firmware back to a safe, verified version. What’s also important to note is that this happens with no manual intervention at machine speed, which is critical for minimizing system downtime.
But Dell goes even further
When it comes to the firmware, it's important to reiterate that Dell is committed to providing rapid response and mitigation to CVEs. What you might not know is that the majority of attacks occur because known vulnerabilities are not being patched in the field.
We don’t want to leave our customers vulnerable, which is why we’re always working to improve our service-level agreements (SLA) for updates and patches that help mitigate new threats as quickly as possible.
Resiliency is just one small facet of Dell’s overall security stance. Take time to learn more about what we’re doing to protect your devices, your data, and your business. PowerEdge, like the rest of the Dell fleet of products, has a broad feature set that goes beyond resiliency — and is capable of meeting your risk tolerance requirements and regulatory and compliance needs.
Find additional resources on Dell Technologies Info Hub.
Related Blog Posts

The power of cyber resiliency at your core
Wed, 19 Oct 2022 21:10:14 -0000
|Read Time: 0 minutes
At Dell Technologies, we often talk about how security is ingrained into our product DNA. What we mean is that security is never an afterthought — it’s never something that we build on after the product itself is complete.
Instead — and our Secure Development Lifecycle (SDL) is a key part of this — we continually design our products with past, current and future security threats in mind. And we supplement secure product development with external audits and continuous testing and evaluation to find and remedy vulnerabilities that do occur.
Dell’s commitment to customers
Attacks on the infrastructure layer, especially the firmware, are on rise. According to a Microsoft Security Signals report, more than 83% of enterprises have experienced at least one firmware attack in the past two years.
At Dell, we understand that securing the infrastructure layer is fundamental to protecting any IT environment against modern threats. Our cyber-resilient infrastructure has security built into every phase starting from the supply chain to the operation and eventual retirement of products. We are also committed to making sure any vulnerabilities or exposures found in the field, that could impact our products, get mitigated through rapid response on our end.
Let’s talk about how we secure our PowerEdge servers.
Cyber resiliency is key
Modern server platforms are highly complex, with hundreds of components — a lot of which require firmware for configuration and management of the component during the boot process and operation of the server.
Given the complexity of today’s platforms and the level of sophistication of cyberattacks, we recognize that it is not possible to prevent 100% of attacks. Some breaches are inevitable, especially when it comes to new devices and firmware, for example. Cyber resiliency — the ability to anticipate, withstand and recover from attacks — is therefore fundamental to surviving in this threat landscape.

At Dell, we use the NIST framework of Protect, Detect and Recover to guide our resiliency efforts. At the same time, the process of identifying and designing these capabilities is done through the zero-trust approach — with a focus on increasing the granularity of controls and checks in the systems — and by anticipating how our customers will want to use these capabilities while they are setting up their zero-trust IT environments and deployments.
Cyber resiliency built into PowerEdge
Dell PowerEdge servers offer cyber-resilient infrastructure by anchoring platform integrity to a silicon-based Root of Trust and using automated features to continuously protect the system during its operation.
Root of Trust: PowerEdge offers end-to-end boot resilience by enabling UEFI secure boot, which is anchored in our silicon-based platform Root of Trust. This immutable Root of Trust is the starting point of the chain of trust used to cryptographically authenticate the different pieces of firmware that get loaded on PowerEdge servers. Our secure boot helps to make sure that the firmware is coming from a trusted source and has not been tampered with in any way.
UEFI certificate customization: PowerEdge servers provide capabilities for complete customization of UEFI secure boot, giving system owners an option to avoid relying on third-party industry keys and industry certificate authorities. The NSA has recognized that fully customized UEFI secure boot offers the highest level of security and provides the best protection against threats. And it’s important to note that Dell was the first server vendor to provide these capabilities to customers.
CPU security
In addition to fully customizable UEFI secure boot, PowerEdge servers offer a complementary layer of protection against things like sleep attacks by enabling Intel Boot Guard and AMD Platform Secure Boot features. These features add robustness to the chain of trust process by verifying the firmware before it gets executed on the processor and eliminating attacks between time of check by UEFI secure boot and time of use of the firmware on the processor.
Drift detection: Beyond assuring boot integrity, PowerEdge can also lock down the system configuration and automatically detect drift in firmware versions and the configuration of the system. If drift is detected, PowerEdge can respond by automatically initiating rollback of the firmware and OS to a “known good” version.
Through these features, PowerEdge servers offer end-to-end boot resilience by protecting against attacks on the firmware, detecting any ongoing attack on firmware and/or system configuration, and automatically recovering from attacks by rolling the system configuration and firmware back to a safe, verified version. What’s also important to note is that this happens with no manual intervention at machine speed, which is critical for minimizing system downtime.
But Dell goes even further
When it comes to the firmware, it's important to reiterate that Dell is committed to providing rapid response and mitigation to CVEs. What you might not know is that the majority of attacks occur because known vulnerabilities are not being patched in the field.
We don’t want to leave our customers vulnerable, which is why we’re always working to improve our service-level agreements (SLA) for updates and patches that help mitigate new threats as quickly as possible.
Resiliency is just one small facet of Dell’s overall security stance. Take time to learn more about what we’re doing to protect your devices, your data, and your business. PowerEdge, like the rest of the Dell fleet of products, has a broad feature set that goes beyond resiliency — and is capable of meeting your risk tolerance requirements and regulatory and compliance needs.
Find additional resources on Dell Technologies Info Hub.
Future-Proof Your Data: Airgap Your Business Continuity Dataset
Thu, 02 May 2024 17:49:35 -0000
|Read Time: 0 minutes
In today's digital age, the ransomware threat looms larger than ever, posing a significant risk to businesses worldwide. As someone deeply entrenched in the intricacies of data protection, I've seen firsthand how devastating data breaches can be. It's not just about the immediate loss of data: the ripple effects can disrupt business operations for weeks, if not months. Interestingly, while nearly 91% of organizations use some form of data backup, a staggering 72% have had to recover lost data from a backup in the past year. This highlights the critical need for robust business continuity plans that go beyond simple data backup.
With the rate of new business failures varying significantly by location, the importance of being prepared cannot be overstated. For instance, in the District of Columbia, 28% of businesses fail in their first year, partly due to inadequate data protection strategies. I aim to shed light on how a well-crafted business continuity dataset can protect your company against ransomware attacks. By understanding common pitfalls and leveraging PowerScale’s Cyber Protection Suite, businesses can ensure that their data remains secure and accessible in an airgap, even in the face of unforeseen disasters.
Understanding ransomware attacks and their impact on business continuity
Ransomware attacks are not just a temporary disruption but a significant threat to a company's ongoing ability to conduct business. As a cybersecurity enthusiast committed to sharing valuable insights, I've seen firsthand how these attacks can dismantle a business's operations overnight. It's crucial for organizations to understand the ramifications of ransomware and to implement strategies that mitigate these risks. Let’s delve into the cost of ransomware to businesses and examine some case studies that highlight the importance of being prepared.
The cost of ransomware to businesses
The financial implications of ransomware attacks on businesses are staggering. Beyond the demand for ransom payments, which can reach millions of dollars, hidden costs can be even more detrimental. I've seen businesses suffer from prolonged downtime, loss of productivity, and irreversible damage to their reputation. According to recent cybersecurity reports, businesses attacked by ransomware often face comprehensive audits, increased insurance premiums, and, in some cases, legal liabilities due to compromised data.
Moreover, the recovery process incurs significant IT expenditures, including forensic analysis, system upgrades, and employee training. With organizations being attacked by ransomware every 14 seconds, the urgency for resilient data protection strategies is clear. Understanding these costs underlines the importance of investing in proactive cybersecurity measures, underscoring that the expense of prevention pales when compared to the costs of recovery.
Recent ransomware attacks
In September 2023, the MGM Grand Hotel in Las Vegas, Nevada faced a significant ransomware attack that had widespread repercussions. The attack targeted MGM Resorts International properties across the U.S. Operational disruptions were severe, including the disabling of online reservation systems, malfunctioning digital room keys, and affected slot machines on casino floors. MGM Resorts’ websites were also taken down. The financial impact was substantial, costing the company approximately $100 million due to operational disruptions and recovery efforts. The perpetrators behind this attack were the ALPHV group (also known as BlackCat), which is believed to have links to the Russian government.
Also in September 2023, further down the Las Vegas Strip, Caesars Entertainment, one of the world’s largest casino companies, fell victim to a ransomware attack. The attack targeted their systems, resulting in unauthorized access to their network. The hackers exfiltrated data, including many customers’ driver’s licenses and Social Security numbers. Caesars confirmed the breach and subsequently paid a multi-million-dollar ransom to the cybercriminals.
These attacks serve as a stark reminder that even seemingly impenetrable organizations can fall victim to sophisticated cyber threats.
Key elements of effective business continuity plans
As I delve deeper into the significance of business continuity planning for mitigating ransomware risks, it's crucial to outline the key elements that make these plans effective. First and foremost, a comprehensive risk assessment stands at the foundation. It enables businesses to identify potential vulnerabilities and ransomware threats, ensuring that all angles are covered. Next, comes the development of a robust incident response plan. This detailed guide prepares organizations to react swiftly and efficiently during a ransomware attack, minimizing operational disruptions and financial losses.
Another essential component is securing data backups. These backups must be regularly stored in an airgap to prevent them from becoming ransomware targets. Communication plans must also be in place to ensure transparent and timely information sharing with all stakeholders during and after a ransomware incident. Lastly, continuous employee training on cybersecurity best practices helps strengthen the first line of defense against ransomware attacks.
Incorporating ransomware preparedness into business continuity plans
Incorporating ransomware preparedness into business continuity plans is not just an option — it's a necessity in today's digital age. To start, adjusting the incident response plan specifically for ransomware involves identifying the most critical assets and ensuring they are protected with the most robust defenses. This can include employing advanced threat detection tools and securing endpoints to limit the spread of an attack.
Next, understanding the specific recovery requirements for key operations is vital. It involves establishing clear recovery time objectives (RTOs) and recovery point objectives (RPOs) for all critical systems. This guides the priority of system restorations to ensure that the most essential services are brought back online first, to minimize the business impact.
Testing the business continuity plan against ransomware scenarios on a regular basis is indispensable. Simulated attacks provide invaluable insights into the effectiveness of the current strategy and reveal areas for improvement. It ensures that when a real attack occurs, the organization is not caught off guard.
How an airgap protects your data
An airgap, also known as an air wall or air gapping, is a network security measure employed on one or more computers to ensure that a secure computer network is physically isolated from unsecured networks, such as the public Internet or an unsecured local area network. This strategy seeks to ensure the total isolation of a given system electromagnetically, electronically, and physically. An airgapped computer or network has no network interface controllers connected to other networks, with a physical and logical airgap.
For example, data on a PowerScale cluster in an airgap is fully protected from ransomware attacks, because the malware does not have access to it. In the following figure, the PowerScale cluster resides in the Cyber Recovery Vault, which has no access to the outside world.
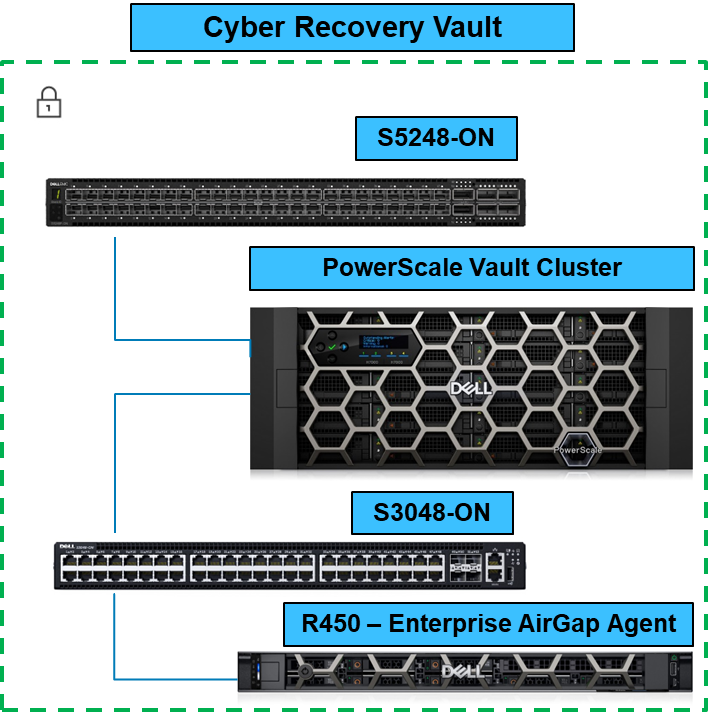
When the Business Continuity Dataset is copied to the PowerScale Vault Cluster, it is completely airgapped from the outside world. You can configure the solution to check for new dataset updates or simply have it remain as a vault.
In this blog, I explained how to airgap a PowerScale cluster. In future blogs, I’ll cover the entire PowerScale Cyber Protection Suite. For more information about the PowerScale Cyber Protection Suite, be sure to see PowerScale Cyber Protection Suite Reference Architecture | Dell Technologies Info Hub.
Author: Aqib Kazi Senior Principal Engineering Technologist




