-
All PowerStoreOS versions support NFSv3 through NFSv4.1 and Secure NFS. Starting with PowerStoreOS 3.0, basic support for NFSv4.2 in compatibility mode is also available.
Each NAS server has options to enable NFSv3 and NFSv4 independently. Support for advanced NFS protocol options is also available. Table 3 shows a list of NFS protocol options, where they are configured, and the default setting for each option.
Table 3. NFS options
Protocol option
Level
Default
Secure NFS (with Kerberos)
NAS server
Disabled
Minimum Security
Share
Sys
Default Host Access
Share
No Access
NFSv4
NFSv4 is a version of the NFS protocol that differs considerably from previous implementations. Unlike NFSv3, this version is a stateful protocol, meaning that it maintains a session state and does not treat each request as an independent transaction without the need for additional preexisting information. This behavior is like Windows environments with SMB. NFSv4 brings support for several new features including NFS ACLs that expand on the existing mode-bit-based access control in previous versions of the protocol.
While PowerStore fully supports most of the NFSv4 and v4.1 functionality described in the relevant RFCs, directory delegation and parallel NFS are not supported.
To configure NFSv4, you must first enable NFSv4 on the NAS server, create a file system, and an NFS export. Then, the file system can be mounted on the host using the NFSv4 mount option.
Secure NFS
Traditionally, NFS is not the most secure protocol because it trusts the client to authenticate users, build user credentials, and send the user credentials in clear text over the network. With the introduction of secure NFS, Kerberos can be used to secure data transmissions through user authentication and data signing through encryption. Kerberos is a well-known, strong authentication protocol where a single key distribution center, or KDC, is trusted rather than each individual client. There are three different modes available on PowerStore:
- Kerberos: Use Kerberos for authentication only
- Kerberos With Integrity: Use Kerberos for authentication and include a hash to ensure data integrity
- Kerberos With Encryption: Use Kerberos for authentication, include a hash, and encrypt the data in-flight
To enable secure NFS, the following must be configured:
- DNS must be configured on the NAS server.
- A UNIX Directory Service (UDS) such as NIS, LDAP, or Local Files must be enabled.
- A Kerberos realm must exist.
If an Active Directory domain joined SMB server existed on the NAS server, that Kerberos realm may be leveraged. Otherwise, a custom realm can be configured for use in PowerStore Manager. LDAP over SSL (LDAPS) is used for Secure NFS to avoid weaknesses in the security chain. Although NFSv3 is supported with Secure NFS, it is preferable to use NFSv4 to maximize security.
Minimum security
The minimum security setting determines the type of security that is enforced on the NFS export. The default setting of Sys uses client-provided UNIX UIDs and GIDs for NFS authentication. If Secure NFS is enabled on the NAS server, the Kerberos options become available. For more information about the Secure NFS with Kerberos options, see the preceding section, Secure NFS.
Default host access
The default host access option determines the access permissions for all hosts that attempt to connect to the NFS export. The available options are:
- No Access (Default)
- Read/Write
- Read-Only
- Read/Write, allow Root
- Read-Only, allow Root
The allow root options are the equivalent to no_root_squash on UNIX systems. If the user has root access on the client, they are also granted root access to the NFS export.
For hosts that need different access than the default, they can be configured by adding hostnames, IP addresses, or subnets to the override list with one of the preceding access options. Multiple entries can also be added simultaneously in a comma-separated format. Table 4 shows the supported options when configuring NFS host access.
Table 4. NFS host access
Option
Example
Notes
Hostname
host1.dell.com
Hostname should be defined in the local hosts file, NIS, LDAP, or DNS.
IPv4 or IPv6 Address
10.10.10.10
fd00:c6:a8:1::1
Subnet
10.10.10.0/255.255.255.0
10.10.10.0/24
IP address/netmask or IP address/prefix
Netgroup
@netgroup
Netgroup should be defined in the local netgroup file or UDS. Netgroup entries should be prefixed with @ to differentiate them from hostnames
DNS Domain
*.dell.com
The DNS server must support reverse lookups and the ns.switch parameter should not exclude DNS. Domain entries should be prefixed with * and follow the Linux convention
Host access can also be configured by uploading a CSV file with a list of hosts and their respective access levels. PowerStore Manager provides a template with examples on the formatting and syntax for this file. This template can be downloaded from the system, edited, and then imported. When multiple NFS exports that require the same access configuration are configured, the same file can be imported multiple times and across multiple clusters as well. Once the file is imported, the newly imported hosts are appended to the access list. The following figure shows the host access configuration on an NFS export.
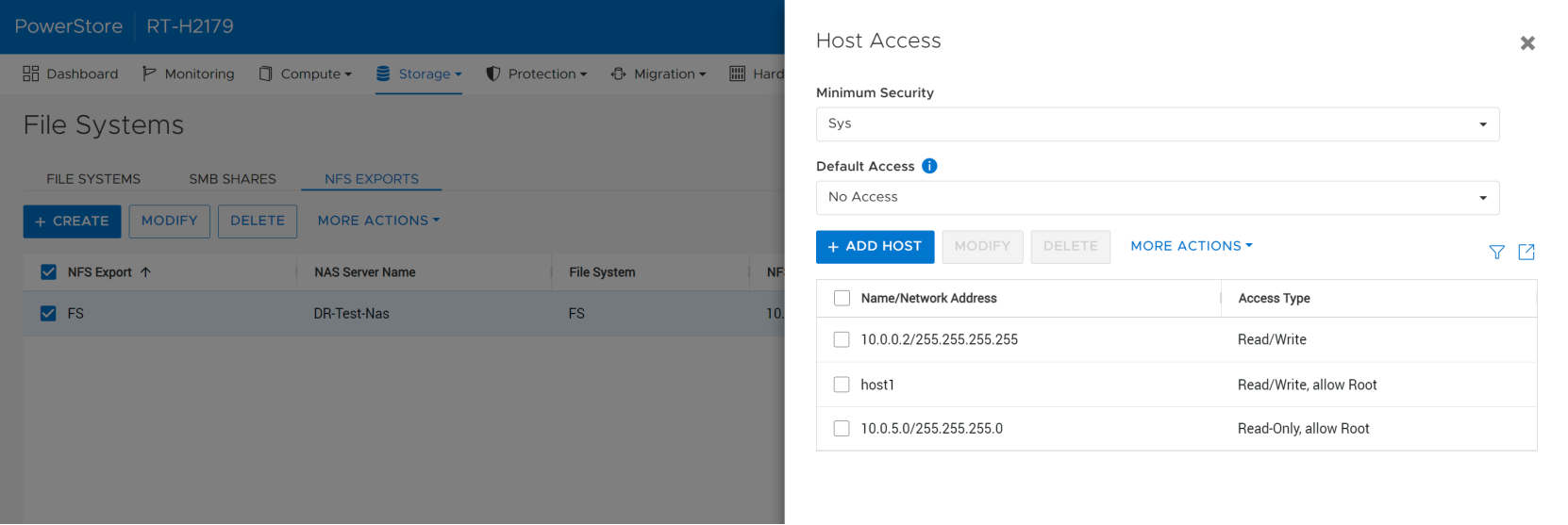
Figure 20. NFS host access configuration
