Home > Workload Solutions > SAP > Guides > SAP Data Intelligence on Dell Ready Stack for Red Hat OpenShift Container Platform 4.6 > SAP Data Intelligence Observer
SAP Data Intelligence Observer
-
SAP Data Intelligence Observer is a pod that monitors the SAP Data Intelligence namespace and the modifying objects in the namespace that enable SAP Data Intelligence to run on OpenShift Container Platform. SAP Data Intelligence Observer runs in a dedicated namespace and must be deployed before the SAP Data Intelligence installation is started.
SAP Data Intelligence Observer template
Deploy SAP Data Intelligence Observer in its own namespace (such as sdi-observer) separately from the SAP Data Intelligence namespace. The sdi-observer is deployed as an OpenShift template. Its behavior is controlled by the template's parameters, which are mirrored to its environment variables. The following table shows the key parameters:
Table 10. SAP Data Intelligence Observer template key parameters
Parameter name
Mandatory
Example
Description
NAMESPACE
Yes
sdi-observer
The desired namespace to which to deploy resources. Defaults to the current namespace.
SDI_NAMESPACE
YES
Sdi
The name of the SAP Data Intelligence namespace to manage. Defaults to the current one. It is set only if the SAP Data Intelligence Observer is running in a different namespace (see NAMESPACE).
SLCB_NAMESPACE
No
sap-slcbridge
The namespace where SLC Bridge runs.
OCP_MINOR_RELEASE
YES
4.6
Minor release of OpenShift Container Platform (for example, 4.6). This value must match the OpenShift Container Platform server version
SDI_NODE_SELECTOR
YES
node-role.kubernetes.io/sdi=
Node selector determining nodes that will be dedicated to SDI workloads. A comma-separated list of key=value pairs. If this parameter is unset (the default), the node selector will not be managed.
- To inspect all the available parameters and their semantics, run:
# oc process --parameters -f https://raw.githubusercontent.com/redhat-sap/sap-data-intelligence/master/observer/ocp-template.json
Deploying SAP Data Intelligence Observer
SAP Data Intelligence Observer monitors the SAP Data Intelligence and SLC Bridge namespaces and applies changes to the deployments to enable SAP Data Intelligence to run on OpenShift Container Platform. SAP Data Intelligence and Observer performs the following operations:
- Adds additional persistent volume to vsystem-vrep StatefulSet to enable it to run on RHCOS
- Grants fluentd pods permissions to logs
- Reconfigures the fluentd pods to parse plain-text file container logs on the OpenShift Container Platform 4 nodes
- (Optional) Marks containers manipulating iptables on RHCOS hosts as privileged when the kernel modules are not pre-loaded on the nodes
- (Optional) Deploys a container image registry that is suitable for mirroring, storing, and serving SDI images and for use by the Pipeline Modeler
- (Optional) Deploys a letsencrypt controller to handle trusted certificate management
- (Optional) Creates a cmcertificates secret to enable SAP Data Intelligence to communicate with the container image registry that was secured by a self-signed CA certificate in the installation
- (Optional) Enables the Pipeline Modeler (or vflow) to communicate with an (HTTP) insecure registry. Note that HTTPS is preferred.
Before deploying SDI Observer, ensure that the following conditions are met:
- The OpenShift Container Platform cluster is fully operational, including the image registry. Ensure that all the nodes are ready, all the cluster operators are available, and none of the operators are degraded by running:
# oc get co
# oc get nodes
- The namespaces for SLC Bridge, SAP Data Intelligence, and SAP Data Intelligence Observer exist. If they do not exist, create them by running:
# # change the namespace names according to your preferences
# NAMESPACE=sdi-observer SDI_NAMESPACE=sdi SLCB_NAMESPACE=sap-slcbridge
# for nm in $SDI_NAMESPACE $SLCB_NAMESPACE $NAMESPACE; do oc new-project $nm; done
To build the images that are needed for SAP Data Intelligence Observer:
- Create a secret with credentials for registry.redhat.io in the SAP Data Intelligence Observer namespace.
Note: To obtain the OpenShift secret, go to Red Hat Registry Service Accounts (see Red Hat Container Registry Authentication).
- After you have downloaded the OpenShift secret file (for example, rht-registry-secret.yaml) with your credentials, import it into $SDI_NAMESPACE by running:
# oc create -n "${NAMESPACE:-sdi-observer}" -f rht-registry-secret.yaml
secret/123456-username-pull-secret created
Deploy SAP Data Intelligence Observer by processing the template
To deploy SDI Observer:
- Run:
# NAMESPACE=sdi-observer
# SDI_NAMESPACE=sdi
# OCP_MINOR_RELEASE=4.6
# DEPLOY_SDI_REGISTRY=true
# INJECT_CABUNDLE=true
# MANAGE_VSYSTEM_ROUTE=true
# REDHAT_REGISTRY_SECRET_NAME=123456-username-pull-secret
# oc process -f https://raw.githubusercontent.com/redhat-sap/sap-data-intelligence/master/observer/ocp-template.json \
NAMESPACE="${NAMESPACE:-sdi-observer}" \
SDI_NAMESPACE="${SDI_NAMESPACE:-sdi}" \
OCP_MINOR_RELEASE="${OCP_MINOR_RELEASE:-4.6}" \
DEPLOY_SDI_REGISTRY="${DEPLOY_SDI_REGISTRY:-true}" \
INJECT_CABUNDLE="${INJECT_CABUNDLE:-true}" \
MANAGE_VSYSTEM_ROUTE="${MANAGE_VSYSTEM_ROUTE:-true}" \
REDHAT_REGISTRY_SECRET_NAME="$REDHAT_REGISTRY_SECRET_NAME" | oc create -f -
Note: It is also recommended to dedicate a set of nodes to the SAP Data Intelligence workload by running SDI_NODE_SELECTOR=node-role.kubernetes.io/sdi= parameter. This command deploys the SDI Observer in namespace sdi-observer in such a way that the Observer deploys the container image registry and injects the default cabundle into SAP Data Intelligence pods to trust the registry. It might take a couple of minutes to build and deploy the sdi-observer image.
- To view the current SAP Data Intelligence Observer configuration, run:
# oc set env --list -n "${NAMESPACE:-sdi-observer}" dc/sdi-observer
SAP Data Intelligence Observer registry
If the SAP Data Intelligence Observer is configured to deploy the container image registry through the DEPLOY_SDI_REGISTRY=true parameter, it deploys the deploy-registry job. The job then:
- Builds the container-image-registry image and pushes it to the integrated OpenShift Image Registry.
- Generates or uses configured credentials for the registry.
- Deploys the container-image-registry deployment config that runs this image and requires authentication.
- Exposes the registry using a route to identify the hostname.
Determine the registry credentials
In the SDI_REGISTRY_HTPASSWD_SECRET_NAME secret, look for the username and password by running:
# # make sure to change the NAMESPACE and secret name according to your environment
# oc get -o json -n "${NAMESPACE:-sdi-observer}" secret/container-image-registry-htpasswd | \
jq -r '.data[".htpasswd.raw"] | @base64d'
The username and password are separated by a colon, as shown in the following example:
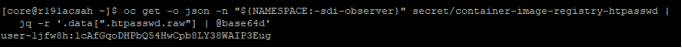
Figure 14. Secret username and password
Create a secret file that contains the container registry credentials
Create a text file vsystem-registry-secret.txt to store the registry username, password, and address.
Note: Make a note of these items. You will be prompted for them when you install SAP Data Intelligence using the SLC Bridge tool.
# # determine registry's hostname from its route
# hostname="$(oc get route -n "${NAMESPACE:-sdi-observer}" container-image-registry -o jsonpath='{.spec.host}')"
# oc get -o json -n "${NAMESPACE:-sdi-observer}" secret/container-image-registry-htpasswd | \
jq -r '.data[".htpasswd.raw"] | @base64d | gsub("\\s+"; "") | split(":") |
[{"username":.[0], "password":.[1], "address":"'"$hostname"'"}]' | \
json2yaml > vsystem-registry-secret.txt
Test the connection
This example assumes that the INJECT_CABUNDLE and DEPLOY_SDI_REGISTRY parameters are set to true and the other parameters use the defaults.
- Obtain the Ingress Router's default self-signed CA certificate:
# oc get secret -n openshift-ingress-operator -o json router-ca | \
jq -r '.data as $d | $d | keys[] | select(test("\\.crt$")) | $d[.] | @base64d' >router-ca.crt
- Perform a simple test using curl, as shown in the following figure:
# # determine registry's hostname from its route
# hostname="$(oc get route -n "${NAMESPACE:-sdi-observer}" container-image-registry -o jsonpath='{.spec.host}')"
# curl -I --user user-qpx7sxeei:OnidDrL3acBHkkm80uFzj697JGWifvma --cacert router-ca.crt \
https://$hostname/v2/
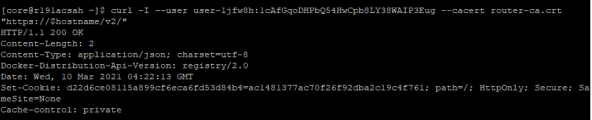
Figure 15. Connection test
Unless the registry's TLS certificate has been signed by a global trusted certificate authority, the OpenShift cluster must be configured to trust it to consume container images that it hosts.
- To configure OpenShift Container Platform to trust the deployed registry using certificates signed by a self-signed certificate authority, follow the steps that are described in Configure OpenShift to trust container image registry.
