Home > APEX > Cyber & Data Protection > White Papers > Ransomware Protection and Recovery with APEX Backup Services > Protection
Protection
-
The first step in preventing damage from ransomware is ensuring that you have a clean backup copy of your data. Built on highly resilient cloud infrastructure, APEX Backup Services makes it impossible for ransomware to encrypt backup data. Zero trust architecture, including multi-factor authentication, envelope encryption, and separate account access ensures that ransomware cannot use compromised primary environment credentials to tamper with backup data. Finally, excess deletion prevention and soft-delete (recycle bin) features provide a further layer of security to safeguard backups against deletion.
Air-gapped backups and object-based storage
Ransomware cannot execute in the APEX Backup Services environment thanks to how its Resiliency Cloud is built.
- The APEX Backup Services platform is not accessible using customer OS/system credentials
- Data is never stored as-is. APEX Backup Services stores data as smaller application-aware blocks before being stored in an object store
- Without access to an operating system, the malware cannot execute on its own. It cannot establish any communication with its command-and-control center for any further triggers or execution code
- The APEX Backup Services cloud environment is not based on Windows and does not depend on the direct-attached storage, Active Directory applications, or Remote Desktop Protocols typically used by ransomware
As an extra layer of security, APEX Backup Services retains deleted snapshots in an inaccessible cache for seven days. It is therefore possible to restore data even if it has been deleted from the backup environment.
Encryption
Another key to security is encryption for data, both in flight and at rest. APEX Backup Services provides a secure, multi-tenant environment for customer data.
- APEX Backup Services issues unique per tenant AES-256 encryption keys and offers encryption for data in flight and at rest. The use of one unique encryption key per customer along with customer held key encryption keys, creates crypto segmentation between customers, preventing data leakage
- APEX Backup Services stores the data by splitting it into blocks and deduplicating, with unique data blocks stored in AWS S3. Metadata is stored in AWS DynamoDB. AWS EC2 provides the computational layer to enable elastic scalability
- The application layer is separate from the data layer. As a result, anyone having access to the application layer does not get access to the data layer
- Within the data layer, APEX Backup Services encrypts the data using envelope encryption technology, making it impossible for anyone besides the customer to access the data
Envelope encryption
Our platform uses a digital envelope encryption model, so your data is protected two-fold. First, a unique key is generated, encrypted, and turned into a token, which is then stored. This token can only be accessed by the administrator or end user providing their credentials as the complementary part to decrypt the stored token; and second, the data itself is also encrypted. To access the encrypted data, both parts of the equation need to work together to recreate the key, which only exists in that unique session. Because only the administrator or end user has access to that token, anyone who wants the data would have to go to them to get the first piece of the puzzle. Effectively, no one can access the data without your knowledge.
Access Control
One of the most effective ways to protect data is to limit who can access it. If too many people can access and delete data or reassign administrative roles, threat actors can compromise even low-level credentials, and use them to destroy data or lock other administrators out of the backup environment.
APEX Backup services provides RBAC (Role Based Access Control). It is strongly recommended to ensure that only a small group of administrators can perform destructive actions such as deleting backup data.
- Administrative control settings prevent end users from deleting backup data. You can also require that two administrators approve major deletions.
- APEX Backup Services also allows you to customize admin roles to prevent deletion (screenshot below). As a best practice, designate no more than two people in the organization as admins with the power to delete snapshots.
- Geofencing capabilities ensure that access to the backup environment is for known IP addresses blocking out potential attacks from any bad actors or embargoed countries.
- Dell Technologies employees cannot access customer data or infrastructure directly, in line with our secure by design philosophy. APEX Backup Services has strict logical access controls to prevent access to production backup nodes. No Dell Technologies employees have direct (SSH) access to servers processing backup operations.
It is also important to consider access control for vendor employees. Due to our unique encryption, Dell Technologies never has access to customer data. There is strict control on how developers can access the code that powers APEX Backup Services.
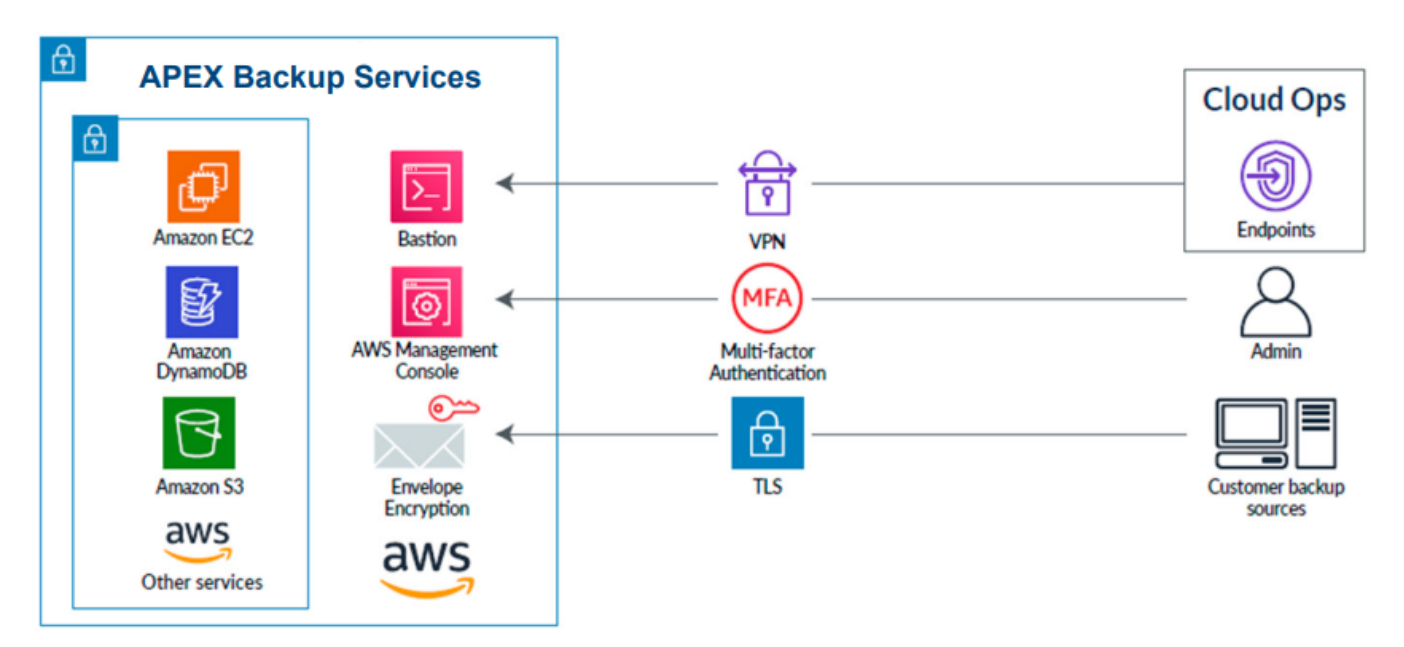
Figure 2. Access control
- Access to applications is monitored and controlled using a multi-factor authentication and access control using a combination of Bastion, VPN, MFA, and auto expiring dynamic credentials
- There is no SSH access to production nodes, closing potential security threats from that access point
Zero Trust Security
Access control is only effective if it is difficult to compromise administrative profiles. To prevent threat actors from gaining access to the backup environment using compromised credentials, you can implement zero trust security protocols.
Zero Trust is a security model based on strict verification processes. This approach treats every access attempt as if it originates from an untrusted source and access is only granted after identity has been verified.
APEX Backup Services was designed around a zero-trust security architecture and offers rich multi-layered defense features including MFA (Multi-Factor Authentication). Built natively on AWS’s security framework, APEX Backup Services also inherits the global security, compliance, and data residency controls, thus adhering to the highest standards for privacy and data security.
Stringent security compliance and certifications for APEX Backup Services
Third-party validation supports the trustworthiness of the security of any SaaS service. APEX Backup Services can claim compliance with the following certifications and frameworks, including (but not limited to):
- SOC 2 type II audited
- HIPAA compliance
- FIPS 140-2 compliant (GovCloud environments)
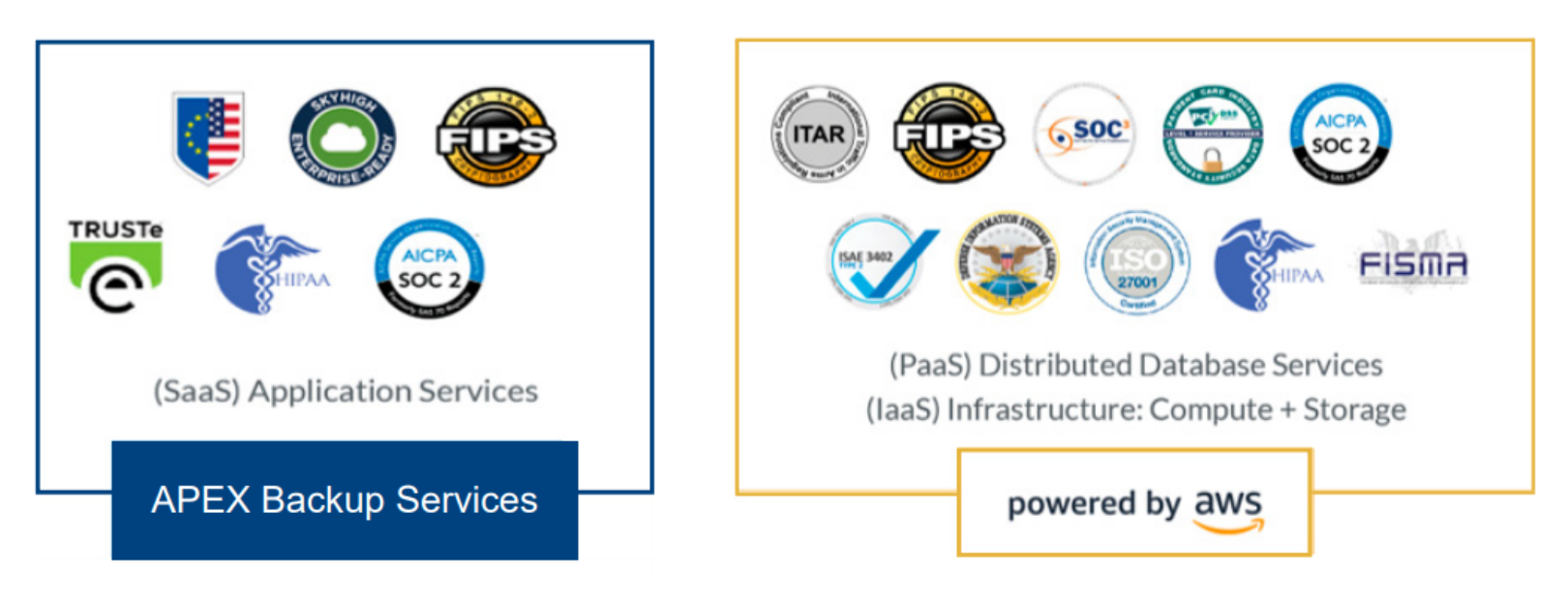
Figure 3. APEX Backup Services - security compliance and certifications
