Home > APEX > Cyber & Data Protection > White Papers > Ransomware Protection and Recovery with APEX Backup Services > Detection
Detection
-
Detecting a ransomware attack as soon as possible can help prevent contamination spread. The APEX Backup Services accelerated ransomware recovery module provides access insights and anomaly detection that help you quickly identify possible ransomware attacks. Access insights let you see location, identity, and activity information for all access attempts. Anomaly detection uses proprietary ML algorithms to provide alerts for unusual data activity. The algorithm learns the norms for your specific backup environment, so it does not require any rules setup or tuning. It also uses entropy-based insights to reduce false positives.
Monitoring security events
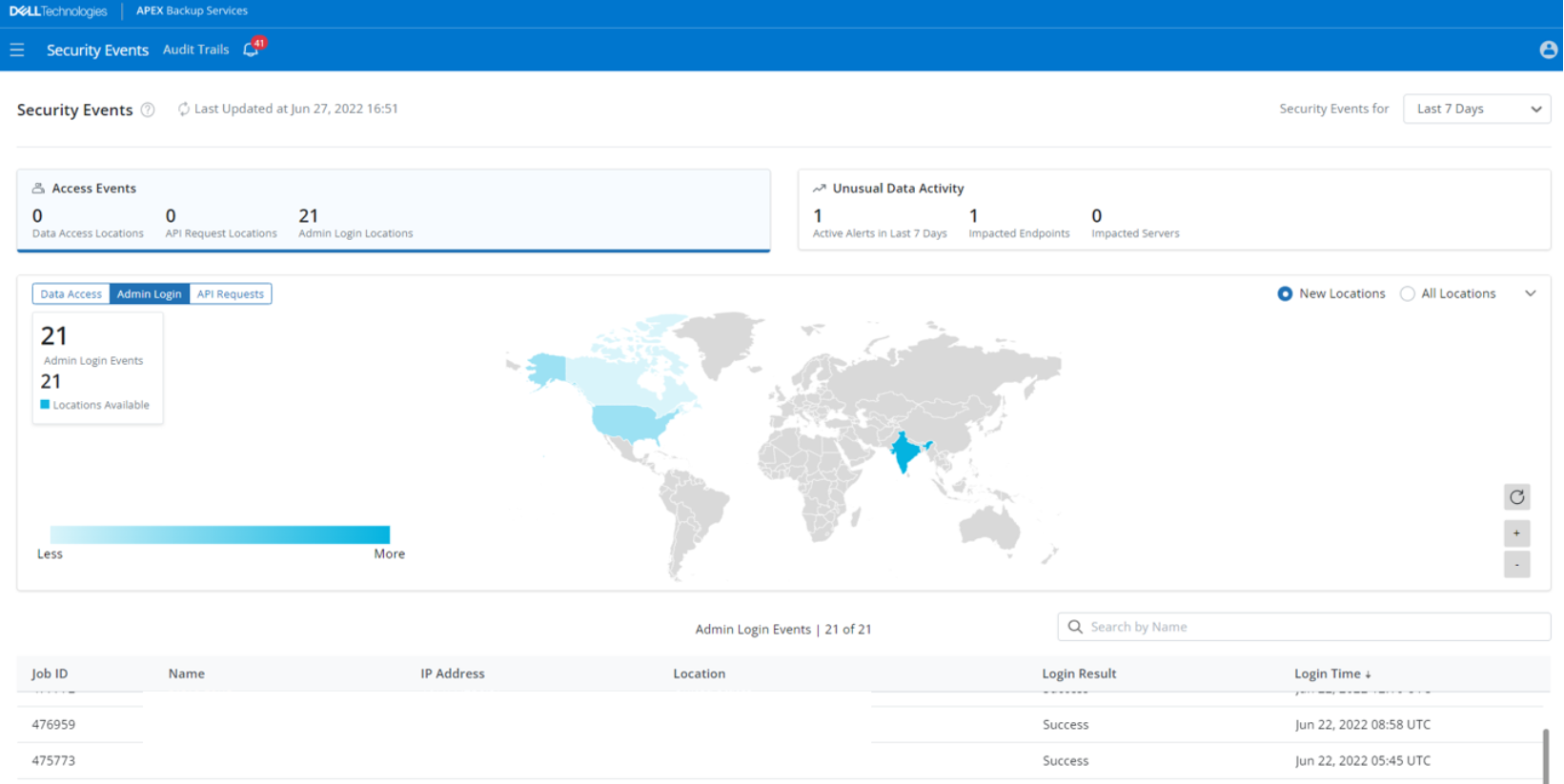
APEX Backup Services offers “Security Events”, a dashboard that shows you upfront the count of all administrator login events, data access events, API requests, and unusual data activity alerts, and nudges you to take remedial actions if required. This data helps you gain situational awareness about the backed-up data by gathering events from all APEX Backup Services products.
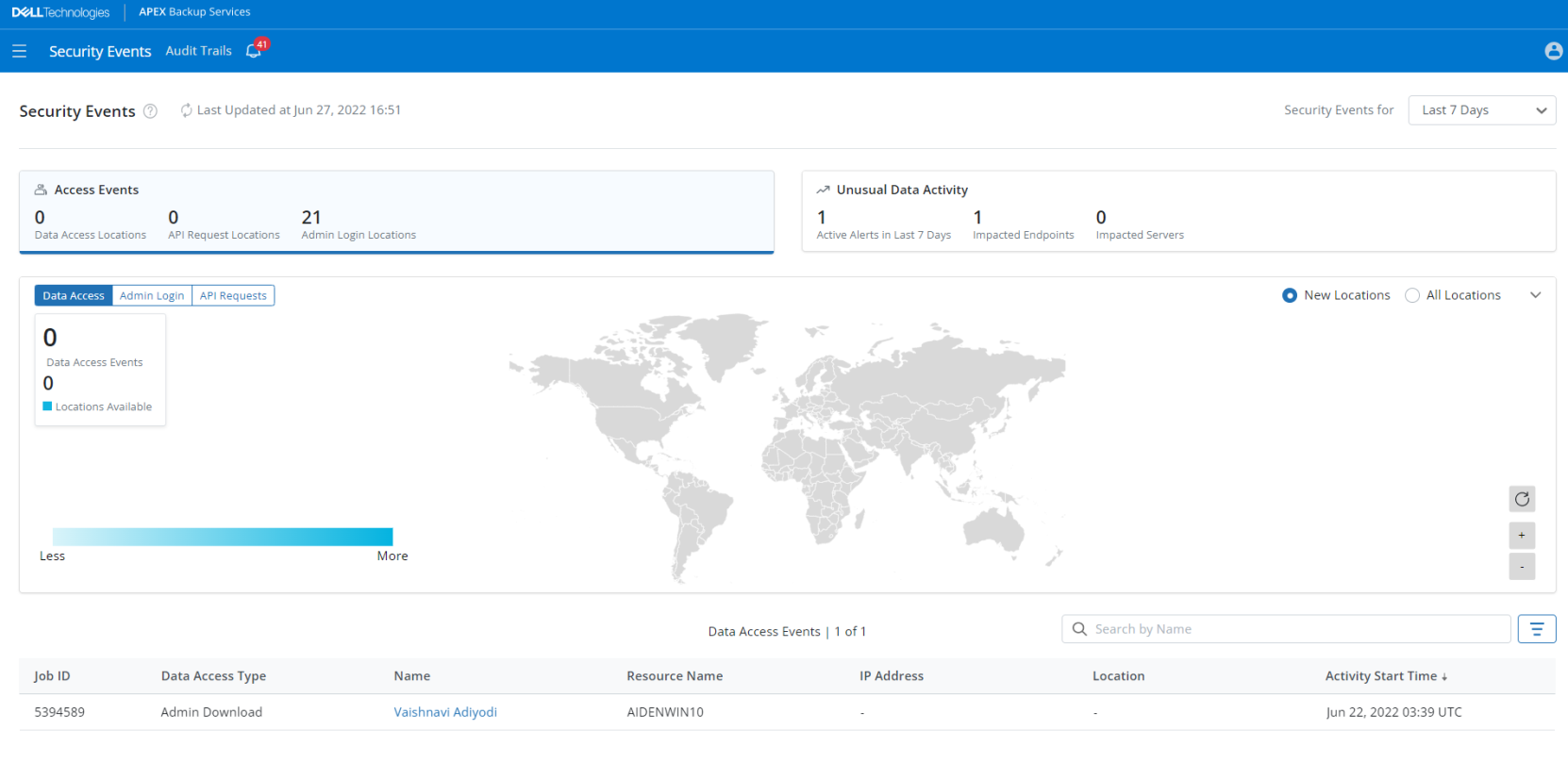
Figure 4. Ransomware recovery - Security Events
The security events dashboard displays the following:
- The total count of administrator logins and API requests from new locations
- The restore and download activities performed by administrators and users
- The locations from where administrators have logged into the APEX Backup Services Cloud platform. The locations are displayed on a map for easy visual reference
- The locations from where administrators have made an API request with several important details
- The number of unusual data activity alerts generated
- The number of endpoints and servers that have been quarantined. You can click the count to view the list of quarantined resources
Anomaly detection
The APEX Backup Services accelerated ransomware recovery module provides access insights and anomaly detection that help you quickly identify possible ransomware attacks. Access insights lets you see location, identity, and activity information for all access attempts.
Access Insights:
The APEX Backup Services dashboard provides a single pane of glass where you can see all access attempts and activity across all your data sources, including:
- Which users and APIs accessed your backup environment
- Where access attempts originated geographically
- When access attempts were made
- What actions were attempted (recover, delete, and so on)
API integrations can feed this information into SIEM (security information and event management) applications such as Splunk and Arcsight for correlation and accelerated incident response.
Unusual Data Activity
The Unusual Data Activity feature with APEX Backup Services provides continuous monitoring of your backup data. Our proprietary entropy-based algorithm uses machine learning to understand norms for your specific backup environment and provides automated alerts for unusual data activity including bulk deletion and encryption. You can use these insights to quickly identify affected snapshots during recovery. API integrations also enable you to feed these alerts to your SIEM solution, supporting ransomware detection.
Anomaly detection uses proprietary ML algorithms to provide alerts for unusual data activity. The algorithm learns the norms for your specific backup environment, so it does not require any rules setup or tuning. It also uses entropy-based insights to reduce false positives.
Suspicious modification of data on a resource is called Unusual Data Activity (UDA). A user or malicious software can make such changes.
When such a potential threat manipulates the data on a resource, it is suspicious in nature and is unlike how the resource owner works with data on that resource. Since anomalies of this type often indicate issues that require attention, APEX Backup Services flags any such anomalous behavior in a resource and generates an alert.
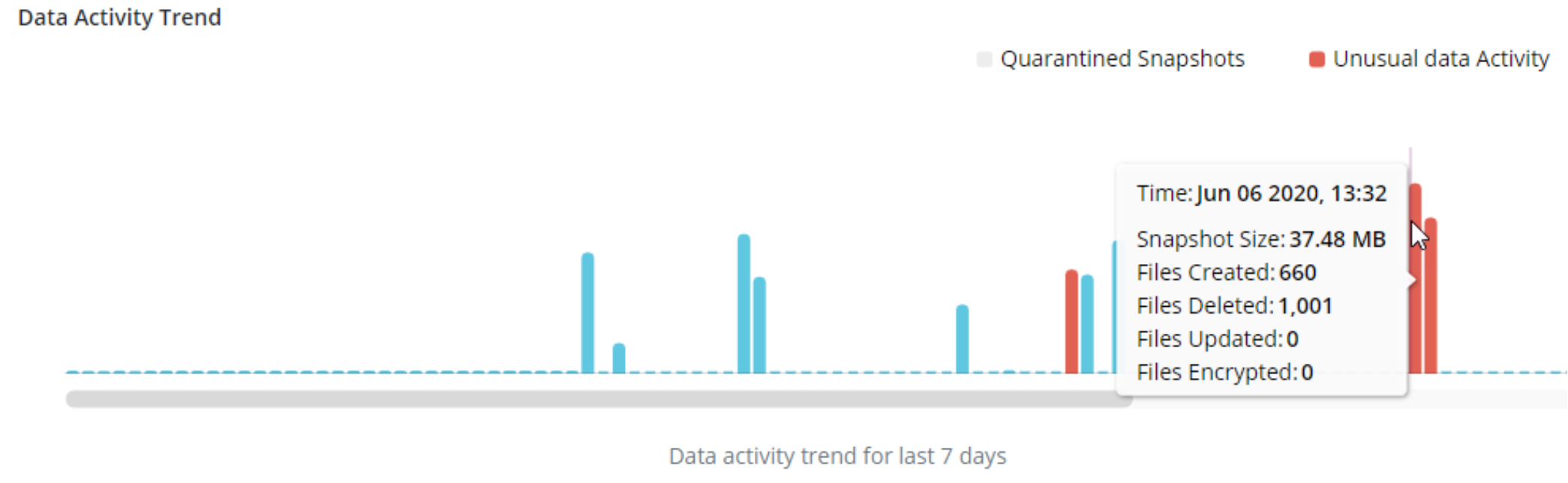
Figure 5. Ransomware recovery - Unusual Data Activity
Monitors the data activity trend for a given resource, and after a sufficient sample size, it builds the anomaly baseline.
Following are the prerequisites to start scanning a resource:
- 33 snapshots: The resource must have a minimum of 33 successfully backed up data snapshots.
- 30 days: Scanning starts 30 days after the resource was configured for backup.
Note: The 30-day count starts from the day the Unusual Data Activity feature was enabled.
Being notified about the resources showing unusual data activity can help you identify a potential threat in your environment such as a ransomware attack or a compromised user.
Click the card to view details of the generated alerts.
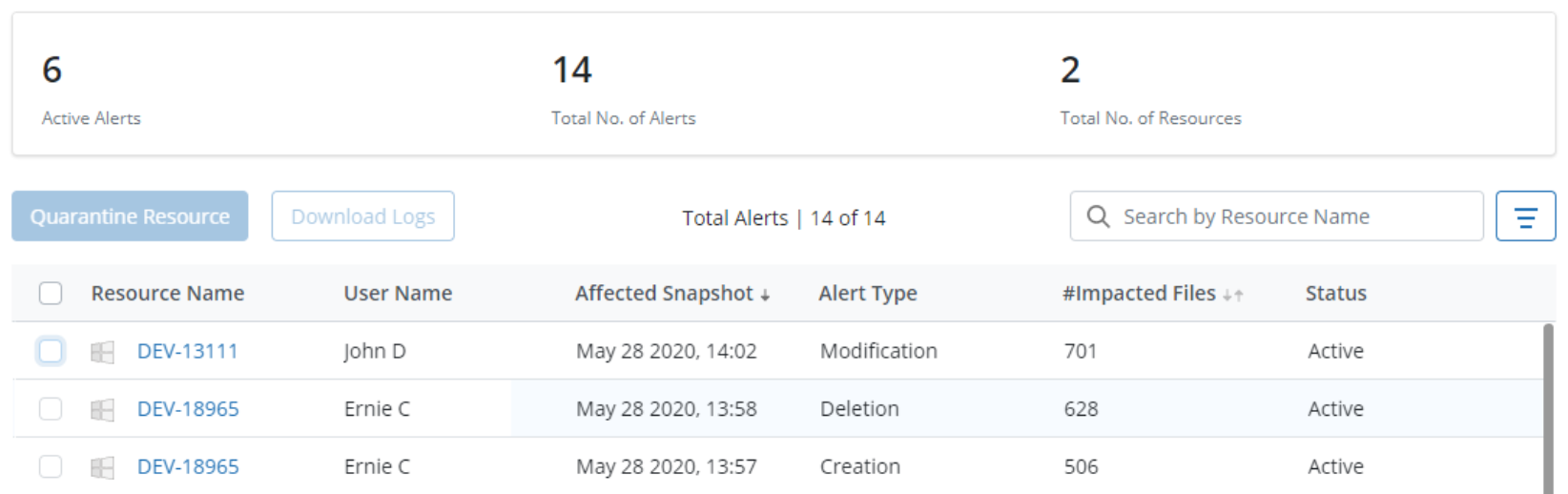
Figure 6. Ransomware recovery - UDA alerts
For any unusual data activity alert, you can do any of the following:
- Ignore the alert: If you deem any alert as a false positive, click the resource name and select the false positive alert. Click Ignore to resolve the alert.
- Quarantine the resource: Select an alert and click Quarantine Resource to stop the ransomware from spreading further.
Beyond anomaly detection, the federated search aids forensic investigation teams in identifying which other data sources are infected, using a hash and metadata-based search, providing more clarity on the scope of a ransomware attack.
