Home > Data Protection > PowerProtect DD Series Appliances > Dell PowerProtect DD Series Appliances: Security > Data security settings
Data security settings
-
Data security settings including data-encryption-enabled controls that prevent data permanently stored by the product from being disclosed in an unauthorized manner.
Figure 7. Data Security settings overview
DD Retention Lock software
DD Retention Lock software provides immutable file locking and secure data retention capabilities for customers to meet both corporate governance and compliance standards.
With DD Retention Lock, administrators can apply retention policies at an individual file level. This software enables customers to use their existing systems for backup and archive data. DD Retention Lock ensures that archive data is retained long term with data integrity and secure data retention.
DD Retention Lock Governance edition and DD Retention Lock Compliance edition can co-exist on the same system to enable different retention periods for different classes of archive data. DD Retention Lock software is compatible with industry-standard, NAS-based (CIFS, NFS) Write-Once-Read-Many (WORM) protocols and is qualified with leading archive applications such as Dell SourceOne, Dell DiskXtender, and Veritas Enterprise Vault.
Dual sign-on requirement
DD Retention Lock Compliance includes additional administrative security in the form of dual sign-on that requires a sign-on by the system administrator and a sign-on by a second authorized authority (the “security officer”). The dual sign-on mechanism of the DD Retention Lock Compliance edition acts as a safeguard against any actions that could potentially compromise the integrity of locked files before the expiration of the retention period.
Secure system clock
DD Retention Lock Compliance implements an internal security clock to prevent malicious tampering with the system clock. The security clock closely monitors and records the system clock. If there is an accumulated two-week skew within a year between the security clock and the system clock, the file system is disabled and can be resumed only by a security officer.
On Retention Lock Compliant DD systems, system time can be modified only within certain restrictions set by date-change-limit and date-change-frequency.
Data integrity
The DDOS Data Invulnerability Architecture protects against data loss from hardware and software failures.
- When writing to disk, the DDOS creates and stores checksums and self-describing metadata for all data received. After writing the data to disk, the DDOS then recomputes and verifies the checksums and metadata.
- An append-only write policy guards against overwriting valid data.
- After a backup is complete, a validation process examines what was written to disk. The process verifies that all file segments are logically correct within the file system and that the data is identical before and after it is written to disk.
- In the background, the online verification operation continuously checks that data on the disks is correct and unchanged since the earlier validation process.
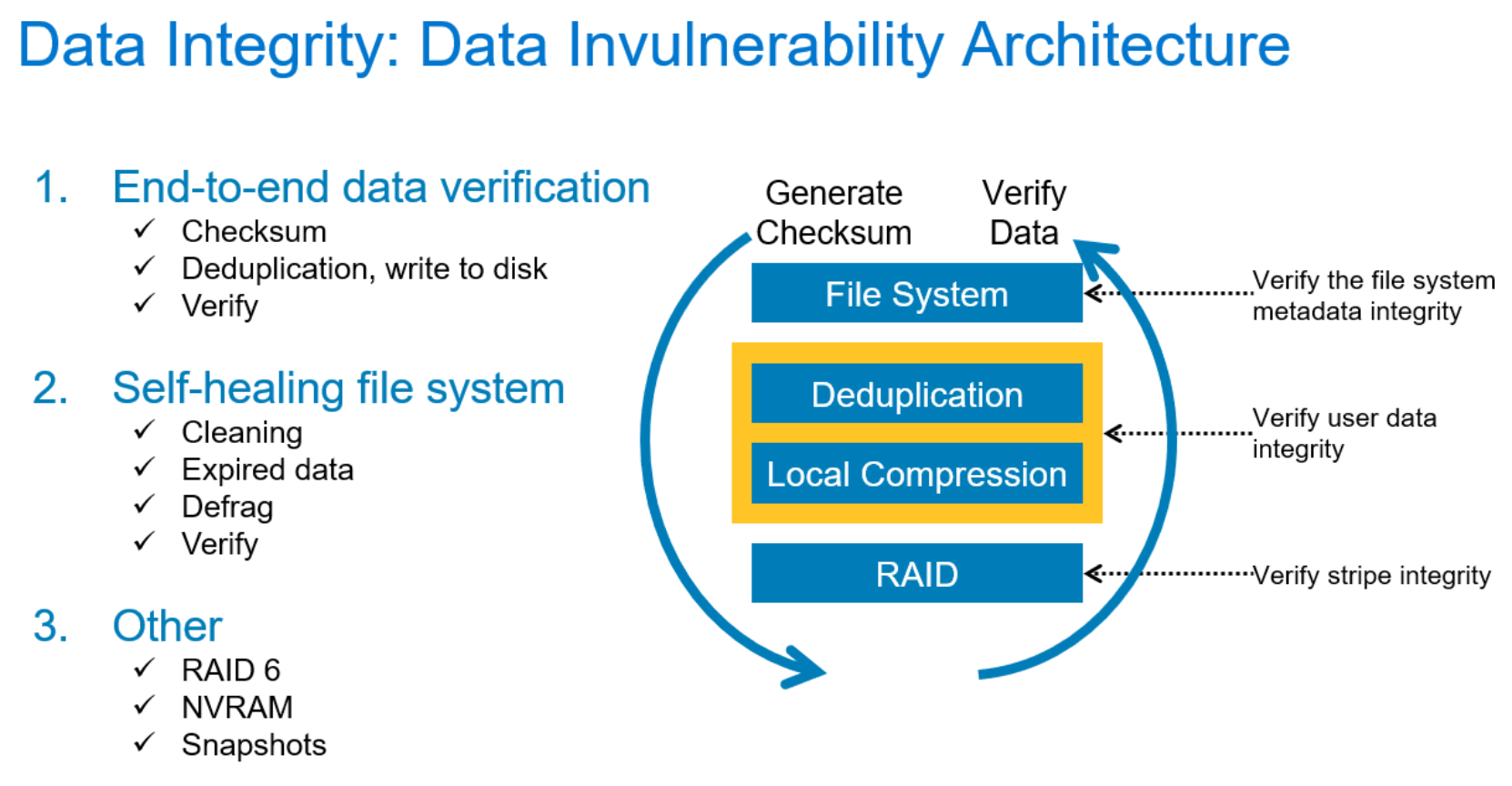
Figure 8. Data Invulnerability Architecture overview
Storage in most systems is set up in a double-parity RAID 6 configuration (two parity drives). Also, most configurations include a hot spare in each enclosure, except in certain low-end series systems that have eight or fewer disks. Each parity stripe has block checksums to ensure that data is correct. Checksums are constantly used during the online verification operation and while data is read from the system. With double parity, the system can fix simultaneous errors on as many as two disks.
To keep data synchronized during a hardware or power failure, the system uses nonvolatile RAM (NVRAM) to track outstanding I/O operations. An NVRAM card with fully charged batteries (the typical state) can retain data for hours, which is determined by the hardware in use. When reading data back on a restore operation, the DDOS uses multiple layers of consistency checks to verify that restored data is correct.
DD series systems support SNMP V2C and SNMP V3. SNMP V3 provides a greater degree of security than V2C by replacing cleartext community strings as a means of authentication with user-based authentication using MD5, SHA1, or SHA-256. Also, SNMP V3 user authentication packets can be encrypted, and their integrity is verified with either DES or AES.
The DDOS file system performs multiple layers of data verification on data that is received from backup applications to ensure that data is written correctly to the system disks. This process ensures that the data can be retrieved without error. The DDOS is purpose-built for data protection, and it is architecturally designed for data invulnerability. There are four critical areas of focus, described in the following sections: end-to-end verification, data erasure, system sanitization, and data encryption.
End-to-End verification
End-to-end checks protect all file system data and metadata. As data comes into the system, a strong checksum is computed. The data is deduplicated and stored in the file system. After all data is flushed to disk, it is read back, and again check summed. The checksums are compared to verify that both the data and the file system metadata are stored correctly.
Data erasure
The filesys destroy command deletes all data in the file system. The file system can be destroyed using the DD System Manager.
System sanitization
System sanitization was designed to remove all traces of deleted files and restore the system to the previous state. The primary use of the sanitize command is to resolve Classified Message Incidents (CMIs) that occur when classified data is copied inadvertently onto a nonsecure system. System sanitization is typically required in government installations. Sanitization is not supported with SSD cache tier. Use the storage remove and storage add commands to remove the logical to physical mapping. This action ensures that physical pages do not return previous written data. However, the previously written data may still be on SSD.
Data encryption
DD series systems offer three types of encryption:
- Inline encryption of data at rest using the DD Encryption software option
- Encryption of data in flight using DD Replicator software, which is used for replicating data between sites over the WAN
- Encryption of data in flight using DD Boost software, using Transport Layer Security (TLS)
Inline encryption of data at rest using the DD Encryption software option
Encryption of data at rest protects user data in the situation where a Data Domain or PowerProtect system is lost or stolen, and it eliminates accidental exposure if a failed drive requires replacement.
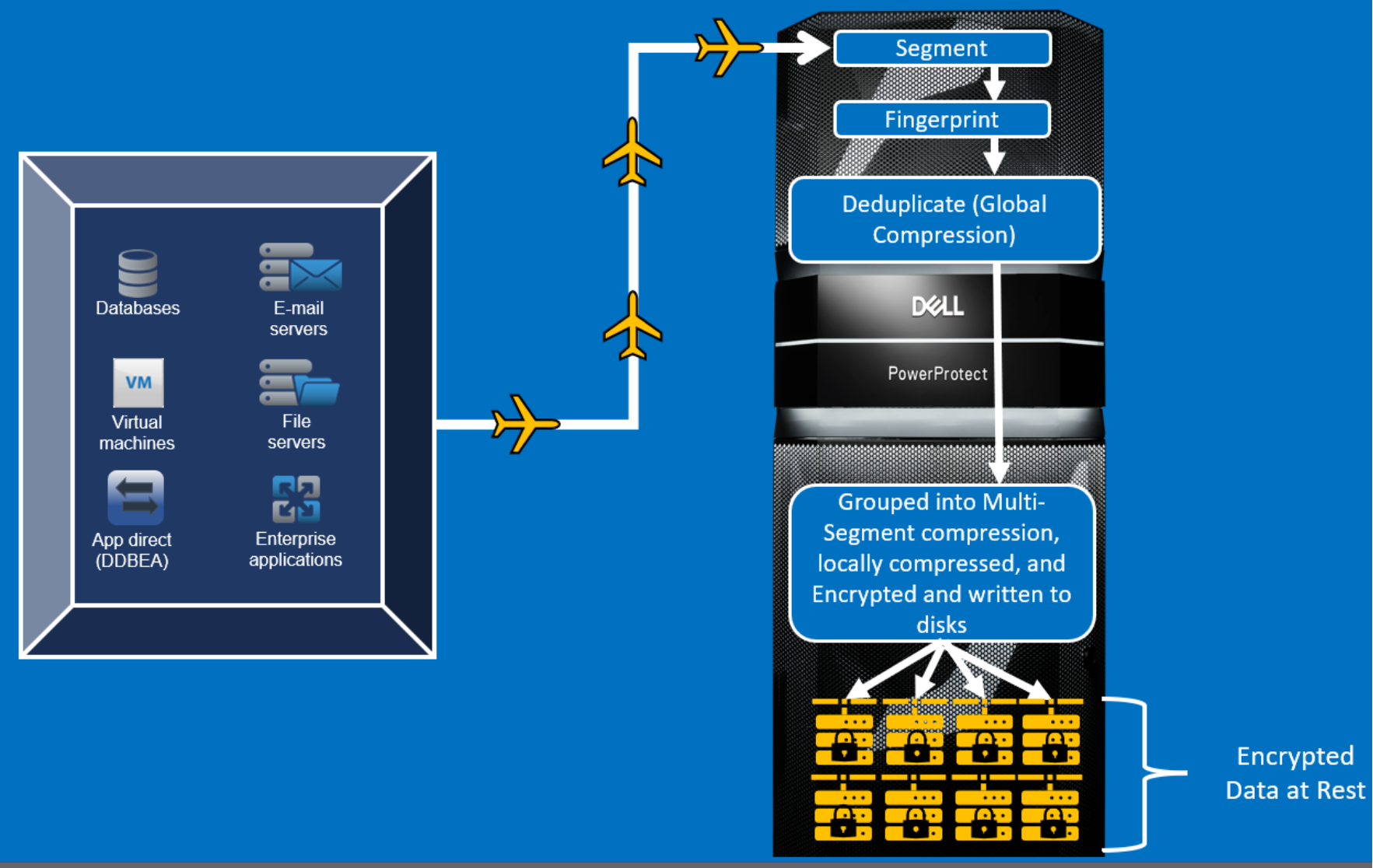
Figure 9. Inline Encryption overview
Encryption of data in flight using DD Replicator software
Encryption of data in flight encrypts data being transferred by DD Replicator software between two DD systems. It uses OpenSSL AES 256-bit encryption to encapsulate the replicated data over the wire.
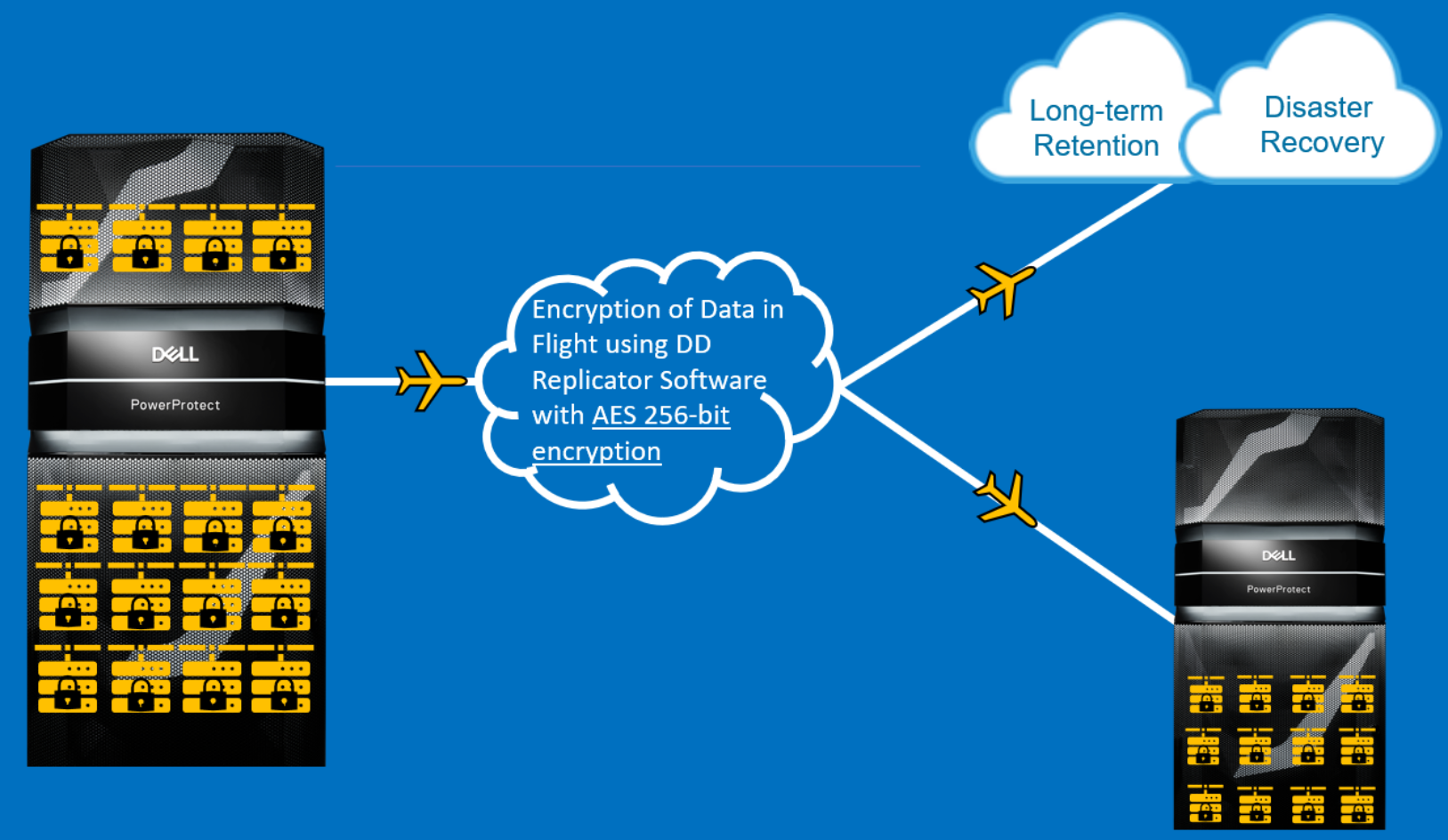
Figure 10. Encryption of data in flight using DD Replicator overview
Encryption of data in flight through DD Boost
The DD Boost protocol can be used with or without certificates for authentication and encryption of data.
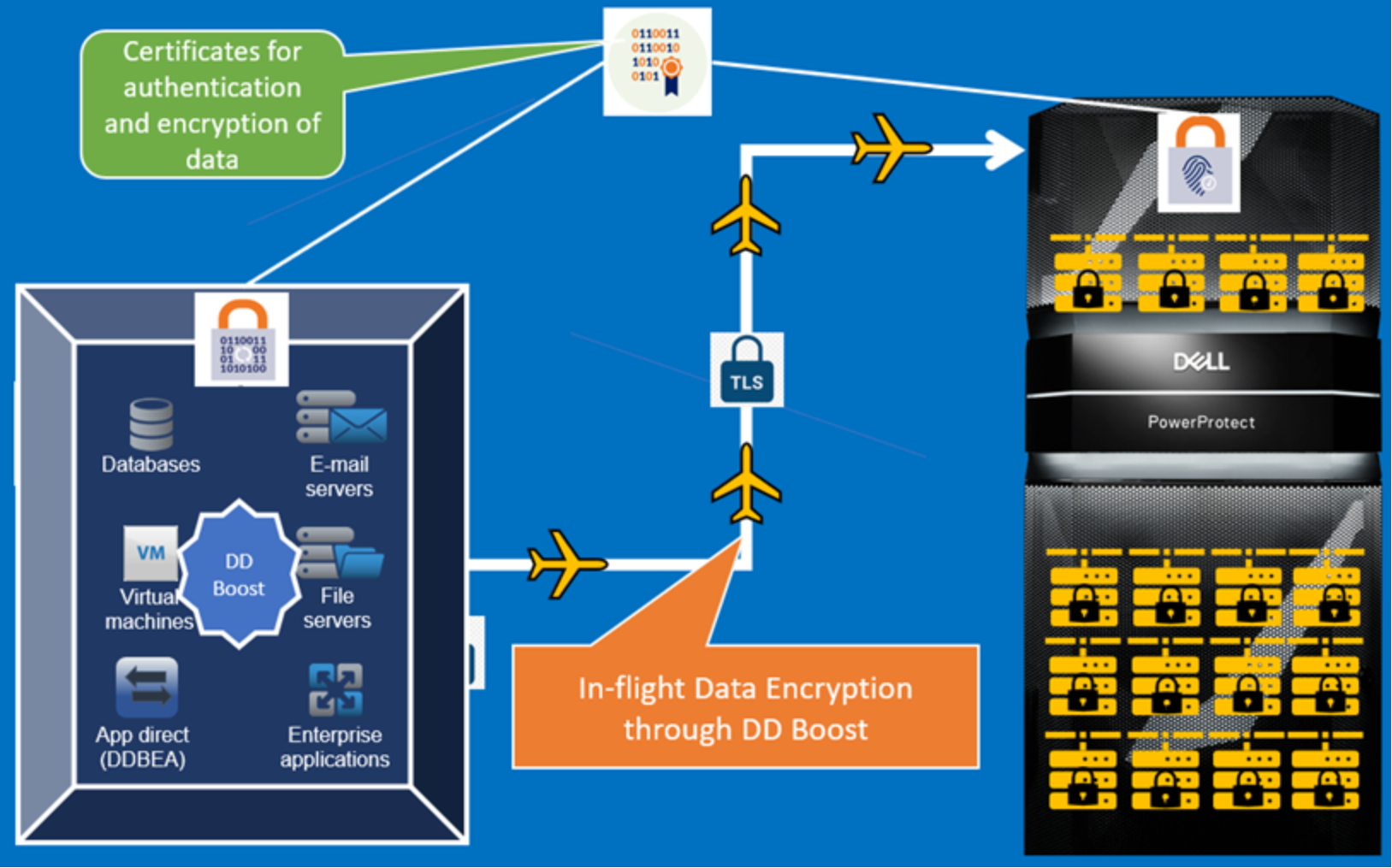
Figure 11. Encryption of data in flight through DD Boost
