Home > Data Protection > PowerProtect DD Series Appliances > Dell PowerProtect DD Series Appliances: Security > Certificate management
Certificate management
-
PowerProtect DD appliances use certificates to securely communicate with the following applications and protocols:
- HTTPS
- KMIP-compliant external key manager such as:
- KeySecure v8.5, v8.9, v8.10, and v8.12.1
- NextGen v1.9.1 and v1.10 from Safenet/Gemalto
- Data Security Manager (DSM) 6.3 from Thales/Vormetric
- CipherTrust 2.1, 2.2, 2.3 and 2.4 from Thales
- DD Boost
- LDAP server
- Cloud tier (AWS, Azure, Alibaba Cloud, Google Cloud, ECS, AWS federal)
- Certificate-based user authentication and two factor authentication with a Common Access Card (CAC)
PowerProtect DD appliances use self-signed certificates to build mutual trust with another system for secure data replication.
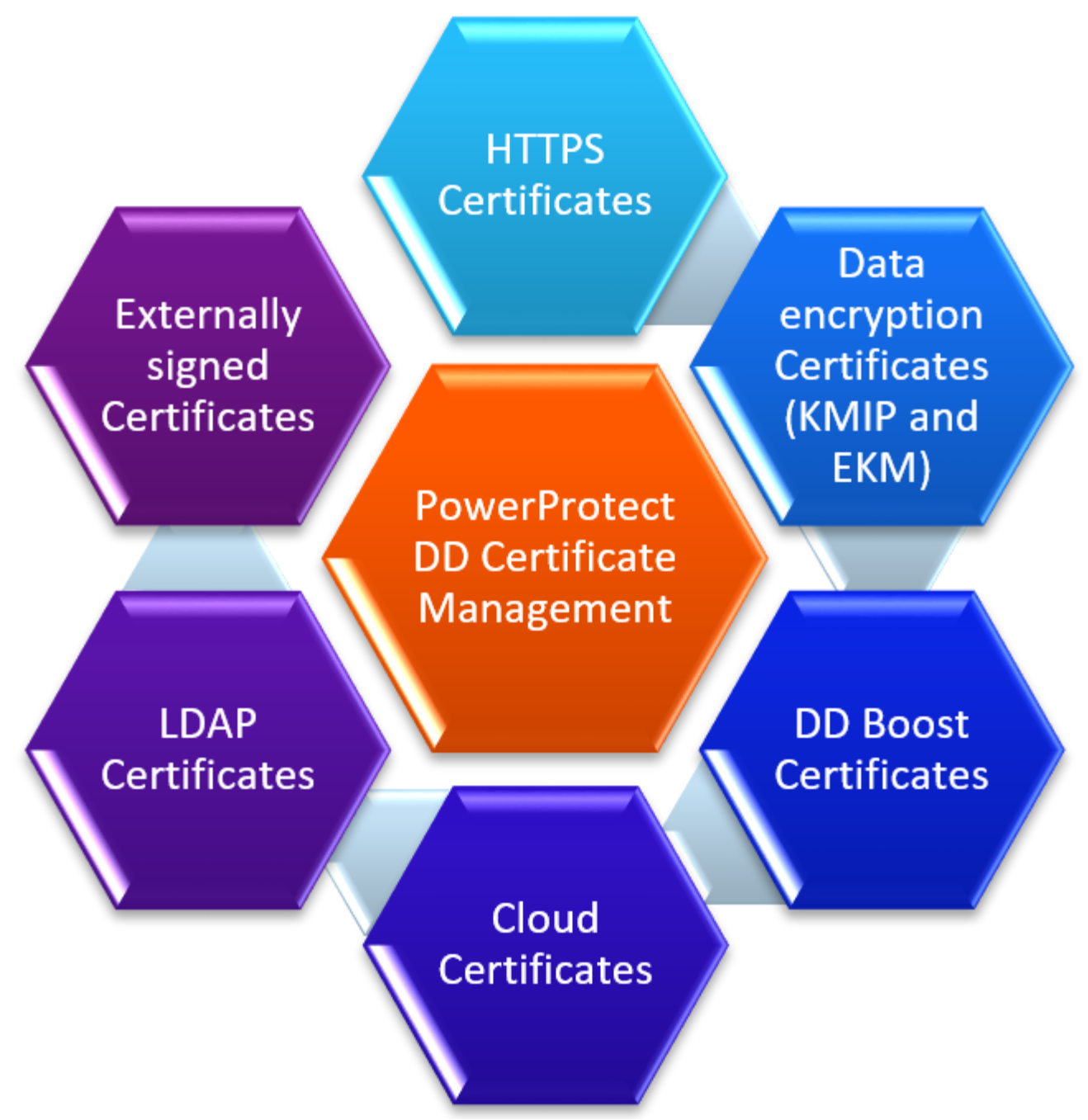
Figure 3. DD series certificate management overview
Managing DD series system with DDMC
To manage a PowerProtect DD appliance, a trust needs to be established between DDMC and the system. A self-signed certificate is used to establish the trust.
Cloud certificates
For PowerProtect DD to verify the identity of a cloud provider before backing up data from a system, the cloud providers have a host certificate that is issued by a CA. Import the CA certificate and any applicable CRLs before backing up any data to the cloud.
Certificate revocation list
A certificate revocation list (CRL) is a PEM-formatted file issued by a CA that lists the revoked user certificate. Once this CRL file is imported to PowerProtect DD System Manager, login is disabled for the revoked certificates. Online Certificate Status Protocol (OCSP) is not supported.
DD Boost certificates
The DD Boost protocol can be used with or without externally signed certificates for authentication and to provide data encryption. Use of certificates provides a more secure data transport capability. The DD Boost protocol also supports optional encryption when certificates are not used. In-flight encryption enables applications to encrypt in-flight backup or restore data over LAN from the system. When configured, the client can use TLS to encrypt the session between the client and the system.
HTTPS certificates
The system can use an imported certificate to establish a trusted connection to manage the system over SSL. If a certificate is not provided, the system can use its self-signed identity certificate.
Data encryption certificates
External CA and host certificates are required to set up the KMIP-compliant key managers such as:
- KeySecure v8.5, v8.9, v8.10, and v8.12.1
- NextGen v1.9.1 and v1.10 from Safenet/Gemalto
- Data Security Manager (DSM) 6.3 from Thales/Vormetric
- CipherTrust 2.1, 2.2, 2.3, and 2.4 from Thales
- Guardium Key LifeCycle Manager 4.1.1.0 from IBM Security
The embedded key manager (EKM) and external key managers (KMIP) are supported for both the active tier and cloud tier.
For information about encryption certificates, see the DDOS Administration Guide.
LDAP certificates
LDAP for NFS ID mapping for folder and file permissions supports secure LDAP using certificates.
High availability
In a high availability (HA) configuration, there are two controllers, where only one at a time is active. They are logically considered as a single file system.
- Both systems have the same root Certificate Authority.
- To establish mutual trust with the HA system, trust is required to be established with the active node only.
- Mutual trust, certificate signing requests, and all the imported certificates on the active node are mirrored to the standby node.
- Host certificate is generated per active and standby node and is used for HTTPS application. CA for secure support bundle upload is also kept per node.
Externally signed certificates
Certificate authority (CA) is in public certificate (PEM) format to establish a trusted connection between the external entity and each system.
If the system or cloud tier uses the SafeNet KeySecure external key manager, it requires a PKCS12 host certificate and CA certificate in PEM (public key) format to establish a trusted connection between the SafeNet KeySecure Key Manager Server and each system that it manages.
The certificate signing requires PKCS10 format. The public certificate key can have either PKCS12 (public plus a private key) or PEM format. The host certificate PEM format is used only with the Certificate Signing Request (CSR) feature. (OCSP) is not supported.
Individual host certificates can be imported for HTTPS and communication with SafeNet KeySecure Key Manager (KMIP). Importing the host certificate in PKCS12 format is supported. If there is a CSR on the system, host certificate can be imported in PEM format after the CSR is signed by a Certificate Authority.
On a FIPS-enabled DD system, the PKCS12 file must be FIPS-compliant. While encrypting the PKCS12 file, compatible encryption algorithms must be used. We recommend using "PBE-SHA1-3DES" for encrypting key and certificate in the PKCS12 file.
