Home > Data Protection > Data Protection (general) > DDVE In-cloud Retention Lock Compliance: Best Practices to Secure In-cloud Deployments > Posture management
Posture management
-
The foundation of a solid security strategy in the cloud starts with securing console access and configuring proper user permissions.
Zero Trust is an information security approach that focuses on data security and lifecycle management on any platform or network, taking into consideration the following principles:
- Assume breach: When considering security for your deployment, reduce the surface attack by assuming other resources in the configuration are compromised.
- Explicit verification: Explicitly validate trust by using multiple data points rather than just assuming trust. For example, when configuring access control to the cloud console, validate user identity, location, device health, and anomalies rather than grant access from an implicit internal network.
- Least-privilege access: Limit the risk of a compromised user by providing just-in-time and just-enough-access, as well as risk-based adaptive policies to help secure your configurations.
Zero Trust principles can be implemented on any public cloud deployments leveraging existing user management services (such as AWS IAM or Microsoft EntraID – formerly Microsoft AD) by following a comprehensive strategy based on asset/data-centric security, policy driven controls, identity management, and security zones/domains. This approach provides organizational flexibility, agility, and adaptability in addition to the traditional confidentiality, integrity, and availability of business assets.
Note: See this article on Zero Trust security for more information.
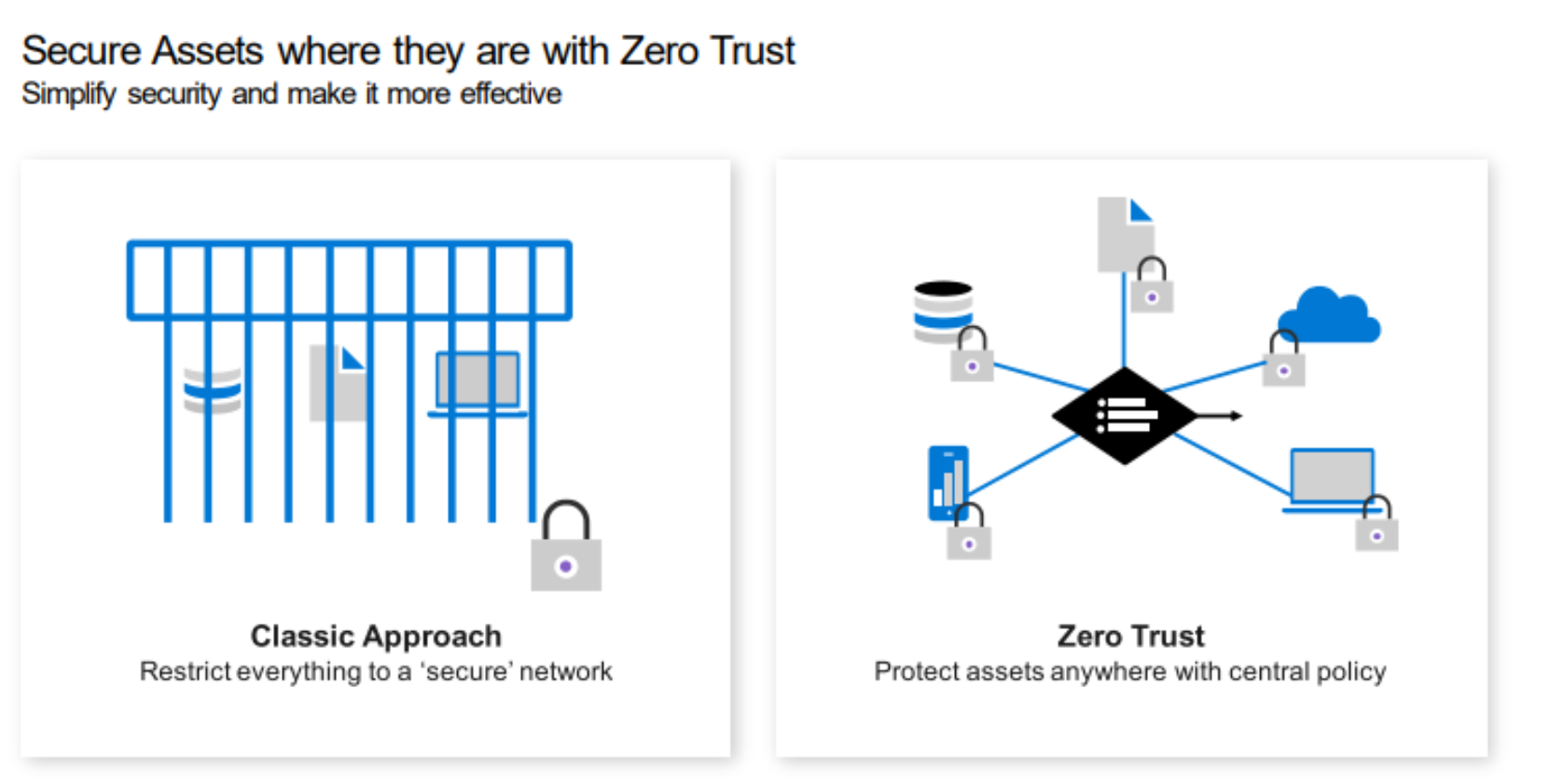
Figure 3. Zero Trust provides protection to critical business assets through a central policy approach
The following security practices describe some options that can be customized to customer needs after deploying APEX Protection Storage (DDVE in-cloud) on any public cloud:
- Access Control: The public cloud configuration allows you to define access boundaries and segmentation of resources with the goal of reducing the reach of potential security breaches through Cloud Console or Cloud APIs.
- Assign accountability by selecting groups or individuals to be responsible for key security decisions. Clearly document these owners and socialize their role so it is easy for all roles to reach them.
- Control access by defining appropriate restrictions for the users:
- Restrict user permissions and set permission boundaries for users to detail allowed operations. For example: A user designated to manage the APEX Protection Storage instances need not have permissions to modify/delete configurations made by the admin user.
- Create roles with only the set of permissions required to manage the APEX Protection Resources. Assign the roles defined to selected users while adhering to the organization’s security policies and restrictions. Refer to the DDVE Installation and Administration guide for the minimum set of permissions required.
- Use S3-specific policies to restrict unexpected management actions that can modify existent deployment configurations or delete data stored in the S3 object storage.
- Standardize a single directory and identity management: Standardize a single directory and identity by using managed application identities instead of human hard-coded accounts for applications to access your cloud resources, including APEX Protection Storage resources. This approach reduces the exposure of credential management while helping to automate the rotation of credentials, ensuring the security of identities. This can be accomplished by using AWS Identity Center, GCP IAM, or Azure AD identities.
- Enable Multi-factor Authentication (MFA): All public cloud users logged into the cloud console should use MFA to fully validate their identity. Enable password-less authentication for all API requests using secure tokens.
- Utilize Role-based Access Control (RBAC) options: Accessing S3 object storage from within APEX Protection Storage (DDVE in-cloud) should only be done using the cloud provider’s role-based access control (RBAC) mechanism.
- Delete long-term access/secret keys for the account: Since RBAC is the only mode of S3 access from within PowerProtect DDVE in the cloud, there is no need to have long-term credentials. Avoid creating temporary access keys specific for the APEX Protection Storage deployment stage.
