Home > Data Protection > Data Protection (general) > DDVE In-cloud Retention Lock Compliance: Best Practices to Secure In-cloud Deployments > Policies and standards
Policies and standards
-
In the public cloud, a security initiative is defined as a collection of policy definitions or rules aimed at a specific goal or purpose. These security initiatives simplify the management of your policies by logically grouping a set of policies into a single item.
A security initiative is initially built with the desired configuration of your cloud workload(s) and how the APEX Protection Storage is expected to interoperate. This approach helps ensure the deployment meets the regulators and organization security requirements. For example, in Azure, the default initiative is automatically assigned to any subscription adhering to the Microsoft Cloud Security benchmark. This benchmark contains a set of guidelines for security and compliance best practices built on the controls defined by the Center of Internet Security (CIS) and the National Institute of Standards and Technology (NIST) with a focus on cloud-centric security.
Additional cloud services such as AWS Guard Duty, Azure Defender or GCP Security Command Center can be used to monitor overall security initiatives and manage multiple subscriptions or entire management groups. The approach provided by Azure Defender is particularly interesting because it facilitates a multicloud posture management by enabling security oversight across other cloud providers including AWS and GCP. The service provides development security operations (DevSecOps), a cloud security posture management (CSPM) solution, and a cloud workload protection platform (CWPP).
Note: See this article on Microsoft Defender for Cloud for more information.
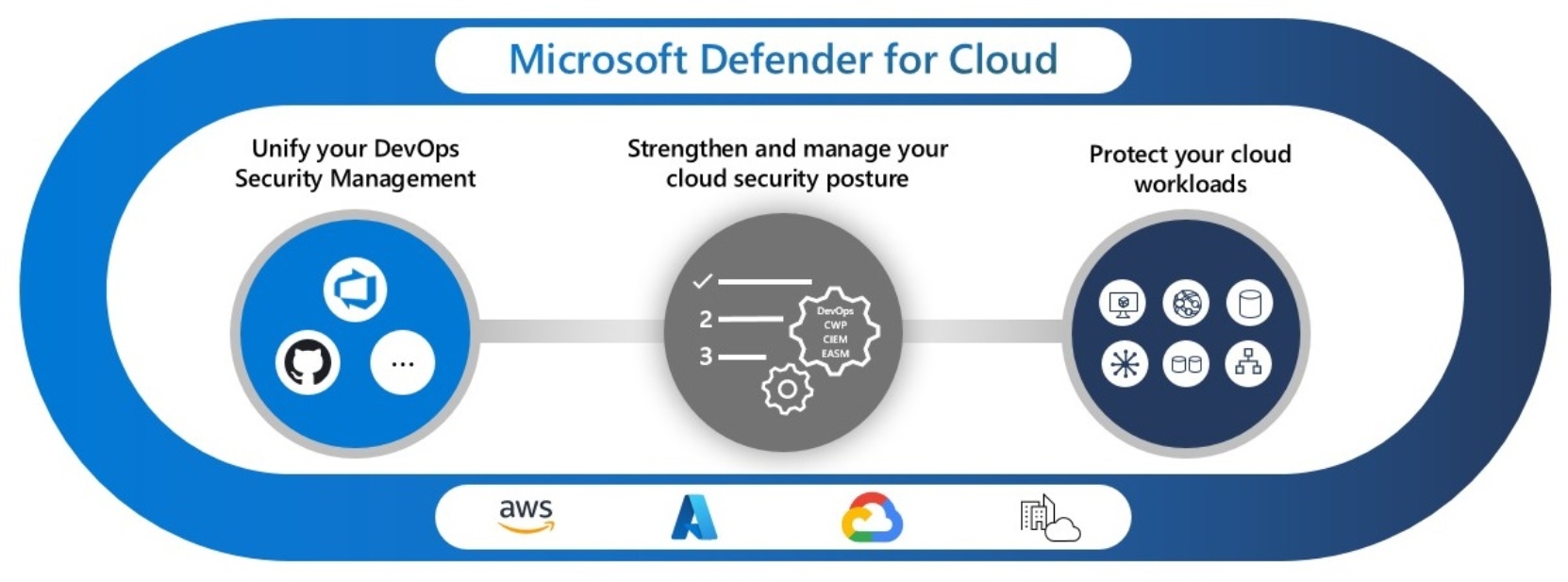
Figure 4. Microsoft Defender for Cloud integrates a multicloud approach for a unified security policy approach
When these cloud security services include APEX Protection Storage components, they can help improve the overall security posture of your deployment. Applying default security policies aligned with the organization’s security objectives allows you to define common security conditions across the entire public cloud configuration. This approach also facilitates the identification of existent deployments that may not comply with the overall security policy defined. Finally, a Secure Score can be calculated to consistently quantify new and existent deployments against the security recommendations defined. Equivalent metrics are available across public cloud providers, helping to achieve a consistent security assessment at any point in time.
Leverage the role-based access controls (RBAC) available on the public cloud provider to configure and assign appropriate policies and roles to the APEX Protection Storage service instances. Ensure appropriate permissions to access the S3 object storage are configured by retrieving short-term/rotating and temporary credentials.
Note: Refer to the DDVE Installation and Administration guide for the procedure on how to utilize the cloud provider’s RBAC on DDVE.
Always consider the least privileged approach by enabling the minimum set of permissions required to operate. Avoid using wild char (*) on policy definitions.
Establish a security posture management. Security is everyone’s job. The team should know how important it is, what to do, and how to do it. Prepare an incident response process that includes your cloud deployments and communicate it to your team, so they know what to do when an active attacker is found.
