Home > Data Protection > Data Protection (general) > Advanced Anomaly Detection with Data Protection Advisor > Working with external data sources
Working with external data sources
-
Data is collected by Data Protection Advisor using agents and defining the data collection parameters when the discovery wizard is used to monitor data protection elements or applications. However, data can also be collected from a range of external data sources. A list of available data source types is shown in Figure 36. For example, extracting assets from a Configuration Management Database (CMDB) and cross matching them against discovered protected clients is extremely useful.
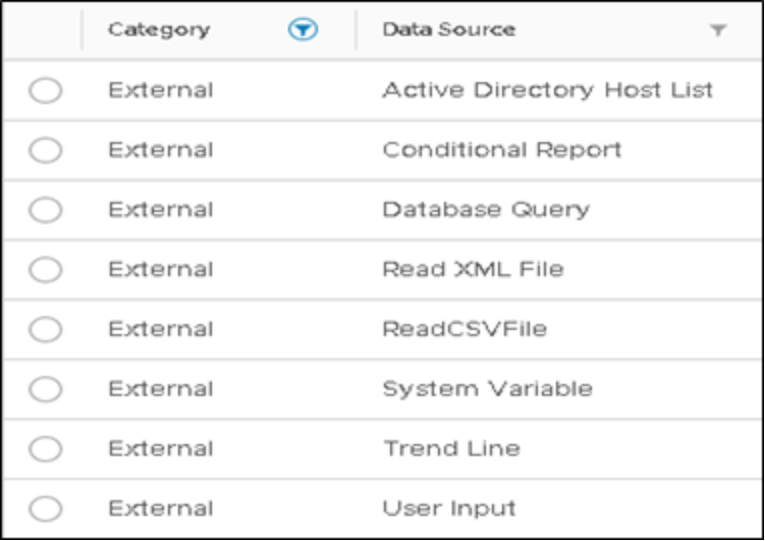
Figure 36. List of available data source types
The primary purpose of leveraging external data sources is to determine which assets listed in the CMDB are not protected, enabling the Backup Administrator to address the exposure of these unprotected clients. Alternatively, if clients in the CMDB no longer exist in the environment, then it provides the organization an opportunity to update the CMDB, providing an accurate inventory of the infrastructure environment.
This section provides an example where external data in the form of a comma separated value (CSV) file represent CMDB data which is imported into a custom report and compared to protected clients. While using CSV files is not sustainable or dynamic, using the Database Query data source type allows data to be extracted directly from a CMDB.
