

Guide for Configuring PowerStore with an SSL Certificate
Tue, 30 Aug 2022 14:11:47 -0000
|Read Time: 0 minutes
SSL certificates are commonly used when browsing the internet. Even corporate intranet pages are usually protected with an encrypted SSL connection. The two major security improvements when using SSL certificates are:
- Authenticity to prove a trusted server
- Encryption to protect (sensitive) data
Let’s start with some quick basics. I guess everyone has seen the nice error message about expired or invalid certificates in a browser. Some browsers even don’t allow you to continue when hitting a page with an expired certificate.
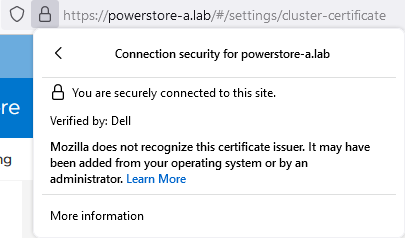
When Dell PowerStore is installed, it internally generates a self-signed certificate to allow data encryption between browser and PowerStore. Because the signed certificate is not trusted by the browser, a warning indicates that the page is not trusted. To mitigate the warning, PowerStoreOS allows the administrator to change the out-of-the box self-signed certificate with a trusted SSL certificate, ideally signed by a trusted certification authority (CA).
Besides the major commercial and public CAs, some companies run their own company-wide certificate authority. A private CA is usually part of a Private Key Infrastructure (PKI) and can provide certificates for different purposes. To allow the browser to validate certificates, the certificate of the private CA needs to be installed as a trusted Certificate Authority in the browser.
A certificate always consists of at least two parts:
- A secret key which is used to sign other certificates or to encrypt data
- A public key which is included in a certificate
When a certificate or data is signed or encrypted with a private key, the public shared key can be used to decrypt the information. Fingerprints within the certificate file help verify whether the shared key and decrypted information can be trusted.
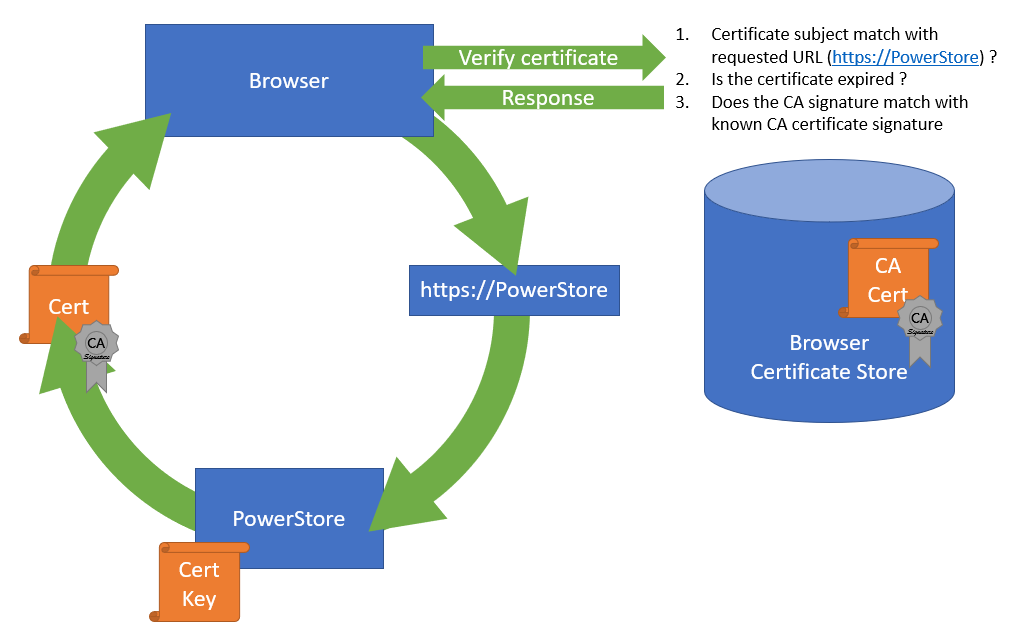
The structure of trusted certificates is always hierarchical and based on a Root CA certificate, which is at the top of the trust chain. A Root CA can have one or more Intermediate CAs, which are usually used to sign a server certificate by a certificate authority. In the same way when a client requests data from an SSL protected site, the server uses the certificate key to sign and encrypt the data and sends the response with the public certificate to the client. The client uses the response to check and validate the certificate attributes. These important attributes are the “valid from” and “valid to” timestamps, whether the URL matches the subject of the certificate, and whether the certificate is signed by a trusted CA certificate in the client certificate store. The check against a trusted CA certificate proves the authenticity. When all checks are passed, the browser indicates that the page can be trusted.
SSL certificates involve some different files:
Certificate | Description |
Certificate “key” file | Contains the key to encrypt and sign data. The key file should be kept safe. |
Certificate Sign Request (CSR) | The certificate sign request is generated with information from the key file and contains the information for a CA to issue a certificate file. Included information for a CSR generated with PowerStore: Subject: Concatenated string containing Organization, Organizational Unit, Location, State, and Common Name as given in PowerStore Manager when creating the CSR. SAN: A X509v2 extension called “Subject Alternate Names” which is the DNS and IP information as entered Public-Key: The public part of the private key file |
Certificate file | This could be either a single certificate or a certificate chain. A certificate chain is a set of concatenated certificates that allows clients to validate a certificate down to a trusted (CA) certificate. There are different file formats possible: PEM: “Privacy-Enhanced Mail” is commonly used to exchange certificates DER: “Distinguished Encoding Rules” is a binary encoding for PEM files PFX/PKCS: Another type called personal information exchange format When dealing with SSL certificates for Dell PowerStore, the PEM format is used. |
CA Certificate / | This is the public certificate of the issuer CA of a certificate. A PowerStore does not know anything of the issuer and needs the CA certificate to build the whole chain of trust for the certificate. Sometimes the file includes the whole certificate chain that consists of concatenated PEM certificates CA -> [Intermediate CA] -> PowerStore The included certificates in a chain depend on the issuer of a certificate. For PowerStore, we require the chain of certificates in following order:
|
Since PowerStoreOS 2.0, it’s possible to install 3rd party / signed server certificates for PowerStore T models in a block only deployment using PowerStore REST API or PowerStore CLI. PowerStoreOS 3.0 adds support for PowerStore T unified deployments and a GUI in PowerStore Manager for SSL import. This provides a comfortable way to generate a certificate sign request (CSR) and install the certificate. The certificate key file is stored in PowerStore and cannot be exported.
The next sections describe how to use PowerStore Manager and the PowerStore CLI to install a third party SSL certificate.
Installing a third party SSL certificate (PowerStore Manager)
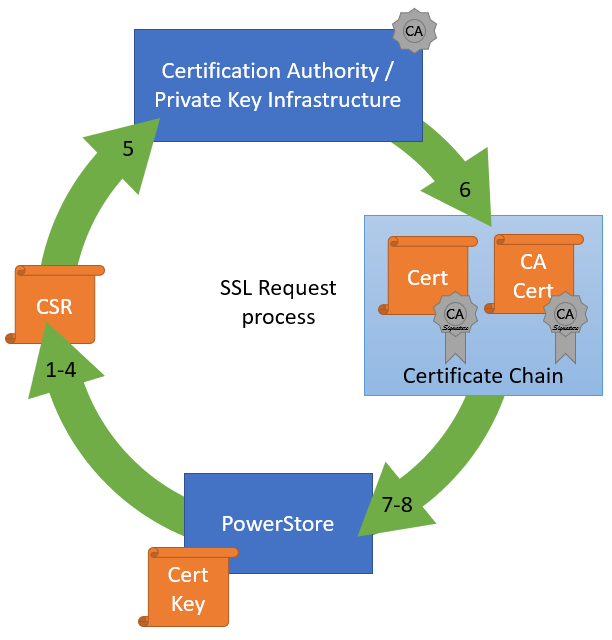
The following figure illustrates the steps required to deploy the certificate in PowerStore Manager:
- Log into PowerStore Manager.
Note that your browser shows that the connection is not secure: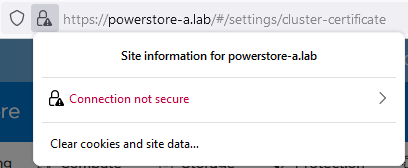
- Go to PowerStore Settings > Security > Signed Cluster Certificate.
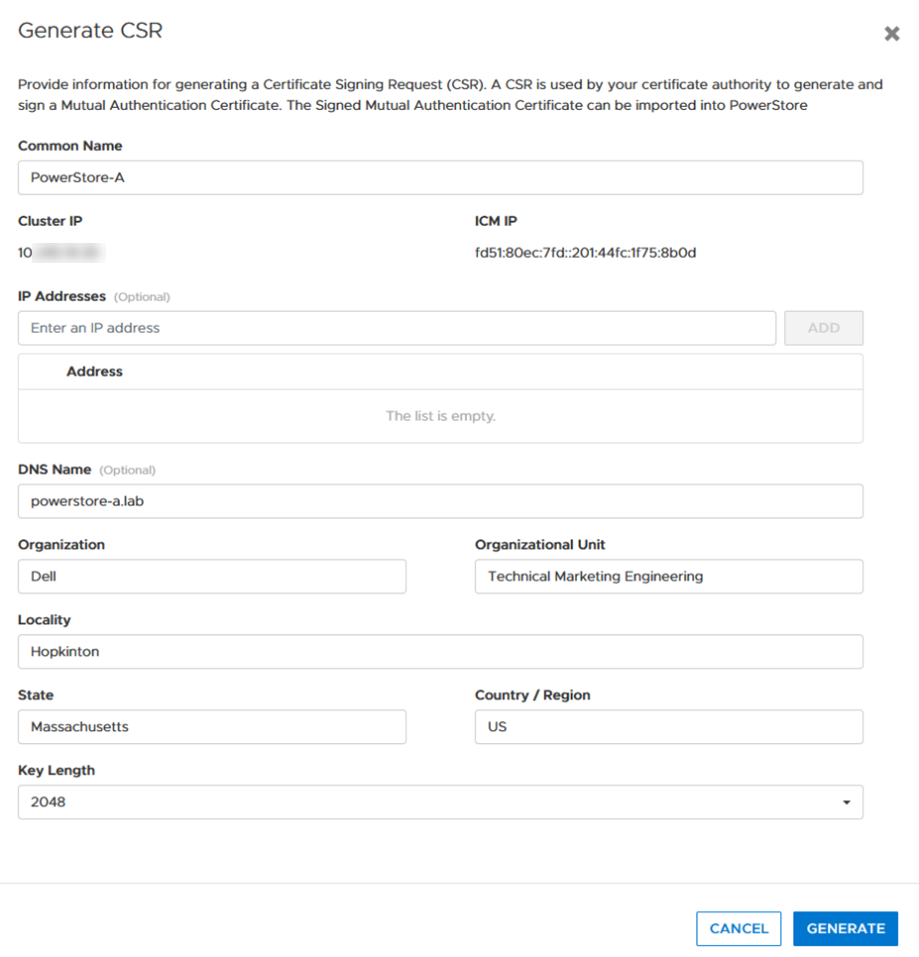
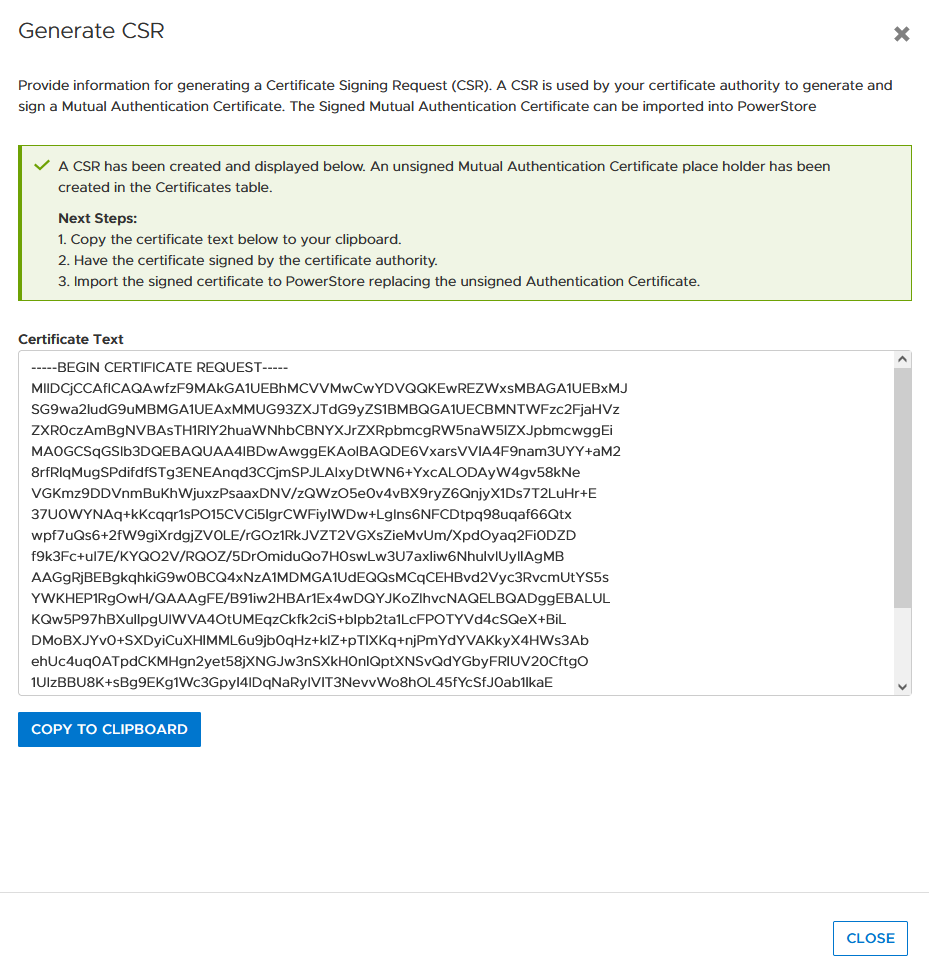
- Click the Generate CSR button and enter the required information to request a certificate.
a. Common Name Name of the certificate – usually the PowerStore cluster name
b. Cluster and ICM IP Mandatory for the Certificate and can’t be changed
c. IP Addresses Alternate IP Addresses which should appear in the certificate.
d. DNS name PowerStore FQDN
e. Organization Company Name
f. Organizational Unit Team / Organization
g. Locality Town
h. State State
i. Country/Region Two-letter country code
j. Key Length 2048 or 4096
4. When the CSR is created, click copy to clipboard and export the CSR content to a file -> for example, PowerStore.CSR
Optional: you can use the openssl tool to extract the contents of the CSR in a human readable format:
# openssl req -noout -text -in PowerStore.CSR
5. Send the CSR to your Certification Authority / PKI.
When there is an option to specify the format of the response, choose “PEM” format for the PowerStore and CA certificate. These files can be easily concatenated to a single certificate chain file (using the Linux CLI or a text editor) for import:
# cat powerstore.crt CA.crt > chain.crt
6. If not completed already, import the CA Certificate into your browser.
7. In PowerStore Manager, import the certificate chain in same screen where the CSR was generated.
Important: Sometimes the certificate file is in blocks. PowerStore expects the certificate in single lines, as in the following example with a PowerStore- and CA certificate:
-----BEGIN CERTIFICATE----- [...Single line PowerStore certificate content...] -----END CERTIFICATE----- -----BEGIN CERTIFICATE----- [...Single line CA Certificate certificate content...] -----END CERTIFICATE-----
If the individual certificates are not on a single line, the import will fail with the error “Failed to update certificate in credential store. Please verify your certificate chain. (0xE09010010013)”. You can use the openssl tool to verify that the file is ok:
# openssl x509 -in powerstore-chain.crt -noout -text
8. Start using PowerStore with a trusted HTTPS connection.
Installing a third party SSL certificate (PowerStore CLI)
Follow these steps to generate a certificate with PowerStore CLI for PowerStore-A. Be sure to format the CSR and certificate file correctly.
1. Generate CSR:
cli> x509_certificate csr -type Server -service Management_HTTP -scope External -key_length 2048 -common_name PowerStore-A -dns_name powerstore-a.lab -organizational_unit "Technical Marketing Engineering" -organization Dell -locality Hopkinton -state Massachusetts -country US
The response shows an ID and the CSR in a block. Keep the ID noted somewhere as it will be required for import. Also, use a text editor to make sure BEGIN- and END CERTIFICATE REQUEST are each on their own line when requesting the certificate:
-----BEGIN CERTIFICATE REQUEST----- [... a nice formatted block or single line ...] -----END CERTIFICATE REQUEST-----
2. Use CSR content to request the certificate.
3. Ensure that the issued certificate file is a single line string as required for import in PowerStore Manager. Note that the required line breaks need to be “\n”.
4. Import the certificate by using the ID and the certificate string:
cli> x509_certificate -id f842d778-0b28-4012-b8d5-66ead64d38e4 set -is_current yes -certificate “-----BEGIN CERTIFICATE-----\n[...Single line PowerStore certificate content...]\n-----END CERTIFICATE-----\n-----BEGIN CERTIFICATE-----\n[...Single line CA Certificate certificate content...] \n-----END CERTIFICATE-----"
Terms used:
CA Certification Authority
CN Common Name
CSR Certificate Sign Request
chain Single “chain” file with concatenated certificates
key Private certificate key
PEM Privacy-Enhanced Mail and commonly used to exchange certificates
SAN Subject Alternate Name
Resources
Author: Robert Weilhammer, Principal Engineering Technologist



