

Dell Technologies Collaborative Contributions to OCP NIC 3.0 Development
Download PDFMon, 16 Jan 2023 13:44:25 -0000
|Read Time: 0 minutes
Summary
After the release of OCP2.0, Dell Technologies collaborated with various technology leaders to design the all-inclusive OCP3.0 adapter card. This DfD shares the story of how Dell Technologies contributed to the OCP3.0 design and will explain how this design is superior to alternate adapter card form factors such as OCP2.0 and PCI.
History Briefing
The Open Compute Project (OCP) is a non-profit organization consisting of technology leaders working together to define and standardize superior data center product designs. In 2015 the group released the first standard OCP2.0 adapter card and soon after decided to focus development around improving the network interface of the next-gen OCP3.0 adapter card. In 2017, Dell Technologies began actively participating with OCP3.0 collaborators to produce the superior NIC adapter card.
Figure 1 - OCP3 Card Figure 2 - Electrical test fixture that Dell Technologies contributed for the 2020 Virtual OCP Summit. *Note that you must register online to access videos*
Key Contributions to OCP3.0
By sharing and making public proprietary test fixtures and design concepts from the existing rack network daughter card (rNDC), Dell Technologies was a key contributor in defining the OCP3.0 architecture in various ways:
1. Designing and manufacturing many of the compliance test fixtures required for compliance testing; this includes PCIe electrical compliance (as seen in Figure 2), systems management, and thermal tier compliance
2. Architecture design contributions taken from the rNDC design:
a. Simplified power supply
b. Basic systems management
c. Complete compliance specified with the adapter, including fixtures for industry-wide consistency
d. Reliability requirements to simplify system integration
e. Mechanical drawings with tolerances
Why OCP3.0 is Important
Production units of OCP3.0 adapter card solutions arrived on the market in 2019 and outperformed existing alternative solutions in various ways:
1. Open > Proprietary
a. Completely open specifications
b. Dell customizations through software and firmware
c. Decreases time to market with new technologies
2. OCP3.0 > OCP2.0
a. OCP NIC 3.0 has a defined SFF mechanical specification, whereas OCP2 did not have defined tolerances, which enables a seamless integration
b. Simplified power delivery, reducing complexity on the system and allowing more general support for adapters
c. Improved thermal performance and power capability
d. Added Hot-Plug capability, which allows for operation in high-availability systems
e. Host interface forward looking to PCIe Gen 5
f. Adapter includes all necessary mechanical components, allowing for ease of replacement
g. Base systems management allows systems to intelligently power the card or not
3. OCP3.0 > PCI
a. More compact design allowing for users to stack PCIe and OCP3 slots in a 1U server design where two PCIe cards would not fit
b. Full compliance mechanical specifications, as explained in 1a
c. High-speed sideband management (NC-SI)
d. Base systems management requires thermal monitoring
4. General Improvements
a. Forward looking for next 5-7 years of use for mainstream servers, including support to 400G I/O throughput
b. Support for hot-aisle and cold-aisle operation using the same adapter
c. Base systems management requires thermal monitoring
Dell Technologies currently supports OCP3.0 on the PowerEdge R6525, R7525 and C6525, and will include support for many future platforms, including the PowerEdge R650, R750 and C6520.
The OCP3.0 NIC adapter card is a standardized data center peripheral that became realized because competing technology leaders, such as Dell Technologies, HPE and Lenovo, were willing to collaborate proprietary information to design a superior innovation together. To learn more about The Open Compute Project, visit www.opencompute.org.
Related Documents

How Dell and Broadcom can help you make the transition to IPv6
Thu, 14 Mar 2024 16:56:04 -0000
|Read Time: 0 minutes
IPv4 vs. IPv6: How we got here
As the internet grew and commercialized late last century, it became increasingly clear that Internet Protocol version 4 (IPv4) limitations would eventually present issues. Enter Internet Protocol version 6 (IPv6) in the 1990s. Despite the technology’s age, its adoption has been slow in the US. Until very recently, many companies and other entities still primarily used IPv4, as shown by IPv6 adoption trackers such as one from Google.[1] Recently, however, the transition to IPv6 has been ramping, as some of those IPv4 limitations—such as the dwindling pool of available IPv4 addresses—are quickly becoming reality. One effort to encourage this transition includes a 2020 mandate from the U.S. Office of Management and Budget (OMB) requiring federal government agency devices be at least 80 percent IPv6-only by 2025.[2]
Regardless of mandates or address pools, there are a host of other reasons to choose IPv6 over IPv4. IPv6 includes features such as support for larger packets and multicasting, simpler header formats, smaller routing tables, and the elimination of the network address translation (NAT) process—all of which can increase performance over IPv4 in certain use cases. IPv6 also has built-in end-to-end encryption and name resolution protocol enhancements that contribute to better base security than IPv4.
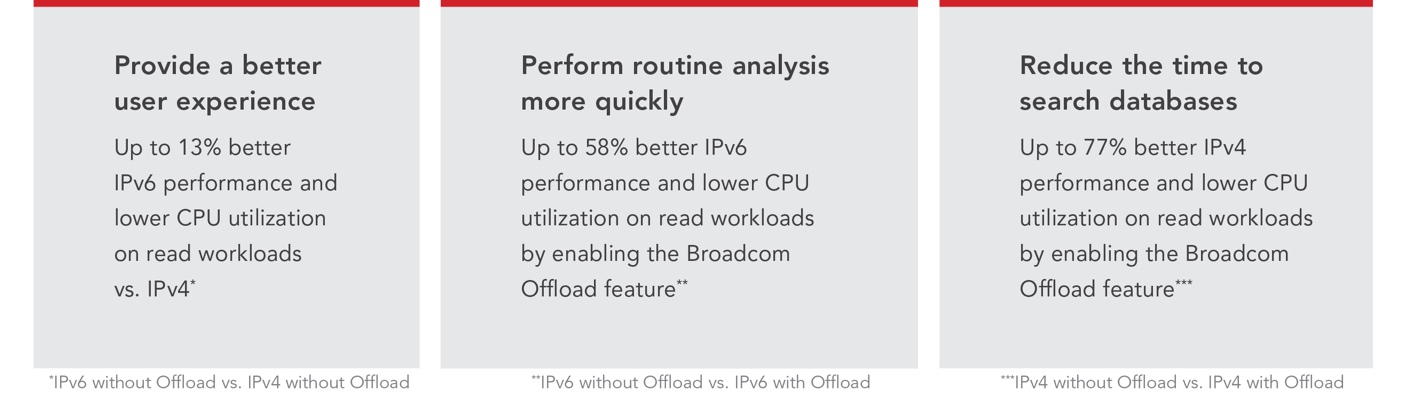
Despite the advantages of using IPv6, some companies have resisted transitioning because it’s not a small undertaking. In this paper, we explain why making the transition can be worth the investment and introduce a solution to help make the transition easier: Dell and Broadcom™ combine to have one of the first IPv6-only compliant end- to-end solutions. We also present the results of our testing, including performance advantages for IPv6 over IPv4 on read workloads and larger performance increases for IPv4 and IPv6 available by enabling the Offload feature in the Broadcom network interface cards (NIC).
Why organizations are shifting to IPv6
The transition to IPv6 has been a long, slow process that is complicated by the fact that IPv4 and IPv6 are not compatible, requiring companies to either choose just one or manage two networks via dual stack. For many companies, however, fully abandoning IPv4 is not an option. Doubling the number of networks you deploy means doubling the security concerns and hardware expenses. Additionally, applications built on IPv4 may need rebuilding or updating to work with IPv6. Despite these factors, we believe these complications to be worth the benefits you gain from taking advantage of the IPv6 landscape. Not only could organizations use the features we mention above, but as more companies and users move to IPv6, it will also be easier for others to follow. Thus, IPv6 will grow more valuable over time. In time, we hope this can lead to companies being able to shed their IPv4 network, leaving the single, more efficient IPv6 network in place.
Below, we detail some of the reasons to transition to IPv6 including current issues with IPv4, specific industries or government agencies with particular IPv6 requirements, and the benefits of IPv6.
The shortage of IPv4 addresses
One of the most important reasons for the push to transition to IPv6 is the limited number of possible IPv4 addresses. The IPv4 address space is a 32-bit field, meaning there are a total of 232, or roughly 4.3 billion, possible IPv4 addresses. As of November 2019, this address space was officially depleted, meaning there are no new IPv4 addresses to obtain.[3] This has created a premium on IPv4 addresses, allowing companies to sell or lease their addresses, increasing the costs of buying an IPv4 address. Amazon Web Services (AWS), for example, is adding a charge to every IPv4 address on its platform, citing a 300 percent cost increase of IPv4 addresses over the past 5 years.[4] Several workarounds for this problem exist, such as NAT, which allows organizations to map several private addresses within a local network to a single public address before transferring information to the internet. However, NAT comes with its own share of problems that can affect the performance and reliability of network applications. By adding an extra layer of translation and processing, NAT can introduce latency, errors, or packet loss.[5]
IPv6, by utilizing a 128-bit address field, increases available IP addresses to roughly 2128, or ~3.4*1028, essentially solving the address limitation for the foreseeable future. Companies that work with the Internet of Things (IoT), virtual reality (VR), self-driving vehicles, telecom, and other technologies requiring many IP addresses could avoid the IPv4 address market and limited address availability by moving to IPv6.
The federal government gets involved
US federal government agencies also find themselves impacted by the Office of Management and Budget (OMB) mandate, which claims that “full transition to IPv6 is the only viable option to ensure future growth and innovation in Internet technology and services.”[6] The latest version of the mandate states that running dual stack IPv4 and IPv6 networks, as previous versions of the mandate dictated, is too complex and no longer necessary. Instead, this new mandate requires IPv6-only networking, outlining four actions agencies must take:
- Create an IPv6 project team.
- Create and publish an agency-wide policy that states their intentions to phase out all IPv4 use and make all federal IT systems IPv6 enabled by the end of 2023.
- Identify and test at least one IPv6 pilot by the end of 2021.
- Develop a plan by 2021 for implementing IPv6-only networking, with milestones including at least 50 percent of IP-enabled assets, transitioned to IPv6-only by the end of 2023, and 80 percent on IPv6-only networks by the end of 2025.[7]
This means that by the end of the first quarter of 2024, federal agencies should already have half of their systems converted to IPv6-only, and the rest fully transitioned in just two more years.
Telecom and ISP industries are leading the way
With the development of the 5G cellular network and its need for high speeds and low latencies, much of the telecom industry has already converted to IPv6. As more and more devices connect over cellular networks with 5G, the increased address pool of IPv6 provides another benefit for internet service providers (ISPs) and cellular network companies. Additionally, the built-in quality of service (QoS) field in the IPv6 header allows ISPs to prioritize voice traffic over other traffic less vulnerable to latency such as http, SSH, and more. According to Akamai, a content delivery network and cloud computing company, ISPs and telecoms such as Comcast Cable, Verizon Business, AT&T, and T-Mobile have all reached IPv6 adoption above 70 percent—T-Mobile has as much as 92.7 percent IPv6 adoption.[8]
As these network providers continue to expand the IPv6 backbone, and mobile app developers continue to embrace IPv6 advantages, the rest of the world’s industries will lag behind if they continue to rely on IPv4.
How IPv6 helps your business
Even if you don’t need a wide range of IP addresses or aren’t part of the government mandate or the telecom industry, there are still benefits you can see from transitioning from IPv4 to IPv6. First, IPv6 could increase performance in several ways, mostly by increasing network efficiency. Second, IPv6 can offer some additional security benefits over IPv4. While IPv4 has had more security upgrades and patches to existing networks—simply by virtue of existing longer—the features that come with IPv6 offer stronger baseline security, which we examine in the following pages. Increased use and investment in IPv6 security enhancements should quickly close any existing gap between it and current IPv4 network security.
IPv6 can also improve network performance over IPv4 by using a more simplified header that takes less time and fewer resources to process. All IP packets include headers that contain the necessary information for proper route allocation and delivery. Much like the parts of a physical address tell postal workers the house, street, city, and country the letter originated from and is destined for, the IP header includes such information as the IP addresses of the source and destination devices, the version indicator, the total length of the packet, and other important information. Instead of requiring routers to perform a header checksum to ensure data integrity of every packet, IPv6 relies on Transmission Control Protocol (TCP), User Datagram Protocol (UDP), and other existing protocol checksums. Additionally, this header allocates optional and non-essential header fields to header extensions, leaving only the most vital information in the header for processing. This practice increases the efficiency of processing data packets across the network by getting the metaphorical “letter” to the right “building” quickly and letting the extension headers then direct it more specifically, to the equivalent of the correct suite, floor, or person.
IPv6 also eliminates the need for NATs as each device on an IPv6 network can have its own unique IP address. If devices aren’t having to share IP addresses, then the routers do not need to translate the network addresses to send the packet to the correct device, thus eliminating a step in the data transmission process. Finally, while the Maximum Transmission Unit (MTU) technology limits packet sizes in many networks to 1,500 bytes, IPv6 networks are capable of much larger packet sizes, up to 4 GB. IPv4 packets, on the other hand, are limited to much smaller theoretical maximums of 64K bytes.[9]
Another way that IPv6 increases network efficiency is with its ability to multicast instead of broadcast. On IPv4, data transmission is broadcast: When a packet leaves a source device, the information is sent to every host connected to the network. Every single host, in turn, checks the packet to see if the data is meant for it. IPv4 is like a kid yelling out, “Mom!” at a crowded playground, causing every mother in the vicinity to stop and check if their child is the one in need. IPv6, on the other hand, uses multicast, which is the ability to transmit a packet only to the device or devices for which it is intended. Now, instead of a child yelling, “Mom!” into a crowd, IPv6 taps their parent on the shoulder and talks directly to them, allowing the other moms to focus on their own children.
IPv4 routing tables, the list of networks and other links a router consults to determine where a packet should go, are quite large—and they continue to grow. The larger the table, the longer it takes to search and find the relevant data. While IPv4 addresses and networks can be difficult to aggregate or simplify, the structure of the IPv6 address allows for just that. The IPv6 address contains three parts: the network or site prefix, the subnet ID, and the host or interface ID.[10] Routers use a site prefix to route the packet through the internet. Network creators and ISPs can also use site prefixes to create packet groups that aggregate packets going in the same general direction. Aggregating the IPs like this allows the internet and routers to act similarly to public transportation. A person boards the train at a specific stop, rides it to another stop, then leaves the train and follows the maps to the exit nearest the actual destination they have in mind. With IPv6, packets behave similarly, where several packets with completely different final destinations can all “exit” the internet at the same stop and travel more granularly from there. This behavior allows for smaller, more efficient routing tables, speeding up the routing process and lowering the overhead on router hardware.
As we mentioned above, comparing IPv4 and IPv6 security isn’t completely straightforward, as professionals have invested more time and effort into the older IPv4 network. However, IPv6 has the potential to be more secure than IPv4 due to at least two built-in advantages. First, IPv6 has end-to-end encryption and authentication built in via default Internet Protocol Security (IPsec) inclusion. While enabling IPsec on IPv6 networks may not be mandatory in some places, implementing it provides better security.[11] The second way IPv6 enhances security is simply by being much larger. With its more numerous IP addresses, IPv6 networks are nearly impossible to brute-force scan.[12]
One more benefit of IPv6 is the ability for users to implement stateful or stateless configurations. While IPv4 network devices rely heavily on dynamic host configuration protocol (DHCP) devices to assign IP addresses, IPv6 networks can use the stateless address auto configuration (SLAAC) technology to let devices generate their own IPs without manual application or the use of a third-party device such as DHCP. If users prefer to use a stateful network, IPv6’s version of DHCP is available.
The NIST and transitioning to IPv6
According to the National Institute of Standards and Technology (NIST), “the IPv6 protocol
suite offers a vastly greater address space than IPv4 and supports significant new capabilities necessary to enable modern network environments.”[13] To facilitate this transition, the NIST National Cyber-security Center of Excellence (NCCoE) “is planning a project to provide guidance and reference architecture that address operational, security, and privacy issues associated with the evolution to IPv6-only network infrastructures.”[14]
The project aims to provide enterprise organizations attempting to transition to IPv6 with guidance and tools that will “ensure that evolving enterprise IT environments to be IPv6-only can be accomplished in a secure and robust manner.”[15]
Regardless of the size of your network, the NIST Cybersecurity Practice Guide will provide best-practices and documentation to ensure that your transition to IPv6 is secure. For more information about the transition resources available from the NIST, visit https://www.nccoe.nist.gov/projects/IPv6-transition.
How Dell servers and Broadcom NICs can help on your journey to IPv6
The National Institute of Standards and Technology (NIST) is part of the U.S. Department of Commerce and serves to support and promote technology and science innovation and investment.[16] In addition to mandating that government agencies switch to IPv6-only networks, the OMB has mandated the NIST to create a set of standards and tools to support the transition. The resulting U.S. Government IPv6 (USGv6) Program develops, tests, and maintains IPv6 standards to help companies and government agencies ensure successful IPv6 transitions and deployments. Vendors can use the IPv6 tests and certifications that NIST developed to certify that their products meet the requirements and standards defined by NIST’s program.[17] In response to the 2020 OMB mandate for all government agencies, NIST revised their USGv6 program to include several objectives including updating specifications to add new and remove old technologies and streamlining their testing program based on previous experience.[18] With a set of agreed upon standards, definitions, and requirements, NIST and the USGv6-r1 provide OEMs a way to ensure their customers that their products are ready for IPv6 implementation.
Dell Technologies™ is the first company to offer a full USGv6-r1 certified server and storage stack for IPv6-only networking.[19] Dell’s certifications include:
- Dell™ PowerEdge™ servers – first in the industry to be fully IPv6 Ready Logo 5.1.2 compliant with RedHat 8.4 and Windows 2019 and 2022.
- Dell PowerEdge iDRAC9 with FW version 5.10.0.00 – first baseboard management controller (BMC) validated by USGv6-r1 as IPv6-only compliant.
- Unity-XT storage array – first storage product validated by USGv6-r1 as IPV6-only compliant meeting the requirements in the IPv6-Only Functional v1.1 (36277) profile.[20]
- Additionally, PowerStore, PowerEdge with VMware 8.0.1, and PowerEdge with SUSE SLES15 SP4 are on the USGv6-r1 registry.
Additionally, Dell servers and storage leverage Broadcom NICs and Adapters to ensure network performance and security for IPv6 customers. Broadcom NICs such as the Broadcom BCM957508-P2200G dual-port 100GbE NIC include several IPv6 offloads that can boost network performance.[21] These offloads allow the NIC to directly handle some of the computational needs of the network rather than use the OS stack, which can provide lower latencies and lower CPU utilization dedicated to network traffic.[22] Broadcom BCM957508-P2200G dual-port 100GbE NICs also offer features such as NVME over Fabrics (NVMe-oF) capabilities that allow NVMe storage traffic to travel through network instead of directly through PCIe channels. NVMe-oF allows users to connect storage via Ethernet (TCP), Fibre, and RDMA.[23] This rerouting of storage network allows for extremely low latency to get the most out of NVMe-based storage.
To show how Dell and Broadcom can provide one great hardware stack option for your IPv6 needs, we conducted some testing to highlight the performance you can expect with IPv6-connected Dell PowerEdge R660 servers to a PowerStore 1200T storage array using 100GbE Broadcom 57508 NICs.
Broadcom NICs
Broadcom NICs can serve most networking needs because they offer speeds ranging from 1G to 200G. According to Broadcom, their network cards feature:
- “Low power adapters and controllers with outstanding thermal performance
- Low latency and high throughput RoCEv2 [for] ground-breaking performance
for machine learning, HPC and
storage applications - Broadsafe™ embedded security [for] Silicon Root of Trust and attestation delivering industry’s most secure Ethernet controller
- Modern architecture [that] delivers industry’s lowest latency and lowest CPU utilization for real-world network conditions
- TruFlow™ engine [to accelerate] virtual switch processing, reduces server CPU usage
- TruManage™ [for] end-user manageability needs to allow fine-tuning of networks for maximum performance
- On-chip tunneling protocol processing for Geneve, VXLAN, and NVGRE [that] provides up to a 5x throughput increase
- Acceleration engines for SDN and NFV [to] enable leading-edge service provider solutions”[24]
Measuring performance
The goal of our performance testing was to show the benefits of the USGv6-r1 IPv6-only certified Dell PowerEdge server and Broadcom NIC solution. This included investigating the performance differences between IPv4 and IPv6 in a real-world environment. Most North American users continue to rely on IPv4, which typically requires NAT or packet fragmentation support from a network router.[25] In a typical scenario, a routing device need only read an IPv4 packet to determine its destination and send it on its way. In the case of IPv4 using NAT or requiring packet fragmentation, the routing device must modify the packet before it can send it along, which requires overhead. We wanted to quantify the impact of this overhead on network performance.
Other than the Layer 3 protocol, every aspect of the test scenario was the same. We used Linux standard tools and NVMe/TCP and/or NFS transport protocols for this test. We did not attempt to enable the best speed of each of these protocols; rather, we used those protocols to drive the tests to compare any differences in speed based on the journey of that data provided by Layer 3 (IP).
We configured two Dell PowerEdge servers as SUSE Linux Enterprise Server 15 SP4 hosts, sending data of diverse sizes to a Dell PowerStore storage array using the transport protocols we identified earlier. The data traversed multiple switches we configured to provide Border Gateway Protocol (BGP) routing and packet fragmentation within a heterogeneous multi-hop network.
We configured the host networks using an MTU of 9,000, with a 1,500 MTU on the switches emulating the core network (which forced packet fragmentation). The edge switches used BGP routing to communicate with the core network.
Comparing IPv6 and IPv4 performance without the Broadcom Offload feature
First, we tested the relative performance of IPv6 and IPv4 on a write workload with the Broadcom Offload feature off. Table 1 presents the results. In terms of both performance (IOPS and throughput in MB per second) and CPU utilization, we observed approximate parity between the two IP versions at both block sizes we tested.
Table 1. IPv6 vs. IPv4 performance on a write workload with Offload off. Higher IOPS and MB/sec and lower CPU utilization are better. Source: Principled Technologies.
Write workload, Offload off |
|
|
| |
IP version | Block size | IOPS | MB/sec | Percentage CPU utilization |
IPv4 | 256K | 8,696.1 | 2,174.01 | 4.9 |
IPv6 | 256K | 8,752.1 | 2,188.02 | 4.9 |
IPv6 % improvement | 0.64% | 0.64% | 0.00% | |
IPv4 | 64K | 34,862.7 | 2,178.92 | 6.6 |
IPv6 | 64K | 34,972.1 | 2,185.76 | 6.5 |
IPv6 % improvement | 0.31% | 0.31% | 1.51% | |
Next, we ran the same test using a read workload. As Table 2 shows, in contrast to the comparable performance we observed on the write workload, IPv6 had a performance advantage over IPv4 on the read workload. At the larger block size of 256K, IPv6 delivered 13.83 percent greater performance. At the smaller block size of 64 K, IPv6 delivered 9.83 percent greater performance. These results indicate that users in a real-world setting would enjoy better performance by using IPv6. We also observed a CPU utilization improvement for IPv6.
Table 2. IPv6 vs. IPv4 performance on a read workload with Offload off. Higher IOPS and MB/sec and lower CPU utilization are better. Source: Principled Technologies.
Read workload, Offload off |
|
|
| |
IP version | Block size | IOPS | MB/sec | Percentage CPU utilization |
IPv4 | 256K | 19,987.8 | 4,996.95 | 14.1 |
IPv6 | 256K | 22,752.4 | 5,688.09 | 13.6 |
IPv6 % improvement | 13.83% | 13.83% | 3.54% | |
IPv4 | 64K | 73,194.1 | 4,574.63 | 13.9 |
IPv6 | 64K | 80,392.4 | 5,024.53 | 12.5 |
IPv6 % improvement | 9.83% | 9.83% | 10.07% | |
Measuring the impact of the Broadcom Offload feature on IPv6 performance
A secondary component of our testing was investigating the capabilities of the Broadcom IP Offload feature. IP Offloading is a feature Broadcom has implemented in its NIC (Layer 2) to process IP (Layer 3) data to offload the processing of this data from the OS/CPU, leaving those clock cycles to process user data rather than managing the flow control of the protocol. We refer to this feature as Offload.
Table 3 presents IPv6 performance on a write workload with Offload off and with Offload on. While performance was comparable under both conditions, CPU utilization was lower with Offload on.
Table 3. IPv6 performance on a write workload with Offload off and Offload on. Higher IOPS and MB/sec and lower CPU utilization are better. Source: Principled Technologies.
Write workload, IPv6 |
|
|
| |
Block size | IOPS | MB/sec | Percentage CPU utilization | |
Offload off | 256K | 8,752.1 | 2,188.02 | 4.9 |
Offload on | 256K | 8,615.5 | 2,153.88 | 2 |
Offload on % improvement | -1.56% | -1.56% | 59.18% | |
Offload off | 64K | 34,972.1 | 2,185.76 | 6.5 |
Offload on | 64K | 34,895.6 | 2,180.97 | 3.4 |
Offload on % improvement | -0.21% | -0.21% | 47.69% | |
Table 4 presents IPv6 performance on a read workload with Offload off and with Offload on. In contrast to the approximate parity we saw on the write workload, performance improved greatly with the use of Offload, particularly at the larger block size, where IPv6 delivered 58.15 percent greater performance than with Offload off. At the 64K block size, enabling Offload improved performance by 25.43 percent. Figure 1 illustrates these advantages. As we saw with the write workload, CPU utilization was lower with Offload on.
Table 4. IPv6 performance on a read workload with Offload off and Offload on. Higher IOPS and MB/sec and lower CPU utilization are better. Source: Principled Technologies.
Read workload, IPv6 |
|
|
| |
Block size | IOPS | MB/sec | Percentage CPU utilization | |
Offload off | 256K | 22,752.4 | 5,688.09 | 13.6% |
Offload on | 256K | 35,983.4 | 8,995.86 | 8.3% |
Offload on % improvement | 58.15% | 58.15% | 38.97% | |
Offload off | 64K | 80,392.4 | 5,024.53 | 12.5% |
Offload on | 64K | 100,840.9 | 6,302.55 | 7.3% |
Offload on % improvement | 25.43% | 25.43% | 41.60% | |
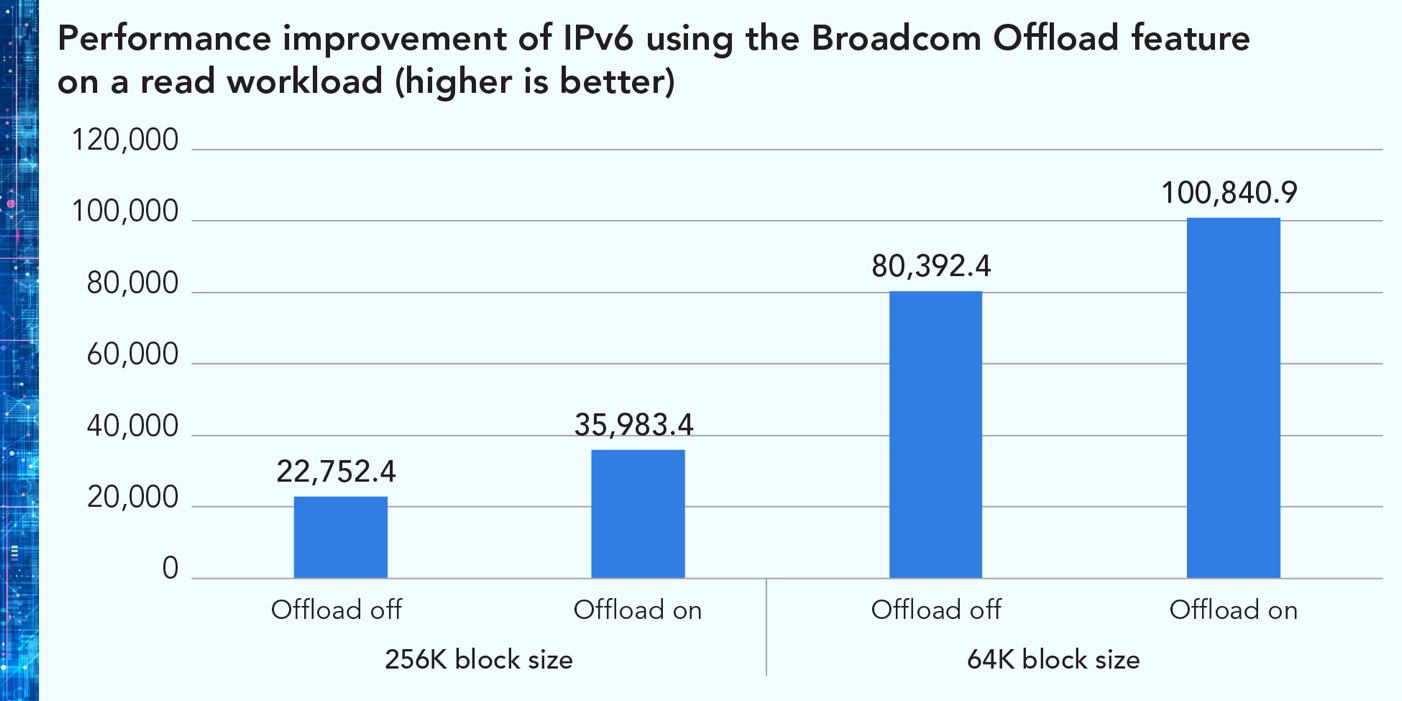
Figure 1. Performance improvement of IPv6 using Offload feature on a read workload. Higher is better. Source: Principled Technologies.
Measuring the impact of the Broadcom Offload feature on IPv4 performance
Table 5 presents IPv4 performance on a write workload with Offload off and with Offload on. As we saw with IPv6, performance was comparable under both conditions and CPU utilization improved with Offload on.
Table 5. IPv4 performance on a write workload with Offload off and Offload on. Higher IOPS and MB/sec and lower CPU utilization are better. Source: Principled Technologies.
Write workload, IPv4 |
|
|
| |
Block size | IOPS | MB/sec | Percentage CPU utilization | |
Offload off | 256K | 8,696.1 | 2,174.01 | 4.9 |
Offload on | 256K | 8,596.0 | 2,148.99 | 2.0 |
Offload on % improvement | -1.15% | -1.15% | 59.18% | |
Offload off | 64K | 34,862.7 | 2,178.92 | 6.6 |
Offload on | 64K | 34,727.8 | 2,170.49 | 3.6 |
Offload on % improvement | -0.38% | -0.38% | 45.45% | |
As Table 6 shows, the impact of enabling Offload on IPv4 read performance followed the same pattern we saw with IPv6. Using Offload dramatically improved read performance, by 77.90 percent at the larger block size and by 38.73 percent at the 64K block size. Figure 2 highlights these performance improvements. Once again, using Offload improved CPU utilization.
Table 6. IPv4 performance on a read workload with Offload off and Offload on. Higher IOPS and MB/sec and lower CPU utilization are better. Source: Principled Technologies.
Read workload, IPv4 |
|
|
| |
Block size | IOPS | MB/sec | Percentage CPU utilization | |
Offload off | 256K | 19,987.8 | 4,996.95 | 14.1 |
Offload on | 256K | 35,559.3 | 8,889.81 | 8.1 |
Offload on % improvement | 77.90% | 77.90% | 42.55% | |
Offload off | 64K | 73,194.1 | 4,574.63 | 13.9 |
Offload on | 64K | 101,545.6 | 6,346.60 | 7.4 |
Offload on % improvement | 38.73% | 38.73% | 46.76% | |
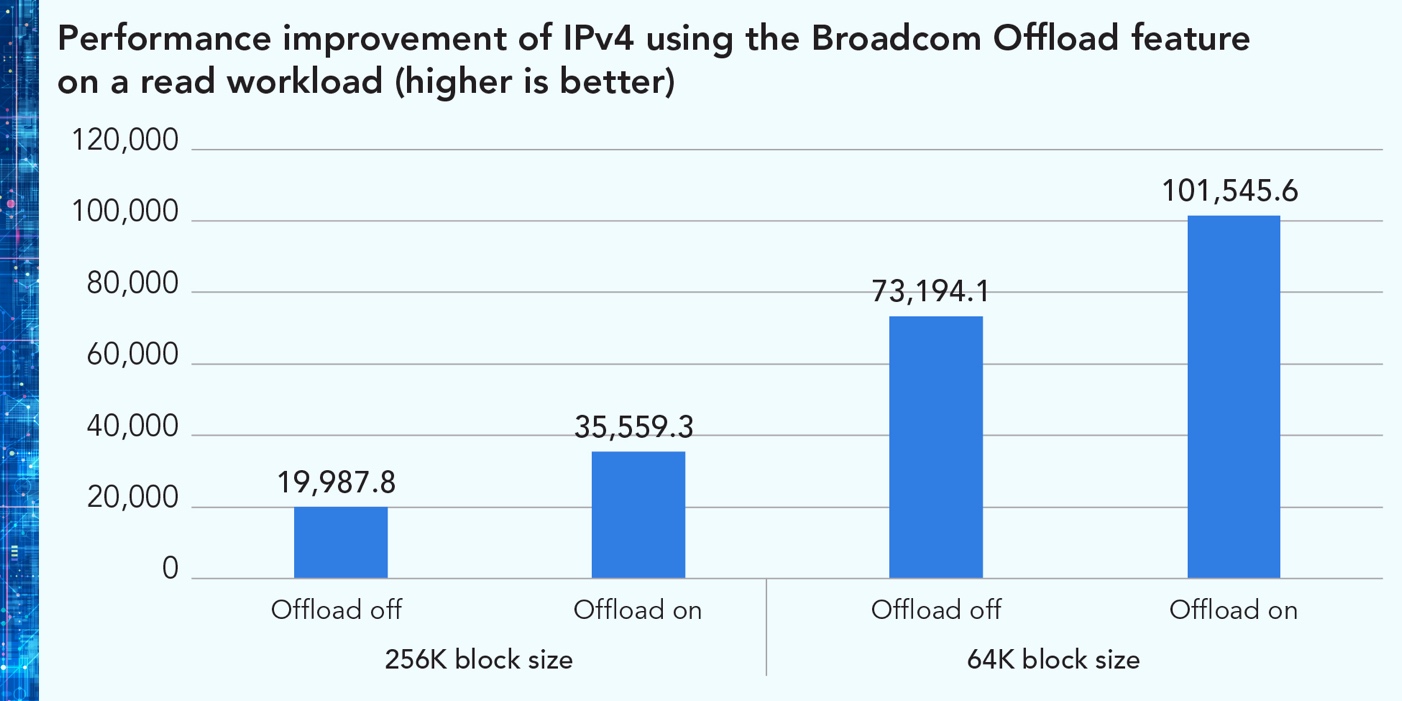
Figure 2. Performance improvement of IPv4 using the Broadcom Offload feature on a read workload. Higher is better. Source: Principled Technologies.
While we have discussed many advantages to making the shift to IPv6, our test results demonstrate that companies who opt not to do so immediately could reap performance benefits on read workloads—and CPU utilization benefits on both read and write workloads—by using the Dell-Broadcom solution we tested and enabling the Broadcom NIC Offload feature.
Conclusion
With IPv4 address pools rapidly disappearing and a federal mandate for government agency devices to begin shifting to IPv6-only and telecom 5G with IoT and edge devices, it’s clear that IPv6 is the future. Transitioning from IPv4 to IPv6 can be a challenge, so organizations may be interested to learn that switching to IPv6 has the potential to improve performance. In our testing without the Broadcom Offload feature, IPv6 delivered comparable performance to IPv4 on write workloads and better performance on read workloads while also reducing CPU utilization. When we enabled the Broadcom Offload feature on both IPv6 and IPv4, read workload performance increased dramatically and CPU utilization on both read and write workloads improved. Whether your organization is transitioning to IPv6 right away or choosing to delay the shift, this feature can boost performance on read workloads, which can improve the experience for users, reduce backup windows, and allow databases to load more quickly.
This project was commissioned by Dell Technologies.
January 2024
Principled Technologies is a registered trademark of Principled Technologies, Inc.
All other product names are the trademarks of their respective owners.
[1] Google, “IPv6,” accessed December 21, 2023, https://www.google.com/intl/en/ipv6/statistics.html.
[2] Russell T. Vought, “MEMORANDUM FOR HEADS OF EXECUTIVE DEPARTMENTS AND AGENCIES,” accessed December 21, 2023, https://www.whitehouse.gov/wp-content/uploads/2020/11/M-21-07.pdf.
[3] RipeNCC, “What is IPv4 Run Out?” accessed December 21, 2023,
[4] Jeff Barr, “New – AWS Public IPv4 Address Charge + Public IP Insights,” accessed December 21, 2023,
https://aws.amazon.com/blogs/aws/new-aws-public-ipv4-address-charge-public-ip-insights/.
[5] Linkedin, “How can NAT affect the performance and reliability of network applications?” accessed December 21,
2023, https://www.linkedin.com/advice/0/how-can-nat-affect-performance-reliability-network.
[6] Russell T. Vought, “MEMORANDUM FOR HEADS OF EXECUTIVE DEPARTMENTS AND AGENCIES,” accessed December 21, 2023, https://www.whitehouse.gov/wp-content/uploads/2020/11/M-21-07.pdf.
[7] Russell T. Vought, “MEMORANDUM FOR HEADS OF EXECUTIVE DEPARTMENTS AND AGENCIES.”
[8] Akamai, “IPv6 Adoption Visualization,” accessed December 21, 2023,
[9] Network Academy, “IPv4 vs IPv6 - Understanding the differences,” accessed December 21, 2023,
[10] Diego Asturias, “Migration to IPv6: Benefits and Techniques,” accessed December 21, 2023,
[11] Diego Asturias, “Migration to IPv6: Benefits and Techniques.”
[12] Diego Asturias, “Migration to IPv6: Benefits and Techniques.”
[13] “IPv6 Transition,” accessed December 21, 2023, https://www.nccoe.nist.gov/projects/IPv6-transition.
[14] “IPv6 Transition.”
[15] “IPv6 Transition.”
[16] NIST, “About NIST,” accessed December 21, 2023, https://www.nist.gov/about-nist.
[17] NIST, “USGv6,” accessed December 21, 2023, https://www.nist.gov/programs-projects/usgv6-program/usgv6.
[18] NIST, “USGv6 Revision 1,” accessed December 21, 2023,
https://www.nist.gov/programs-projects/usgv6-program/usgv6-revision-1.
[19] George Dilger, “Industry First IPv6-only Support on Servers and Storage,” accessed December 21, 2023,
https://www.dell.com/en-us/blog/industry-first-ipv6-only-support-on-servers-and-storage/.
[20] George Dilger, “Industry First IPv6-only Support on Servers and Storage.”
[21] Broadcom, “Broadcom Ethernet NICs PCIe NIC Ethernet Adapters Specification Sheet,” accessed December 21,
2023, https://docs.broadcom.com/doc/PCIe-NIC-Ethernet-Adapters-Specification-Sheet.
[22] Eden Kim and Fred Zhang, “Optimizing NVMe® over Fabrics (NVMe-oFTM),” accessed December 21, 2023,
https://www.snia.org/sites/default/files/education/snia-optimizing-nvme-over-fabrics-nvme-of.pdf.
[23] Juan Mulford, “What is NVMe-oF?,” accessed December 21, 2023, https://www.storagereview.com/review/nvme-nvme-of-background-overview.
[24] “Ethernet Network Adapters,” accessed December 21, 2023,
https://www.broadcom.com/products/ethernet-connectivity/network-adapters.
[25] Google, “IPv6,” accessed December 21, 2023, https://www.google.com/intl/en/ipv6/statistics.html.

Foundation for Enterprise Security and Cyber Resiliency: Dell PowerEdge and Broadcom
Wed, 13 Mar 2024 20:49:09 -0000
|Read Time: 0 minutes
Executive Summary
There are numerous challenges companies face to establish and maintain the cybersecurity capabilities required to operate in today’s complex and increasingly hostile digital world. Companies are reminded daily of the potential cost to their reputation, revenue and more for failing to maintain a competent cyber resiliency profile. Often, even a single breach can result in regulatory fines, loss of revenue and customers, and in some cases may even cause existential implications for a firm.
A Futurum Group study conducted in 2023, with more than 150 IT Security professionals from companies with 1,000 or more employees resulted in several insights. More than 80% of companies surveyed reported an increase in their cybersecurity budgets while nearly 50% are increasing their cybersecurity headcount in response to these growing threats. In terms of challenges faced, the top two items were limited budgets and high solution costs, indicating a need to improve cybersecurity without significant cost implications.
As part of The Futurum Group’s ongoing research and analysis, The Futurum Group Labs has developed a cyber-resiliency framework that is designed as a holistic tool for evaluating how well a product or service offering helps a company meet their cybersecurity requirements. This framework incorporates multiple industry standards and best practices to provide a comprehensive perspective for evaluating their security requirements. The Futurum Group utilizes this framework when evaluating security aspects of products and services.
In this paper we review the important security features of Dell and Broadcom components, and how they can help companies improve their security posture and overall cyber resiliency. The Futurum Group Labs tested Dell 16th Generation PowerEdge servers with Broadcom 57508 Ethernet Network Interface Card (NIC) and PERC RAID controller cards both within our lab facilities, and remotely within Dell’s lab. This analysis provides a real-world use case of managing security across a multi-site, distributed environment.
Summary of Findings
The Futurum Group Labs performed hands on testing and review of many of the security features and capabilities of Dell PowerEdge 16th Generation servers, together with Broadcom 57508 dual port 100 Gb Ethernet NIC and Broadcom SAS4116W ROC based Dell PERC 12, H965i RAID cards. Our evaluation included analyzing security best practices, along with overall system security features and capabilities.
Additionally, The Futurum Group has developed a security framework comprising areas for review across multiple areas of enterprise security. The Futurum Group’s Security Framework builds upon industry best practices and multiple NIST standards and provided the basis for our evaluation process.
Against this framework, we found the Dell PowerEdge servers, together with Dell PowerEdge RAID Controller 12 (PERC) and Broadcom NICs provided an integrated security solution that met or exceeded requirements in all areas evaluated. Strengths included the following areas:
- Adherence to standards, including the NIST concepts of Identify, Protect, Detect, Respond & Recover
- Zero Trust security principles utilized by both Dell and Broadcom for all aspects of the systems
- Integrated security management via iDRAC, OME and CloudIQ provide enterprise-wide capabilities
- Dell’s Secure Component Verification Process helps ensure security from order to delivery
Futurum Group’s Security Framework
The Futurum Group has developed a security framework for evaluating the overall cyber resiliency rating of products operating within IT environments. This framework encompasses multiple inter-related aspects of security including ensuring that secure design methodologies are utilized during product creation.
The first area assessed is the design methodology utilized for developing products and services. Next the security features of a product are evaluated, along with the security of the manufacturing and supply chain processes. Finally, the IT security implementation of a company using the product is important. Taken together, these components provide a comprehensive tool for evaluating and analyzing the security profile of a product operating within a particular company. An overview is shown in Figure 1.
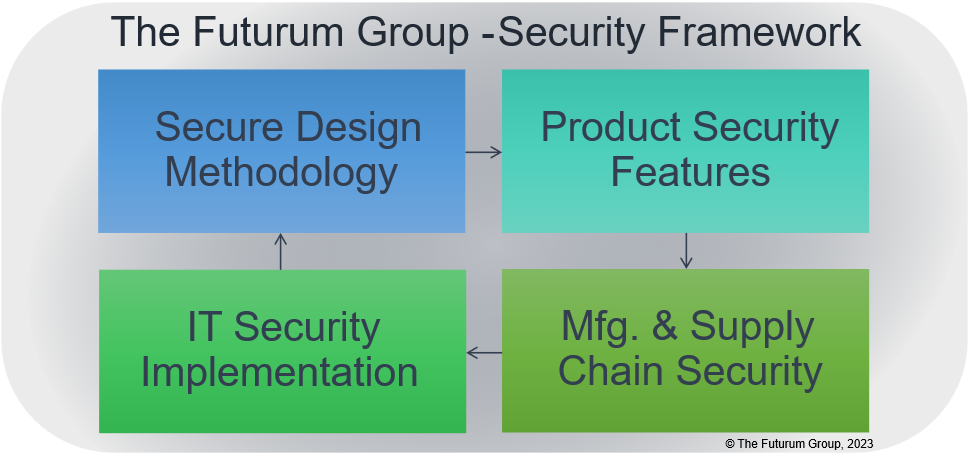
Figure 1: Security Framework Overview (Source: The Futurum Group)
It should be noted that “IT Security Implementation” was outside of the scope of work for this project. Since security responsibilities fall upon each company to utilize and implement security features appropriately.
Dell Solution Overview
As a foundation for securing PowerEdge server products, intrinsic security practices are incorporated into hardware product design and software or firmware code development. These practices include the following processes to ensure security features are implemented at the time of product inception and continue throughout the development cycle. To perform this practice effectively, Dell engineers are required to take mandatory security training before handling the code. Security “champions” are assigned to each development team to drive a security culture within the organization. Dell combines all components to create an integrated solution with hardware, software and services that together address security threats companies are facing.
Dell and Broadcom asked The Futurum Group Labs to evaluate Dell’s servers together with Broadcom add-in cards with respect to how these products can help IT clients address security vulnerabilities and achieve the levels of cyber resiliency necessary for operations in today’s challenging environment.
Specifically, The Futurum Group Labs validated the latest, 16th Generation Dell PowerEdge servers, together with Dell - Broadcom PERC 12 RAID cards and Broadcom 57508 NIC cards, along with relevant firmware and software that address security and cyber resiliency within IT environments. The Broadcom components helped provide overall end-to-end security capabilities through integration into Dell’s management tools.

Figure 2: Dell PowerEdge and Broadcom NIC Products (Source: Dell and Broadcom)
Dell’s Security Principles for Cyber Resiliency
As companies have become increasingly sophisticated in their approach to security, it is clear that point solutions are insufficient to address today’s complex cybersecurity requirements. While there is naturally a focus on the hardware components themselves, an important part of the overall Dell and partner security ecosystem is the use of critical software elements that help enable security features and provide easy-to-use interfaces for IT users.
| Futurum Group Comment: Too often, security features require IT administrators to choose between usability or security. As a result, IT administrators may ignore or circumvent security best practices to improve ease of use. The management tools of the PowerEdge systems enable IT users to easily follow best practices while utilizing the comprehensive security features of Dell servers and Broadcom. This functionality helps reduce attack surfaces for malicious actors, while maintaining usability and performance. |
As described previously, The Futurum Group’s Security Framework incorporates multiple best practices and industry standards, including NIST Cybersecurity Framework (CSF) which outlines five tenants:
- Identify: Ensure that an organization understands and can manage cybersecurity risk, assets, and data
- Protect: Develop and implement appropriate safeguards to ensure critical infrastructure is protected
- Detect: Quickly detect cyber events via anomaly detection and continuous monitoring
- Respond: Prepare and implement the ability to take appropriate action in response to a cyber event
- Recover: Establish the ability to maintain business resiliency and restore impacted systems
The Futurum Group Security Framework extends the NIST framework, including the following areas for assessing Dell’s Cyber Resilient Architecture for security:
- User authentication and authorization using multi-factor authentication applied to users and devices (User AA and Device AA) with role-based and least privileged access controls.
- Dell PowerEdge hardware RoT creates a chain of trust from firmware to devices and supports complete customization of Secure Boot, including removal of all industry-standard certificates provided by Microsoft, VMware, or the UEFI CA.
- Using PowerEdge cyber resilient platform RoT extends to Secure Enterprise Key Management for data-at-rest protection.
- Applications and workload security to protect runtime environments, leveraging data and network security technologies including end-to-end encryption and cryptographic signatures.
- Utilize Security Protocol and Data Model (SPDM) capabilities for device attestation as part of the Zero-Trust/cyber resiliency architecture. Future capabilities include internal encrypted communication capabilities.
- Auditing and analytics for visibility and alerting of security issues using persistent event logging and real-time code and firmware scanning.
- Automation and orchestration technologies to enable automated API and CLI driven actions, along with enterprise web UI tools to provide easy-to-use global management of security alerting, reporting and automation.
Test and Validation Findings
The Futurum Group Labs Security Framework shown previously in Figure 1, was used to analyze the overall security capabilities of products or features. Our analysis examined each aspect of the Security Framework with details provided in the following four sections.
1 - Secure Design Methodology
Requirements
Confirm that security considerations begin at product inception with cybersecurity and resiliency capabilities integrated throughout product design and development.
Verify that hardware security features based on Zero Trust, such as tamper proof TPM often form the basis of software security, to deliver an integrated secure system.
Asses if the software architectures leverage hardware security and utilize the available security capabilities. Additionally, validate that threat modeling and penetration testing along with external audits and ongoing mitigation of vulnerabilities are performed.
Dell PowerEdge and Broadcom Design
Dell utilizes a secure Software Development Lifecycle (SDL) as the basis for instilling security throughout the design process. A comprehensive SDL process should ensure that any identifiable attack methods are mitigated utilizing standards-based security mechanisms to thwart these attack vectors.
As outlined previously, security starts with using a secure design methodology, with multiple considerations required to help products provide cyber resiliency:
| - Security is considered for each feature - Following industry best practices, Dell software is designed to obstruct, oppose and counter malicious attacks - External audits of security features - On-going evaluation of new vulnerabilities - Rapid response to common vulnerability exposures (CVEs) with remediation | |
Table 1: Dell SDL Principles | Figure 2: Dell SDL Model |
Additional aspects of secure design include end-to-end secure communication based upon cryptographically signing certificates used to authenticate and authorize components such as with Device-ID, 802.1x, and SPDM.
Finally, even with good design and secure implementations, vulnerabilities and breaches may still occur. Thus, it is important for products to be designed with resiliency and Zero Trust implementation, so that when penetrations do occur, their impact is limited. Dell’s rapid response to critical CVEs and patching of identified components is an important aspect of mitigating threats from CVE’s as they arise.
| Futurum Group Comment: Dell’s rapid response to critical CVEs and patching of identified components is an important aspect of mitigating threats from CVE’s as they arise. As one of the largest system vendors, Dell leverages their significant real-time monitoring via CloudIQ and other tools, to quickly respond to emerging threats and provide their customers with tools and processes to thwart attacks. |
2 – Product Security Features
Product security was an area of particular focus by The Futurum Group Labs when measuring how Dell PowerEdge servers, together with Broadcom based PERC 12 and 57508 Ethernet NICs met Futurum’s Security Framework. System security requires a layered approach, with hardware security features and capabilities utilized by the firmware, that provides a secure foundation for the operating system (OS) and applications running within the OS. The hardware root of trust provides several foundational security capabilities including a secure, tamper-proof key storage location, a unique hardware encryption key, and other facilities required as part of a cryptographic framework.
Specifically, The Futurum Group Labs tested the following system components:
- Dell PowerEdge 16th Generation systems with a Trusted Platform Module (TPM)
- Dell PERC 12 (PowerEdge RAID Controller, 12th generation)
- Broadcom 57508 Dual Port, 100 Gb Ethernet NIC with QSFP adapter connectivity
- Secure BIOS management system settings, via iDRAC
- Device identification via cryptographic framework (devices attestation uses a devices hardware RoT)
Each aspect of a system must be secured, ideally with each element utilizing industry best practices including Zero Trust principles, enabled via a silicon Root of Trust (RoT) as the foundation of physical security. Utilizing a certified RoT device that provides tamper resistance, the hardware protects the device firmware, which in turn is utilized to ensure critical software security features are verifiably operating securely. Security breach examples could include the exchange of entire PCIe cards, uploading compromised firmware or other attacks that target PCIe cards.
Delivering end-to-end security requires the entire solution integrates multiple hardware RoT devices, together with software features that leverage the underlying hardware capabilities. Dell’s PowerEdge servers together with Broadcom NIC and RAID controllers provide this capability by validating each layer, from hardware to firmware and the OS using cryptographic attestation. Dell’s iDRAC and other management tools leverage this integrated security environment to deliver a secure, easy to manage solution.
| Futurum Group Comment: A key aspect of the Zero Trust approach is to utilize hardware RoT devices to provide cryptographic verification to build a secure ecosystem. Using Zero Trust, each component first verifies, then trusts their counterpart based upon certified key exchanges and mutual authentication, attestation and authorization. These features are critical for the additional security mechanisms used throughout the Dell servers along with supported devices. |
As part of a standards-based approach to secure system management, a new Security Protocol and Data Model (SPDM) standard has emerged. This standard leverages Zero Trust principles and enables devices to securely verify each other (device attestation) and then establish secure communications over a variety of internal, server transport connections. Dell’s 16th Generation servers, along with 12th generation PERC and Broadcom 57508 NICs now utilize SPDM, to enhance security. The SPDM standard leverages existing technologies including public key encryption, and cryptographic signing of certificates to provide device attestation between Dell’s servers and Broadcom devices. In future implementations, the SPDM standard can also enable secure communication channels between devices.
Broadcom Networking
Broadcom 57508 Ethernet NIC, with speeds from 25 Gb to 200 Gb operate with Dell’s security features and leverage some of the same Zero Trust principles. Broadcom’s NICs also have a hardware based, silicon RoT which enable multiple additional benefits, including:
- Silicon RoT with secure key storage on servers and PCIe devices
- Secure firmware loading, updates and recovery on servers and PCIe devices
- Signed UEFI drivers, with Secure PXE boot for onboard NICs and PCIe NICs
- Device attestation (SPDM 1.2) between servers and devices, and audit logging of all devices
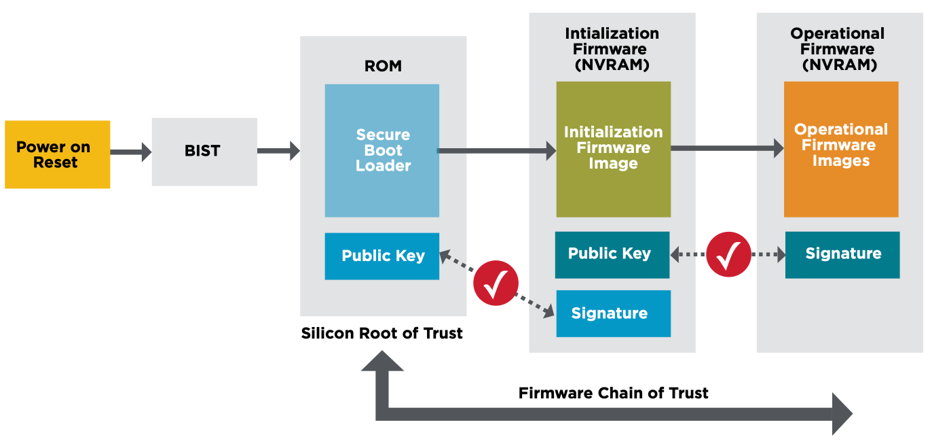
Figure 3: Broadcom’s Silicon RoT w/ Secure Firmware Loading (Source: Broadcom)
Hardware TPM
The Futurum Group Labs verified that Dell PowerEdge’s hardware security operated correctly by testing the supplied TPM version 2.0. Testing verified that all supplied features operated correctly including key generation using a true random number generator, and a secure key store. Additionally, after verifying TPM functionality, we then enabled security features including secure boot, secure lifecycle management, out of band management, and firmware updating.
Dell PowerEdge RAID Controller (PERC)
Dell’s PowerEdge RAID Controllers, aka PERC 12th generation use Broadcom controller interfaces and support a variety of RAID levels and device connectivity. The PERC 12 H965i controllers tested are designed for internal and external device support and include multiple RAID levels along with SAS and NVMe connectivity.
The Dell 12th gen PERC security features include:
- Silicon based hardware RoT: Foundation for Zero Trust
- Onboard RoT builds a chain of trust by authenticating all PERC firmware prior to execution, permits only authenticated firmware upgrades
- SPDM support: Provides device attestation and secure communications
- UEFI secure boot: Helps reduce attack vectors, and root kit installations
- Secure Firmware Updates: Simplifies administrative security updates
As shown above previously in Figure 3, the process for secure booting from a Dell PERC 12 controller card is similar to securely booting via a NIC.
Dell PowerEdge 16th Generation Servers
Multiple areas of evaluation and testing were performed with the PowerEdge servers together with PERC RAID cards and Broadcom NICs. One of NIST’s specifications (NIST SP 800-193) specifically addresses platform firmware resiliency. It stipulates methods for securing the BIOS, boot ROMS, along with firmware and driver signatures to verify authenticity. This guideline also outlines a method for providing a “secure boot” mechanism, whereby each component verifies subsequent components in the stack from hardware all the way to the operating system.
Secure Boot
Dell PowerEdge secure boot via Broadcom NIC, Dell PERC or local disk occurs via similar mechanisms. The secure boot process is important to ensure that a validated OS image is ultimately loaded and is used to operate the system. If an OS is altered, system security cannot be guaranteed. At a high-level, secure boot validates the UEFI drivers and boot loaders which then guarantees the authenticity and integrity of each subsequent component, firmware or software element that is loaded. This chain of trust is one of the basic elements of the Zero Trust model and basic system security. Secure boot functionality was verified with multiple devices, including secure boot of a verified OS image from Dell’s PERC 12 controller, and via PXE boot using a Broadcom 100 GbE NIC card.
Authentication Access, Authorization and Auditing (IAM)
These areas include identity and access management of systems (IAM), components and users, multi-factor authentication, audit logging and alerting, and access based upon authenticated authorization. The IAM capabilities are implemented throughout Dell’s management tools, including iDRAC, OME and CloudIQ.
Secure Lifecycle Management
Secure lifecycle management features were verified by first establishing a baseline, and then updating to the latest firmware and drivers via iDRAC. The secure process was verified both via the successful updates and notices, along with one image that did not update due to an invalid security certificate. The test properly identified an invalid certificate, and would not allow the firmware to be updated, which was the correct behavior. Upon obtaining a firmware image with the proper security certificate, the firmware update was successfully applied, which again was the desired security behavior.
Management, Alerting and Reporting
A critical part of Dell’s cybersecurity capabilities are the management tools available. Dell’s iDRAC tool continues to evolve and add capabilities for BIOS and low-level system management of PowerEdge servers and attached devices. Incorporating standards such as Redfish for secure remote manageability, enables secure programmatic API, CLI and scripting access, while also enabling secure web UI access for users preferring a graphical interface.
The Futurum Group Labs utilized and validated numerous functions and capabilities of each of Dell’s enterprise management solution. iDRAC, Open Manage Enterprise and CloudIQ are designed to work together to enable a spectrum of management, alerting and reporting capabilities.
- Dell’s iDRAC: system level management software pre-installed on all Dell PowerEdge servers, providing secure out-of-the box management capabilities for individual systems.
- OpenManage Enterprise (OME): Designed for IT staff to monitor and manage Dell servers within a datacenter. OME provides roll-up features to aggregate information while still providing the ability to manage individual systems, either from within OME or via linking to iDRAC.
- CloudIQ: Enables multi-site and enterprise-wide monitoring and management, with high-level management and reporting while also providing drill-down system management of some features and function.
A key part of iDRAC with OME is the integration of Broadcom components throughout, including the ability to monitor Broadcom-based PERC and NICs for firmware levels, vulnerabilities and provide updates through the secure lifecycle management capabilities.
The Dell OME management server was utilized throughout testing. Installation was straightforward and accomplished without needing to consult manuals. Downloading a preconfigured VMware image (OVA) and deploying to a VMware cluster, the OME server was operational in under 30 minutes. OME provided a way to both perform health monitoring and alerting, along with active management of desired systems. The OME interface was intuitive and provided significant fleet management features, by helping to highlight potential issues and providing the ability to resolve problems.
| Futurum Group Comment: Looking specifically at the security features of iDRAC, OME and CloudIQ, we found the health and security scoring mechanism and recommendations to be extremely effective. A significant challenge for most IT environments is prioritizing which updates are the most critical and then quickly remediating these issues. Dell’s management tools enable finding and applying critical updates quickly, and is one of the most effective solutions for security we have evaluated to date. |
With CloudIQ’s health scores and recommendations, it required only a few clicks to sort by the most critical issues, and then utilize the appropriate management tools to apply remediation for the vulnerabilities. Some issues may be resolved entirely from CloudIQ, with others enabled via links to OME for remediation.
Dell’s CloudIQ service has continued to evolve since its storage system origins into a Dell product-wide SaaS application that effectively provides health monitoring and alerting, along with recommendations. Dell’s overall management architecture provides robust security manageability, alerting and reporting capabilities that provide the critical link IT administrators require to effectively manage a secure IT environment.
3 - Manufacturing & Supply Chain Security
The concept of evaluating a product’s manufacturing and supply chain for security is relatively new to many companies. Although these practices have been standard for regulated industries for years, only recently have companies began to apply supply chain security practices to products designed for commercial use. One reason is that due to increased focus on other threats, the supply chain is now seen as an area of increasing vulnerability.
One area of supply chain security that sets Dell apart from their competitors is Dell’s Secured Component Verification (SCV), which is designed to help verify that the security of all components is maintained from order until it is delivered and installed at the customers location. Dell’s approach to supply chain threats includes supply chain integrity with ISO certification of sites, software bill of materials and the Dell SCV process, which all help to prevent counterfeit components or malware being inserted into systems or components.
| Futurum Group Comment: Dell’s approach to securing product manufacturing and supply chain is perhaps the best processes the Futurum Group Labs has evaluated. In particular, Dell’s Secured Component Verification process provides unique value, enabling IT clients to quickly and easily ensure their products have not been altered or modified, including verification of both hardware and firmware components. Dell SCV is an important tool for addressing overall cybersecurity. |
An overview of the Dell SCV process is shown below in Figure 4.
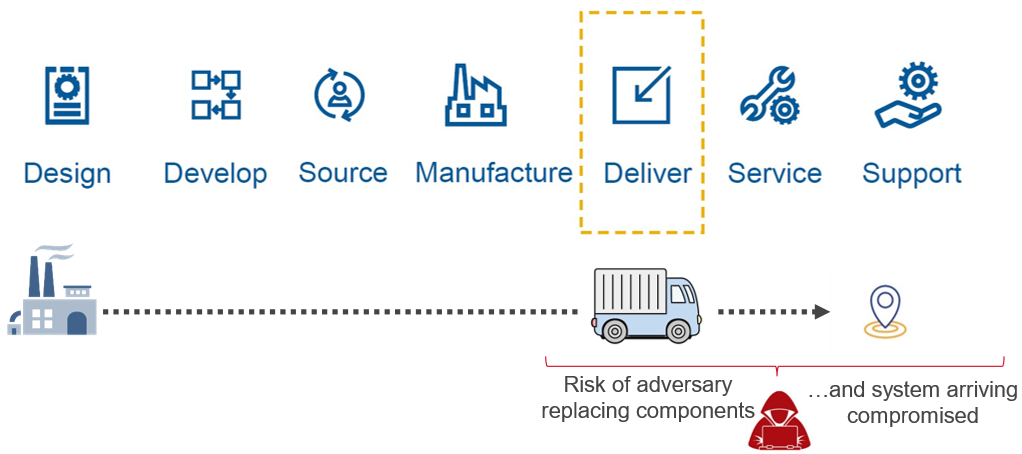
Figure 4: Dell’s Secured Component Verification Process (Source: Dell)
The Futurum Group Labs verified that Dell’s SCV can accurately report on each major system element, showing whether it is a verifiable component that was part of the original bill of materials or not. The SCV leverages the earlier security principles and technologies outlined, including Secure RoT and hardware TPM modules, cryptographic signatures for device attestation and Zero Trust principles to create a process to verify that a system has not been altered in any way.
During testing The Futurum Group Labs verified that the SCV correctly verified components that were part of the original bill of material and order, and items that were added afterwards. This capability provides a unique and easy-to-use method for IT users to attest to the authenticity and integrity of their systems.
4 - IT Security Implementation
The last major component of the Futurum Group’s Security Framework is how well a company and the IT organization operates with respect to security. IT security has multiple standards, industry best practices and recommendations to help inform and guide companies towards implementations that provide the necessary security and cyber resiliency.
One guideline covering IT security is the NIST CSF [1] which includes the key phrases, Identify, Protect, Detect, Respond and Recover. The most recent update to this framework, the version 2.0 draft, adds a sixth area “Govern” to the previous list, placing more emphasis on corporate oversight and implementations.
Although important, this area falls largely outside the scope of vendors’ product offerings but may be supplemented via professional services and training. As a result, The Futurum Group did not formally assess the IT Security aspects of the Futurum Group’s Security Framework.
| Futurum Group Comment: The Futurum Group’s Security Framework evaluates IT security through the lens of a products ease-of-use and ability to implement security best practices. In this regard, Dell enables IT security by making security best practices the default option when possible, and ensuring security features are easy-to-use. As a result of security integration between PowerEdge servers, Broadcom 57508 NICs and Dell management tools helps companies implement security best practices. |
For companies that desire security consulting to help supplement their capabilities, Dell and their partners offer a variety of security services, including cybersecurity advisory services that are designed to assess a company’s security posture, and help improve internal procedures and help elevate security capabilities to attain proficiency in this area. Based upon the principles outlined previously, Dell security services include Cybersecurity Advisory Services, Recovery Services for Cyber-attacks, along with managed services for cyber-attack detection and response.
Moreover, the product design, product features, together with the secure supply chain features and security consulting services all provide sufficient tools to enable IT organizations to manage and maintain a highly secure environment that meets NIST and industry best practices for maintaining a cyber resilient posture.
Final Thoughts
Security and cyber resiliency have become areas of critical focus for enterprises according to The Futurum Group’s research. Additionally, conversations with IT clients often include a discussion of ransomware and cyber resiliency. Organizations that follow best practices follow the NIST or other frameworks to integrate security throughout their organization and operational procedures.
Attempting to purchase point products, or simply “add security” to existing infrastructure is challenging at best. Starting with products that are designed from the ground up with security is a key priority. According to The Futurum Group’s research, a significant number of security breaches utilize compromised servers as part of their attack vector. Thus, securing servers, their networking interfaces and storage devices is an ideal area of focus for companies looking to improve their cyber resiliency.
In assessing Dell PowerEdge servers together with Broadcom add-in cards against the Futurum Group’s Security Framework, we found that the systems meet or exceed requirements in all categories. There were several areas of strength noted, where PowerEdge significantly exceeded expectations. These include several security integrations between Dell’s silicon RoT and Zero Trust approach, together with Broadcom NICs and PERC RAID cards own embedded RoT and Zero Trust capabilities and importantly with Dell’s management tools.
Another area where PowerEdge exceeded expectations is the seamless management capabilities of iDRAC for baseboard system management, with OME for datacenter management, coupled with CloudIQ for global monitoring, alerting and reporting of multiple datacenters. The particular focus on security alerting and recommended actions of CloudIQ help IT administrators move from inaction due to an overwhelming number of issues, to action focused on the most important configuration or security issues.
Finally, Dell’s SCV process significantly exceeded expectations, offering a best-in-class end-to-end process for ensuring system integrity from suppliers, manufacturing and configuration, shipping, delivery and installation. A significant area of concern for organizations is ensuring their systems do not contain malicious hardware elements that could circumvent even robust security practices. Dell’s SCV provides a simple and easy way for organizations to ensure their infrastructure has not been compromised.
Taken together, Dell PowerEdge servers, with Broadcom NIC cards provide comprehensive security capabilities that provide a foundation for IT users to quickly and efficiently establish a highly secure computing environment that leverages industry best practices.
Resources
[1] NIST Cybersecurity Framework, draft version 2.0, August 2023:
About The Futurum Group
The Futurum Group is dedicated to helping IT professionals and vendors create and implement strategies that make the most value of their storage and digital information. The Futurum Group services deliver in-depth, unbiased analysis on storage architectures, infrastructures, and management for IT professionals. Since 1997 The Futurum Group has provided services for thousands of end-users and vendor professionals through product and market evaluations, competitive analysis, and education.
Copyright 2023 The Futurum Group. All rights reserved.
No part of this publication may be reproduced or transmitted in any form or by any means, electronic or mechanical, including photocopying and recording, or stored in a database or retrieval system for any purpose without the express written consent of The Futurum Group. The information contained in this document is subject to change without notice. The Futurum Group assumes no responsibility for errors or omissions and makes no expressed or implied warranties in this document relating to the use or operation of the products described herein. In no event shall The Futurum Group be liable for any indirect, special, inconsequential, or incidental damages arising out of or associated with any aspect of this publication, even if advised of the possibility of such damages. All trademarks are the property of their respective companies.
This document was developed with funding from Dell Inc. and Broadcom. Although the document may utilize publicly available material from various vendors, including Dell, Broadcom and others, it does not necessarily reflect such vendors' positions on the issues addressed in this document.



