

VDI Data Protection Part 1: Protecting Your VDI Environment - What You Need to Consider
Tue, 11 Jul 2023 18:44:31 -0000
|Read Time: 0 minutes
Virtual Desktop Infrastructure (VDI) plays a crucial role in today's business transformation initiatives. Although there is an increase in SaaS-based and cloud native applications, the majority of the applications in today's enterprises continue to be Microsoft Windows-based applications. VDI is the most efficient way to present these Windows applications to end users in their digital workspaces, and provides a consistent user experience across user devices for the modern-day mobile workforce. Organizations increasingly rely on VDI to provide the agility, security, and centralized management that are so important for their workforce.
According to the Global Data Protection Index survey by Dell EMC, organizations managed an average of 9.7PB of data in 2018 - representing an explosive growth of 569% compared to the 1.45PB managed in 2016. What’s worrying is that the number of businesses unable to recover data after an incident nearly doubled between 2016 and 2018. This information is alarming because incidents such as these can cause substantial monetary losses, reduced employee productivity, and damage to the reputation of the affected organizations. VDI environments are arguably the most critical workload in the corporate data center because they impact user desktops and user data - the primary gateways to user productivity. Any loss or reduced availability of these components will directly impact both user productivity and the business.
For physical desktops and laptops, data protection is often restricted to storing user data on a shared folder somewhere in the organization's network, then protecting that folder. But when it comes to VDI, virtual desktops reside in the data center, and it is the responsibility of IT to not only protect the user-specific data but also to protect the desktop and associated desktop management infrastructure.
The success of a VDI data protection plan depends on these classic data protection parameters:
- Availability -- the percentage of time that a service/application (in this case the VDI environment) is available. Five-nines or 99.999% availability means 5 minutes, 15 seconds or less of downtime in a year.
- Recovery time objective (RTO) -- the elapsed time to when virtual desktops can be available after an incident
- Recovery point objective (RPO) -- the time period (minutes, hours) of acceptable user and configuration data loss from the VDI environment prior to when the incident occurred
For example, a policy might state that we must restore service within 4 hours (RTO) with no more than 1 hour of data loss (RPO). A robust data protection plan is necessary to ensure that availability, RTO, and RPO objectives are met. Such a plan will require the protection of all essential components of the VDI environment to ensure that the plan meets its service level agreement (SLA) to avoid business impact.
As shown in Figure 1 below, a VDI environment typically consists of management infrastructure, desktop infrastructure, and user data components (often a file share or dedicated unstructured data storage platform such as Dell EMC Isilon) where user data is stored. The functions of these layers are summarized below:
- The management layer performs the provisioning, brokering, policy management, and related management functions
- The desktop layer is the user’s desktop, which is often made available to multiple users using an appropriate cloning technology
- The third layer is the user data (stored in user profile shares, home folders, etc.)
A VDI data protection plan should cover all three of these component layers.
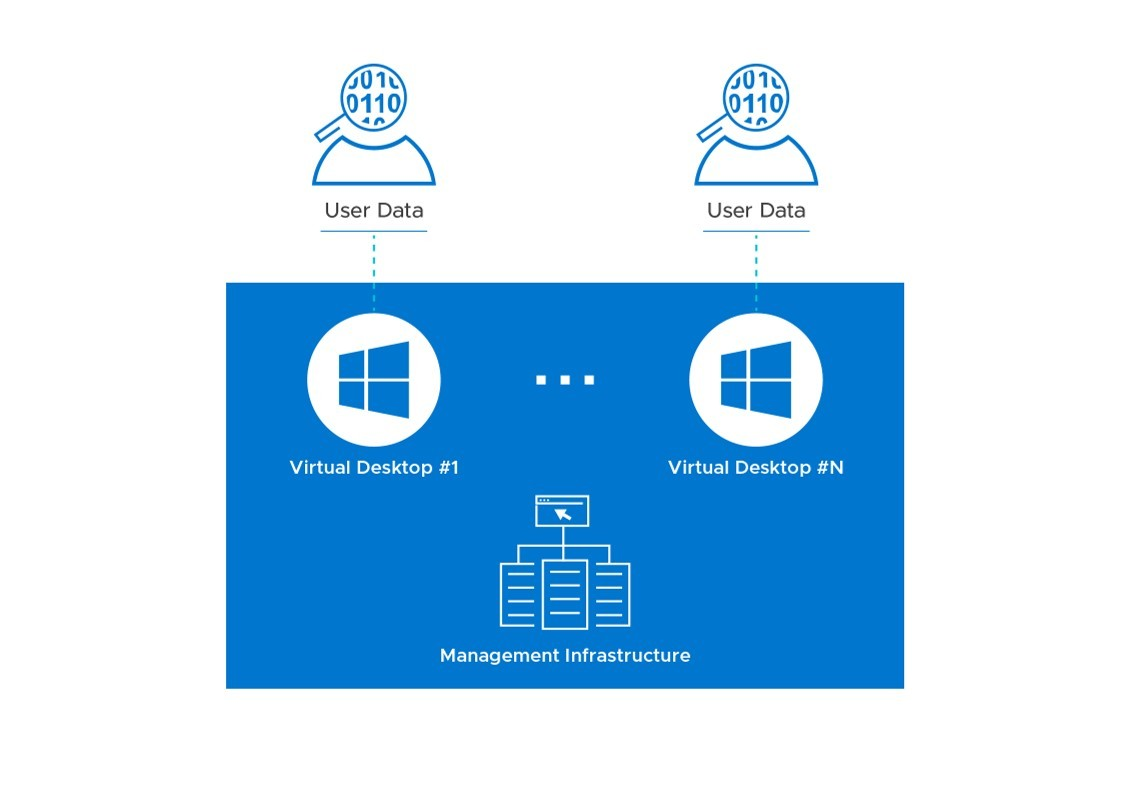
Figure 1: Components of a VDI Environment that Require Protection
The availability and recoverability goals described above will determine the overall design for your VDI infrastructure. The level of redundancy and other factors will vary depending on whether it will be a single-site or multi-site design. The operational backup of data and the disaster recovery plan, two major aspects of data protection, will vary across organizations based on these parameters. Careful consideration needs to be given to these requirements during the design of the VDI infrastructure, to meet the Service Level Agreement (SLA).
In the next installments of this blog series on data protection for VDI, we will discuss in detail how these objectives can be met by describing some of the important considerations for multi-site disaster recovery, single-site protection, and what the future of data protection for VDI environments in a multi-cloud world might look like. The next blog will be a deep-dive on VDI multi-site disaster recovery from a Dell EMC perspective. Stay tuned and we’d love to get your feedback!
Published By



