

Protecting AI Infrastructure: VxRail's Answer to Advanced Threat Vectors
Wed, 09 Oct 2024 14:16:27 -0000
|Read Time: 0 minutes
As AI entwines itself within the fabric of our technological ecosystem, it brings with it a host of sophisticated vulnerabilities that require equally sophisticated defenses. In last week’s initial entry to the series, we introduced key attack vectors for AI deployments and highlighted how VxRail and Dell Technologies’ ecosystem can help establish a secure environment. This week, we take a magnifying glass to these previously identified potential breach points and explore how VxRail's security measures are uniquely positioned to protect your AI infrastructure.
Countering AI Threats with VxRail
Diving into the world of AI security, we explore how VxRail's inherent design anticipates AI-related threats. VxRail’s security controls provide mitigations for a range of attacks, from Injection to Denial of Service, utilizing both physical hardware measures and advanced software protocols.
Supply Chain Security
In any deployment, supply chain security takes center stage, especially when hosting an AI environment. The integrity of the infrastructure, training data, and AI models hinges on preventing the introduction of malware and other threats. Attack vectors related to supply chain contamination—such as Injection, Infection, Poisoning, and Excessive Agency—aim to infiltrate vulnerable software or hardware during development, manufacturing, shipment, and assembly processes.
Production
Supply chain security measures extend across the entire product lifecycle, starting from the initial stages of product development and production. Vendors must adhere to industry standards, including guidelines like the NIST (National Institute of Standards and Technology) Guidance for Supply Chain Risk Management. At the operational level, maintaining a traceable chain of custody, rigorous quality assurance, and thorough inspection and testing are critical controls to minimize the risk of using compromised materials. Dell Technologies, for instance, employs asset tracking processes to ensure that materials come exclusively from their approved vendor list, matching the bill of materials, and directly from the original manufacturers — thereby avoiding third-party intermediaries. These processes align with industry specifications and standards, reinforcing supply chain security.
Shipment
Dell Technologies’ factories meet the stringent security requirements outlined by the Transported Asset Protection Association (TAPA). These measures come into play during packaging and transportation to the customer. Key TAPA controls include closed-circuit cameras in critical areas, access controls, and vigilant monitoring of entries and exits. To safeguard shipments, Dell employs tamper-evident packaging, conducts security reviews of shipping lanes, ensures locks and hardware meet required specifications, and even utilizes GPS tracking devices for continuous monitoring until delivery confirmation.
Deployment & Maintenance
Silicon-Based Root-of-Trust
Beyond physical controls, VxRail and PowerEdge servers incorporate Silicon-based Root-of-Trust. This technology, in conjunction with Intel Boot Guard or AMD Root-of-Trust capabilities, attests to the integrity of BIOS and iDRAC firmware. Attestation is accomplished when, during manufacturing, encryption keys cryptographically sign a hash of the boot image before it leaves the factory. These read-only keys are used during the boot process and if any tampering evidence surfaces, the server is promptly shut down. VxRail and PowerEdge also extends signature verification to firmware updates, ensuring only authentic firmware runs on the server platform.
Secured Component Verification (SCV)
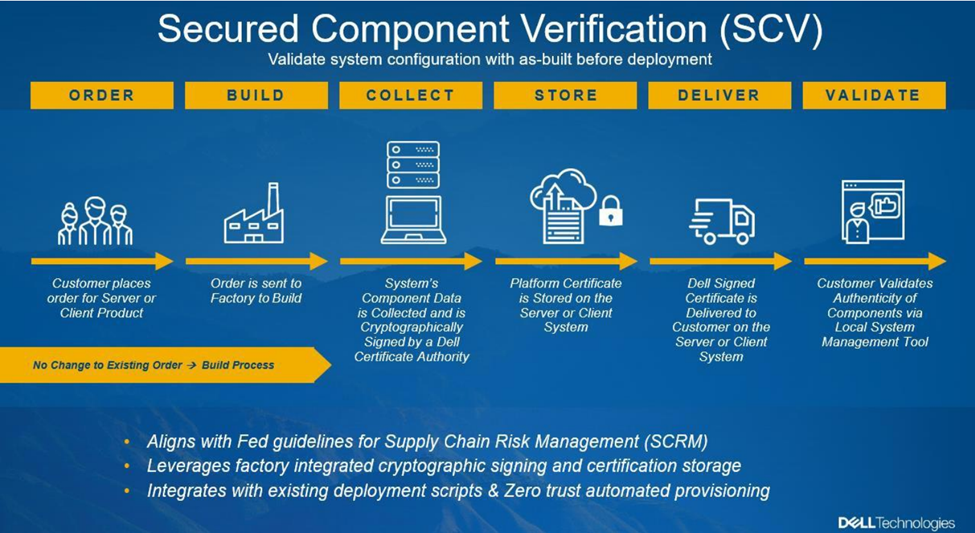
Dell VxRail and PowerEdge servers offer an optional feature called SCV to enhance the supply chain assurance of Silicon-based Root-of-Trust. SCV validates that the server and components received at the customer site match the factory-shipped configuration. A certificate containing a unique system component IDs is generated during manufacturing, cryptographically signed, and stored within iDRAC. Customers can leverage SCV to verify their current inventory against the original shipment.
Protecting Software Supply Chain
Moving beyond hardware and firmware, VxRail employs multiple security controls to safeguard the software supply chain:
- Proactive Verification and Validation: Rigorous security testing occurs throughout the software development lifecycle, ensuring robust protection against vulnerabilities.
- Third-Party Code Scanning: Regular scans prevent the inclusion of compromised supporting software.
- Code Signing and SecureBoot: Pairing code signing with SecureBoot guarantees that our software remains untampered.
- Software Bill of Materials (SBOM): We provide an SBOM upon request, offering full transparency regarding third-party software usage.
Decommission
In the lifecycle of any device, there comes a critical step: decommissioning. Whether a device is discarded or repurposed, handling this phase properly is essential to prevent bad actors from accessing sensitive data related to its original use.
Steps taken during decommissioning to protect the overall supply chain include:
- Reconfiguring Access Controls: To prevent unauthorized access, reconfigure access controls and invalidate previous credentials associated with the system.
- Asset Tracking: Maintain a traceable chain of custody during decommissioning to protect against attacks during the final transport phase.
- Trusted Partnerships: Collaborate with trusted partners who adhere to Zero Trust security practices for secure decommissioning.
- Data Sanitization: Render any remaining data on the system inaccessible.
Data Sanitization
VxRail provides functionality to support the data sanitization step. The goal is to make all data on the system completely unrecoverable—even by advanced digital forensics. VxRail employs cryptographic sanitization, where targeted data is encrypted, and the encryption keys are subsequently destroyed. This efficient approach aligns with NIST SP 800-88 guidelines. Three paths lead to a full cryptographic erase:
- PowerEdge System Erase: Sanitizes server storage devices and nonvolatile stores.
- VMware vSAN Encryption: Once a vSAN is encrypted, vSphere allows destruction of relevant encryption keys, rendering vSAN-stored data inaccessible.
- VMware VM Encryption: Similar capabilities encrypt VMs and then destroy the associated encryption keys.
Zero Trust: Securing AI's Supply Chain
Supply chain security is foundational in modern Zero Trust practices. As AI becomes increasingly central to our lives, safeguarding against supply chain attacks is imperative. Together VxRail and PowerEdge provide solid supply chain security to protect infrastructure and AI deployments.
Stay tuned for our next post where we merge technology with trust, detailing how VxRail establishes a Trusted Execution Environment, a vital component for any AI-driven operation.
Author:
Joann Kent, Cybersecurity Product Manager



