
How SQL Server can protect your digital currency
Mon, 03 Aug 2020 16:10:30 -0000
|Read Time: 0 minutes
Do you wonder if your data is under attack? When should we worry if our data is safe and secure? What precautionary steps we have taken to protect data? Can we eliminate data breaching? In this article I want to introduce some of the great security features built into SQL 2017. No product can prevent all risk of data loss or unauthorized access.The best defense is a combination of good products, knowledgeable people, and rigorous processes design with data protection at all levels of the organization.
Let us start by understanding what data is?
There were relatively few methods to create and share data before the advent of computers – primarily paper and film. Today there are many ways to create, store and access digital data (0’s and 1’s). Data may be a collection of raw facts, data may be a numbers or words, data may be a recorded information of something or someone and in typical digital language data is binaries. Digital data is much easier to create, share, transfer and store in digital forms, such as an email, digital images, digital movies, e-books but also much more difficult to secure.
The digital data ecosystem
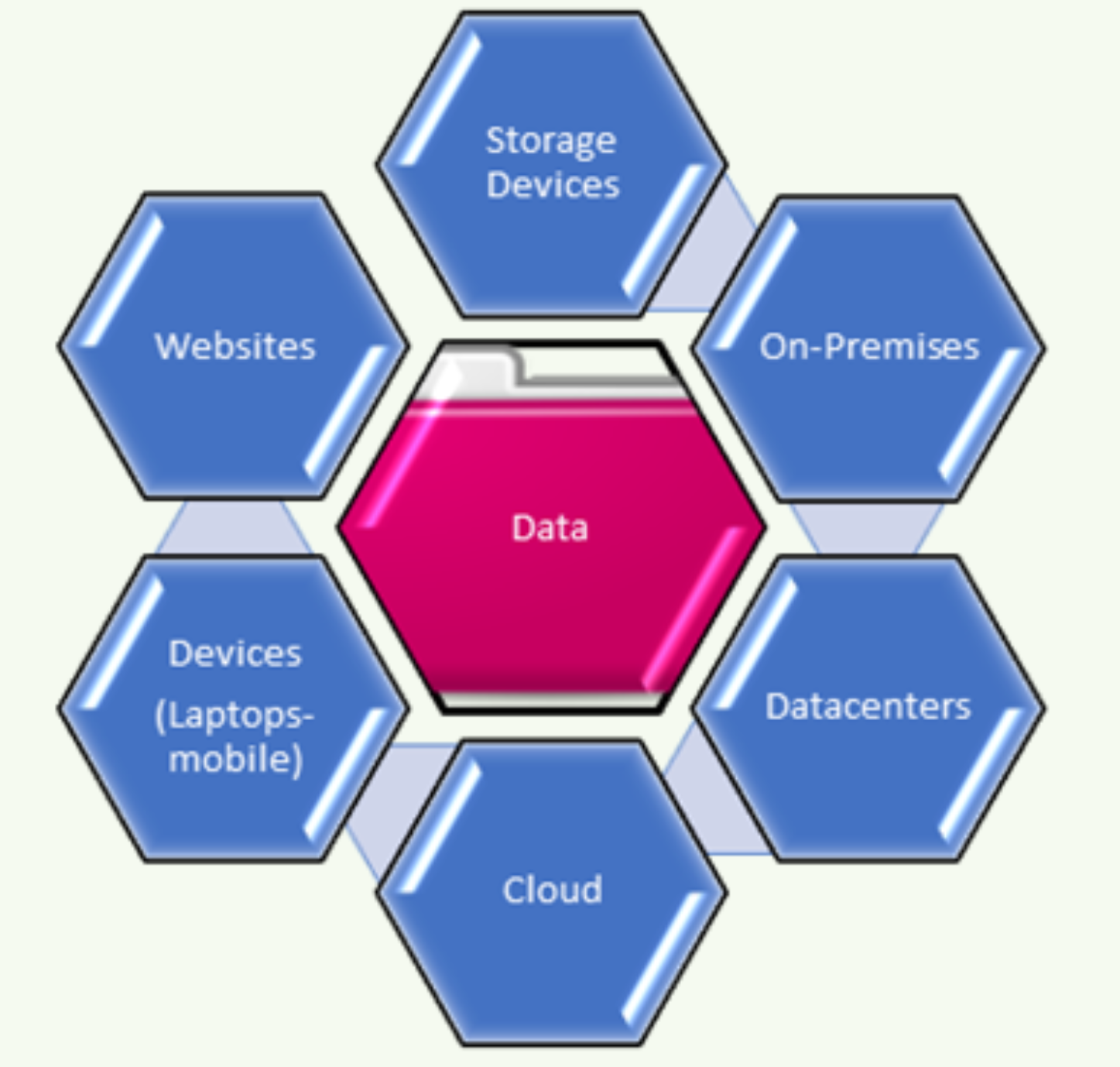
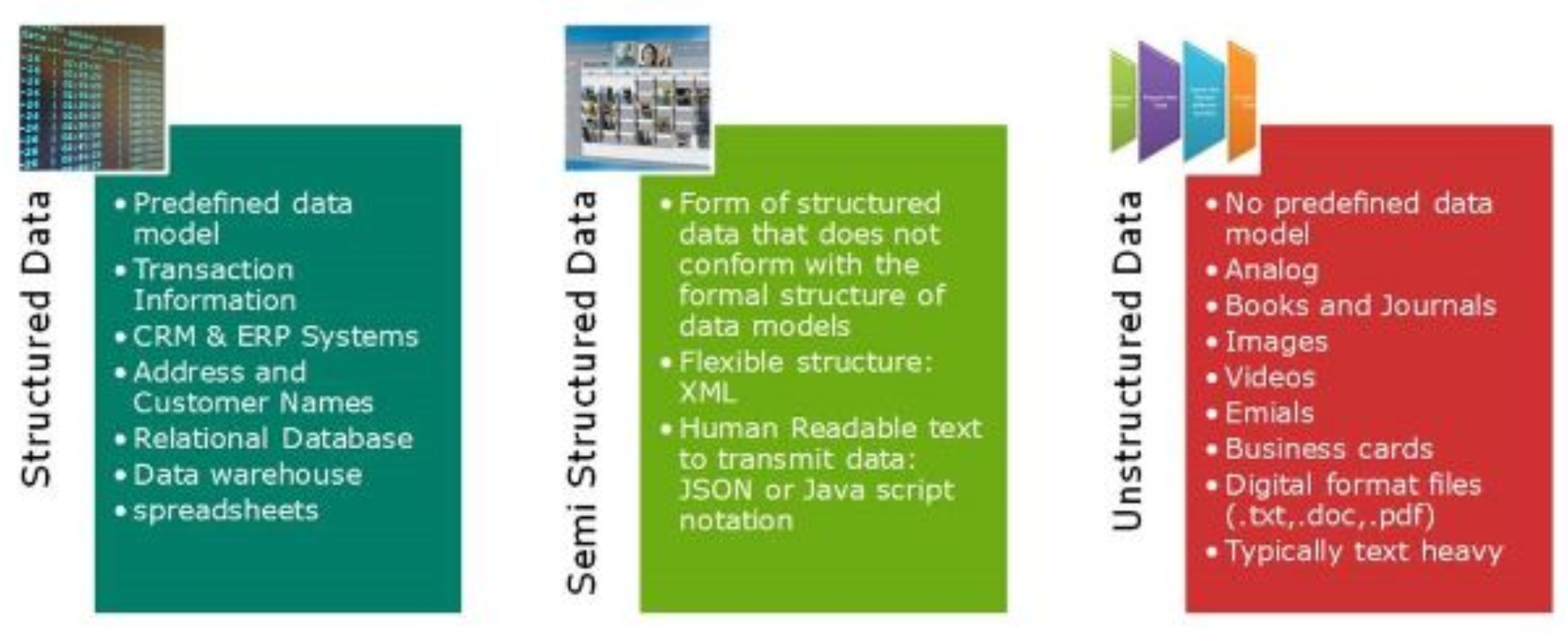
Most data can be classified as structured and unstructured. Most of data being created today is unstructured. With the advancement of computer and communication technologies, the rate of data generation and sharing has increased exponentially.
In simple terms, structured data is typically stored using a database management system (DBMS) in rows and columns. Structured data is easily searchable by basic algorithms. Unstructured data is pretty much everything else and does not have a predefined data model. Unstructured nature is much more difficult to retrieve and process. Numerous sources and techniques (data mining, natural language processing (NLP) and text analysis) are evolving rapidly by industry to analyze, derive, manage and store both unstructured and structured data.
In 1988, Merrill Lynch cited a rule of thumb somewhere around 80 to 90% all potentially usable business information may have originated in unstructured form. IDC and EMC projected that data will grow to 40 zettabytes by 2020.
https://www.kdnuggets.com/2012/12/idc-digital-universe-2020.html
https://www.emc.com/about/news/press/2012/20121211-01.htm
The chart below shows the amount of the data generated every minute in social media according to Domo's Data Never Sleep 5.0 report.
https://web-assets.domo.com/blog/wp-content/uploads/2017/07/17_domo_data-never-sleeps-5-01.png
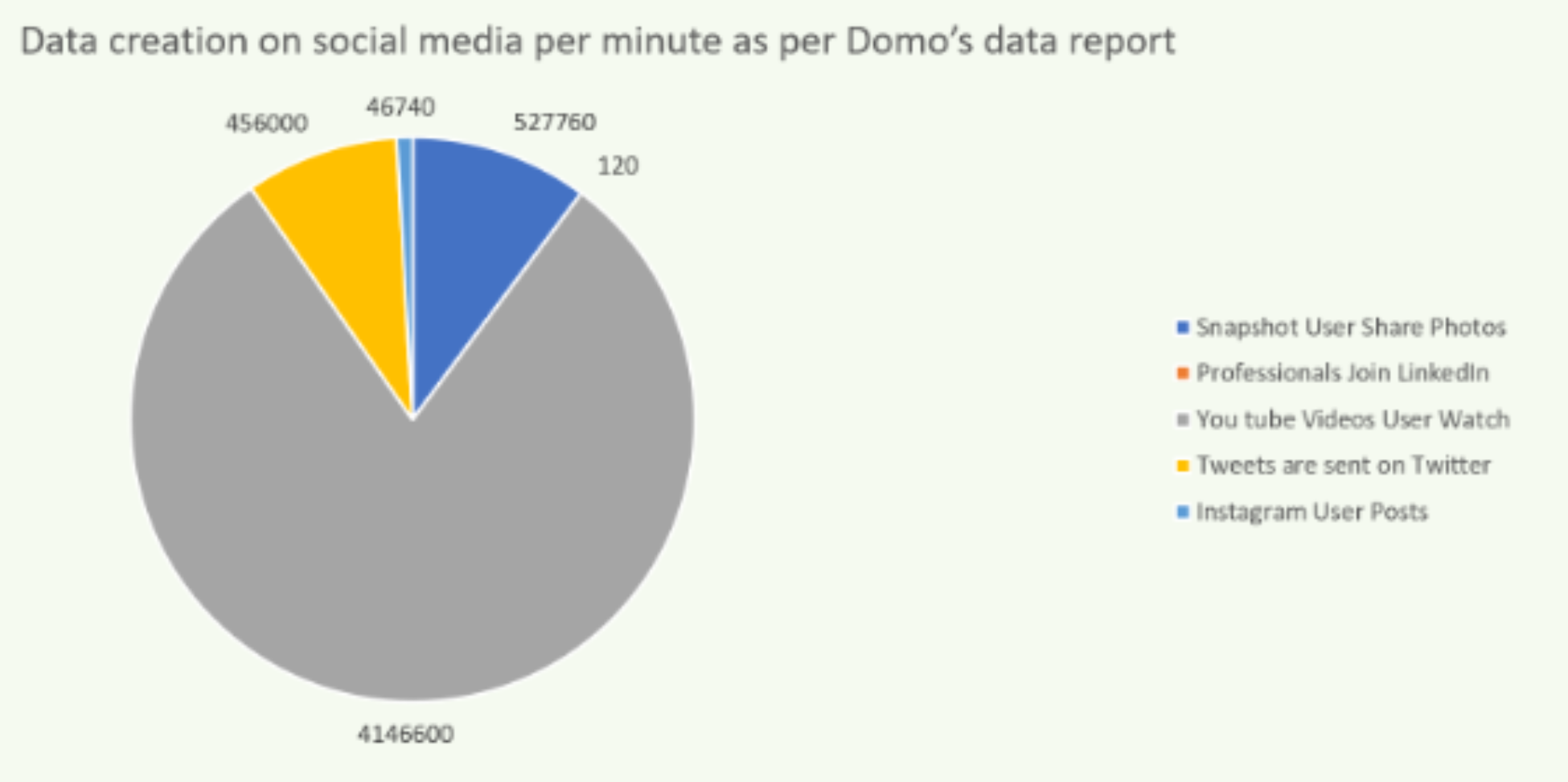
It is not necessary to store all the unwanted data. IDC predicts that by 2025 nearly 20% of the data in global data sphere will be critical to our daily lives. Organization should have a prior plan to store right amount of data and how to extract the business value, the value for human experience and personal value. That's the choice and its a definitive challenge.
Following chart provides a view of the total number of records containing personal and other sensitive data that have been in compromised between Jan 2017 and March 2018.
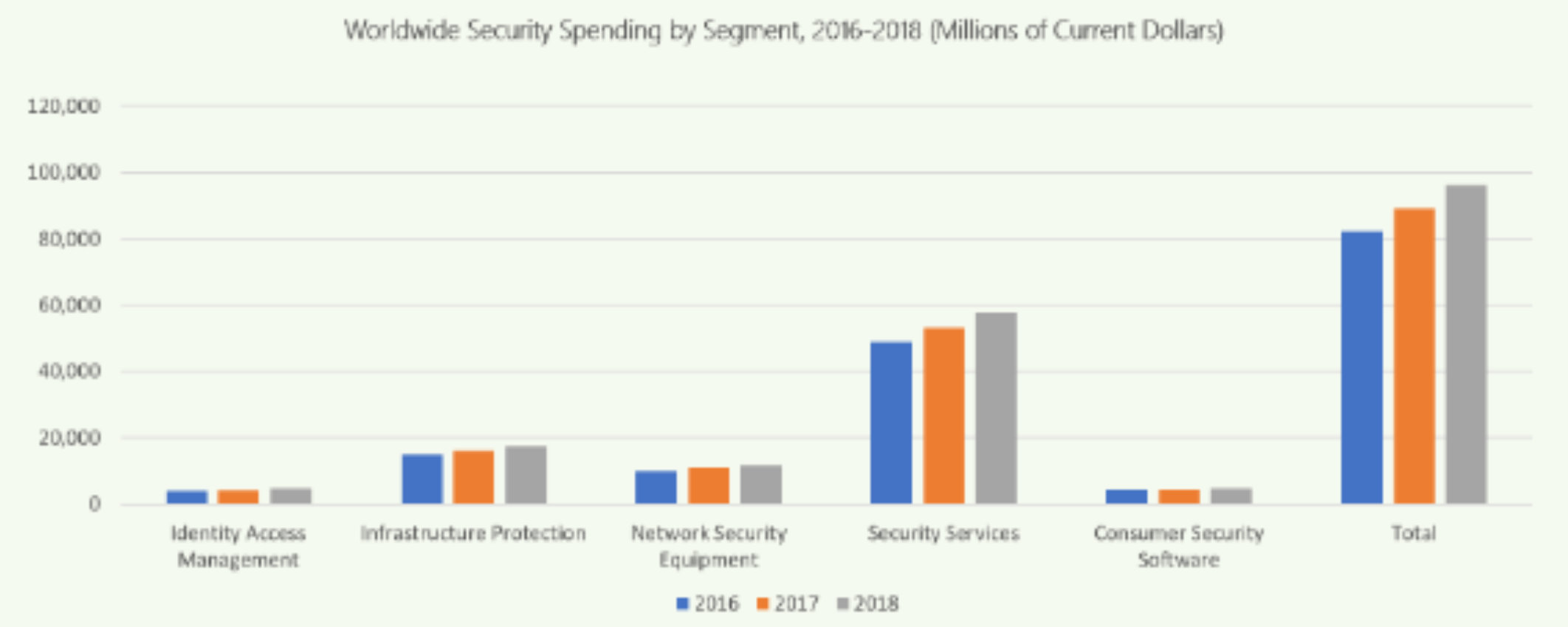
As per Gartner forecast the total spending of cyber security by the organizations world wide were up by 8% from 2017 and the predicted number is $96 Billions in 2018.
What could possibly go wrong?
A data breach is when confidential information exposed or compromised by intentional or unintentional means.
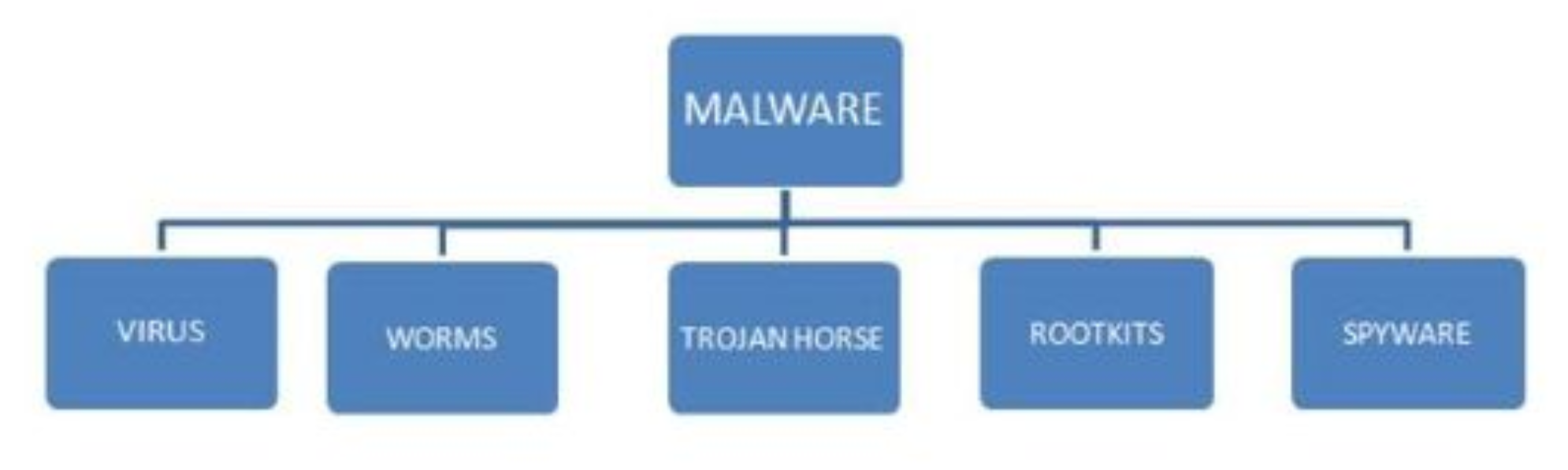
Malware: Any type of virus, including worms, ransomware, spyware and Trojans which gains access to damage a computer without the knowledge of the owner. Malware is usually injected and installed on a machine by tricking to user to install or access a program from the internet.
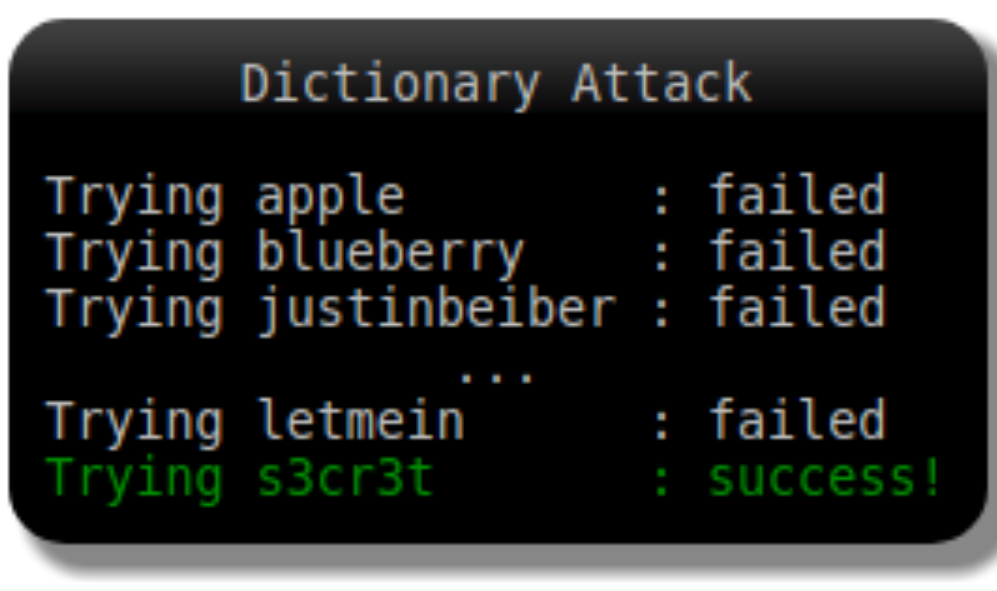
Password attack: Brute force attacks can be very successful for gaining access to systems with insecure passwords. 81% of confirmed data breaches involved weak, default or stolen passwords.
Phishing: Capitalizing on our apparent human need to click things, phishing campaigns try to get the recipient to open an infected attachment or click and equally infectious link.
Social Engineering: Email or phone call contact with authorized user of sensitive data for obtaining personal information that can be used in an attack to gain unauthorized access.
One ounce of prevention is worth a pound of cure.
SQL 2017 is equipped with many features to help secure and protect your data from breaches. With SQL server, security is just so well integrated, it’s literally something you mostly just turn on. For example, it is extremely easy to encrypt data on disk, on the wire and in memory, which is big.
- Always Encrypted (Secure at rest in motion): Large amounts of data lead to added complexity. Data is queried, transmitted, backed up, and replicated nearly and constantly. With all that activity, any link in the chain could be a potential vulnerability. Always Encrypted, enables encryption of sensitive data inside application and on the wire, while never revealing the encryption keys to the database engine. As a result, always encrypted provides a separation between those who own the data and those who manages the data.
- SQL Dynamic data masking prevents the abuse of sensitive data by controlling what users can access the unmasked data.
- SQL Server Authentication ensures that only authorized users have access by requiring valid credentials to access the data in databases.
- SQL Server 2017 audit is the primary auditing tool in SQL Server, enabling you to track and log server-level events as well as individual database events. It uses extended events to help create and run audit-related events. SQL server audit components are SQL Server Audit, SQL Server Specification and Database Audit Specification.
- Row-Level Security, helps database administrator to implement restricted access to the specific engineer or a user to the rows in a database table. This makes the security system more reliable and robust by reducing the systems surface area
SQL Server Provides enterprise-grade security capabilities on Windows and On Linux. All built in.
Protect Data | Transparent Data Encryption Backup Encryption Cell-level Encryption Transport layer Security (SSL/TLS) Always Encrypted |
Control Access (Database Access/Application Access) | SQL Server Authentication Active Directory Authentication Granular Permission Row Level Security Dynamic Data Masking |
Monitor Access | Tracking Activities (Fine-grained Audit) |
Summary: Digitization has led to an explosion of new data that is not expected to abate anytime soon. As data continues to play a vital role in our future, Cyber Criminals are causing organizations to spend ever increasing amounts of money every year to protect data. It is important that organizations get the most value from these investment in data protection.
DATA IS DIGITAL CURRENCY



