Home > Communication Service Provider Solutions > Telecom Multicloud Foundation > Red Hat > Guides > Red Hat Open Shift Container Platform Guides > Reference Architecture Guide: Dell Technologies - Red Hat OpenShift Reference Architecture for Telecom > PowerProtect Data Manager
PowerProtect Data Manager
-
Introduction
Data is becoming increasingly important to mobile operators and their customers, and the requirements for managing and protecting data are growing. As enterprises increasingly run business-critical applications on their network, these enterprises expect their data to always be protected, secure, and available. Also, the data from operations used to maintain and optimize network performance, enhance customer experience, and identify new ways of engaging with customers drives competitive advantage.
Like all network architectures, cloud-native networks carry risks of operations-affecting data loss from events such as human error, machine error, natural disaster, sabotage, or cyber attack. This is especially true as the network topologies move to open, disaggregated ecosystems that stich together network functions in containers running from the core to the far edge of the network. Having a comprehensive data protection and management strategy becomes essential to ensuring operations and delivering services. For this reason, Dell Technologies has partnered with Red Hat to support OpenShift Container Platform environments with the Dell EMC PowerProtect Data Manger data protection solution.
This reference architecture guide and its companion deployment guide each address the integration of PowerProtect Data Manager with an existing OpenShift 4.6 cluster, as well as the procedures to back up and restore namespaces containing workloads or persistent volume claims.
Protecting OpenShift environments with PowerProtect
Fully protecting a telecom network using OpenShift Container Platform means not only protecting the data generated by applications, but also protecting the metadata associated with the platform and the infrastructure on which those applications are running. OpenShift adds several components on top of the standard Kubernetes distribution. Components such as Build, BuildConfig, ImageStream, ImageStreamTag, ImageTag, and DeploymentConfig must also be backed up to restore OpenShift namespaces, data, and metadata. These components support the source to image and image to deployment workflow that takes an existing source code repository and converts it to associated container or docker images. Dell Technologies uses the OpenShift plug-in to allow these components to be backed up and restored, thus extending the benefits of PowerProtect Data Manager to OpenShift environments. The following figure illustrates how these components work together to provide backup and restore services:
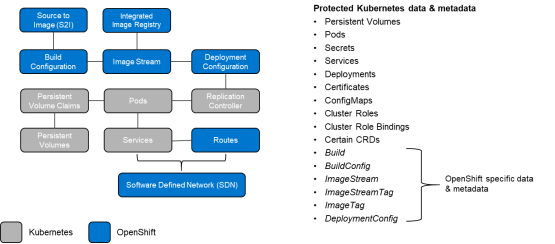
Figure 12. OpenShift data and metadata components
The PowerProtect Data Manager solution uses a specially designed boost plug-in that allows it to write to PowerProtect DD Series physical and virtual appliances that are located on-premises or in the public cloud. During the discovery process, PowerProtect Data Manager detects OpenShift clusters and automatically installs the OpenShift plug-in. During backups and restores, the OpenShift plug-in is used to protect the associated OpenShift components. This process is transparent to the user. PowerProtect Data Manager automatically discovers and protects databases, virtual machines, file systems, and Kubernetes containers, while a common policy engine automates compliance and governance across workloads. Power Protect Data Manager also provides application-consistent protection for databases such as MySQL, Oracle, SAP, Cassandra, MongoDB, and PostgreSQL.
PowerProtect Data Manager empowers application owners with self-service restore processes while maintaining central governance. DevOps and admin teams can quickly create point-in-time copies for test and development, cluster migration, data analysis and more. These teams can also assign protection policies from a published list and ensure application-consistent protection for databases from customizable templates.
PowerProtect Data Manager significantly reduces network congestion through inline deduplication and compression, achieving up to 65 times data reduction rates with PowerProtect DD Series Appliances. It includes software-defined data movers that enable it to run multiple concurrent backup streams to create a highly scalable data protection solution for OpenShift environments.
Recovery from a cyber attack
Cyber threats are growing across every industry, and telecommunications is no exception. Cyber recovery processes must be an integral part of any cyber resiliency strategy. Protecting a copy of critical data, in an isolated manner, is the best-known way to provide recovery from attacks. Cyber security experts and leaders now recommend that organizations evaluate an offline and air-gapped “data vault” that contains point-in-time copies of the critical data to meet these requirements. Dell EMC PowerProtect Cyber Recovery, which is enabled by the PowerProtect data protection solution, provides an air-gapped data vault to protect critical data in OpenShift environments.
The PowerProtect Cyber Recovery data vault provides a physical and logical separation from the main network. In the event of a ransomware attack or other network breach, a copy of all data, including the container information that is needed for service recovery, is preserved and remains available for recovery using standard data recovery processes.
At a high level, the response to a cyber attack consists of four steps:
- The management server unlocks the air gap and synchronizes critical data into the data vault’s target storage. The air gap is then relocked.
- A copy of that data is made with a configurable retention policy.
- The data is retention-locked to further protect it from accidental or intentional deletion.
- CyberSense analyzes the data for anomalies and remediation of corrupted files.
As the following figure shows, data recovery from the vault if a cyber attack occurs can be performed using PowerProtect:
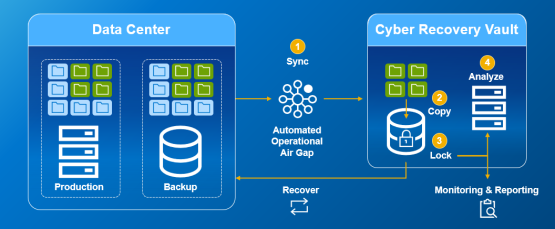
Figure 13. Cyber recovery process with PowerProtect Cyber Recovery
Further reading
For more information, see the following documentation:
