As technology evolves, so do the threats that can compromise the integrity and reliability of a power distribution network. Cybersecurity at a substation is to protect and safeguard critical infrastructure that facilitates the distribution and transmission of electricity. It prevents power disruption and unauthorized access, detects potential threats, and helps to maintain the reliability and stability of the power grid that we depend on.
Forescout eyeInspect offers end-to-end cyber resiliency for your operational technology (OT) network with the following features:
- Comprehensive assets risk framework
- Ongoing automated asset management
- Compliance monitoring
- Threat detection
Confidentiality
OT personnel must safeguard confidential data such as network configurations, security protocols, and other operational details from unauthorized access at substations. If such sensitive data was to be leaked, it could compromise the integrity of the substation operations.
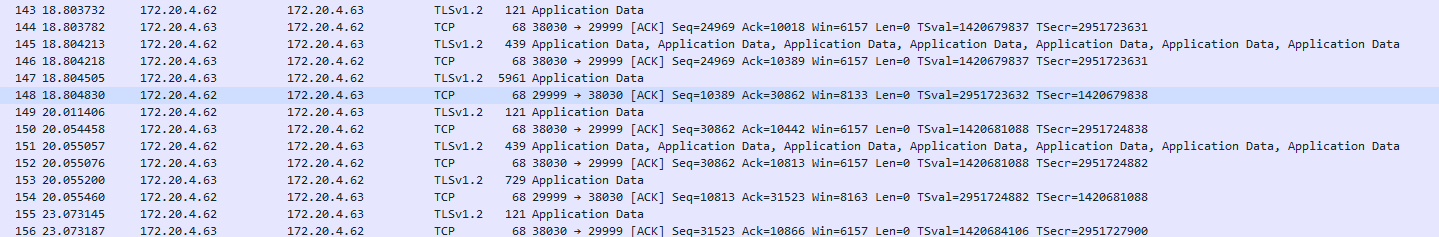
Secure connection between CC and sensor
To ensure the communication between the command center and sensors (end-to-end), networks are encrypted to prevent eavesdropping and data tampering. Using security protocols like TLS can effectively safeguard against malicious activities. Utilities like Wireshark and tcpdump can be used to validate whether critical network traffic is encrypted.
Implementing confidentiality enhances the privacy, security, and reliability of interactions between devices.
Authentication
Authenticate users and services to verify their identity when authenticating to Command Center. This ensures that the authenticating entity is who they claim to be. Various authentication techniques like passwords can be used to validate the identity of the authenticating entity. After authentication, user authorization is checked to ensure that users can access only the resources that have been assigned. Users are not able to access additional resources beyond what they have been authorized for. This helps maintain security and control over sensitive information and functionalities.
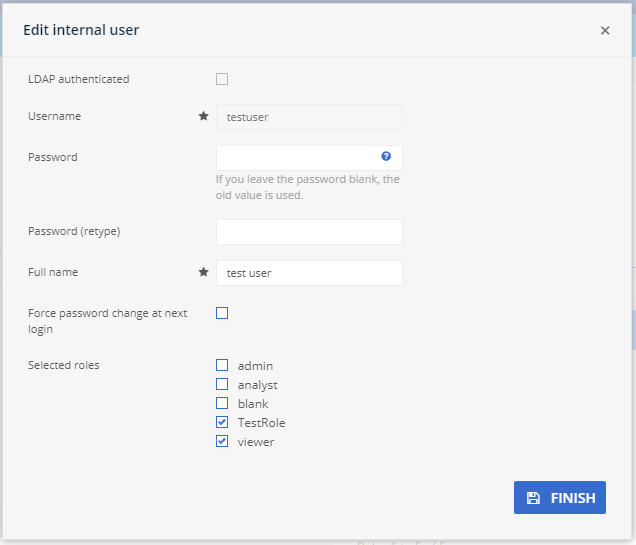
User creation
Create user accounts or profiles with the appropriate roles to ensure only the authorized personnel have access to the system .
Command Center allows creating user accounts with strong passwords, and other security considerations enhance the protection of sensitive data and systems. Properly implementing authentication also improves user experience and maintains security compliance.
Federated users (LDAP)
Authenticate user accounts using LDAP protocol from Command Center to facilitate federated identity and access control in a centralized manner. LDAP is commonly used for tasks that are related to identity and access management, user authentication, and directory services.
LDAP allows for centralized management of user accounts, attributes, and access rights across all connected services, reducing discrepancies and errors.
SSO
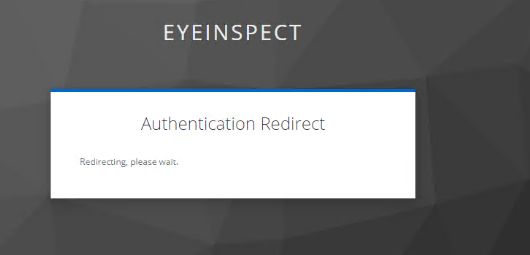
Authenticate users to Command Center and allow users to log in with a single set of credentials to gain access to multiple applications and services at multiple locations. This eliminates the need to repeatedly enter login credentials and enhances user experience and security.
SSO allows secure remote access and provides a seamless login experience. Users only need to remember one credential to access multiple applications. Moreover, it provides logs and audit trails of user activities.
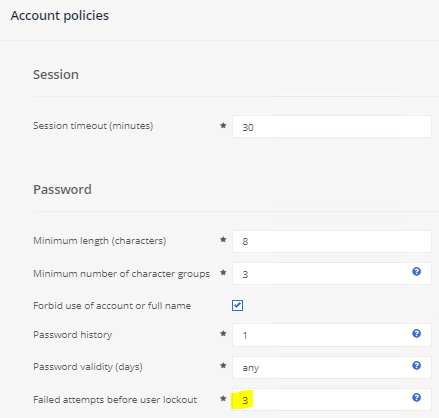
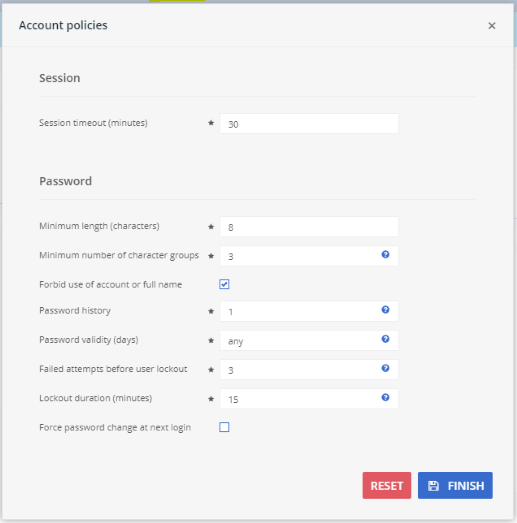
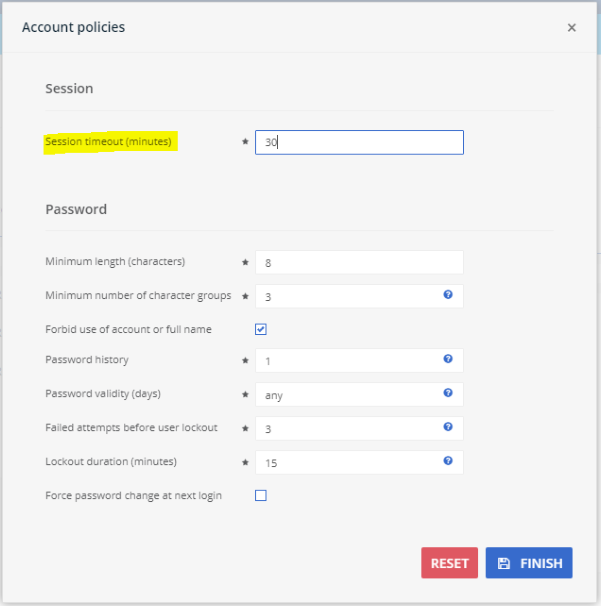
Password policy
Command Center allows administrators to set rules and guidelines that establish how passwords are managed with enforcement policies. When a user creates their password, it must meet the defined requirements (for example, minimum length, special characters, complexity, uniqueness, and so on).
A strong password policy can reduce the risk of compromise, enhance security, and adopt best practices and meet compliance requirements. Forescout allows administrators to modify password policies, as shown in the following figure.
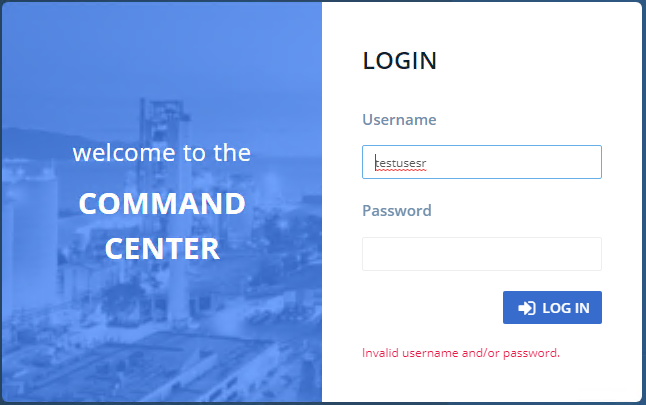
Authentication feedback
This feature responds to users during the authentication process to inform them that their login attempt is unauthorized and provides guidance for how to proceed.
This informs the user of the potential errors before they attempt to log in again. Forescout is validated to provide the appropriate authentication feedback without exposing too much information.
Authorization
Authorization is the process of granting or denying access rights to the systems based on the user/service credential. This ensures that only the relevant access is allowed based on defined roles.
User roles and privileges
Create roles and assign privileges for access control. This defines and manages the level of access and actions that users can perform. This helps to maintain security and manage the data integrity of the system.
With user roles and privileges, Forescout administrators can customize access to the individual to prevent unauthorized access to sensitive data.
Session timeouts
The system automatically logs users out of Command Center who have been idle for a specific period of time. It is designed to enhance security by reducing the risk of unauthorized access when users forget to lock their computer or leave it unattended.
Timeouts help to prevent unauthorized access when the user is inactive and protects sensitive data if the device is lost.
Accountability
Accountability is crucial in maintaining robust and effective cybersecurity. The individual is held responsible for their actions on the system.
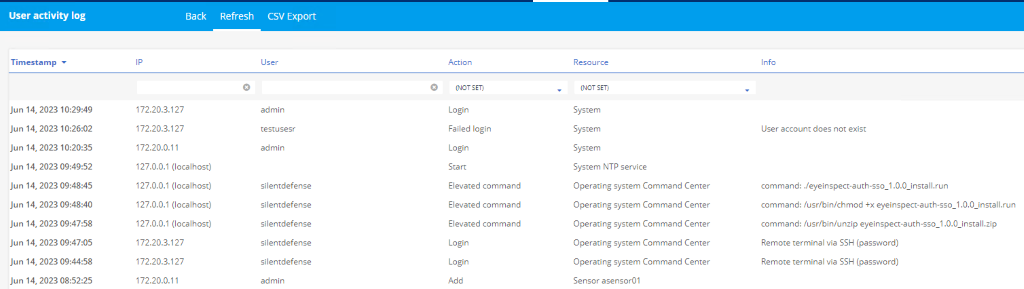
User activity log
Forescout keeps track of all user activities on Command Center and on servers. It captures information about user interactions, changes made to data, system activities, and other events.
These logs help to monitor for suspicious activities, provide insights into what caused a problem, and helps with problem solving, auditing, and accountability.
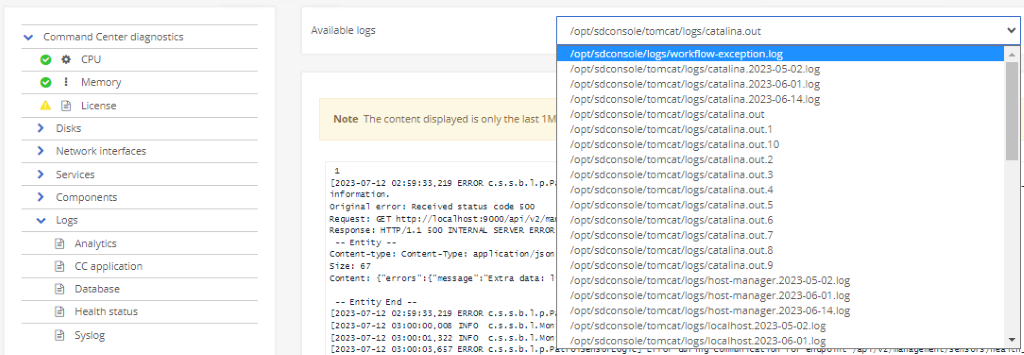
System event logs
The system event log keeps a record of various events and activities that occur within the system, captures important data about the system operations, errors, and warnings, and allows users to view logs in the Forescout Command Center diagnostic feature.
Value: System events help diagnose technical issues and errors, and help to identify trends or patterns within the system. Additionally, system events allow administrators to track changes and to detect, and respond to, potential security breaches.
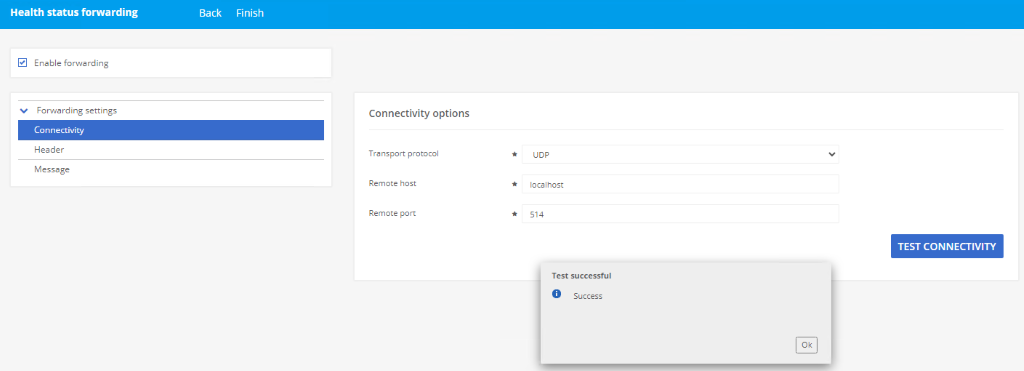
Forwarding health status logs
Forescout provides the capability to notify users when the health status changes to above or below a critical level. These notifications can be forwarded to a remote syslog server or SIEM (for example, Splunk ) to warn the user of any issues while they are not actively using the eyeInspect Command Center.
This results in faster response time to crucial events, helps avoid losses, ensures that sensitive data remains secure, and helps to maintain the trust of customers.
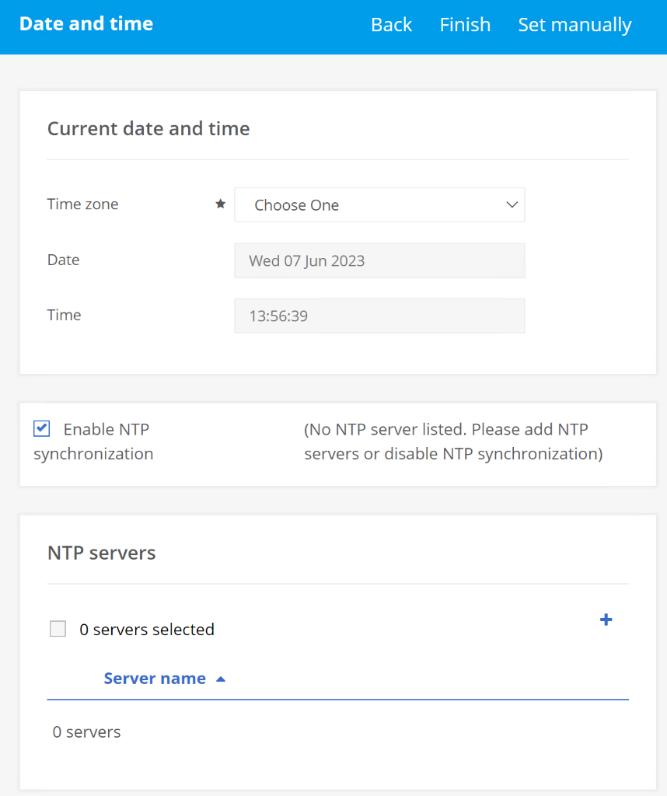
Clock
Time skew can impact the accuracy of logs, making them difficult to troubleshoot. To mitigate time skew, the Command Center date and time can be manually set, modified, or synced with NTP servers.
This helps with troubleshooting when using logs.
Account lockout
This feature helps to avoid brute force attacks. Forescout user accounts are locked when a certain number of consecutive failed logins have been attempted within a given time period. The user is temporarily denied access until the administrator unlocks their account, or the user has to wait for a period of time until their account is automatically unlocked.
This feature prevents unauthorized access and cyberattacks.