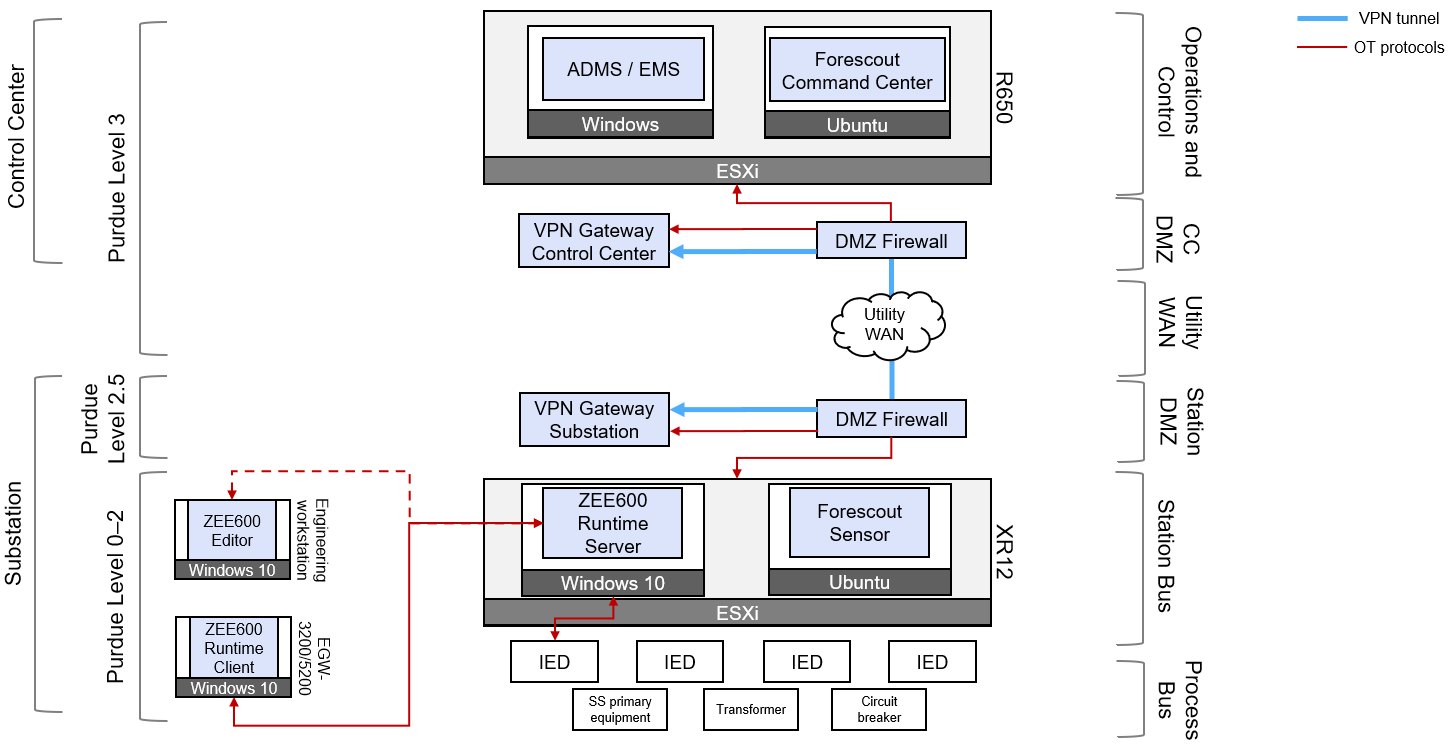
Connectivity between substations and the control center often requires connectivity over WAN connections. In many cases, the WAN connections can pose a major risk to the substation because of potentially untrusted activity on the WAN network. To defend against threats from outside the substation network, a secure architecture using a VPN tunnel has been validated for this solution. The VPN tunnel encrypts traffic between the substation and the control center, ideally terminating at the DMZ network of each location. The VPN tunnel protects any data that is transmitted over the WAN and it also applies best-practice routing using a DMZ so that there is no direct communication between the substation and external networks. The following figure illustrates an example of the validated secure architecture with both ABB ZEE600 and Forescout eyeInspect.
The following table lists firewall rules that can be applied at the substation DMZ firewall to allow the VPN traffic to establish between the VPN endpoints.
| Description | Source network/Host | Source device | Destination network | Destination device | Port |
| Allow the substation DMZ VPN client to connect to control center DMZ VPN server to establish a VPN tunnel. | Substation | Substation VPN client | WAN | Control center VPN server | TCP/UDP ###1 |
Another important factor to consider is the routing between the substation and control center. Traffic originating in the control center must know to use the VPN server to reach the substation network. The same is true for the hosts in the substation network, where traffic must be forwarded into the VPN client at the substation to be tunneled to the control center.
Lastly, firewall rules also have to be added in this architecture to allow traffic from the control center into the substation, and in reverse for traffic originating from the substation destined for the control center. To support these use cases, see the DMZ sections in the following ABB and Forescout cybersecurity sections.
