Home > Data Protection > PowerProtect Cyber Recovery > Dell PowerProtect Cyber Recovery: Reference Architecture > Cyber Recovery solution components
Cyber Recovery solution components
-
The Cyber Recovery solution includes the following components:
Production DD series—The source DD series contains the production data that the Cyber Recovery solution protects.
Vault DD series—The DD series system in the Cyber Recovery vault is the replication target for the source DD series.
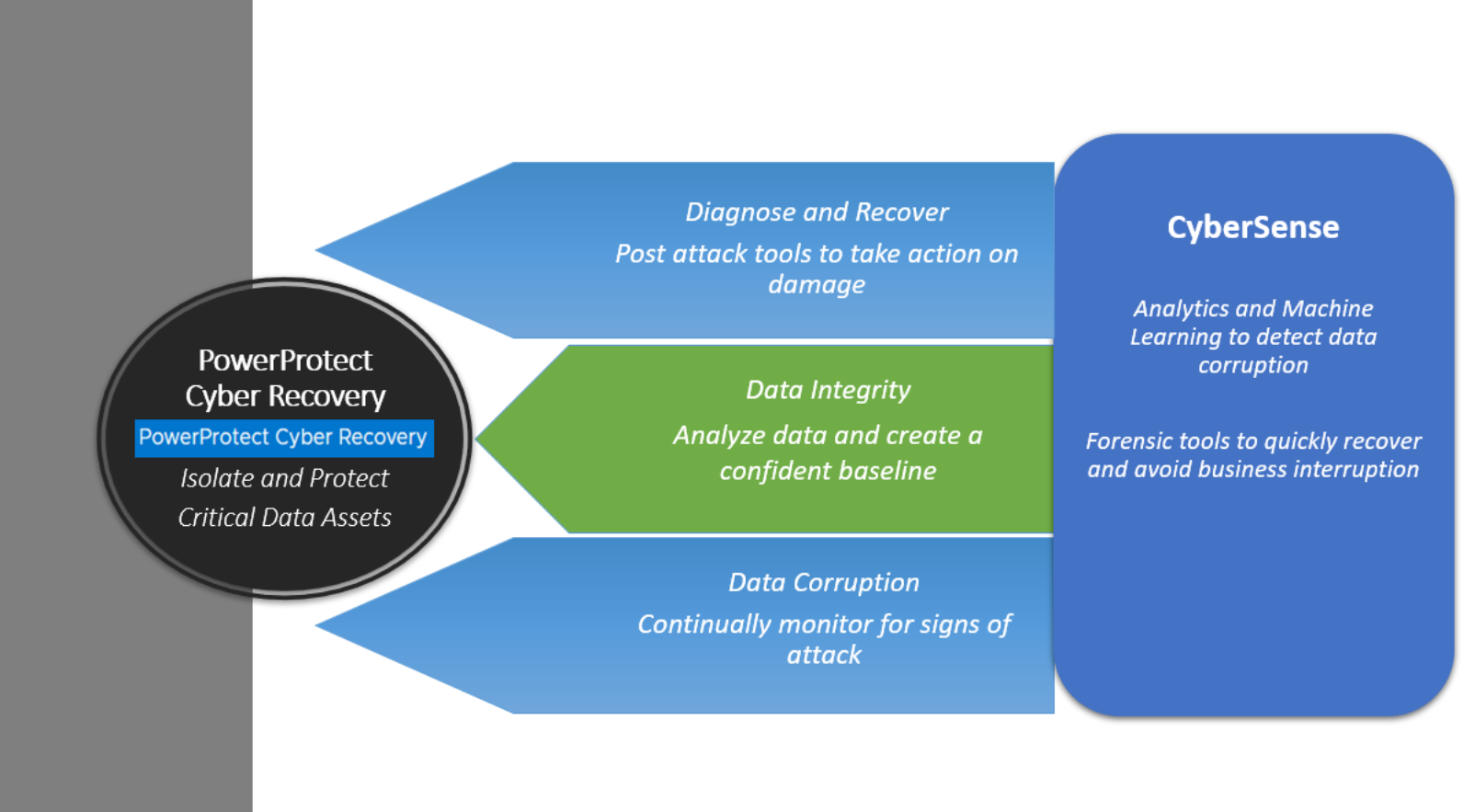
Cyber Recovery software—The Cyber Recovery software orchestrates synchronization, manages, locks the multiple data copies that are stored on the DD series in the Cyber Recovery vault, and orchestrates recovery. The software also governs the optional process of performing analytics on data that is stored on the DD series in the Cyber Recovery vault using the CyberSense feature.
Retention Lock (governance or compliance) software—Data Domain Retention Lock technology provides data immutability for a specified time. Retention Lock functionality is enabled based on Cyber Recovery policy configuration.
Cyber Recovery management host—Cyber Recovery software is installed on the management host. This server is installed in the vault environment.
Recovery hosts—The backup application recovery server is a designated server to which the backup application (NetWorker, Avamar, PowerProtect Data Manager, or other applications or combination of applications) and backup application catalog are recovered. Multiple servers can be deployed, depending on the recovery requirements of the solution. The backup application recovery server is sized so that all backup applications that are being protected by the Cyber Recovery solution can be recovered. If the Cyber Recovery solution is protecting a physical, single-node Avamar system in a production environment, a single-node Avamar system must also reside in the vault for recovery purposes.
Analytics/indexing host (CyberSense)—Cyber Recovery is the first solution to fully integrate with CyberSense. CyberSense adds an intelligent layer of protection to help find data corruption when an attack penetrates the data center. CyberSense is deployed on the Cyber Recovery vault environment. This innovative approach provides full content indexing. It uses machine learning (ML) to analyze the backup copies in the vault with over 100 content-based statistics and detects signs of corruption due to ransomware. CyberSense detects corruption with up to 99.5 percent confidence, identifies threats, and diagnoses attack vectors while protecting the business-critical content – all within the security of the vault.
Enhancements with CyberSense Version 7.9:
- Improved performance when indexing Dell Technologies backups on the PowerProtect DD server by using the DD Boost delta block API. CyberSense supports both performance Optimized and Capacity Optimized backups.
- Improved performance for the following workloads:
- For Avamar - VMDK
- For NetWorker - VMDK and file system Block Based Backup (BBB)
- For PowerProtect Data Manager - VMDK, file system BBB, and Exchange
Enhancements with CyberSense Version 8.0:
- An OVA deployment option is available.
- CyberSense support for SELinux Linux - SELinux can be set to “active” and “Enforcing” to meet STIGs requirement
- CyberSense can be deployed on AWS using an AMI which will be shared with customers’ AWS accounts by Dell Technologies
- Support for CyberSense migration from RHEL to SLES - Migrate data from a RHEL server to a SLES server
- CyberSense analyze dashboard - Provide a UI that was designed specifically for CyberSense workflow
Enhancements with CyberSense 8.2.0:
- CyberSense 8.2.0 supports Avamar backups of virtual machines running in a Microsoft Hyper-V environment.
- Before CyberSense 8.2.0, the host names in the CSV file attached to the CyberSense email that a customer received were obfuscated. The customer now receives a CSV file with the host names displayed, and the number of columns is reduced to only those columns that are of interest to the customer.
- For new deployments (CS OVA and CS package), you must provide a password (iepasswd admin) using a CLI command before you can log in to the CyberSense UI
- Before CyberSense 8.2.0 the licensed capacity of an index could not decrease; it could only increase if the amount of active data in the index increased. With the 8.2.0 release, high water mark licensing is eliminated. The licensed capacity of the index can decrease to reflect the amount of currently active data in the index.
- Before CyberSense 8.2.0, the CyberSense software identified files suspected of being attacked based on a fixed query for each attack class. With the 8.2.0 release, a new machine learning model that was trained with many real ransomwares identifies files that were likely attacked. This model increases the accuracy of identifying suspect files after an attack.
- The combination of CyberSense 8.2.0 and Cyber Recovery 19.13 provides the capability to create a storage configuration among the CyberSense servers and the Data Domain systems it connects with. This new configuration provides ongoing link integrity checking and improves the performance of indexing by introducing the ability to use multiple network links for accessing the Data Domain through the DDBoost protocol.
- When a ransomware attack is detected, the audit trail output that goes to the Linux syslog is enhanced with a message for each directory or folder that holds a file suspected of being attacked by the ransomware. This message contains a description of the detected attack, the host name, and the directory or folder that holds a suspect file.
Logical air gap
The term “air gap” implies physical isolation from an unsecure system or network. Logical air gap describes a physical connection but logical isolation from the network. The logical air gap provides another layer of defense by reducing the surface of attack.
Cyber Recovery provides the air-gapped feature to keep the Cyber Recovery vault disconnected from the production network. The DD series in the Cyber Recovery vault is disconnected (air-gapped) from the production network most of the time and is only connected when Cyber Recovery triggers replication.
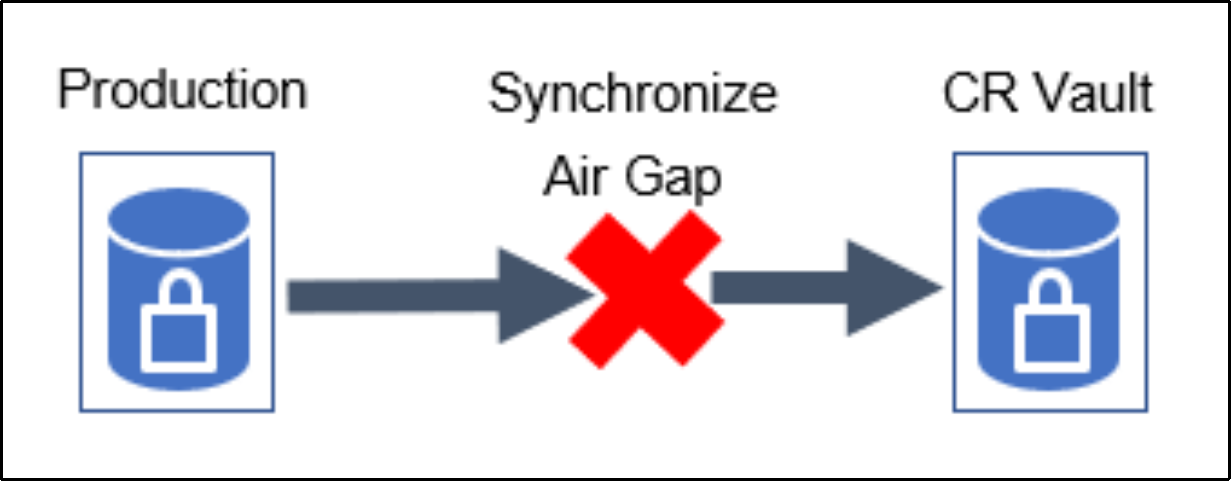
The DD series in the Cyber Recovery vault is connected to the production DD series only during the data synchronization operation.
