Home > Networking Solutions > Campus Switches and Solutions > Campus and Mobility Networking Solutions > Guides > ClearPass NAC and Posture Assessment for Campus Networks Deployment Guide > Dell W-ClearPass configuration – wireless
Dell W-ClearPass configuration – wireless
-
W-ClearPass is configured using a UI on standard browsers. This guide will show the key steps and screenshots for configuring the example scenario. The entire browser window is not shown in each screenshot to improve readability. Usually, the navigation window on the left side of the screen is not shown. To ensure readers understand the configuration location shown, the navigation path is given before each screenshot. Within each major section, the current tab is highlighted with a dark blue color.
W-ClearPass allows administrators to configure policies and profiles directly from the main service configuration screen. When using this method of configuration, the necessary windows are opened automatically, which can streamline the amount of time it takes an experienced user to configure a fully functional service. In this guide, each profile and policy will be built before the creation of the service to aid in the description of navigating this configuration in this document.
Note: This guide does not detail the initial setup of the W-ClearPass server. For more information about VM installation, initial server configuration, and licensing, see the W-ClearPass User Guide at https://www.dell.com/support.
Add W-series as a network device
Before W-ClearPass will recognize authentication requests, the controller originating the request must be added to the list of network devices in W-ClearPass. The IP Address and RADIUS shared secret must match the configuration used on the controller as shown in the figure below.
- From the W-ClearPass Welcome screen, click the ClearPass Policy Manager module. The ClearPass Policy Manager opens.
- Go to the Network Devices page by clicking Configuration > Network > Devices.
- Click +Add. The Add Device window opens.
- Enter the Name of the switch, IP Address, Description, and RADIUS Shared Secret in the fields provided.

Figure 46. W-series device settings
- From the Vendor Name drop-down box, select Aruba and click Add.
Add Active Directory as an Authentication Source
To add Active Directory as an Authentication Source, perform the following steps:
- Open the Authentication Sources page by clicking Configuration > Authentication > Sources.
- Click +Add.
- Enter the details for the authentication source as shown in the following figure.

Figure 47. Active Directory Authentication Source
The figure above shows a partial configuration of the Active Directory Authentication Source. This example uses a Windows Server with Active Directory installed as the source for username and password credential store.
W-ClearPass supports many different authentication sources.
Note: For more details on Active Directory configuration and other source types, see the W-ClearPass User Guide at https://www.dell.com/support.
Create 802.1X Wireless service with Posture checks
W-ClearPass includes templates for many common services. These templates allow administrators to easily build the services and their associated policies.
This section details the use of the Aruba 802.1X Wireless template in the Start Here section within the Configuration section.
To create an 802.1X Wireless Service with Posture checks:
- Click Configuration > Start Here.
- To launch the wizard, select the Aruba 802.1x Wireless template.

Figure 48. Aruba 802.1X Wireless template
- From the General tab, enter the Name Prefix in the field provided. This name identifies the service name and policy names that the template generates.
Note: The 802.1X Wireless name is later appended to the name prefix.

Figure 49. Aruba 802.1X Wireless – General tab
- Click Next. The Authentication tab opens.

Figure 50. Aruba 802.1X Wireless – Authentication tab
- From the drop-down menu, select the Authentication Source that was configured in the previous steps.
Note: Extra authentication sources can be added later.
- Click Next >. The Wired Network Settings tab opens.

Figure 51. Aruba 802.1 Wireless – Wireless Network Settings tab
- From the drop-down menu, select the network device (W-series controller) that was configured in the previous steps.
- Click Next > The Posture Settings tab opens.

Figure 52. Aruba 802.1X Wireless – Posture Settings tab
- Select the operating systems that OnGuard needs to support.
- Enter a Quarantine Message in the Quarantine Message: field.
Note: This message is displayed any time OnGuard detects a posture compliance issue.
- Click Next >. The Enforcement Details tab opens.

Figure 53. Aruba 802.1X Wireless – Enforcement Details tab
- Enter the user role information configured on the wireless controller.
Note: The User Role names must match exactly. These settings can be changed and added later.
- Click Add Service.
Two Services are now added to the Services list.

Figure 54. Services added using template wizard
Note: The numbering may vary between deployments.
To view the services, go to Configuration > Services. The two Services shown in previous figure are modified after the Posture, Role Mapping, and Enforcement Policies are configured.
Define Posture policies
The Aruba 802.1x Wireless template creates three posture policies with the prefix name used in the template. These policies are identical to the policies generated in the wired Define Posture policies section.

Figure 55. Posture policy list
Note: Administrators can use the same wired and wireless policies to simplify the configuration. This example uses the wired policies previously created. If the wired example has not been completed within your network, see the Define Posture policies section.
Define Roles and Role Mapping
Role Mappings are used to apply conditions to each user to classify them into Roles. The Roles are then used to identify users and can be used to enforce policies within the Service. There are numerous conditions and rules that can be used to form a Role Mapping. For more information about Roles and Role Mapping, refer to the W-ClearPass Policy Manger User Guide at https://www.dell.com/support.
In this guide, this example uses default Roles built into the W-ClearPass Policy Manger. The two Roles are [Employee] and [Guest]. Brackets surrounding the name identify default configurations in W-ClearPass.
Create a new Role Mapping
- Click Configuration > Identity > Role Mappings.
- Click the + Add link in the upper right corner.
- Enter a Name for the policy, in the field provided. For this example, W-Series Wireless Role Mapping is used.
- In the Default Role drop-down, choose [Guest] and then click Next.
- From the Mapping Rules tab, click Add Rule. The Rules Editor opens

Figure 56. Rules Editor screen
- Enter the following information in the designated fields:
- Type: Authorization: CPDC (name of the Active Directory used in this example)
- Name: Department
- Operator: CONTAINS
- Value: Employee (value used in the department field of an Active Directory user account)
- Use the [Employee] Role for the Role Name.
Administrators can build sophisticated condition lists and any number of Rules to be as specific as needed to identify many types of users. This simplistic example will result in any user with the Employee department name in Active Directory being assigned the [Employee] Role. Any user that does not have this Active Directory department field populated with Employee will be assigned the default [Guest] Role.
- Click Save and then click Next > to move to the Summary tab.
- Verify the information is correct, then click Save. The new role mapping displays in the Role Mapping list.
The new role mapping will be used in the 802.1x RADIUS Service. A role mapping will not be used for the Health Check Service. A more detailed explanation of the two services is discussed later in this section.
Define Enforcement policy and Profiles
Enforcement Policies are a group of rules with conditions that direct enforcement actions that ultimately are sent to the Network Access Device, which in this example is the W-Series controller. Enforcement profiles are a collection of attributes that define those enforcement actions.
The Aruba 802.1x Wireless template with posture checks produced two Services the Health Check Service and the Radius Service. Both of these services need Enforcement Policies, and their associated Enforcement Profiles. The Health Check Service produces a posture token by performing an action), while the Radius Service will use that token (within its conditions) to determine a User Role assignment action.
Enforcement Profiles are used within the Enforcement Policies, so the profiles are configured first.
Health check enforcement profiles and policies
Terminate Session profile for the Health Check service
The Health Check Service requires a profile to terminate the session so that the RADIUS 802.1X authentication Service can use the posture token in a new authentication routine. The terminate session profile uses the Change of Authorization feature to force a reauthentication.
W-ClearPass has a default terminate session profile that can be used with the W-series controller. The name of the profile is [Aruba Terminate Session]. This example uses the default profile.
Enforcement policy for the Health Check service
The following will detail an example of configuring the Enforcement Policy for the Health Check Service. The prepopulated policy from the template is sufficient for this example and most of the default settings are kept.
- Click Configuration > Enforcement > Policies to access the list of Enforcement policies.
- Click the prepopulated policy name for the Health Check Service.
In this example, the name is Posture Scenario Aruba 802.1X Wireless OnGuard Agent Enforcement Policy, and its type is WEBAUTH. The template automatically generates this policy based on the prefix name.
- Click the Enforcement tab.
- Under the Default Profile, verify that the [RADIUS_CoA] Aruba Terminate Session is selected.
- Click the Rules tab.
For the example in this guide, use the prepopulated conditions and actions, leaving all other conditions at their default setting.

Figure 57. Enforcement policy for OnGuard Service
The first condition states that any posture token values not equal to HEALTHY (0) trigger this rule to be enforced. The Enforcement Profiles under the condition are the actions that are applied if the conditions in this rule are met. The first profile in the list is named [Agent] Posture Scenario Aruba 802.1X Wireless Quarantined Agent Enforcement. This profile displays a quarantine message to the client. You can access this profile in the list of Enforcement Profiles by clicking Configuration > Enforcement > Profiles. The profile was created from the Service template during the Service creation earlier. The settings for this profile are kept as the default and are not shown in this guide.
The second condition states that any posture token values equal to HEALTHY(0) trigger this rule to be enforced. The Enforcement Profiles under the condition are the actions that are applied if the conditions in this rule are met. The first profile in the list is named [Agent] Posture Scenario Aruba 802.1X Wireless Healthy Agent Enforcement. This profile displays a healthy message to the client. You can access this profile in the list of Enforcement Profiles by clicking Configuration > Enforcement > Profiles. The profile was created from the Service template during the Service creation earlier. The settings for this profile are kept as the default and are not shown in this guide.
This concludes the Enforcement Policy and profiles for the Health Check Service. The next steps detail the configuration for the policy and profiles used in the RADIUS 802.1X Service.
RADIUS 802.1X Enforcement profiles and Policies
Enforcement profile for RADIUS 802.1X service
The RADIUS 8021.X Service requires an Enforcement profile to enable the assignment of a user role. In this example, a client device that fails a health check will be assigned to a quarantine user role named OnGuard-redirect. A client device that passes a health check will be assigned an employee user role named Employee. These user roles were previously configured in the W-Series controller.
The following steps create a profile to enforce a user role assignment.
- Click Configuration > Enforcement > Profiles to access the list of Enforcement Profiles.
- Click the + Add link in the upper right corner.
- From the Template drop-down menu, select Aruba RADIUS Enforcement.
- Enter a Name for the policy in the field provided and leave all other options at their default setting.
Note: This example uses W-Series Employee Role as the profile name.
- Click Next > to move to the Attributes tab.
- For the Attribute value, click Value Enter Role here and manually enter the name of the User roles configured on the W-series controller for employees.
Note: In this example, Employee is the User role. Verify that the User role name exactly matches the user role name on the controller.
- Click the disk icon on the right to save the attribute line.
- Click Next > and review the information within the Summary tab.
- Click Save. The Summary tab should look similar to the following image:

Figure 58. Enforcement profile – Employee role
Create a profile to enforce a Quarantine User role
The following steps create a profile to enforce a quarantine user role assignment.
- To access the list of Enforcement Profiles, click Configuration > Enforcement > Profiles.
- Click the + Add link in the upper right corner.
- From the Template drop-down menu, choose Aruba RADIUS Enforcement.
- Enter a Name for the policy in the field provided and leave all other options at their default setting.
Note: This example uses W-Series Redirect to OnGuard as the profile name.
- Click Next > to move to the Attributes tab.
- On the Attribute value, click Value Enter Role here and manually enter the name of the user roles configured on the W-series controller for employees.
Note: In this example, OnGuard-redirect is the user role.
- Verify that the user role name exactly matches the user role name on the controller.
- Click the disk icon on the right to save the attribute line.
- Click Next > and review the information within the Summary tab.
- Click Save.
Enforcement policy for the RADIUS 802.1X service
Use the following steps in this section to configure the Enforcement Policy for the RADIUS 802.1X Service. Use the prepopulated policy from the template for this example and note that some settings will be kept as default.
The following steps describe the contents of the Enforcement Policy.
- Click Configuration > Enforcement > Policies.
- Click the prepopulated policy name for the Health Check Service.
Note: In this example, the name is Posture Scenario Aruba 802.1X Wireless Enforcement Policy, and the type is RADIUS. The template for this policy is automatically generated based on the prefix name.
- Click the Enforcement tab.
- Under the Default Profile, choose [W-Series Redirect to OnGuard].
Note: This example uses the quarantine profile to place users that fail authentication checks into the quarantine user role. If the administrator chooses, a profile to deny access or place users into a different user role is possible here.
- Click the Rules tab.
- Remove all the default rules by selecting each rule and clicking Remove Rule.
In this example, the authentication policy has only two outcomes given the correct credentials:
- The user is authenticated, is identified as an Employee, and has a Healthy token
- The user is authenticated and does not have a Healthy token
The first outcome places the user in the employee user role Employee. The second outcome places the user into a quarantine user role OnGuard-redirect.
Note: If other user classifications and conditions are needed, you can add them now. More profiles or user roles may be required.
- Click Add Rule to configure rules per the example above.
- Create two conditions:
Note: The first condition must be saved before the second condition can be created.
Condition 1
- Type: Tips
- Name: Role
- Operator: EQUALS
- Value: [Employee] (add other roles to the list here if applicable)
Condition 2
- Type: Tips
- Name: Posture
- Operator: EQUALS
- Value: HEALTHY (0)
- Under the Enforcement Profiles section, choose [RADIUS] W-Series Employee Role. The Rules Editor screen should look like the following figure:

Figure 59. Enforcement policy – Healthy Employee rule
- Click Save.
- Click Add Rule to create a second rule.
- Create two conditions:
Note: The first condition must be saved before the second condition can be created.
Condition 1
- Type: Tips
- Name: Role
- Operator: EQUALS
- Value: [User Authenticated]
Condition 2
- Type: Tips
- Name: Posture
- Operator: NOT_EQUALS
- Value: HEALTHY (0)
- Under the Enforcement Profiles section, choose [RADIUS] W-Series Redirect to OnGuard.
- The Rules Editor screen should look like the following figure:

Figure 60. Enforcement policy – Not Healthy rule
- Click Save.
- Click Save again to save the Enforcement Policy.
Configure Services
After you have defined and configured all the components of the Service, you can now configure the Services.
- Click Configuration > Services.
- Select Service: Posture Scenario Aruba 802.1X Wireless.
- Select the Service tab.
The template populates the Service Rules with two rules and requires that all rules match. In this example, you will only have to define the SSID name. Administrators can add other rules to narrow the devices that this Service will be applied to.
- Click the third rule and change Operator to CONTAINS, and the Value to the Name of the SSID of your network.
Note: In this example, the SSID name is Employee_CPDG. The Service tab should look like the following image.

Figure 61. 802.1X Wireless Service – Service tab
- Click the Authentication tab.

Figure 62. 802.1X Wireless Service – Authentication tab
Note: This example uses Microsoft Active Directory with username and password credentials. Keep the authentication methods for this example at the default settings. Dell Technologies recommends that you use any type of authentication method as required by your network security policy.
- Remove or add authentication methods.
- Remove or add authentication sources as needed
- Click the Roles tab.

Figure 63. 802.1X Wireless Service – Roles tab
- For the Role Mapping Policy, select W-Series Wireless Role Mapping from the drop-down menu.
- Click the Enforcement tab. The template populates the appropriate Enforcement Policy in the drop-down menu.
- Verify that the correct policy details are shown.

Figure 64. 802.1X Wireless Service – Enforcement tab
- Click Save.
- Click Service: Posture Scenario Aruba 802.1X Wireless Posture Checks.
- Click the Service tab.
Note: For this example, leave all other options at their default setting.
- Click the Roles tab.
Note: For this example, Roles are not needed for the Health Check Service.
- Select the Posture tab.

Figure 65. 802.1X Wireless Posture Service – Posture tab
During testing, you can keep the Posture Policies at their default settings, however, Dell Technologies recommends that you modify each policy specific to the operating system to reflect the heath posture being tested.
- Click the policy agent type and click Modify to open the policy window.
- Select the Posture Plugins tab and click the Configure button under Plugin Configuration. Default settings enable antivirus and firewall checks for each operating system version.
For initial testing, Dell Technologies recommends that you validate the functionality using the health check settings within a single operating system, such as Windows 7 and firewall.
- Click Save to save the Plugin Configuration.
- Click Save again to save the Posture Policy.
Note: It is also useful to have control over the health status of the client. Autoremediation can fix many health issues automatically on the device. To verify that the assigned VLANs and other enforcement actions, Dell Technologies recommends that you clear the Remediate End-Hosts checkbox. This box can be checked at any time after verifying the policy actions are behaving as expected.
- Click the Enforcement tab.

Figure 66. 802.1X Wireless Posture – Enforcement tab
The template populates the appropriate Enforcement Policy in the drop-down menu.
- Verify that the correct policy details are shown.
- Click Save.
W-ClearPass Services are now configured to include all supporting policies and roles.
Create OnGuard landing webpage
The captive portal function within the W-Series controller can be used on both guest and employee networks. In this example, an employee network is enabled with a captive portal to allow easy access to the OnGuard download URL. It also provides access to the OnGuard dissolvable client URL.
W-ClearPass Guest provides a single solution web-hosting feature that does not require a separate webpage. If necessary, administrators can also use their own web hosting solution.
To create an OnGuard landing webpage:
- From the W-ClearPass Welcome screen, select the ClearPass Guest module.
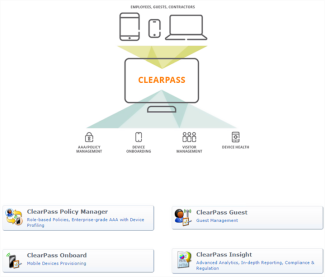
Figure 67. W-ClearPass Welcome page
- Click to Home > Configuration > Pages > Web Logins.
- In the upper right corner of the screen, click Create a new web login page.
- In the Name field, enter a descriptive name. For example, you can enter OnGuard Portal.
- For the Page Name, enter a name used in the URL. For example, you can enter OnGuard.
Note: The Page Name should match the name used in the URL in the Create Captive Portal Authentication Profile section (http://ClearPass.IP.address/guest/page_name.php where page_name is the name entered in this step).

Figure 68. Web Login Editor – Name, Page Name, and Login Method selections
- From the Login Method, select Policy – initiated. This option ensures that an enforcement policy will control a change of authorization.
- For the Login Form - Authentication, select Anonymous. The selection of this option ensures that you will not require a username or password.
- Click to place a checkmark in the Auto-Generate the anonymous account.
Note: Leave the Anonymous User field blank, as it will autopopulate the necessary information.

Figure 69. Web Login Editor – Authentication, Auto-Generate, Anonymous User, Pre-Auth Check, and Log In Label selections
- If needed, click to place a check in the Enable bypassing the Apple Captive Network Assistant.
- For the Login Form – Custom Labels, click to place a check in the Override the default labels and error messages box.
- For the Login Form - Pre-Auth Check, select Local – match a local account.
- Under the Login Form – Log In Label section, enter a descriptive label in the field provided. For example, enter Press to Run Health Check.
- From the Login Page – Header HTML section, enter any instructions or webpage html customization requirements for the header. In this example, the following HTML coding is used:
{nwa_text id=7980}<p>
<br>
To determine if your client meets the minimum security requirements:
<br>
<br>
Press the button below to run the dissolvable agent
<br>
<br>
</p>{/nwa_text}

Figure 70. Web Login Editor – Header HTML and Footer HTML field examples
- For the Under Login Page – Footer HTML section, enter additional instructions and the URL for each OnGuard download link.
Note: You can view the URL by accessing the W-ClearPass Policy Manager UI, or by clicking Administration > Agents and Software Updates > OnGuard Settings.
In this example, the following HTML is used:
{nwa_text id=7979}<p>
<br>
<p>OR</p>
<br>
<br>
<p>Click the link to download the persistent client.
<br>
<br>
</p>
<a href="http://172.25.172.188/agent/installer/windows/ClearPassOnGuardInstall.exe">Windows OnGuard Persistent Agent
</a>
<br>
<br>
<a href="http://172.25.172.188/agent/installer/mac/ClearPassOnGuardInstall.dmg">Mac OSX OnGuard Persistent Agent
</a>
<br>
<br>
<a
href="http://172.25.172.188/agent/installer/ubuntu/ClearPassOnGuardInstall.tar.gz">Ubuntu OnGuard Persistent Agent
</a>
</p>{/nwa_text}
- From the Post-Authentication - Health Check section, click to place a check in the Require a successful OnGuard health check.

Figure 71. Require a successful OnGuard health check, Client Agents, and Save Changes options
- In the Post-Authentication - Health Check section, select Native agents only.
- Click Save Changes.
- From the Configuration page, verify that the web login page is successfully configured by selecting the name of the web login and clicking Test under the name.

Figure 72. Confirmation of web login page configuration
The page displays in a new browser. If the example settings and HTML coding provided was used, the Login page should look like the following example:

Figure 73. Example Web Login page
Test the configuration
The W-ClearPass and N-Series configuration in this guide can be tested with any client. The following details the use of a Windows 7 laptop.
- Ensure that the user is defined and entered into the Active Directory with a Department of Employee and that the laptop is part of the domain.
- Connect the laptop to the appropriate SSID and verify that the laptop firewall is enabled.
- When prompted, enter the log in credentials on the laptop.
- When the user is authenticated, verify that the user is placed into the quarantine user role due to absence of a health token.
- Open a browser so that you are redirected to the landing page.
- Install OnGuard by clicking the appropriate download link (persistent or dissolvable).
- Once installed, wait for OnGuard to scan the health. OnGuard initiates a reauthentication where the user is placed into the employee user role.
- Turn off the laptop firewall.
- Wait for OnGuard to rescan health after detecting a change to the firewall. OnGuard initiates a reauthentication where the user is placed into the quarantine user role.
- Turn firewall on.
- Wait for OnGuard to rescan health after detecting a change to the firewall. OnGuard initiates a reauthentication where the user is placed into the employee user role.
