

Multi-factor Authentication with Unisphere for PowerMax
Wed, 29 Mar 2023 12:58:42 -0000
|Read Time: 0 minutes
Protecting your data is what Dell storage arrays do best, but protecting who can control and manage that storage is equally important. Features like multi-factor authentication (MFA) are a must-have for many industry sectors. MFA reduces the potential for bad actors to cause malicious damage to storage configurations, providing additional peace of mind for security concerns on storage platforms.
In Unisphere for PowerMax 10.0, we are introducing MFA for Unisphere for PowerMax. This feature introduces the ability to combine authentication for your LDAP users with additional RSA token validation.
Note: Since the original publication of this blog, MFA for Unisphere for PowerMax has been backported to Unisphere 9.2.3 as well.
MFA works on existing PowerMax arrays and on the new PowerMax 8500 and 2500 models running Unisphere for PowerMax 10.0 or higher. MFA also enforces role-based access policies for users and groups for enhanced security. This blog briefly walks you through the few steps required to set up this feature.
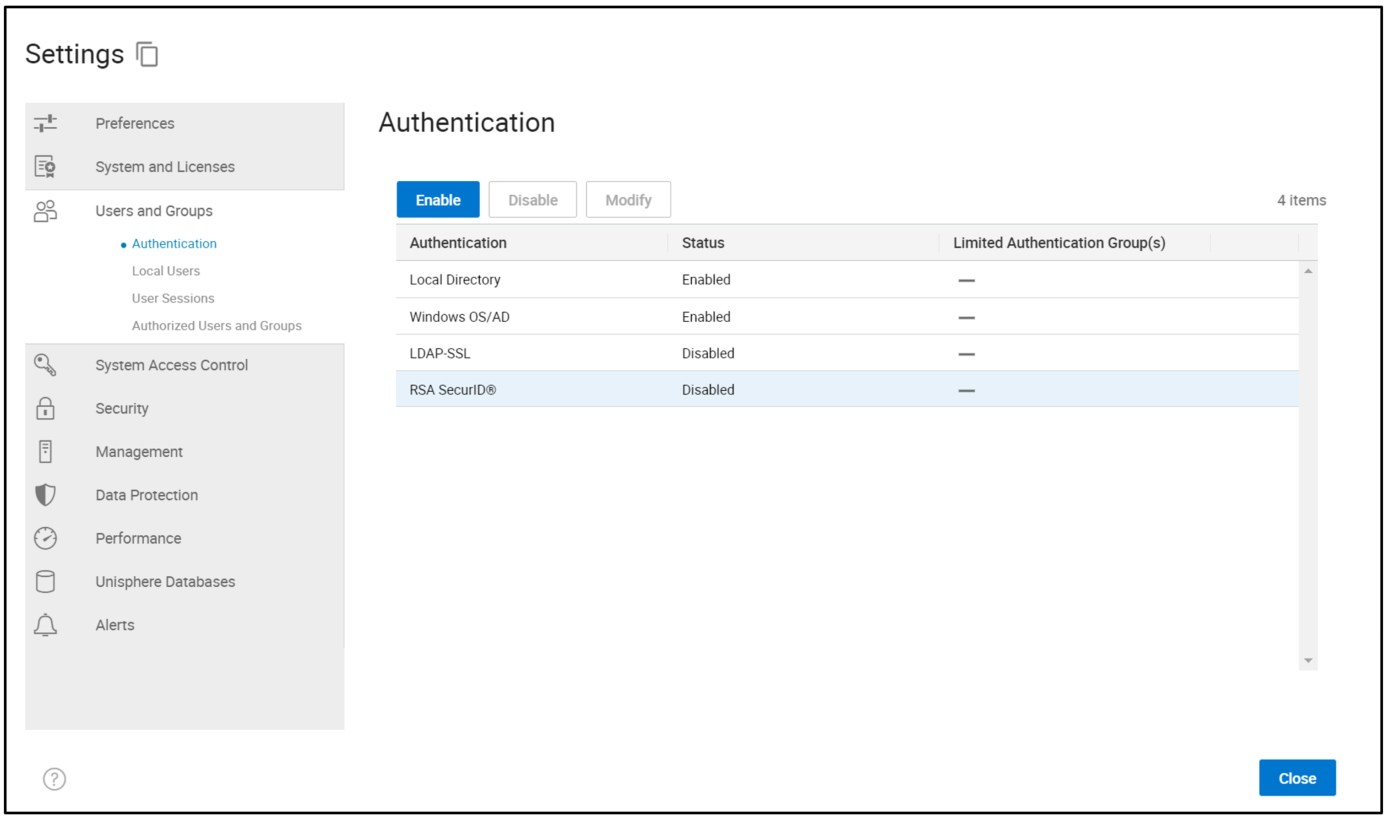
When you use the Unisphere UI to configure MFA, under Users and Groups > Authentication, you will see RSA SecurID®. Before you start, you must configure LDAP-SSL for user authentication and set up your users and groups with the required permissions. (There is no change to this process – for guidance, see the existing documentation or Unisphere online help.)
When LDAP is set up, select RSA SecurID®, and then click Enable to launch the configuration wizard, as shown here.
This displays the next screen in the wizard (Enable RSA SecurID®).
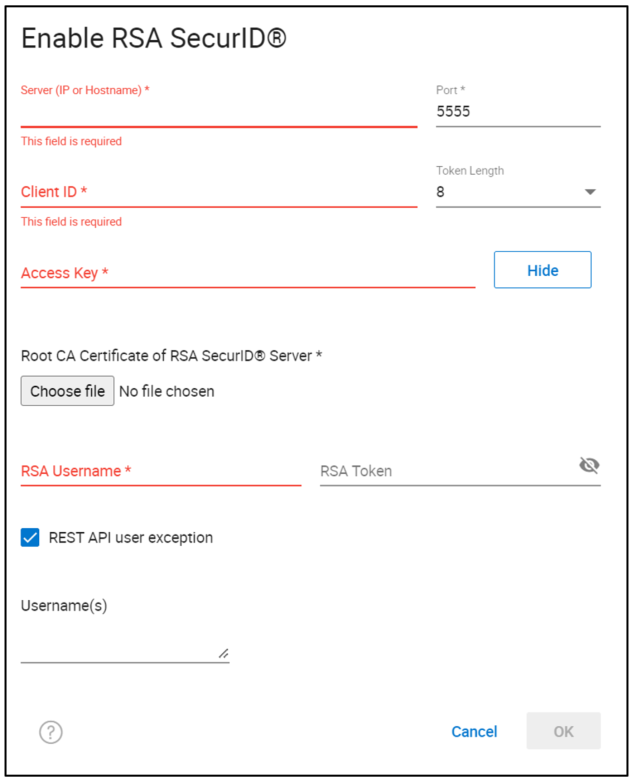
This screen prompts you to provide input for the required fields to configure multi-factor authentication with RSA, specifically:
- The Server name of the RSA server.
- The Port number for the RSA server.
- The Token Length, either 6 or 8 digits, indicating the length of the token that will be generated by your RSA fob or APP.
- Client ID and the Access Key – This information must be provided by the RSA administrator from the RSA Security Console, as shown here.
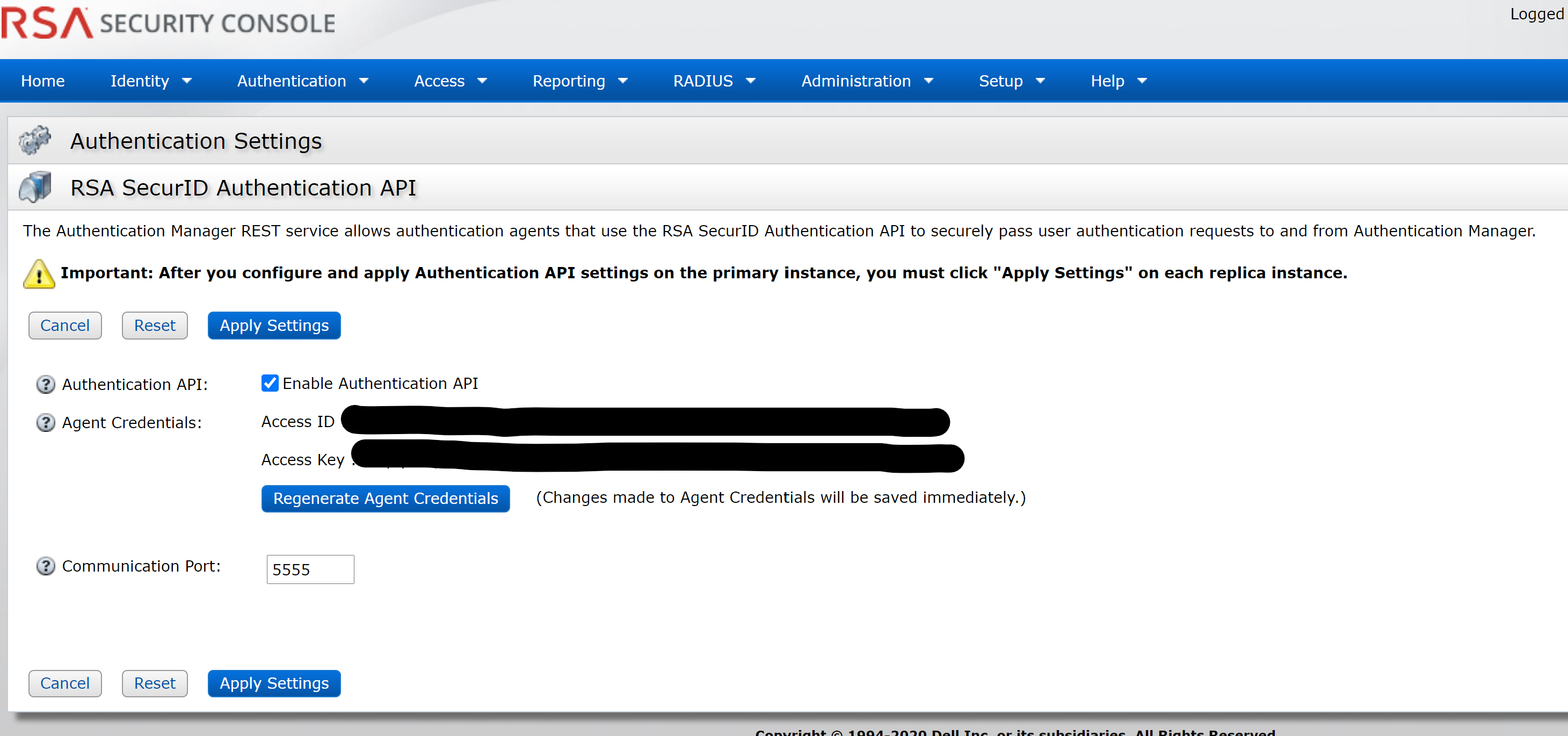
Log into the Security Console and select Home > System Settings > RSA SecurId Authentication API.
The Access ID and Access Key are entered as the Client ID and Access Key, respectively. Because this information is highly sensitive, it will likely require collaboration between teams to enable it.
Back on the Enable RSA SecurID® screen, on the Unisphere server, enter the Root CA Certificate of the RSA controller.
When these fields are configured, you will need an RSA user and token that can initiate the configuration handshake with the RSA server supplied in the config. To validate the connection, the RSA user can be any user. After entering this, click OK and RSA MFA is enabled!
There is an option to omit certain user accounts from MFA, such as for REST API users, where it is not practical to validate RSA tokens on each call. Credentials for these users should be stored in a secure vault with additional authentication for REST applications to obtain and use.
At this point, any user attempting to log in to the Unisphere for PowerMax UI will need to provide their LDAP username and password, prefixed with their six- or eight-digit RSA Token ID, providing additional security through multi-factor authentication with the RSA server and LDAP.
Author: Paul Martin, Senior Principal Technical Marketing Engineer
Twitter: @rawstorage



