Configure SSH Multi-Factor Authentication on OneFS Using Duo
Thu, 27 Jan 2022 21:03:07 -0000
|Read Time: 0 minutes
Duo Security at Cisco is a vendor of cloud-based multi-factor authentication (MFA) services. MFA enables security to prevent a hacker from masquerading as an authenticated user. Duo allows an administrator to require multiple options for secondary authentication. With multi-factor authentication, even though a hacker steals the username and password, he cannot be authenticated to a network service easily without a user’s device.
SSH Multi-Factor Authentication (MFA) with Duo is a new feature introduced in OneFS 8.2. Currently, OneFS supports the SSH MFA with Duo service through SMS (short message service), phone callback, and Push notification via the Duo app. This blog describes how to integrate OneFS SSH MFA with the Duo service.
Duo supports many kinds of applications, such as Microsoft Azure Active Directory, Cisco Webex, and Amazon Web Services. For a OneFS cluster, it appears as a "Unix Application" entry. To integrate OneFS with the Duo service, you must configure the Duo service and the OneFS cluster. Before configuring OneFS with Duo, you need to have Duo account. In this blog, we used a trial version account for demonstration purposes.
Failback mode
By default, the SSH failback mode for Duo in OneFS is “safe”, which allows common authentication if the Duo service is not available. The “secure” mode will deny SSH access if the Duo service is not available, including the bypass users, because the bypass users are defined and validated in the Duo service. To configure the failback mode in OneFS, specify the --failmode option using the following command:
# isi auth duo modify --failmode
Exclusion group
By default, all groups are required to use Duo unless the group is configured to bypass Duo auth. The groups option allows you to exclude or specify dedicated user groups from using Duo service authentication. This method provides a way to configure users so they can still SSH into the cluster even when the Duo service is not available and failback mode is set to “secure”. Otherwise, all users may be locked out of the cluster in this situation.
To configure the exclusion group option, add an exclamation character “!” before the group name and preceded by an asterisk to ensure that all other groups use Duo service. For example:
# isi auth duo modify --groups=”*,!groupname”
Note: zsh shell requires the “!” to be escaped. In this case, the example above should be changed to:
# isi auth duo modify --groups=”*,\!groupname”
Prepare the Duo service for OneFS
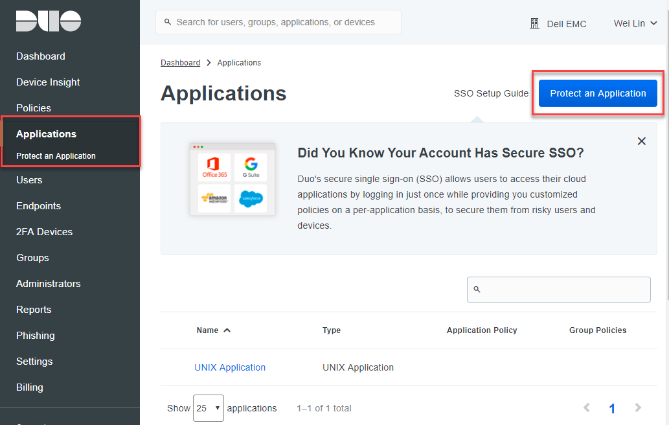
1. Use your new Duo account to log into the Duo Admin Panel. Select the Application item from the left menu, then click Protect an Application, as shown in Figure 1.
Figure 1 Protect an Application
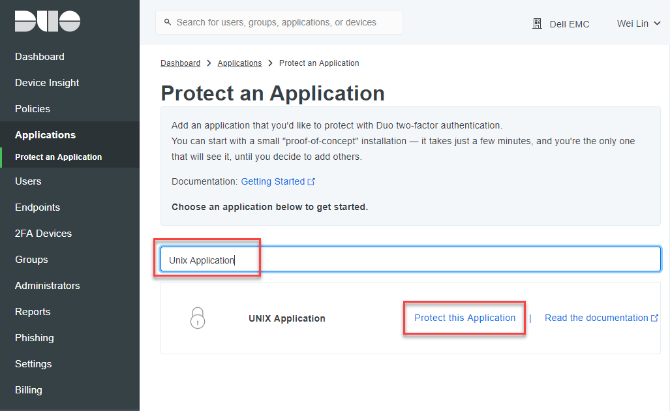
2. Type “Unix Application” in the search bar. Click Protect this Application to create a new UNIX Application entry.
Figure 2 Search for UNIX Application
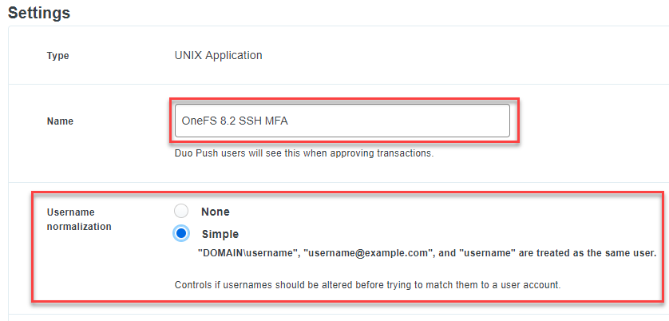
3. Scroll down the creation page to find the Settings section. Type a name for the new UNIX Application. Try to use a name that can recognize your OneFS cluster, as shown in Figure 3. In the Settings section, you can also find the Duo’s name normalization setting.
By default, Duo username normalization is not AD aware. This means that it will alter incoming usernames before trying to match them to a user account. For example, "DOMAIN\username", "username@domain.com", and "username" are treated as the same user. For other options, refer to here.
Figure 3 UNIX Application Name
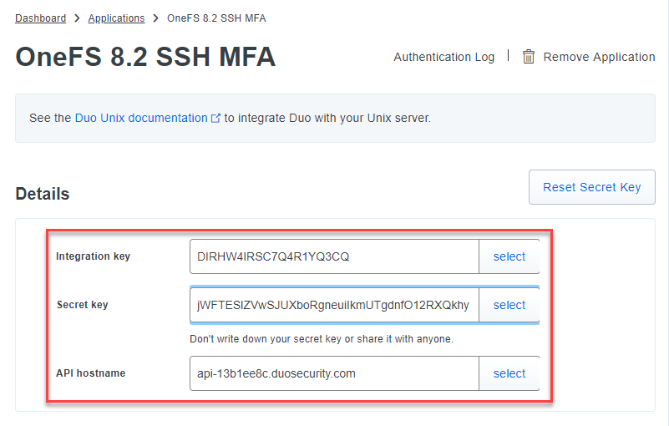
4. Check the required information for OneFS under the Details section, including API hostname, integration key, and secret key, as shown in Figure 4.
Figure 4 Required Information for OneFS
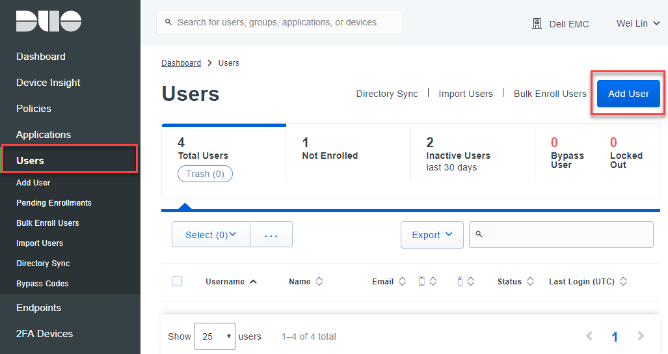
5. Manually enroll a user. In this example, we are creating a user named admin, which is the default OneFS administrator user. Switch the menu item to Users and click the Add User button, as shown in Figure 5. For details about user enrollment in the Duo service, refer to the Duo documentation Enrolling Users.
Figure 5 User Enrollment
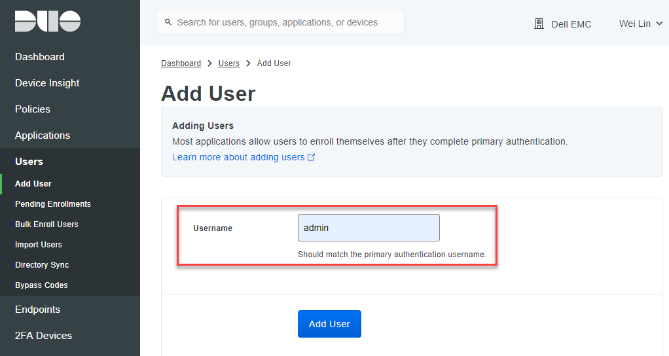
6. Type the user name, as shown in Figure 6.
Figure 6 Manually User Enrollment
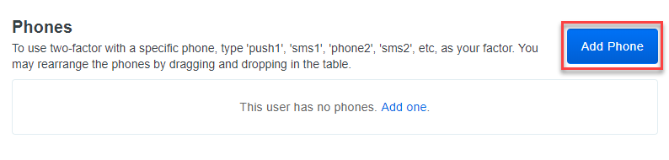
7. Find the Phones settings in the user page and click the Add Phone button to add a device for the user. See Figure 7.
Figure 7 Add Phone for User
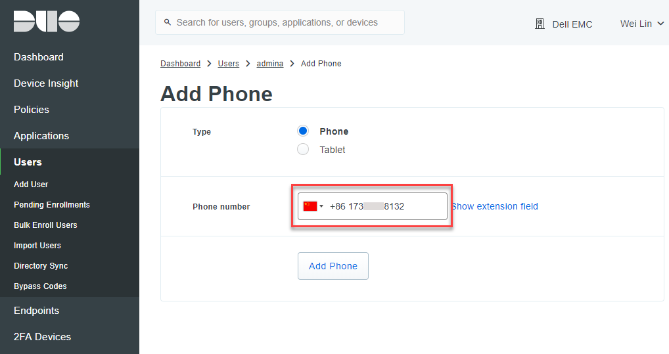
8. Type your phone number.
Figure 8 Add New Phone
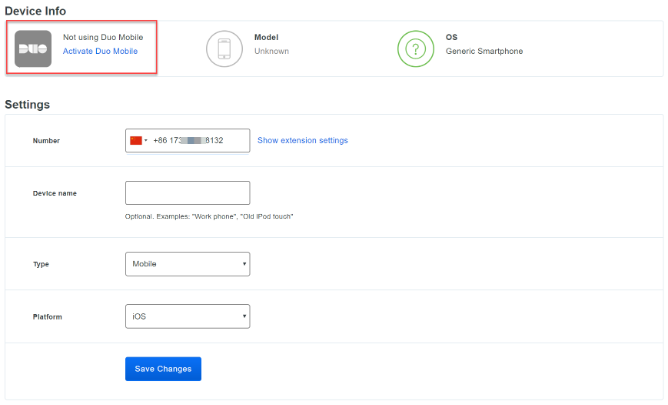
9. (optional) If you want to use Duo push authentication methods, you need to install the Duo Mobile app in the phone and activate the Duo Mobile app. As highlighted in Figure 9, click the link to activate the Duo Mobile app.
Figure 9 Activate the Duo Mobile app
The Duo service is now prepared for OneFS. Now let's go on to configure OneFS.
Configuring and verifying OneFS
1. By default, the authentication setting template is set for “any”. To use OneFS with the Duo service, the authentication setting template must not be set to “any” or “custom”. It should be set to “password”, “publickey”, or “both”. In the following example, we are configuring the setting to “password”, which will use user password and Duo for SSH MFA.
# isi ssh modify --auth-settings-template=password
2. To confirm the authentication method, use the following command:
# isi ssh settings view| grep "Auth Settings Template"
Auth Settings Template: password
3. Configure the required Duo service information and enable it for SSH MFA, as shown here. Use the same information as when we set up the UNIX Application in Duo, including API hostname, integration key, and secret key.
# isi auth duo modify --enabled=true --failmode=safe --host=api-13b1ee8c.duosecurity.com --ikey=DIRHW4IRSC7Q4R1YQ3CQ --set-skey Enter skey: Confirm:
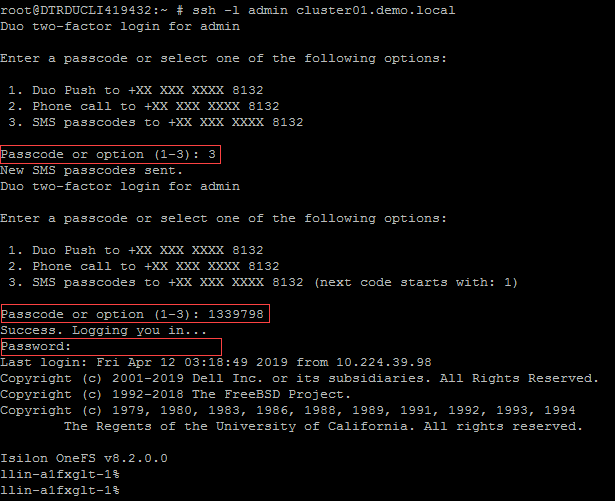
4. Verify SSH MFA using the user “admin”. An SMS passcode and the user’s password are used for authentication in this example, as shown in Figure 10.
Figure 10 SSH MFA Verification
You have now completed the configuration on your Duo service portal and OneFS cluster as well! SSH users have to be authenticated with Duo, therefore, you can further strengthen your OneFS cluster security with MFA enabled.
Author: Lieven Lin