

VDI Data Protection Part 1: Protecting Your VDI Environment - What You Need to Consider
Tue, 11 Jul 2023 18:44:31 -0000
|Read Time: 0 minutes
Virtual Desktop Infrastructure (VDI) plays a crucial role in today's business transformation initiatives. Although there is an increase in SaaS-based and cloud native applications, the majority of the applications in today's enterprises continue to be Microsoft Windows-based applications. VDI is the most efficient way to present these Windows applications to end users in their digital workspaces, and provides a consistent user experience across user devices for the modern-day mobile workforce. Organizations increasingly rely on VDI to provide the agility, security, and centralized management that are so important for their workforce.
According to the Global Data Protection Index survey by Dell EMC, organizations managed an average of 9.7PB of data in 2018 - representing an explosive growth of 569% compared to the 1.45PB managed in 2016. What’s worrying is that the number of businesses unable to recover data after an incident nearly doubled between 2016 and 2018. This information is alarming because incidents such as these can cause substantial monetary losses, reduced employee productivity, and damage to the reputation of the affected organizations. VDI environments are arguably the most critical workload in the corporate data center because they impact user desktops and user data - the primary gateways to user productivity. Any loss or reduced availability of these components will directly impact both user productivity and the business.
For physical desktops and laptops, data protection is often restricted to storing user data on a shared folder somewhere in the organization's network, then protecting that folder. But when it comes to VDI, virtual desktops reside in the data center, and it is the responsibility of IT to not only protect the user-specific data but also to protect the desktop and associated desktop management infrastructure.
The success of a VDI data protection plan depends on these classic data protection parameters:
- Availability -- the percentage of time that a service/application (in this case the VDI environment) is available. Five-nines or 99.999% availability means 5 minutes, 15 seconds or less of downtime in a year.
- Recovery time objective (RTO) -- the elapsed time to when virtual desktops can be available after an incident
- Recovery point objective (RPO) -- the time period (minutes, hours) of acceptable user and configuration data loss from the VDI environment prior to when the incident occurred
For example, a policy might state that we must restore service within 4 hours (RTO) with no more than 1 hour of data loss (RPO). A robust data protection plan is necessary to ensure that availability, RTO, and RPO objectives are met. Such a plan will require the protection of all essential components of the VDI environment to ensure that the plan meets its service level agreement (SLA) to avoid business impact.
As shown in Figure 1 below, a VDI environment typically consists of management infrastructure, desktop infrastructure, and user data components (often a file share or dedicated unstructured data storage platform such as Dell EMC Isilon) where user data is stored. The functions of these layers are summarized below:
- The management layer performs the provisioning, brokering, policy management, and related management functions
- The desktop layer is the user’s desktop, which is often made available to multiple users using an appropriate cloning technology
- The third layer is the user data (stored in user profile shares, home folders, etc.)
A VDI data protection plan should cover all three of these component layers.
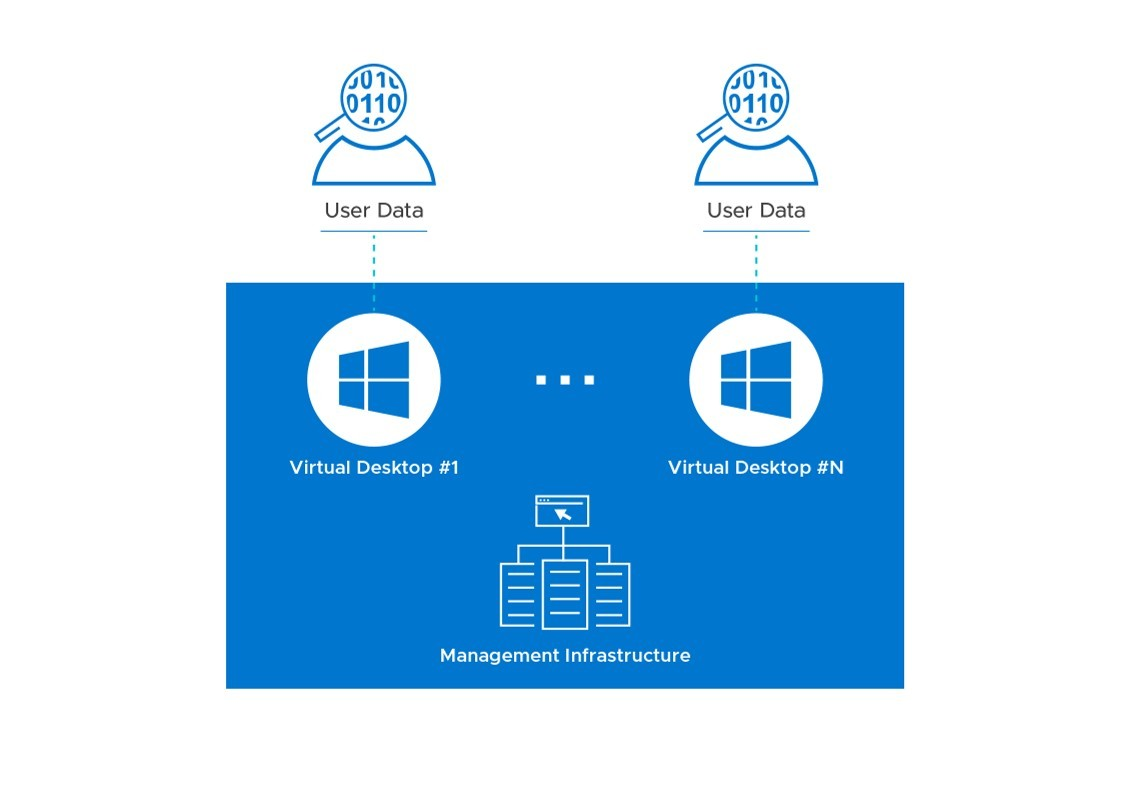
Figure 1: Components of a VDI Environment that Require Protection
The availability and recoverability goals described above will determine the overall design for your VDI infrastructure. The level of redundancy and other factors will vary depending on whether it will be a single-site or multi-site design. The operational backup of data and the disaster recovery plan, two major aspects of data protection, will vary across organizations based on these parameters. Careful consideration needs to be given to these requirements during the design of the VDI infrastructure, to meet the Service Level Agreement (SLA).
In the next installments of this blog series on data protection for VDI, we will discuss in detail how these objectives can be met by describing some of the important considerations for multi-site disaster recovery, single-site protection, and what the future of data protection for VDI environments in a multi-cloud world might look like. The next blog will be a deep-dive on VDI multi-site disaster recovery from a Dell EMC perspective. Stay tuned and we’d love to get your feedback!
Published By

Anand Johnson
Principal Engineer at Dell EMC, Technical Marketing ,Ready Solutions for VDI
Related Blog Posts

VDI Data Protection - Part 4: Summary
Mon, 12 Dec 2022 21:26:48 -0000
|Read Time: 0 minutes
In the previous blog posts in this series (part 1, part 2 and part 3) we discussed the components of data protection, disaster recovery, and operational backup approaches in a VMware Horizon environment. The components that require data protection in a Horizon environment are management infrastructure, desktop infrastructure, and user data components where user profiles, home drives and so on are stored.
Today’s organizations rely heavily on VDI to extend their business-critical applications to digital workspaces, giving users on-demand access from any device, no matter where they are. An outage to the VDI environment can cause a major disruption to business continuity and productivity as users are prevented from accessing the applications. So, a well-formulated DR and backup plan are critical to business continuity and for the success of VDI deployments. You can read more about the components of data protection, DR, and the backup aspects of Horizon data protection in the previous posts in this blog series.
We will conclude this series by exploring the public cloud disaster recovery options that are enabled by Horizon on the Dell Technologies Cloud Platform (DTCP) solution from the Dell Technologies Ready Solutions for VDI team.
VDI Data Protection in a Public Cloud - With DTCP and VMC on AWS
VMware Horizon on DTCP is a true hybrid cloud platform for VDI workloads that easily enables disaster recovery on the public cloud. DTCP is based on Dell EMC VxRail hyper-converged infrastructure running VMWare Cloud Foundation (VCF) delivering consistent infrastructure and operations. DTCP allows you to build standardized VMware Software-Defined Data Center (SDDC) architecture that provides a consistent infrastructure connecting your on-premises and a public cloud. Watch this video to learn more about Horizon on DTCP solution.
With DTCP, you can configure DR for Horizon 7 by having an on-premises active-primary site and a passive-secondary site on VMC on AWS, one of our partner public cloud. VMC on AWS delivers VMware SDDCs as-a-service on the AWS cloud. The consistent infrastructure that is offered by DTCP allows you to leverage the same existing skills to build a Horizon 7 infrastructure on VMC on AWS. By using VMC on AWS as a passive site for DR, you can take advantage of the hourly billing option and the pay-as-you-go benefit.
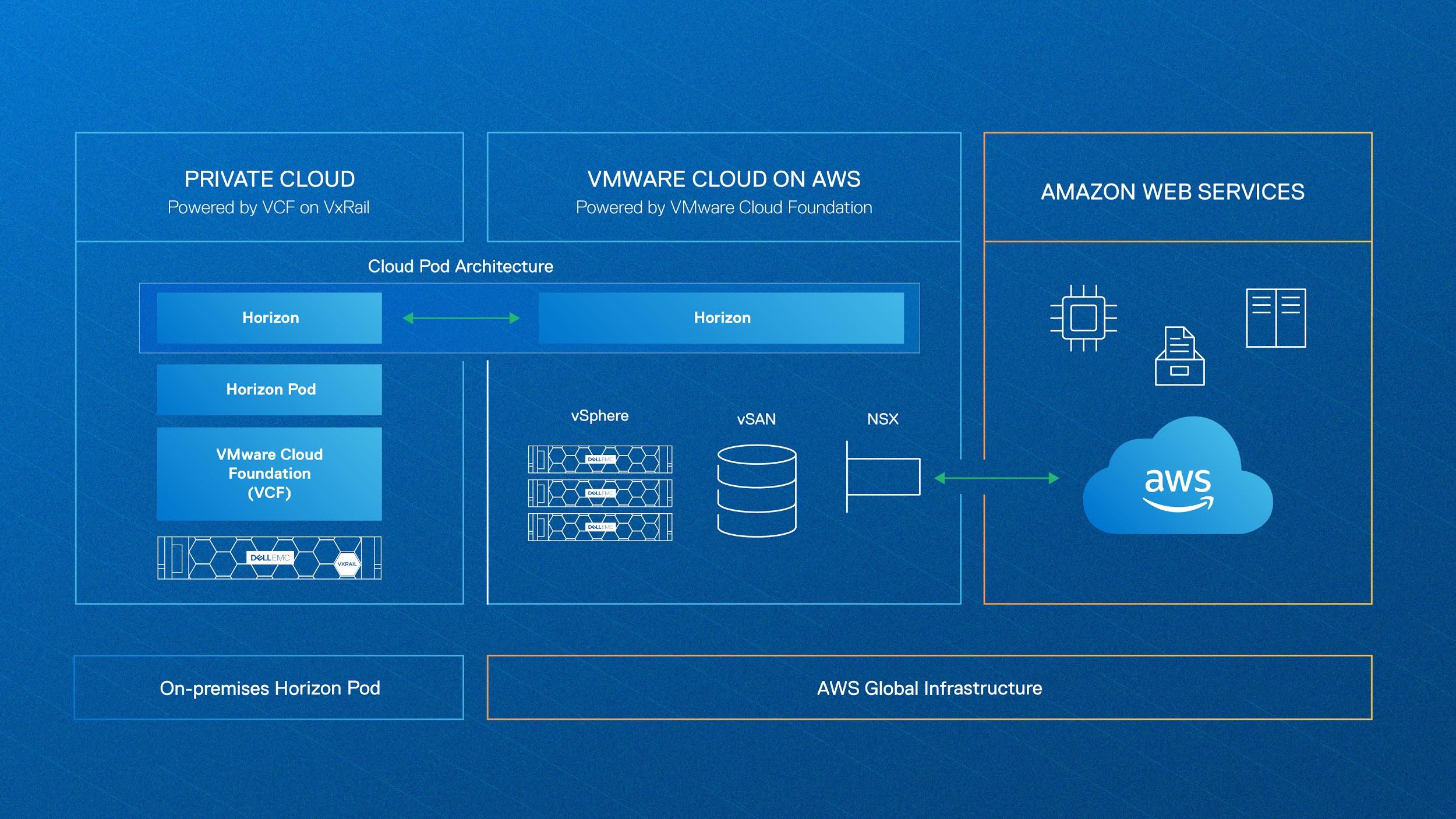
Figure 1: VMware Horizon on DTCP using VMC on AWS as a DR site
VMware Cloud Pod Architecture (CPA) allows you to join multiple pods to form a single Horizon implementation. This pod federation can span multiple sites and data centers, simplifying the administration effort that is required to manage a large-scale Horizon deployment. The CPA architecture also simplifies the DR fail-over process. Read more about CPA and different Horizon DR approaches in part 2 of this data protection blog series.
For a VDI environment based on non-persistent or stateless virtual desktops, you can keep a small host footprint on VMC on AWS, where you will deploy your Horizon 7 instance, store your updated golden images, and create a small pool of VMs. You should also replicate App Volumes, Dynamic Environment Manager settings, user profiles, and other user-related data to maintain consistency across on-premises and VMC on AWS sites. If you have an environment based on persistent or stateful virtual desktops, you must periodically replicate your full-clone desktop from on-premises to VMC on AWS. However, this type of protection is expensive and involves more effort. See this reference architecture guide from the Dell Technologies Ready Solutions for VDI team to learn more about the design considerations and replication options when deploying a Horizon solution based on DTCP and VMC on AWS.
Conclusion
VDI consolidates desktop storage from many devices onto centrally managed infrastructure in the data center. The management of centralized desktops is easier and more secure than distributed physical desktops and it gives more control to administrators. However, an outage to the VDI environment could affect the user’s ability to access business-critical data.
All three component layers (desktop, management, and user data) must be considered when developing a backup strategy for your Horizon environment. The backup approach might vary depending on whether you are using a persistent or non-persistent virtual desktop environment. For multi-site disaster recovery, it is recommended that you use an approach based on Horizon CPA architecture.
The availability and recoverability goals that are defined in the service level agreement (SLA) will determine the overall data protection plan for your VDI infrastructure. The level of redundancy and other factors will vary depending on whether it is a single-site or multi-site design. For the data protection of a Horizon 7 environment, you can choose from the broad range of Dell Technologies data protection products to match your user environment and existing data protection policy. For further information, see the Dell Technologies Data Protection web page.

VDI Data Protection - Part 3: An Operational Backup Approach for Horizon 7
Mon, 12 Dec 2022 21:26:48 -0000
|Read Time: 0 minutes
In Part 1 of this blog series we discussed how disaster recovery and operational backup are two significant aspects of Virtual Desktop Infrastructure (VDI) data protection. In this blog, we will discuss the operational backup aspects of VMware Horizon data protection. For details on disaster recovery, see Part 2.
Loss of VDI environment availability or data has the potential to degrade a user’s ability to perform daily operational tasks. So, it is important for organizations to have an optimal plan to back up and recover VDI data. A robust data protection plan should meet the availability, Recovery Time Objective (RTO), and Recovery Point Objective (RPO) targets defined in Service Level Agreements (SLAs).
For a VMware Horizon virtual desktop environment, three key component layers require protection:
- The desktop layer, that is, the user’s desktop (which is often made available to multiple users using an appropriate provisioning technology)
- The management layer (which performs the provisioning, brokering, policy management, and related management functions)
- The user data layer (stored in user profile shares, home folders, and so on)
The backup and recovery requirements of each component layer depend on the type of the desktop pools and provisioning method used in the Horizon 7 environment. For example, a persistent (stateful) desktop pool can be created with full clones or full virtual machines, which requires a full backup of the virtual machines. A persistent pool can also be created with Horizon instant clones or linked clones with App Volumes (App Stacks and User Writable Volumes) to store the user-installed apps and user-related data. In this scenario, the gold image of the desktop and the persistent data related to App Volumes need protection.
For a non-persistent (stateless) desktop pool, only the gold image of the desktop needs to be protected. In the case of non-persistent desktops, you should consider protecting the user data that is stored in user profile shares and home folders, based on the user environment.
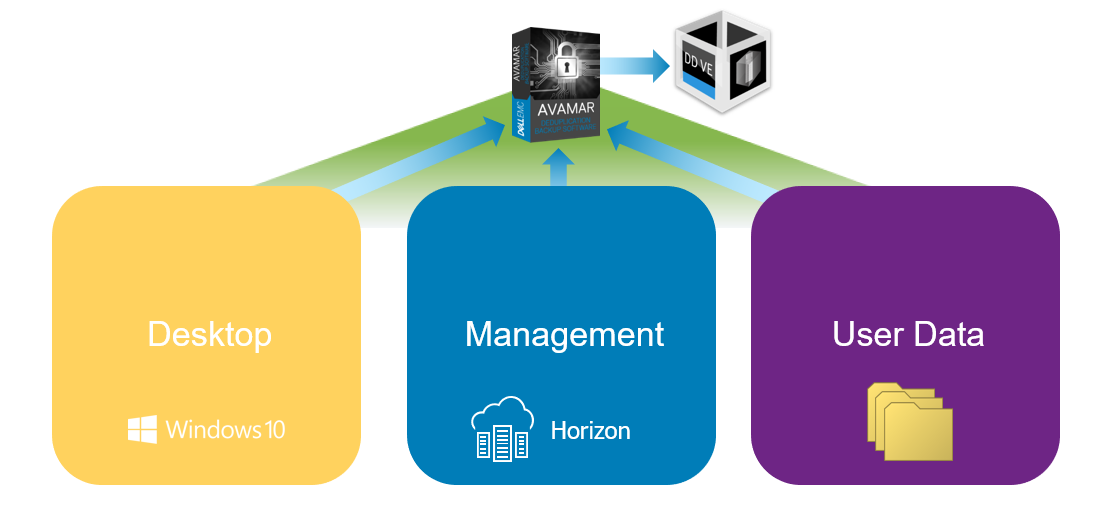
Figure 1: Horizon 7 Operational Backup Approach
Dell EMC offers comprehensive backup and recovery solutions that include products like Integrated Data Protection Appliances (IDPA), Avamar, Data Domain, and Data Protection Suite. For the data protection of a Horizon 7 environment, you can choose from this broad range of Dell EMC data protection products to match your user environment and existing data protection regime. For further information, visit the Dell EMC Data Protection web page.
The Dell EMC Ready Solutions for VDI team has published an operations guide that outlines how Avamar Virtual Edition (AVE) and Data Domain Virtual Edition (DD VE) can be used to facilitate backup and recovery of a Horizon 7, non-persistent desktop pool provisioned by instant clone technology. AVE and DD VE are the software-defined versions of the industry-leading Dell EMC data protection products Avamar and Data Domain. Avamar facilitates fast and efficient backup and recovery for a Horizon environment. Variable-length data deduplication, a key feature of Avamar data protection software, reduces network traffic significantly and provides better storage efficiency. Data Domain provides backup as well as archival capabilities. Data Domain’s tight integration with Avamar delivers added performance and scalability advantages for large Horizon 7 environments. Let’s see some of the key points discussed in the operation guide for backup and recovery of Horizon 7 desktop, management, and user layers.
The Horizon 7 configuration details are in the management layer stored in a View LDAP repository as part of the connection server configurations details. To schedule backups of this database, select the connection server instance from the Horizon console to generate a configuration backup file in a file share. You can then use Avamar VE to back up and restore this configuration backup file. If you are using linked clones, you also need to back up the Composer database.
As discussed earlier in this blog, the backup requirements of the desktop layer depend on the desktop pools and provisioning method. In the case of Horizon instant clones, only the gold image of the respective desktop pools need to be backed up. We recommend taking a clone of the original gold image (containing snapshots) and use that copied cloned image for the backup cycles.
The user data layer contains user-profile shares and other user-related files that are backed up by Avamar software. This layer needs to be protected using a standard data protection approach that is appropriate for user data in any environment.
For a more detailed description of the process to protect each of the layers described above, refer to the operations guide published by the Dell EMC Ready Solutions for VDI team.
The backup and recovery approach for Horizon virtual desktop environments is different from the approach followed for physical desktops and other virtual machines. For developing a successful operational backup strategy for Horizon, the key thing to be aware of is that all three component layers (desktop, management, user data) must be considered. The successful recovery of each of these interdependent components is essential to restore and deliver a fully functional user desktop. To make sure that your backup and recovery plan is effective from a user and business perspective, we recommend that you perform a backup and recovery test for all three layers simultaneously.
In the next part, we will conclude the blog series with some discussion on multi-cloud and hybrid cloud strategies for Horizon 7. So, stay tuned for more!
Thanks for Reading,
Anand Johnson - On Twitter @anandjohns


