

Say No to Costly Ransom Demands with APEX Backup Services
Tue, 14 Jun 2022 15:27:47 -0000
|Read Time: 0 minutes
Ransomware attacks are constantly evolving. Whatever you build today will be obsolete sooner than you might expect because multiple groups are constantly releasing new ransomware packages. You need to be able to evolve with them.
Ransomware is a relentless threat to every enterprise and the attacks are becoming more frequent, advanced, and expensive. Ransomware is a form of malicious software or malware that when downloaded to a computer or server, encrypts victims’ data so that threat actors can demand a “ransom” in exchange for a decryption key needed to unlock your data. Even if the ransom is paid, there is no guarantee that the attacker will provide you with the decryption key.
Ransomware attacks today play out across the entire IT infrastructure, targeting all forms of data and requiring a more robust response. In addition to solutions for preventing attacks, organizations need response and data recovery plans that can quickly bring information back online.
How does ransomware work?
Infection and attack vectors
There are several vectors that ransomware can take to access the target system. One of the most common delivery systems is phishing spam attachments or links that come to the victim in an email. When the victim falls for the phish, the ransomware is downloaded and executed on the target system where ransomware starts encrypting the data.
Encrypt data
When ransomware gains access to the system, it begins to encrypt the files. It encrypts the files with an attacker-controlled key and replaces the original files with the encrypted versions.
Ransom demand
When the file encryption is complete, the victim is presented with a message explaining that the files are now inaccessible and will only be decrypted if the victim sends the requested payment to the attacker through an untraceable medium.
Defensive steps to prevent ransomware
Some of the steps that can be taken to prevent ransomware infection include:
- Ensure that the operating system is patched regularly and up to date
- Install antivirus software that detects malicious programs such as ransomware
- Do not install unauthorized software
- Do not open email attachments automatically or trust email attachments with macros
- And of course, frequently back up important data externally
In today’s diverse and distributed IT environment, restoring your organization’s applications and data quickly in the event of a ransomware attack is a significant challenge. Reliable backup and recovery are a crucial line of defense against ransomware.
Dell Technologies APEX Backup Services ransomware recovery
Dell Technologies APEX Backup Services ransomware recovery is a fast, reliable data recovery solution that eliminates any reason to even think of paying a ransom. APEX Backup Services is based on a secure and robust cloud architecture that can help you protect your business assets, limit the impact of ransomware, and accelerate recovery. Data protected in APEX Backup Services cannot be modified or deleted by ransomware. APEX Backup Services can ensure that your backup data is safe, help you operationalize security across your backup and primary environments, and accelerate the recovery process so you can get back to normal faster.
APEX Backup Services empowers security operations and IT teams to protect, detect, respond, and recover faster from external or internal attacks, ransomware, and accidental or malicious data deletion.
How does APEX Backup Services protect against ransomware?
Zero-trust security and immutable backups
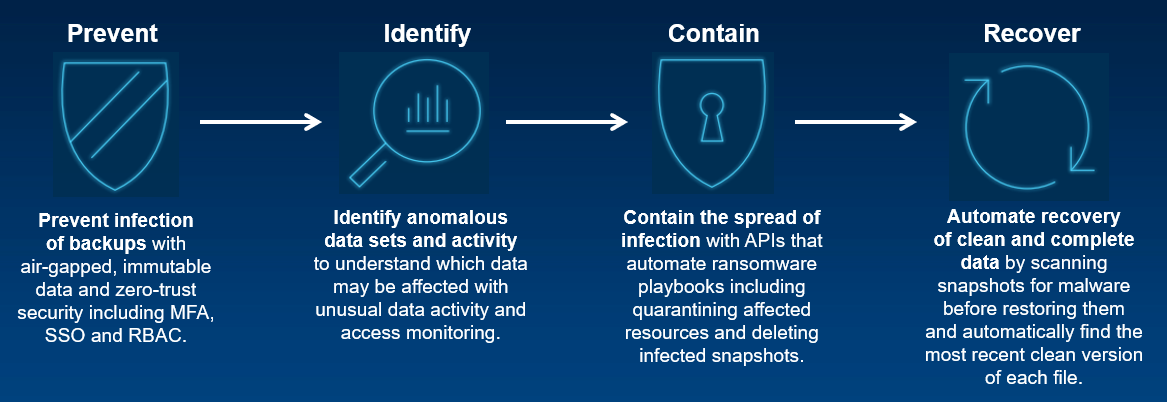
Prevent infection of backups with air-gapped, immutable data and zero-trust security including MFA (multi-factor authentication), single sign-on (SSO) and role-based access control (RBAC).
APEX Backup Services was designed around a zero-trust security architecture and offers rich multi-layered defense features including MFA. Built natively on AWS’s security framework, APEX Backup Services also inherits the global security, compliance, and data residency controls, thus adhering to the highest standards for privacy and data security.
APEX Backup Services provides RBAC. It is strongly recommended to ensure that only a small group of administrators can perform destructive actions such as deleting backup data.
APEX Backup Services offers immutable protection in which backup data is isolated from the customer’s network and protected within the APEX Backup Services platform.
Another key to security is encryption for data, both in flight and at rest. APEX Backup Services provides a secure, multi-tenant environment for customer data. APEX Backup Services encrypts the data using envelope encryption technology, making it impossible for anyone other than the customer to access the data.
Unusual data activity monitoring and user access insights
Identify anomalous data sets and activity to understand which data may be affected with unusual data activity and access monitoring.
Suspicious modification of data on a resource is called Unusual Data Activity (UDA). A user or malicious software can make such changes. The UDA feature with APEX Backup Services provides continuous monitoring of your backup data. With UDA and access monitoring, you can identify anomalous data sets and activity to understand which data might be affected. Our proprietary entropy-based algorithm uses machine learning (ML) to understand norms for your specific backup environment and provides automated alerts for unusual data activity, including bulk deletion and encryption.
APEX Backup Services offers “Security Events”, a dashboard that shows you upfront the count of all administrator login events, data access events, API requests, and unusual data activity alerts, and nudges you to take remedial actions if required. This data helps you gain situational awareness about the backed-up data by gathering events from all APEX Backup Services products.
The APEX Backup Services accelerated ransomware recovery module provides access insights and anomaly detection that help you quickly identify possible ransomware attacks. The APEX Backup Services dashboard provides a single pane of glass where you can see all access attempts and activity across all your data sources. You can use these insights to quickly identify affected snapshots during recovery.
Contain the spread of infection and orchestrate response using API based integrations
Contain the spread of infection with APIs that automate ransomware playbooks, including quarantining affected resources and deleting infected snapshots.
The APEX Backup Services accelerated ransomware recovery enables you to quarantine infected snapshots on the impacted resources, which helps safeguard your system from further infection by barring users or administrators from downloading or restoring data to other resources.
The APEX Backup Services accelerated ransomware recovery module offers robust API integrations that make it easy to fit the solution into your overall security ecosystem. Orchestrating response activities using security information and event management (SIEM) and Security orchestration, automation, and response (SOAR) solutions can dramatically reduce your mean time to respond (MTTR) by automatically completing actions such as quarantining infected systems or snapshots based on a predetermined ransomware playbook.
After you quarantine snapshots, access to the quarantined snapshots is blocked for the administrators and the users of that resource. Administrators and users cannot download data or restore data from the quarantined snapshots.
Automated recovery with curated snapshots
Automate the recovery of clean and complete data by scanning snapshots for malware before restoring them and automatically find the most recent clean version of each file.
The APEX Backup Services cloud platform backs up workloads directly to the cloud, so that they are ready for immediate recovery in the event of a ransomware attack. The accelerated ransomware recovery module enables you to recover with confidence by ensuring the hygiene of recovery data.
You can scan snapshots for malware and IOCs (indicators of compromise) using built-in antivirus detection or using threat intelligence from your own forensic investigations or threat intel feeds. Scanning snapshots before recovery eliminates reinfection.
Accelerated ransomware recovery also solves the problem of data loss due to point-in-time recovery. Flexible recovery options allow you to restore full backups or specific files from a previous point in time. Now you can automatically identify the most recent clean version of every file within a specified timeframe and consolidate those versions into a single “Golden Snapshot”. Eliminating the manual search and recovery process drastically reduces time to recovery and prevents data loss.
The Curated Recovery feature automatically finds the most recent clean version of every file and compiles it into a single curated snapshot. 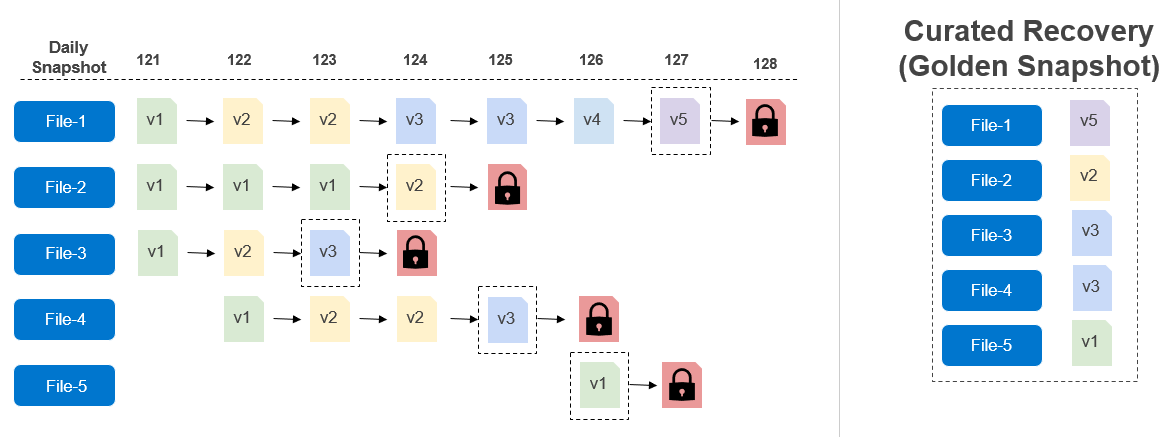
It is unlikely that paying will resolve the problem or allow the victim to recover the encrypted data. It may even make the situation worse, confirming for the hacker that they have found a good target. By selecting the right ransomware recovery solution, you can ensure that your organization has a rock-solid multi-layer defense plan in place to reduce the impact of ransomware or malware.
With APEX Backup Services accelerated ransomware recovery solution, you’ll be far less vulnerable to costly ransom demands and debilitating downtime. The APEX Backup Services cloud-based ransomware protection and accelerated ransomware recovery module prevent data loss, reduce costs, and accelerate ransomware attack response and recovery.
For more details about APEX Backup Services ransomware recovery, visit the dell.com/apex-backup-services website.
Author: Vinod Kumar Kumaresan, Principal Engineering Technologist, Data Protection Division
Related Blog Posts

How Dell Technologies Simplifies Data Protection
Thu, 04 Aug 2022 19:31:34 -0000
|Read Time: 0 minutes
As we are moving to the era of digitalization, more data is vulnerable to corruption, compromise, and loss. As a result, organizations are focusing on data protection strategies to improve security and data integrity. The key principle of data protection is to safeguard and make data available under all circumstances. Dell Technologies offers a variety of data protection products to make sure that data is secure and readily available. In this blog I’ll be covering a few of the outstanding data protection products that Dell provides.
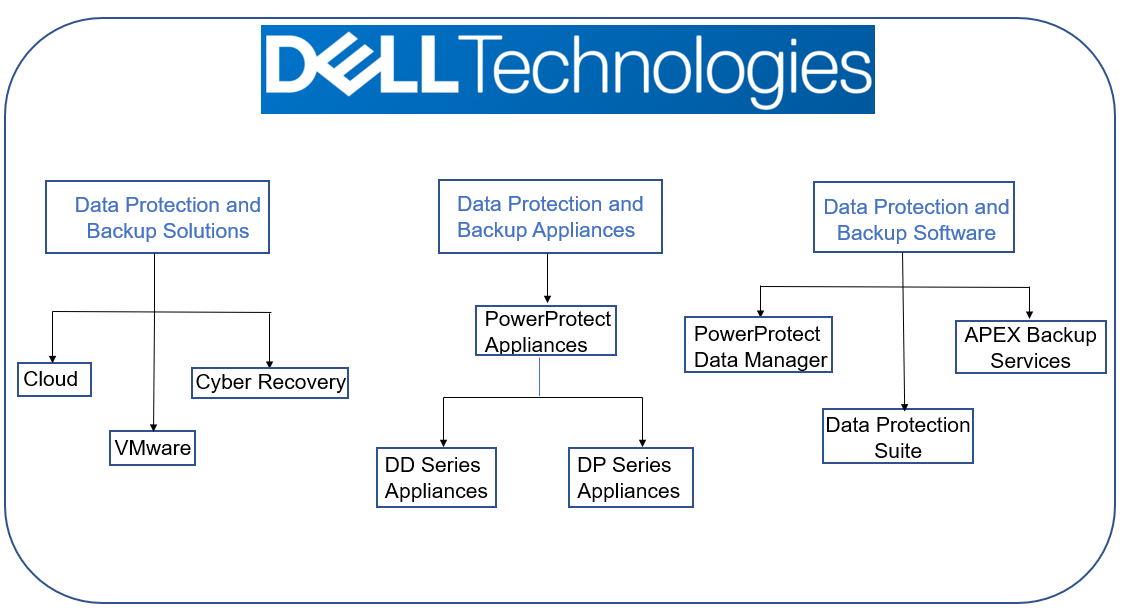
Data protection and backup solutions
Cloud
As organizations are redistributing and extending their data to the cloud or to multiple clouds, protecting that data becomes critical. By implementing a multi-cloud data protection solution, users and developers can avoid cloud vendor lock-in by keeping data independent of the cloud, to reduce worry about high egress charges, migration risk, or time required to move data. Multi-Cloud Data Services for Dell PowerProtect, enabled by Faction, supports a data centric approach for users, allowing them to separate their data and cloud management strategies across public cloud providers. Multi-Cloud Data Services for Dell PowerProtect is a fully managed service that provides a single target for backup and recovery for AWS, Microsoft Azure, Google Cloud, and Oracle Cloud.
VMware
Data protection solutions from Dell Technologies gives customers the power to confidently plan their modern data protection strategies through constant innovation, agile engineering, and tight integration with VMware - all at a lower cost of ownership (TCO). Dell offers protection solutions for VMs, applications, and Kubernetes for a single platform for containerized products and workloads. The solution simplifies deployment and management of VMware workloads on-premises or in one or more public clouds.
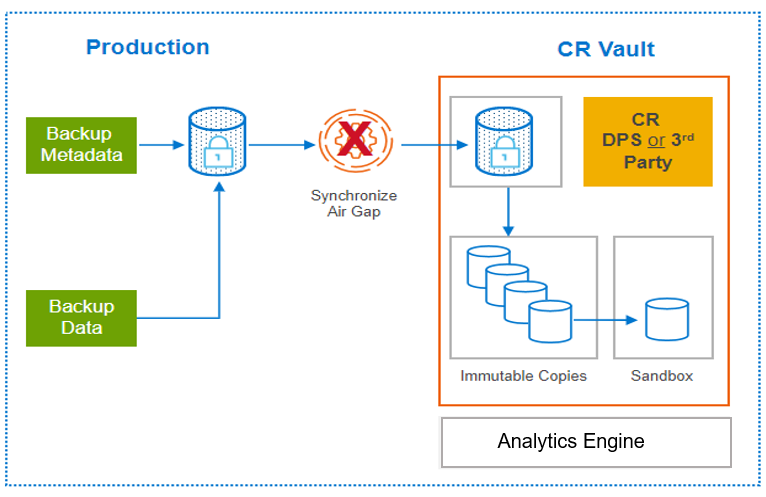
Dell PowerProtect Cyber Recovery
PowerProtect Cyber Recovery provides proven, modern, and intelligent protection to isolate critical data, identify suspicious activity, and accelerate data recovery, allowing you to resume normal business operations with confidence in case of a cyberattack. Critical data is stored immutably in a hardened vault, enabling recovery with assured data availability, integrity, and confidentiality. CyberSense is the analytics engine that is integrated with Cyber Recovery to help find data corruption when an attack penetrates the data center. CyberSense enables confident recovery of good data and offers insight into attack vectors from within the Cyber Recovery vault.
Data protection and backup appliances
Dell PowerProtect DD series appliances
 DD series is our purpose built backup target appliance. The DD operating system (DDOS) provides inline deduplication for data protection and disaster recovery (DR) in the environment. DDOS is the intelligence that powers DD series and PowerProtect systems. It provides the agility, security, and reliability that enables the platform to deliver scalable, high-speed and cloud-enabled protection storage for backup and archive. DD series appliances vary in storage capacity and data throughput. PowerProtect DD Virtual Edition (DDVE) is the software-defined version of the DD series: a virtual deduplication appliance that provides data protection for small-to-medium sized business, enterprise and service provider environments both on-prem and in-cloud.
DD series is our purpose built backup target appliance. The DD operating system (DDOS) provides inline deduplication for data protection and disaster recovery (DR) in the environment. DDOS is the intelligence that powers DD series and PowerProtect systems. It provides the agility, security, and reliability that enables the platform to deliver scalable, high-speed and cloud-enabled protection storage for backup and archive. DD series appliances vary in storage capacity and data throughput. PowerProtect DD Virtual Edition (DDVE) is the software-defined version of the DD series: a virtual deduplication appliance that provides data protection for small-to-medium sized business, enterprise and service provider environments both on-prem and in-cloud.
Dell PowerProtect DP series appliances
DP series is an integrated appliance solution thatprovides complete backup, replication, recovery, deduplication, instant access and restore, search & analytics, seamless VMware integration — plus, cloud readiness with disaster recovery (DR) and long-term retention (LTR) to the cloud — all in a single appliance. With the DP series, customers reduce their time-to-protect and become more agile with a reliable solution that’s fast, protected more efficiently, and can be recovered quickly.
Data protection and backup software
Dell Data Protection Suite
Dell PowerProtect Data Manager
 PowerProtect Data Manager software protects data and delivers governance control for modern cloud workloads across your evolving physical, virtual, and cloud environments. Address ever-changing growth and IT complexity by leveraging Dell software defined data protection platforms. PowerProtect Data Manager delivers next generation data protection that enables faster IT transformation, while giving you the assurance that you can easily safeguard and quickly unlock your data’s value. This software-defined solution includes self-service protection, centralized governance, and SaaS-based reporting and monitoring.
PowerProtect Data Manager software protects data and delivers governance control for modern cloud workloads across your evolving physical, virtual, and cloud environments. Address ever-changing growth and IT complexity by leveraging Dell software defined data protection platforms. PowerProtect Data Manager delivers next generation data protection that enables faster IT transformation, while giving you the assurance that you can easily safeguard and quickly unlock your data’s value. This software-defined solution includes self-service protection, centralized governance, and SaaS-based reporting and monitoring.
Dell Avamar
Avamar is backup and recovery software that provides integrated data deduplication technology. Avamar solves the challenges that are associated with traditional data protection, enabling fast and reliable backup and recovery for remote offices, VMware environments, DD series and Cloud Tier, and data center LANs. Unlike traditional solutions, Avamar reduces the size of backup data at the source—before it transfers across the network and stores to disk. As a result, Avamar delivers fast, efficient daily full backups despite slow or congested infrastructure, and data encryption for added security.
Avamar is available as a virtual edition or as a component of Data Protection Suite, which offers you a complete suite of data protection software options.
Dell NetWorker
NetWorker software provides unified backup and recovery of enterprise applications and databases. With centralized administration, NetWorker helps you take advantage of the data protection that fits your needs best: deduplication, backup to disk and tape, snapshots, replication, and NAS. NetWorker protects both physical and virtual environments including VMware and Microsoft Hyper-V. It provides the same enterprise-level experience, whether you are protecting data and applications within the data center or in the public cloud.
NetWorker is available as virtual edition (NVE) or as a component of the Data Protection Suite, which offers you a complete suite of data protection software options.
Dell Data Protection Advisor
Data Protection Advisor allows you to unify and automate monitoring, alerting, and reporting across your data protection software and storage environments, including on-premises and cloud. Data Protection Advisor enables you to make informed decisions faster, to increase efficiency.
Dell RecoverPoint for Virtual Machines
RecoverPoint for Virtual Machines enables quick recovery of VMware virtual machines to any point in time. RecoverPoint for VMs provides continuous data protection (CDP) for operational recovery and disaster recovery. It is hypervisor-based, software-only data replication that integrates with VMware vCenter.
Dell APEX Backup Services
APEX Backup Services is a cloud-based data protection solution that ensures predictable, controllable costs without increasing complexity. It deploys in minutes and provides unlimited on-demand scaling to ensure that growing data volumes are always protected. An intuitive web-based experience provides centralized visibility and management across workloads and users, to ensure that your data is always protected.
With changing times, data protection solutions provided by Dell have also changed, and for the better. The variety of data protection products provided by Dell Technologies makes sure that data is easy to access, readily available, secured, and uncorrupted.
For more details, see the following resources:
Author: Charu, Engineering Technologist 2

Smart Scale for Dell PowerProtect Appliances, Part III: MSU Migration, Replication, Recoverability, Security
Tue, 18 Jul 2023 15:44:25 -0000
|Read Time: 0 minutes
In the first blog post of this series, we covered what Smart Scale is and why we need it. In the second part of the series, we covered the architecture deep dive of the solution and how to deploy, set up, and configure workflows.
In this part, let’s discuss Smart Scale Mobile Storage Unit (MSU) migration, replication topology, recovery, and security.
Migrating Mobile Storage Units
Migrating a Mobile Storage Unit (MSU) is a new feature that helps to migrate a MSU from one DD series appliance to another. In the following figure, notice that “MSU7” has been migrated to DD series appliance 3 from DD series appliance 2 and the client continues to use the “MSU7” on DD series appliance 3 for backup and recovery operations.
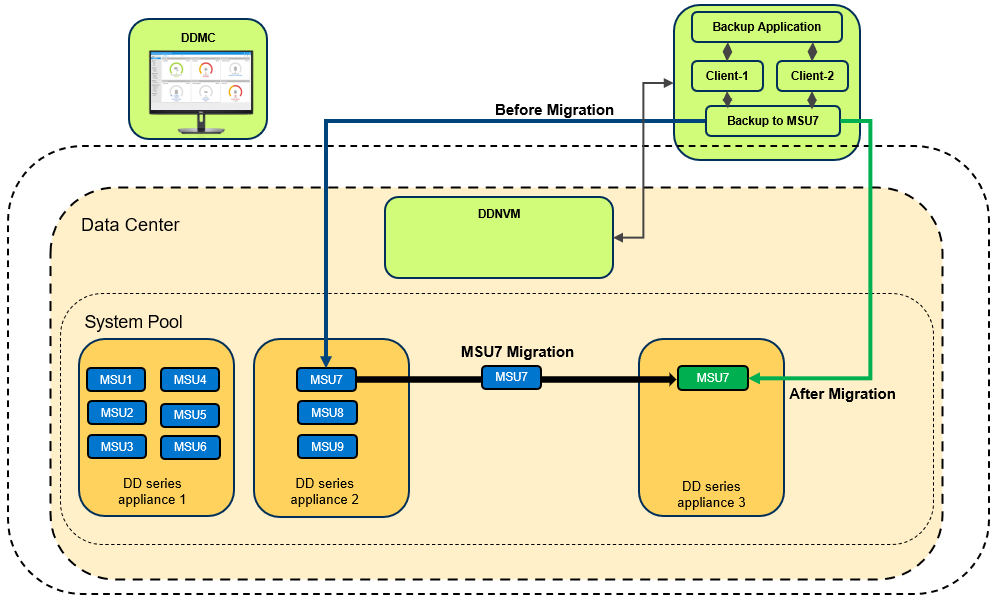
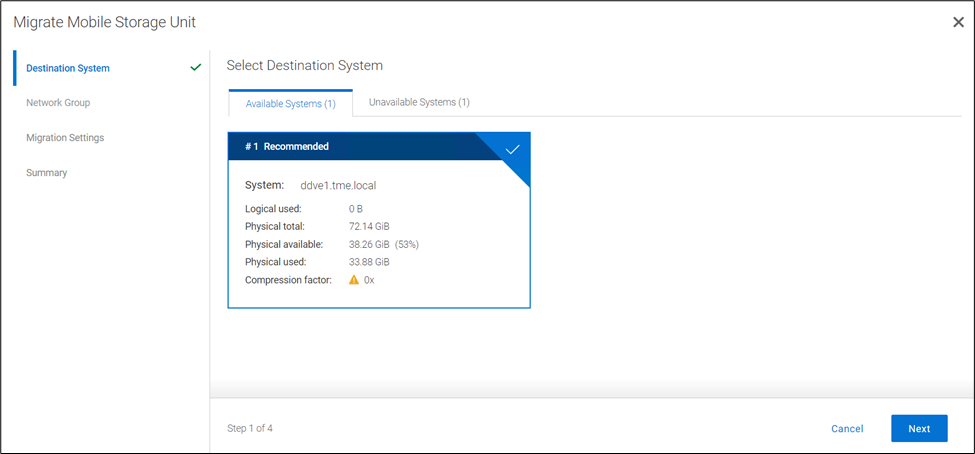
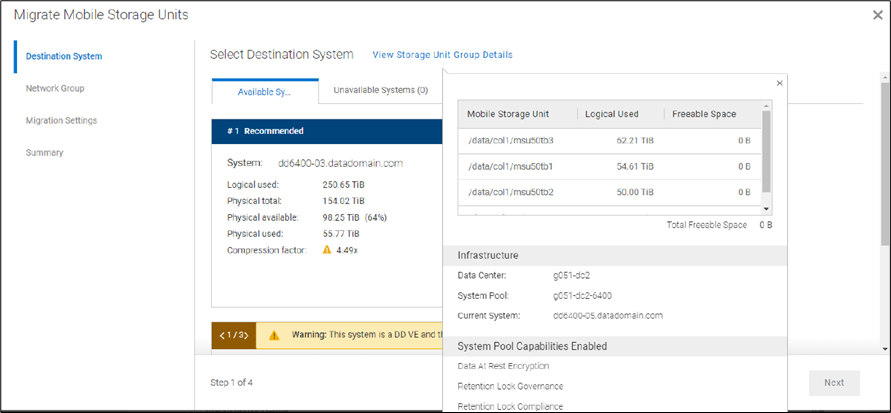
When you initiate the migration, the Migration and Placement Service provides the recommended list of DD series appliances from the available list of DD series appliances in the Data Center. Based on that list, you can select the target system and initiate the migration.
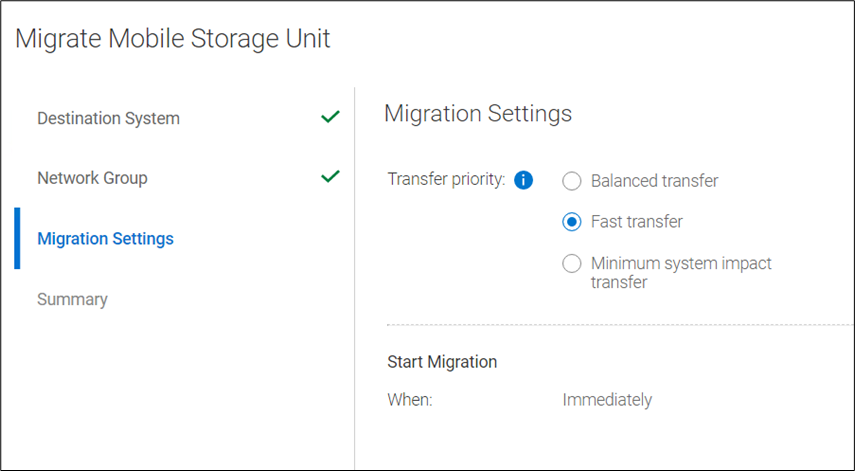
You can select which Network Group to use, and can select from the following migration transfer priorities:
- Balanced Transfer – Balances the resources between the backup and the migration
- Fast Transfer – Uses more resources for migration
- Minimum system impact – Uses fewer resources for the migration
The final step of the migration provides a Review and Commit screen, which includes several migration statistics (such as logical capacity used, physical capacity used and available, and compression factor). Using these analytics, users can optimize appliance and workload lifecycles. When the migration job reaches 100%, it is ready to commit. All the operations (backup or restore) to the source MSU need to be canceled or stopped before committing the migration. There are two options available for the source MSU: you can either mark the MSU to be deleted after a successful migration or you can keep the MSU on the source system. When the commit is done, the remaining data that needs to be synced with the target DDR will be updated. The source MSU is marked as read only; the target MSU is marked as read write. The source MSU is demoted to an Mtree and target system has a new MSU with the same name. The Migration and Placement Service in PowerProtect DD Management Center updates the Namespace Redirection Service Data Manager (NRSDM) about the new location of the MSU. NRSDM then provides that information to the NRS. When a boost client now requests the physical location of the MSU to write the data, NRS provides the target DDR’s IP address. Critically, none of these operations requires reconfiguring the backup software.
Note: Smart Scale is an additional feature of DDMC designed to make administration simple, agile, and flexible. When Smart Scale services are enabled, the customer’s existing environment remains undisturbed. This means that traditional backup operations and storage units co-exist with operations that system pools and mobile storage units support.
MSU affinity group migration
Starting with DDMC version 7.12, migration of a group of MSUs in an affinity group (or a subset of the group) from one DD system to another in a system pool is supported. With MSU affinity group migration, a DDMC administrator can migrate a group of MSUs without having to manually set up multiple migration jobs. There can be up to 32 MTrees in an affinity group.
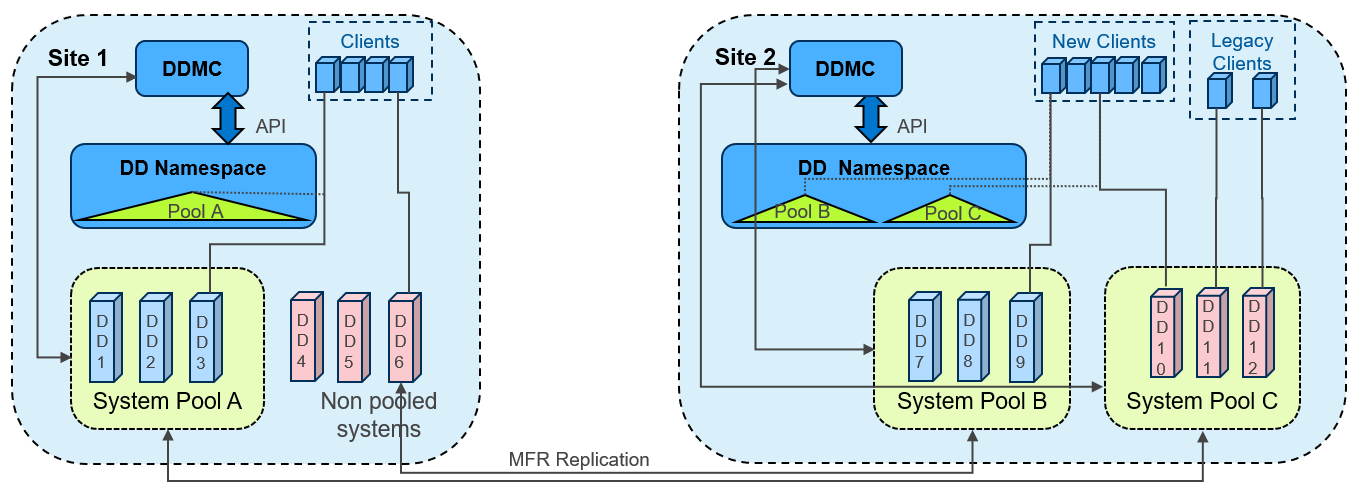
Replicating Mobile Storage Units
DD series appliances provide automated, policy based, network efficient, and encrypted replication for disaster recovery and multi-site backup and archive consolidation. Smart Scale supports Managed File Replication (MFR) on Mobile Storage Units (MSUs) with Dell PowerProtect Data Manager, Dell NetWorker, and Veritas NetBackup. Types of replications supported are:
- Storage Unit to Storage Unit
- MSUs to Storage Unit, and Storage Unit to MSUs
- MSUs to MSUs
Replication is supported between storage units or MSUs that are within the same data center or not, within the same system pool or not, within the same appliance or not, and within the management domain of a single DDMC or across DDMC deployments.
Recoverbility of Smart Scale services
In the era of performance on appliances, what organizations often ignore is the recoverability of the appliance or service when failures occur. Dell recognizes the importance of your SLA and RPO, keeping that in mind we have built Smart Scale architecture so that it provides an automated response to any disaster, by providing options for quick recovery to ensure minimum downtime.
Let’s divide the Smart Scale architecture into two parts: the Management plane which has all the Smart Scale management services, and the Data plane which stores the actual data (that is, the DD series appliance). Now let’s examine the various recovery abilities available in both planes.
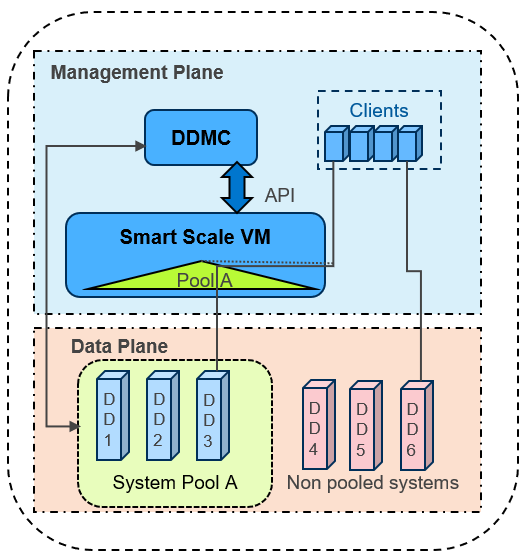
In the management plane
- Smart Scale has intelligent Analytics Services that provide capacity predictions, initial placement, and rebalancing recommendations.
- Micro services in PowerProtect DD Management Center (DDMC) and DD Namespace VM (DDNVM) automatically restart and recover as needed.
- Automated alert notifications are triggered by periodic monitoring of services in DDMC and Namespace VM. In the worst case, DDMC administrators may need to redeploy DDNVM using DDMC (which is quick, by just re-entering the VM credentials).
- The reconciliation service automatically resynchronizes and fixes discrepancies between DDMC and DDNVM.
- DDMC backs up the configuration regularly on a timed basis and whenever administrators make a configuration change.
- DDMC can be recovered with a clean reinstall using configuration backup. If there are no issues in the DDNVM, DDMC can then resynchronize with the running DDNVM, with no need to redeploy DDNVM.
In the data plane
- Data Center services hold a copy of the overall namespace for each pool of DD series appliances, to enable the redirection of backup clients to the appropriate DD series appliance in the pool
- After it is redirected, the backup client connects to the DD series appliance and starts data transfer, then (unless it is restarted) it continues to work even if DDMC or DDNVM have any issues.
- DDMC VM will redeploy DDNVM if necessary
- DDNVM continues working even if DDMC is not available
- Reinstalling DDMC does NOT require reinstalling DDNVM
Security options with Smart Scale services
With the increased rate of cyber-attacks and ransomware threats, it is essential to have services and appliances that have adequate security restrictions for shielding your data from malicious attacks. Smart Scale enables security at every level of the solution. Let’s take a look at the security options available:
Data plane
- D@RE Encryption at rest is supported within Smart Scale. A System Pool may have a mix of encrypted and non-encrypted systems. During migration a warning is given if the selected migration is from encrypted to non-encrypted systems.
- Encryption in flight is supported both for backup/restore and replication, with the same modes of operation as regularly available for PowerProtect appliances.
- MSUs are protected by Mobile Boost Users. These users are migrated between systems automatically as required when MSUs are migrated.
Management plane
- Overall security is applied and managed from DDMC, both in the creation of System Pools and in the creation and mobility of MSUs.
- Certificates are enabled to secure communications between DDMC and DDNVM.
- Most services run as non-root user.
- DDNVM is guest OS enabled, and no customer login is allowed.
Network security
- When creating and enabling MSUs, the supported network groups are selected. Redirection from Pool Access IP to MSUs is restricted only to those network groups enabled for specific MSUs.
- VLANs are supported (but not mandated) using either trunk or access mode (that is, tagging on the node or the network switch) for both appliances and DDNVM.
Smart Scale is about simplifying capacity management across multiple DD series appliances, but it's more than just management and reporting. While it includes analytics, insights, and recommendations around capacity needs and placement, the real value is the system pooling and management it provides. Smart Scale services deliver the next generation of data protection scale, mobility, and insights for PowerProtect DD series appliances.
Thank you for taking a moment to read this series of Smart Scale blog posts. We hope they were useful and helped you to understand the Smart Scale feature comprehensively.
To catch up on the previous Smart Scale blog posts in this series, see:
- Smart Scale for Dell PowerProtect Appliances, Part I: Innovative Technology to Manage Multi-Exabyte Data
- Smart Scale for Dell PowerProtect Appliances, Part II: Architecture Deep Dive
Additional resources for Smart Scale
- Dell PowerProtect DD series appliances
- Smart Scale for PowerProtect Appliances – Technical white paper
- Dell PowerProtect DD Management Center Interactive Demo
Authors:



