

OpenManage Enterprise: Security Built In
Sun, 10 Jul 2022 15:50:17 -0000
|Read Time: 0 minutes
I've heard it said that the two biggest cybersecurity fears that customer security teams have are: everyone who works at the company and everyone who doesn't.
Given this fact, this blog describes the most common security features designed in to open manage enterprise, Dell's on-premise server life cycle management solution.
So let’s review the security built into Dell OpenManage Enterprise (or “OME” for short). OME has many security features to protect data held within the appliance and to guard against unauthorized access and use. The Dell server management team aims to provide best in class, on-premise, one-to-many PowerEdge server management capabilities with OME, and ensures that these can be used while meeting customers security requirements.
In December 2021, Dell Technologies released OpenManage Enterprise 3.8.4 update with a mitigation for Apache Log4j Java vulnerability. This Java Vulnerability was a catalyst for many customers to have a broader security review of many commonly used IT tools and solutions.
Since then, Dell has released OME 3.9 that includes an updated plugin for Dell CloudIQ with the new PowerEdge Cybersecurity feature (see the video Building & Tracking Dell CloudIQ Cyber Security Policies for PowerEdge Servers).
Secure foundations
OpenManage Enterprise “OME” is a systems management appliance that is delivered in a virtual machine format, ready to be deployed. This virtual appliance is based on hardened Security-Enhanced Linux (SELinux) with an internal firewall configured. Policies ensure data protection and managed access to the OME workflows. OME stores all sensitive data encrypted with the OME generated encryption key. All user credentials are stored with a one-way hash and cannot be decrypted. In addition to local user authentication, OME offers authentication by means of AD/LDAP or OpenID Connect. Of course, OME supports only user connections over a TLS v1.2 channel and redirects all HTTP requests to HTTPS to ensure that communications follow a secure channel.
Role and scope access control
OME has Role Based Access Control (RBAC) that clearly defines the user privileges for the three built-in roles—Administrator, Device Manager, and Viewer. Scope-based Access Control (SBAC) is an extension of the RBAC feature that allows an administrator to restrict a Device Manager role to a subset of device groups, called “scope”. For more information about RBAC and SBAC, see Role and scope-based access control in OpenManage Enterprise on the Dell Support site.

Login policies
OME security configuration settings allow customers to restrict incoming connections to the appliance. This can be done by a restricted “allowed” network IP range, so that only certain IP addresses are valid for access. Also, a “lockout” policy can be created, using either username or an IP address to block multiple unauthorized access attempts.
Network interfaces
OpenManage Enterprise enables customers to add multiple network interfaces that allow for the configuration of a more secure management network. For example, applying different firewall rules to the interface can provide a greater level of security for the external-facing network interface.
In addition, OME supports customizing the TCP ports used by core https console access and for the NFS share. IPv6 Protocol, including communications to and from iDRACs, is also supported as an option.
Auditing and logging
Auditing provides a historical view of the users and activity on the system. For example, an audit log is recorded when a group is assigned, access permissions change, or a user role is modified.
These events are written to the OME audit log files and can be exported to CSV file format. In addition, if an administrator enables forwarding to a syslog system and configures an appropriate event rule, OME can forward event message(s) to the syslog server.
To wrap up
This blog has highlighted some of the key methods and features Dell uses to keep OpenManage Enterprise secure, so that customers can use it with confidence.
Resources
To learn more about OME and related topics, see:
- OpenManage Enterprise
- Dell OpenManage Enterprise Security Features Video
- Dell OpenManage Enterprise 3.8.2 Security Configuration Guide
- Dell Response to Apache Log4j Remote Code Execution Vulnerability (CVE-2021-44228)
- Role and scope-based access control in OpenManage Enterprise
Author: Mark Maclean, PowerEdge Technical Marketing Engineering
Related Blog Posts

Sweet 16 ways OpenManage helps customers to maximize their investment in PowerEdge
Wed, 12 Apr 2023 01:27:49 -0000
|Read Time: 0 minutes
As we at Dell announce details of the new wave of PowerEdge servers (details here), we want to highlight 16 examples of how the OpenManage portfolio of systems management software enhances our server range. Like I always say, where there are servers, there are server management requirements.
The OpenManage portfolio exists to save customers of any size time and money, eliminating the necessity of high-touch, manual steps to deliver efficiency. Designed to scale, with integrated security, Dell’s OpenManage strategy is to give customers a choice by using orchestration, automation, and integration, leveraging APIs with open standards.
#1 – Server health monitoring—This is server management 101. However, given the fact that PowerEdge servers are the foundation of the modern data center, this basic element is critical to application and services uptime. OpenManage solutions have many ways to get this information from the agent-free iDRAC directly (GUI/SNMP/SMTP/syslog/API and more) or through the Dell OpenManage Enterprise console, OpenManage mobile, Dell CloudIQ, VMware vCenter integration, Microsoft System Center, and leading third-party management software such as Nagios.
#2 – Remote access to servers—If deep one-to-one control for troubleshooting, deployment, configuration, console access, and so on is needed, then iDRAC is the answer. Dell's unique iDRAC9 offers out-of-band remote server connection, including firmware configuration, full server console remote control through eHTML5 (sometimes called vKMV) GUI, virtual media, and server telemetry. iDRAC agentless architecture offers server monitoring and control from anywhere without the need to install any software. There are many additional features, from basic power on/off control offered through the GUI, CLI, or API to advanced server profile configuration to ensure that servers have the correct firmware configuration settings.
#3 – Server deployment—The time between when a server is racked and powered until it is live (time to value) can be greatly reduced by leveraging the automation integrated into OpenManage. Starting with streamlining one-to-one deployments, the iDRAC features a lifecycle controller that rapidly configures elements such as RAID storage configurations and populate deployments with up-to-date operating system drivers. In addition, iDRAC also features a zero-touch deployment to automatically download a server configuration profile (SCP) and even complete an unattended operating system installation the first time the server powers up on a customer’s network. Beyond one-to-one solutions, OpenManage offers a broad number of deployment solutions, including: OpenManage Enterprise, offering firmware setting configuration and supporting agnostic operating system installation through ISO images; Microsoft System Center integration; and deeper customizable VMware installations through OpenManage Enterprise for VMware vCenter. Finally, for customers using tools such as Ansible, Terraform, or Prometheus, OpenManage supplies integration packs and sample code leveraging Dell's APIs.
#4 – Manage and update firmware—There are multiple methods to update PowerEdge server firmware, depending on needs. Methods range from one-to-one, using iDRAC/Lifecycle Controller, to console-based methods for updating multiple servers. Leveraging large-scale automation, these tools can audit existing servers, compare online catalogs, then download and apply the correct updates quickly and consistently with massive time savings compared to manual methods. One example is the integration into VMware using OpenManage Enterprise for VMware vCenter, which offers cluster-aware updates, updating one cluster node at a time using DSR to keep workloads up and running. Dell supplies Repository Manager to build custom firmware catalogs like the packaged interpretable ISOs that are used by other Dell updating tools where servers are isolated or air gapped. And, of course, Dell supplies an Ansible module offering firmware updates to the DevOps user base.
#5 – Configuration drift detection—OpenManage Enterprise provides compliance features that detect, highlight, and remediate configuration drift issues, with simple processes for both firmware versions and firmware configuration settings.
#6 – Secure supply chain assurance—Using Dell’s Secure Component Verification (SCV) allows organizations to ensure that their new servers are delivered with the same components installed at Dell Technologies’ manufacturing facility, using a digital, cryptographically secured signed inventory certificate.
#7 – Power usage reporting (and carbon emissions calculations)—There are multiple ways to view server power consumption data, depending on needs and preferences. One way is to open the iDRAC web GUI, while another way is to use scripts, either Racadm or Redfish, to retrieve the data. iDRAC can also send data to the OpenManage Enterprise Power Manager plug-in, where power data, including carbon emissions, is processed and grouped, and can be displayed, reported, and actioned. OpenManage Enterprise can also forward this information to CloudIQ for PowerEdge for additional analysis and visualization. For those customers looking for maximum data, iDRAC9 can stream these power statistics as telemetry data to analytics solutions such as Splunk or ELK Stack for real-time in-depth analysis.
#8 – Power usage control—Power consumption capping ability is integrated into iDRAC. OpenManage Enterprise Power Manager adds the capability to apply power caps to individual servers or groups of servers. This power capping can be permanent, scheduled at particular times for specific weekends, or ad hoc in response to an incident when reduction in power consumption is required, such as when running on UPS or on-premises generators.
#9 – Thermal event management—While thermal monitoring alerting and even shutdown is integrated into PowerEdge servers through the iDRAC, OpenManage Enterprise Power Manager augments this through powerful Emergency Power Reduction (EPR) policies. This feature reduces the power consumption of servers through a power cap policy to throttle a group of servers. EPR policies can be used as a permanent or scheduled method to limit server power consumption or as an immediate temporary measure during a thermal emergency, for example, CRAC unit failure.
#10 – Performance monitoring—From the iDRAC GUI, CLI, and API, server performance telemetry data can be obtained. OpenManage Enterprise Power Manager can consume and report this data, automatically highlighting idle servers. Telemetry information can be passed to third-party solutions such as Splunk. Finally, CloudIQ can analyze information and present the information in a dashboard format with graphical visualization, and, for key metrics, highlight anomalies based on historic seasonality data.
#11 – Enterprise secure key management—iDRAC provides a standards-based Key Management Interoperability Protocol (KMIP) to encrypt data at rest on self-encrypting SSDs or self-encrypting hard drives and pass the key to a key management system. Solutions such as Thales CipherTrust Manager offer centralized key management for multiple PowerEdge servers and many other products.
#12 – Detailed server telemetry—iDRAC9 provides more than 180 data metrics that can integrate advanced server hardware operation telemetry. Many of these can be reported and visualized in CloudIQ or streamed to analytics solutions such as Splunk. This server telemetry data allows customers to access detailed information to avoid failure events, optimize server operation, and enhance cyber resiliency.
#13 – Automatic call and ticket creation—This ranges from the Dell services plug-in for OpenManage Enterprise, which offers the creation of a support case directly with Dell without any human intervention, to integration with ServiceNow by Dell’s integration pack. Alternatively, OpenManage Enterprise offers a flexible set of actions, including running scripts, SNMP forwarding Syslog event, and emailing based on the monitoring of SNMP events. This automation can be used to pass information to a third-party solution for incident management.
#14 – Capacity planning—The iDRAC provides a large amount of performance statistics. This data can be collected and analyzed by the Dell CloudIQ IOPS solution to produce a forward-looking capacity analysis on items such as CPU usage based on real historical data values for a given server and workload.
#15 – Cloud-based infrastructure management—Dell's AIOp’s CloudIQ can not only consolidate multiple instances of OpenManage Enterprise, but it can also integrate Dell storage, server, data protection, networking, HCI, and CI products. Hosted in Dell’s secure data center, CloudIQ combines proactive monitoring, machine learning, and predictive analytics to reduce risk, plan ahead, and improve productivity from core to edge.
#16 – Cybersecurity from concept to retirement—Dell Cyber Resilient Architecture 2.0 includes features such as iDRAC silicon-based root of trust, dynamic USB port management, UEFI Secure Boot, and signed firmware updates. All these features are controlled by OpenManage tools that let customers protect, detect, and recover in response to security threats.
We hope that this list has given you a few suggestions on how the OpenManage portfolio can help your organization. Servers are a vital element of organizations’ infrastructure and the foundation of modern business, and it’s critical to manage and monitor them to deliver visibility, productivity, and control. Server management tools not only make tasks easy, faster, and consistent but also decrease failures with increased efficiency. Remember, don't just manage, automate.
Is your organization using all the features that Dell OpenManage offers and getting the maximum benefits from investing in PowerEdge servers? Ask your account manager for more details.
References
#2 Support for Integrated Dell Remote Access Controller 9 (iDRAC9)
#3 How to create and deploy a Server Template in OpenManage Enterprise (video)
#4 Updating Firmware and Drivers on Dell PowerEdge Servers
#5 Improve Operational Efficiency Through OME Server Drift Management
#6 Dell Technologies Secured Component Verification for PowerEdge
#7 #8, #9 Server Power Consumption Reporting and Management
#10 CloudIQ Provides Data Driven Server Management Decisions
#11 OpenManage Secure Enterprise Key Manager Solutions Brief
#12 Transform Datacenter Analytics with iDRAC9 Telemetry Streaming
#13 Support for OpenManage Integration with ServiceNow
#14 Talking CloudIQ: Capacity Monitoring and Planning
#15 CloudIQ: AIOps for Intelligent IT Infrastructure Insights
#16 Cyber Resilient Security in Dell PowerEdge Servers
Additional resources
- Dell server management portfolio: OpenManage microsite
- API catalog (interactive support resource): Dell Technologies Developer
- Ansible Python PowerShell module library and code examples: Dell Technologies GitHub
- Dell systems management offerings: Dell Systems Management Overview Guide

Strengthen the Security Posture of your PowerEdge Servers
Tue, 25 Oct 2022 19:27:27 -0000
|Read Time: 0 minutes
We've heard it said “Give a hacker a 0-day vulnerability, and they will have access for a day; teach a hacker to phish, and they will have access for life.” That made us smile. However, at Dell Technologies we take security very seriously with the mindset that security should be built in, not an add on. In our roles at Dell, we focus on the server management portfolio and we have created a number of tools to help organizations strengthen the security posture of PowerEdge servers.
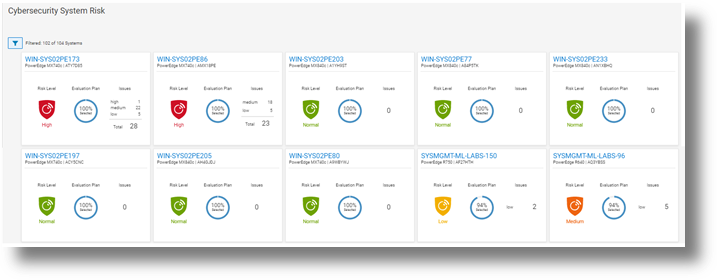
Starting with CloudIQ, our cloud-based AI OPS infrastructure analytics offering, we incorporate a cybersecurity engine that includes a selection of click to enable security policies for PowerEdge servers, based on Dell best practices. We recently published two DfD (direct from development) papers:
- Harden Your Server Cybersecurity With Dell CloudIQ DfD highlights the details of the security policy engine now included in CloudIQ.
- Dell CloudIQ Cybersecurity For PowerEdge: The Benefits Of Automation DfD highlights the time saved using CloudIQ cyber security to police PowerEdge configurations. The results demonstrated that customers can easily create a 15 test policy and apply it to 1000 servers in under three minutes*, as compared to over 98 hours to perform these tasks manually.
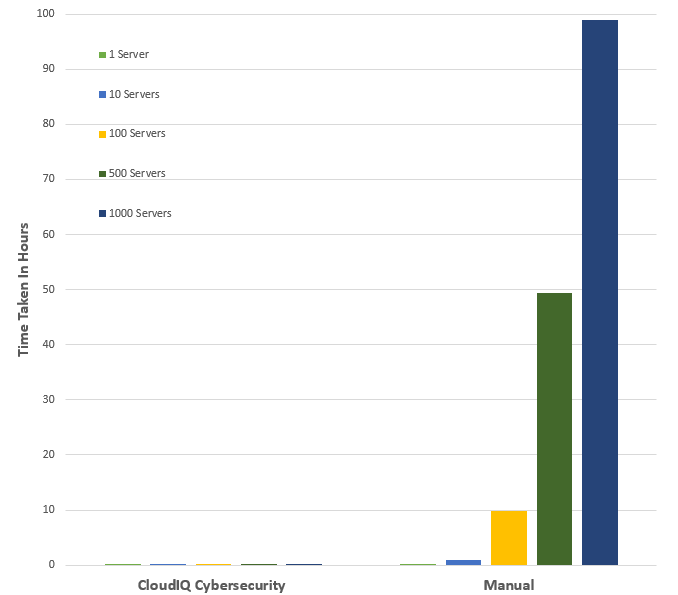
*Projected outcomes based on Dell internal analysis of results of one and ten servers, customer results may vary.
Then looking on premise — OpenManage Enterprise (OME), Dell’s server management solution, scales up to 8000 nodes. OME provides full and rich server configuration drift detection and remediation management of the server configuration profiles accessed from each individual server’s iDRAC. For an overview of that feature, and details about firmware versions and the firmware configuration process, see Improve Operational Efficiency Through OME Server Drift Management.
References
- Dell CloudIQ Cybersecurity For PowerEdge: The Benefits Of Automation (DfD)
- Harden Your Server Cybersecurity With Dell CloudIQ (DfD)
- OpenManage Enterprise: Security Built In (Blog)
Authors: Kim Kinahan and Mark Maclean, PowerEdge Technical Marketing Engineering




