

Q2 2024 Update on Terraform Providers for Dell Infrastructure
Wed, 03 Jul 2024 16:22:05 -0000
|Read Time: 0 minutes
This post covers all the new Terraform resources and data sources that have been released in the last two quarters: Q4’23 and Q1 ‘24. You can check out previous releases of Terraform providers here: Q1-2023, Q2-2023 and Q3-2023. I also covered the first release of PowerScale provider here.
Following is a summary of the Dell Terraform Provider versions released over the last two quarters:
- First beta release of the new provider for Dell APEX Navigator for Multicloud storage! We covered this in full detail in this blog post.
- v1.3 and v1.4 of the provider for PowerScale
- v1.5 of the provider for PowerFlex
- v1.3 of the provider for Redfish
PowerScale provider v1.3 and v1.4
Following are the enhancements to the provider:
Support for OneFS 9.8 (v1.3)
OneFS 9.8 has a plethora of new functionality, including support for APEX File Storage on Azure. You can find a summary of all that is new in the release in this blog post by Nick Trimbee. Starting in v1.3, PowerScale Terraform provider supports OneFS 9.8.
New resource/data source: Roles (v1.3)
PowerScale Roles is part of the role-based-access-control available in Dell PowerScale. Roles in OneFS allow role definitions that are highly granular based on various user privileges. These privileges are named after the isi commands used to perform the actions. Check out this article to delve deeper into how the different privileges are mapped to the ISI commands. Here is an example ISI command to add some write privileges to a role:
isi auth roles modify StorageAdmin --add-group=isilonarrayadmins --add-priv-write=ISI_PRIV_ANTIVIRUS,ISI_PRIV_AUDIT,ISI_PRIV_AUTH,ISI_PRIV_CERTIFICATE
With the new Role resource and data source, you can create and manage OneFS Roles from Terraform. Here is how a resource can be declared:
resource "powerscale_role" "role_test" {
# Required
name = "role_test"
# Optional fields only for creating
zone = "System"
# Optional fields both for creating and updating
description = "role_test_description"
# To add members, the uid/gid is required. Please use user/user_group datasource to look up the uid/gid needed.
members = [
{
id = "UID:10"
},
{
id = "UID:0"
},
{
id = "GID:31"
}
]
# To add privileges, the id is required. Please use role privilege datasource to look up the role privilege id needed.
privileges = [
{
id = "ISI_PRIV_SYS_SUPPORT",
permission = "r"
},
{
id = "ISI_PRIV_SYS_SHUTDOWN",
permission = "r"
}
]
}New resource/data source: User Mapping Rules (v1.3)
OneFS supports mapping users to multiple identity directory service providers like Active Directory (AD) and other providers. For example, a user who authenticates with an Active Directory domain like Desktop\jane automatically receives identities for the corresponding UNIX user account for jane from LDAP or NIS. In the most common scenario, OneFS is connected to two directory services, Active Directory and LDAP. In such a case, the default mapping provides a user with a UID from LDAP and a SID from the default group in Active Directory. The user’s groups come from Active Directory and LDAP, with the LDAP groups added to the list. To pull groups from LDAP, the mapping service queries the memberUid. The user’s home directory, gecos, and shell come from Active Directory.
Here is an example of retrieving the mapped identities of a user across AD and LDAP using the ISI command line tool:
isi auth users view --user=york\\stand --show-groups Name: YORK\stand DN: CN=stand,CN=Users,DC=york,DC=hull,DC=example,DC=com DNS Domain: york.hull.example.com Domain: YORK Provider: lsa-activedirectory-provider:YORK.HULL.EXAMPLE.COM Sam Account Name: stand UID: 4326 SID: S-1-5-21-1195855716-1269722693-1240286574-591111 Primary Group ID : GID:1000000 Name : YORK\york_sh_udg Additional Groups: YORK\sd-york space group YORK\york_sh_udg YORK\sd-york-group YORK\sd-group YORK\domain users
Here is how the Unix LDAP mapping looks:
isi auth user view --user=stand --show-groups Name: stand DN: uid=stand,ou=People,dc=colorado4,dc=hull,dc=example,dc=com DNS Domain: - Domain: LDAP_USERS Provider: lsa-ldap-provider:Unix LDAP Sam Account Name: stand UID: 4326 SID: S-1-22-1-4326 Primary Group ID: GID: 7222 Name: stand Additional Groups: stand sd-group sd-group2
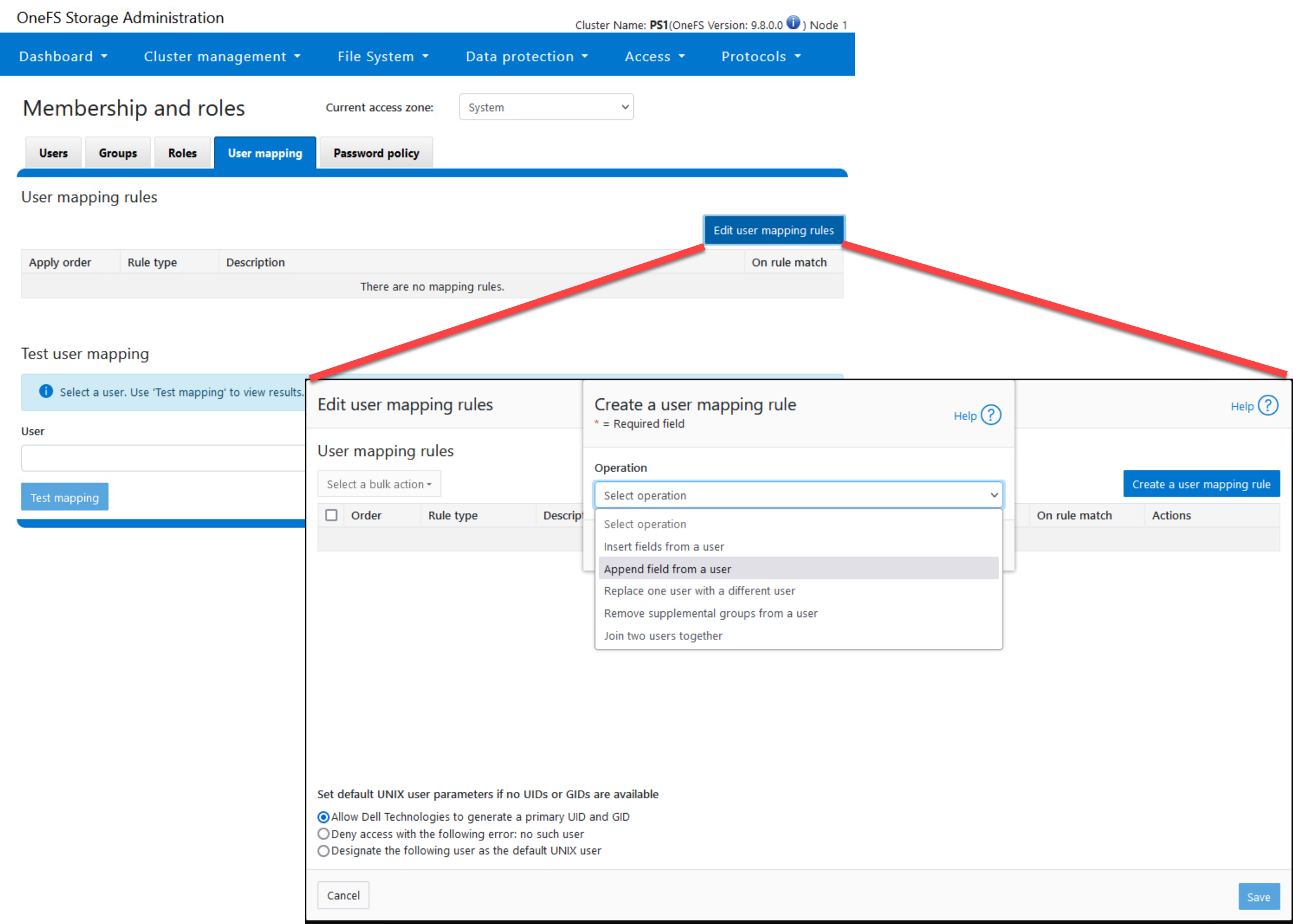
User mapping rules are created by combining operators with user names to create rules that override automatic mapping. Here is where you do this on OneFS Console:
Here is how you can create explicit mapping rules using the Terraform provider:
resource "powerscale_user_mapping_rules" "testUserMappingRules" {
# Optional params for updating.
# The zone to which the user mapping applies. Defaults to System
zone = "System"
# Specifies the parameters for user mapping rules.
parameters = {
# Specifies the default UNIX user information that can be applied if the final credentials do not have valid UID and GID information.
# When default_unix_user is not null: Designate the user as the default UNIX user.
# When default_unix_user is null: Allow Dell Technologies to generate a primary UID and GID.
# When default_unix_user.user is " ": Deny access with the following error: no such user.
default_unix_user = {
# Specifies the domain of the user that is being mapped.
domain = "domain",
# Specifies the name of the user that is being mapped.
user = "username"
}
}
# Specifies the list of user mapping rules.
rules = [
{
# Specifies the operator to make rules on specified users or groups. Acceptable values: append, insert, replace, trim, union.
operator = "append",
# Specifies the mapping options for this user mapping rule.
options = {
# If true, and the rule was applied successfully, stop processing further.
break = true,
# Specifies the default user information that can be applied if the final credentials do not have valid UID and GID information.
default_user = {
# Specifies the domain of the user that is being mapped.
domain = "domain",
# Specifies the name of the user that is being mapped.
user = "Guest"
},
# If true, the primary GID and primary group SID should be copied to the existing credential.
group = true,
# If true, all additional identifiers should be copied to the existing credential.
groups = true,
# If true, the primary UID and primary user SID should be copied to the existing credential.
user = true
},
# Specifies the target user information that the rule can be applied to.
target_user = {
domain = "domain",
user = "testMappingRule"
},
# Specifies the source user information that the rule can be applied from.
source_user = {
domain = "domain",
user = "Guest"
}
},
]
}The “trim” operator-based mapping rule can be specified as follows:
{
# Operator 'trim' only accepts 'break' option and only accepts a single user.
operator = "trim",
options = {
break = true,
},
target_user = {
domain = "domain",
user = "testMappingRule"
}
}The “union” operator-based mapping rule can be specified as follows:
{
# Operator 'union' only accepts 'break' option.
operator = "union",
options = {
break = true,
default_user = {
domain = "domain",
user = "Guest"
},
},
target_user = {
user = "tfaccUserMappungRuleUser"
},
source_user = {
user = "admin"
}
},The “replace” operator-based mapping rule can be specified as:
{
# Operator 'replace' only accepts 'break' option.
operator = "replace",
options = {
break = true,
default_user = {
domain = "domain",
user = "Guest"
},
},
target_user = {
domain = "domain",
user = "tfaccUserMappungRuleUser"
},
source_user = {
domain = "domain",
user = "admin"
}
},New resources to configure NFS global settings zone settings
NFS Global Settings resource can be configured as follows:
resource "powerscale_nfs_global_settings" "example" {
# Optional fields both for creating and updating
# nfsv3_enabled = true
# nfsv3_rdma_enabled = false
# nfsv4_enabled = false
# rpc_maxthreads = 16
# rpc_minthreads = 16
# rquota_enabled = false
# service = true
}NFS Settings for a particular zone can be configured using the nfs_zone_settings:
resource "powerscale_nfs_zone_settings" "example" {
# Required field both for creating and updating
zone = "tfaccAccessZone"
# Optional fields both for creating and updating
# nfsv4_no_names = false
# nfsv4_replace_domain = true
# nfsv4_allow_numeric_ids = true
# nfsv4_domain = "localdomain_tfaccAZ"
# nfsv4_no_domain = false
# nfsv4_no_domain_uids = true
}New resource to configure SMB Server Settings (v1.4)
Following is how this settings resource can be configured:
resource "powerscale_smb_server_settings" "example" {
# Optional fields both for creating and updating
scope = "effective"
# access_based_share_enum = false
# dot_snap_accessible_child = true
# dot_snap_accessible_root = true
# dot_snap_visible_child = false
# dot_snap_visible_root = true
# enable_security_signatures = false
# guest_user = "nobody"
# ignore_eas = false
# onefs_cpu_multiplier = 4
# onefs_num_workers = 0
# reject_unencrypted_access = true
# require_security_signatures = false
# server_side_copy = true
# server_string = "PowerScale Server"
# service = true
# support_multichannel = true
# support_netbios = false
# support_smb2 = true
# support_smb3_encryption = false
}New resource/data source: S3 Bucket (v1.4)
OneFS provides S3-compatible access to data. The new S3_bucket resource is how you create and manage S3 buckets and apply access control permissions to them in OneFS:
resource "powerscale_s3_bucket" "s3_bucket_example" {
# Required attributes and update not supported
name = "s3-bucket-example"
path = "/ifs/s3_bucket_example"
# Optional attributes and update not supported,
# Their default value shows as below if not provided during creation
# create_path = false
# owner = "root"
# zone = "System"
# Optional attributes, can be updated
#
# By default acl is an empty list. To add an acl item, both grantee and permission are required.
# Accepted values for permission are: READ, WRITE, READ_ACP, WRITE_ACP, FULL_CONTROL
# acl = [{
# grantee = {
# name = "root"
# type = "user"
# }
# permission = "FULL_CONTROL"
# }]
#
# By default description is empty
# description = ""
#
# Accepted values for object_acl_policy are: replace, deny.
# The default value would be replace if unset.
# object_acl_policy = "replace"
}New resource/data source: Namespace ACL Management
OneFS provides a single namespace for multiprotocol access and has its own internal ACL (Access Control Lists) representation to perform access control. The internal ACL is presented as protocol-specific views of permissions so that NFS exports display POSIX mode bits for NFSv3 and show ACL for NFSv4 and SMB.
You can use the Namespace ACL to create and manage ACLs for a given namespace:
resource "powerscale_namespace_acl" "example_namespace_acl" {
# Required and immutable once set
namespace = "ifs/example"
# # Optional query parameters
# nsaccess = true
#
# # Optional fields both for creating and updating
# # For owner and group, please provide either the UID/GID or the name+type
# owner = {
# id = "UID:0"
# }
# group = {
# name = "Isilon Users",
# type = "group"
# }
#
# # acl_custom is required for updating. It can be set to [] to remove all acl.
# # While creating, if owner or group is provided, acl_custom must be specified as well. If none of
# # the three parameters are provided, Terraform will load the settings from the array directly.
# # For trustee, please provide either the UID/GID or the name+type
# # Please notice, the field acl_custom is the raw configuration, PowerScale will identify and calculate the accessrights
# # and inherit_flags provided and return its effective settings, which will be represented in the field acl in state.
# acl_custom = [
# {
# accessrights = ["dir_gen_all"]
# accesstype = "allow"
# inherit_flags = ["container_inherit"]
# trustee = {
# id = "UID:0"
# }
# },
# {
# accessrights = ["dir_gen_write", "dir_gen_read", "dir_gen_execute", "std_read_dac"]
# accesstype = "allow"
# inherit_flags = ["container_inherit"]
# trustee = {
# name = "Isilon Users",
# type = "group"
# }
# },
# ]
}PowerFlex Provider v1.5
Following are the enhancements to the provider:
- Support for PowerFlex 4.6
- Support for the provider on AWS
- Support for Restricted Mode
- Support for comma separated values in all possible fields of CSV
- Resource 'powerflex_service' renamed to 'powerflex_resource_group'
Support for SDC deployment for Windows and ESXi OS
SDC Host Configuration for an ESXi host looks as follows with the os_family attribute set to “esxi”:
resource "powerflex_sdc_host" "sdc" {
ip = "10.10.10.10"
remote = {
user = "root"
# we are not using password auth here, but it can be used as well
# password = "W0uldntUWannaKn0w!"
private_key = data.local_sensitive_file.ssh_key.content_base64
host_key = data.local_sensitive_file.host_key.content_base64
}
os_family = "esxi"
esxi = {
guid = random_uuid.sdc_guid.result
drv_cfg_path = "/root/terraform-provider-powerflex/drv_cfg-3.6.500.106-esx7.x"
}
name = "sdc-esxi"
package_path = "/root/terraform-provider-powerflex/sdc-3.6.500.106-esx7.x.zip"
mdm_ips = ["10.10.10.5", "10.10.10.6"]
}SDC Host Configuration for a Linux host looks as follows with the os_family attribute set to “linux”:
resource powerflex_sdc_host sdc {
depends_on = [ terraform_data.ubuntu_scini ]
ip = "10.225.110.40"
remote = { user = "root”
private_key = data.local_sensitive_file.ssh_key.content_base64
certificate = data.local_sensitive_file.ssh_cert.content_base64
}
os_family = "linux"
name = "sdc-linux2"
package_path = terraform_data.sdc_pkg.output.local_pkg
mdm_ips = ["10.247.100.214", "10.247.66.67"]
}SDC Host Configuration for a Windows host looks as follows with the os_family attribute set to “windows”:
resource "powerflex_sdc_host" "sdc_windows" {
ip = "10.10.10.10"
remote = {
user = "username"
password = "password"
port = 5985
}
os_family = "windows"
name = "sdc-windows"
package_path = "/root/terraform-provider-powerflex/EMC-ScaleIO-sdc-3.6-200.105.msi"
# mdm_ips = ["10.10.10.5", "10.10.10.6"] # Optional
}Redfish Provider v1.3
Following are the enhancements to the provider:
Server configuration profile support
When onboarding a new server or repurposing an existing, the systems admin looks for a standard configuration profile that can be applied to the server before deploying workloads on it. Server configuration profiles can be exported from a machine to a remote location and can be imported from a remote location to a local server. Here is the resource to export a profile:
resource "redfish_idrac_server_configuration_profile_export" "share_type_local" {
for_each = var.rack1
redfish_server {
user = each.value.user
password = each.value.password
endpoint = each.value.endpoint
ssl_insecure = each.value.ssl_insecure
}
share_parameters = {
filename = "demo_local.xml"
target = ["NIC"]
share_type = "LOCAL"
}
lifecycle {
replace_triggered_by = [terraform_data.trigger_by_timestamp]
}
}iDRAC supports multiple export types. Following are the variants for the share parameters of the resource for NFS, CIFS, HTTPS, and HTTP cases:
share_parameters = {
filename = "demo_nfs.xml"
target = ["NIC"]
share_type = "NFS"
ip_address = "10.0.0.01"
share_name = "/dell/terraform-idrac-nfs"
}share_parameters = {
filename = "demo_cifs.xml"
target = ["NIC"]
share_type = "CIFS"
ip_address = "10.0.0.02"
share_name = "/dell/terraform-idrac-nfs"
username = var.cifs_username
password = var.cifs_password
}share_parameters = {
filename = "demo_https.xml"
target = ["NIC"]
share_type = "HTTPS"
ip_address = "10.0.0.03"
port_number = 443
}share_parameters = {
filename = "demo_http.xml"
target = ["NIC"]
share_type = "HTTP"
ip_address = "10.0.0.04"
port_number = 80
proxy_support = true
proxy_server = "10.0.0.05"
proxy_port = 5000
}The import resource is almost identical to the export resource. You can find a more detailed note on these new resources here.
User Account Password resource enhancements
Here is how the new resource can be used to change user passwords:
resource "redfish_user_account_password" "root" {
username = "root"
endpoint = "https://my-server-1.myawesomecompany.org"
ssl_insecure = false
old_password = "Test@1234"
new_password = "Root@1234"
}Resources
Here are the link sets for key resources for each of the Dell Terraform providers:
Provider for PowerScale
Provider for PowerFlex
Provider for PowerStore
Provider for Redfish
Provider for APEX Navigator
Author: Parasar Kodati, Engineering Technologist, Dell ISG



