

Port Isolation to the Rescue at the Edge
Tue, 26 Sep 2023 15:35:00 -0000
|Read Time: 0 minutes
IT to Operation Technology (OT) convergence is in full swing in many vertical markets and understanding the differences in each expertise from the personas who make purchasing and architectural decisions is crucial when enterprises are planning their IT and OT investments.
Many IT professionals practice port isolation in networking, which is considered a critical skill and is a well-known way of protecting applications, virtual machines, and containers and providing secure separation. Common practices include DMZs, VLANs, layer 7, or traditional firewalls. Virtualization can bring an additional layer of memory protection in these cases.
IT network port isolation is all around the isolation of networked resources. In researching port isolation, most of the results will solely focus on the IT administrators trying to isolate these ports in their network environment. Addressing applications over TCP or IP ports and implementing port isolation to protect them from network attacks, spoofing, or other methods are good practices for defending against these threats.
In OT and industrial control systems (ICS), port isolation is a crucially different task and is classified as electrical overstress (EOS) protection.
In edge and industrial environments, it is expected that devices will run continuously regardless of the interference they encounter. Therefore, ensuring resilience against electric static discharge (ESD), electric fast transients (EFT), and Lightning strikes (Surges) is crucial. Achieving good electromagnetic compatibility (EMC) for these systems can be challenging.
Port isolation is a way to protect devices from environmental electrostatic interferences in serial, industrial networking, or CAN. Many Edge devices are exposed to greater interferences due to their deployment in locations that do not provide exhaustive protection. Metal cabinets give Ingress Protection (IP) which is an international standard (IEC 60529) for the degree of protection and resistance to dust and moisture. IP protection does not protect against the EOS. The wires that communicate with the engines, sensors, conveyor belts, and pumps are often outside and fully exposed to the surroundings. These wires are all routed into the same compute endpoint and the length of these wires amplifies the exposure to EMC interference.
Helping customers that have experienced incidents that had catastrophic failures, and, sometimes, even epidemic failures can be time-consuming and costly. Often these happen not because of the lack of quality of the devices, but mainly using them outside of the validated and appropriate work areas. Special attention is needed during the purchase, architecture, and assembly of hardware components before they are rolled out into Edge environments.
Electrical components that are inside these Edge devices are vulnerable to these failures; CMOS ICs (chips), and integrated circuits built with MOSFETs. Examples: computer CPUs, graphics ICs, and computer cards.
ESD
Many people have experienced static electricity or "shocks" called electrostatic discharge (ESD) when touching a metal after walking across a carpeted floor or getting from a turning office chair and then shaking someone’s hand. However, static electricity and ESD have created serious industrial problems for centuries. In the early 15th century military forts were using grounding devices to prevent ESD —Electrostatic discharge is known for causing damage to sensitive electronics. This damage can occur in several different ways depending on the potency of the ESD and the type of electronics you are working with.
- Shorting—ESD can cause shorting by connecting two parts of a circuit that shouldn’t be connected. This will usually only occur if the electronics are powered up when the ESD hits them, and it may not cause permanent damage.
- Over-powered components—Many small electrical components have specific power ratings. Potentially coming in at thousands of volts, ESD can over-power the components inside your electronics and damage them from the inside out.
- Heat damage—ESD can create a significant amount of heat rapidly, and this has the potential to cause physical damage to the components inside your electronics.
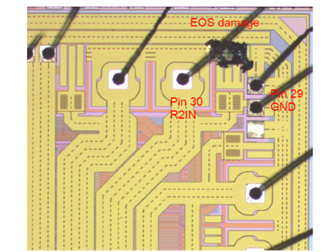
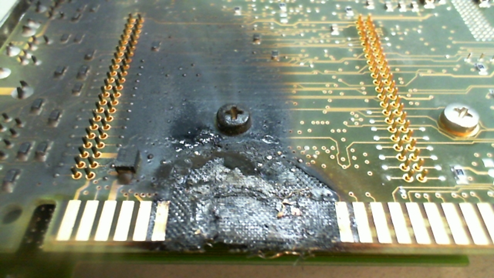
EOS damage
EOS damage can be degrading over time and components that have been exposed to EOS damage can work for some time in the field. Over time when components age and get damaged they will come to a point where they cannot do their work anymore.
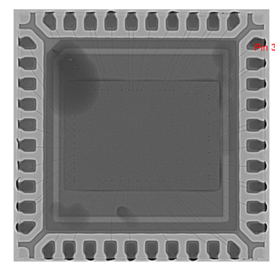
The following figures show almost unnoticeable damage for the naked eye, but it will result in component failure over time.
EFT
Cables near motors can pick up high-voltage and high-frequency electrical fast transients (EFTs). The longer the cables the bigger of an antenna they form, making it easier for electronics to pick this up, and this can have the same effect on electronics and damage them. If these communication lines such as RS-485 use a different signal, they still can be vulnerable to these transients.
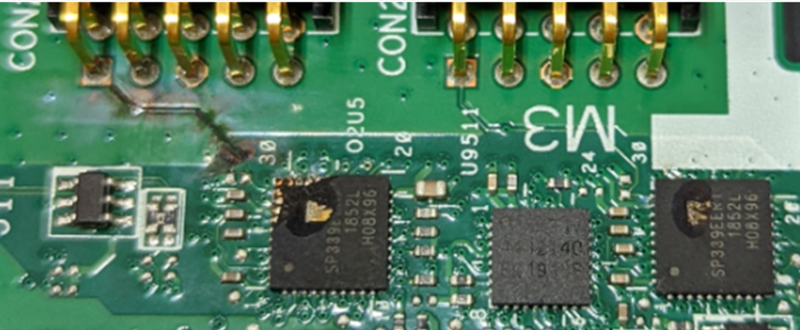
The following figures are examples of components being exposed to EFT and visible in this case. Both serial ports in this example have been exposed to high voltages resulting in even the tops of the components being blown away.
Surge
Things like lightning can cause serious damage to equipment. When lightning strikes, the energy can expose equipment to high energy, especially if the devices are in areas that are vulnerable to these incidents, without protection. For example, telco base stations could be due to the height of the poles being vulnerable to these exposures.
The following figure shows that the transformer has not been sufficient to protect against the surge that was exposed to this Ethernet port.
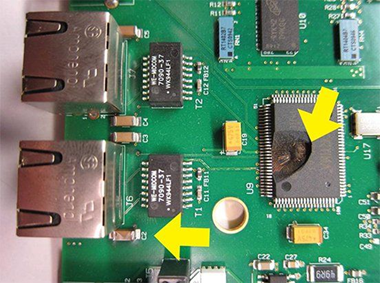
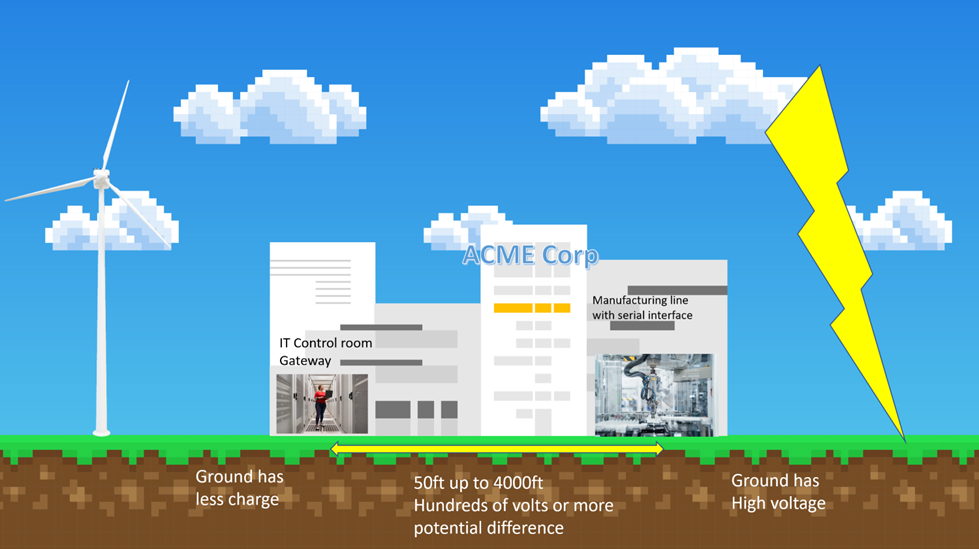
 This effect can be increased if the location of the sensors and the computing equipment are in locations with different ground potentials. During a lightning strike, one location can be charged differently causing heavy current flow through the serial lines, which can cause surges.
This effect can be increased if the location of the sensors and the computing equipment are in locations with different ground potentials. During a lightning strike, one location can be charged differently causing heavy current flow through the serial lines, which can cause surges.
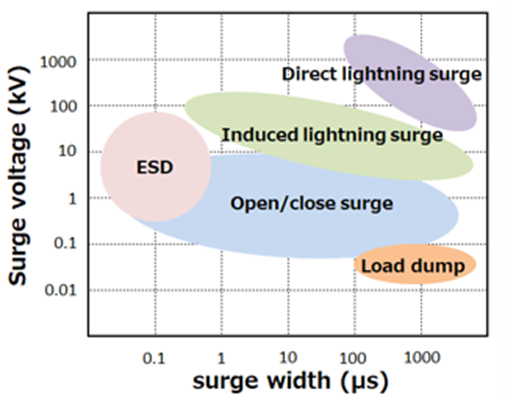
Severity
Equipment has been validated to withstand a significant amount of EOS, especially our industrialized products which are designed to meet these rugged environments, but the amount of degradation that will occur in these industrial environments can vary, and the following figure indicates a scope of what can be expected in the environments. The following figure explains EOS severity; and surge voltage against the duration of EOS.
Preventive measures against ESD
The environment where the devices are being handled can be a cause of failure and requires different measures to prevent devices from being introduced to ESD. Safe working environments typically have ESD safe flooring and ESD safe workbenches where strap bands are used to handle sensitive equipment.

Hipot testing
High Potential (Hipot) testing or insulation resistance testing method that assures sufficient dielectric withstand is used to determine whether the ground wall can handle an over-voltage situation. An over-voltage situation is a voltage higher than the peak operating voltage of a device under test.
Preventive measures against EOS in Dell Edge Gateways
By introducing isolation components into the design and replacing traditional serial, CAN, or network ports with isolated options, the potential damage caused by surges can be reduced. Designs against the different threats can significantly reduce the damage caused to the devices and assure device uptime.
To reduce the risk and exposure to EOS, the Dell Edge Gateway 5200 and Dell Edge Gateway 3200 can be equipped with special addon. The two gateways can be purchased to introduce isolation protection. This will replace the non-isolated legacy ports and introduce protection towards endpoints that have potentially greater exposure to EOS.
SKU | SKU external description | Isolation protection |
492-BDFK | EGW-3200 isolated Canbus (EMUC-B202) | Complies with EN61000-4-5 2.5 kV Surge protection. Complies with IEC 60950-1:2005 + A1: 2009 + A2:2013 2.5kV HiPOT protection. Complies with EN61000-4-2 (ESD) Air-15 kV, Contact-8 kV. |
555-BIDQ + 492-BDFX | EGW-3200 isolated PoE Out Module (EMPL-G2P1) + EGW32/52 60 W AC Adapter (excluding power cord) | Complies with EN61000-4-2 (ESD) Air-15 kV, Contact- 8 kV. |
492-BDHQ | EGW-3200 isolated RS-422 & RS-485 Module (EMP2-X4S2) | Supports port-to-computer isolation, complies with IEC 60950-1:2005 + A1: 2009 + A2:2013 2.5 kV HiPOT protection. Complies with EN61000-4-2 (ESD) Air-15 kV, Contact-8 kV. |
492-BDHR | EGW-3200 isolated RS-232 Module (EMP2-X2S1) | Support port-to-computer isolation. Complies with IEC 60950-1:2005 + A1: 2009 + A2:2013 2.5 kV HiPOT protection. Complies with EN61000-4-2 (ESD) Air-15 kV, Contact-8 kV. |
492-BDFM | EGW-3200 isolated Gigabit Ethernet (EMPL-G201) | Complies with EN61000-4-5 1kV Surge protection. Complies with IEC 60950-1:2005 + A1: 2009 + A2:2013 2 kV HiPOT protection. Complies with EN61000-4-2 (ESD) Air-15kV, Contact-8 kV. |
SKU | SKU external description | Isolation protection |
492-BDGW | EGW-5200 isolated Canbus (EMUC-B202) | Complies with EN61000-4-5 2.5 kV Surge protection. Complies with IEC 60950-1:2005 + A1: 2009 + A2:2013 2.5 kV HiPOT protection. Complies with EN61000-4-2 (ESD) Air-15 kV, Contact-8 kV. |
492-BDFN+ 492-BDFX | EGW-5200 isolated PoE Out module (EMPL-G2P1) + EGW32/52 60 W AC adapter (excluding power cord) | Complies with EN61000-4-2 (ESD) Air-15 kV, Contact- 8 kV. |
492-BDGU | EGW5200 isolated RS-422 & RS-485 module (EMP2-X4S2) | Supports port-to-computer isolation, complies with IEC 60950-1:2005 + A1: 2009 + A2:2013 2.5 kV HiPOT protection. Complies with EN61000-4-2 (ESD) Air-15 kV, Contact-8 kV. |
492-BDFL | EGW-5200 isolated RS-232 module (EMP2-X2S1) | Support port-to-computer isolation. Complies with IEC 60950-1:2005 + A1: 2009 + A2:2013 2.5 kV HiPOT protection. Complies with EN61000-4-2 (ESD) Air-15 kV, Contact-8 kV. |
492-BDGX | EGW-5200 isolated Gigabit Ethernet (EMPL-G201) | Complies with EN61000-4-5-1 kV Surge protection. Complies with IEC 60950-1:2005 + A1: 2009 + A2:2013 2kV HiPOT protection. Complies with EN61000-4-2 (ESD) Air-15 kV, Contact-8 kV. |
 About the Author: Jeroen Mackenbach
About the Author: Jeroen Mackenbach
Jeroen Mackenbach is a Technical Staff – Engineering Technologist for Edge in the Infrastructure Solutions Group. He is a trusted advisor for engineering, leadership, and global customers bringing edge solutions to the market and complementing sales teams with essential technical insights. Jeroen draws on more than 25 years of expertise in embedded systems hardware and software, as well as the Linux ecosystem, helping customers address the challenges associated with edge and distributed environments. Jeroen joined Dell Technologies in 2018 and was invited to become a CTO ambassador. Jeroen is a regular speaker at Executive Briefings and industry events, including the Embedded Linux Conference in 2018 and 2019. Before joining Dell Technologies, Jeroen spent more than 20 years in Production Management and Technical Sales roles for design and manufacturing services. He speaks English and Dutch and holds technical qualifications in Electronics and Communications Engineering from the Hogeschool Rens en Rens in Hilversum, Netherlands.



