Home > Storage > PowerMax and VMAX > Storage Admin > Implementing Dell SRDF SRA with VMware SRM > Dell SRDF SRA
Dell SRDF SRA
-
The following paragraphs present the access controls that were put in place in the test environment used in this paper. This example can be used as a guide when implementing Symmetrix Access Controls in VMware vCenter Site Recovery Manager configurations utilizing Dell SRDF Adapter. This example uses Unisphere for VMAX but Unisphere for PowerMax has a similar navigation.
Note: Because the use of SYMACL with the SRDF SRA requires granting permission to devices used by TimeFinder in test failover, the global option AutoTargetDevice is not supported.
AutoTargetDevice can automatically create SnapVX targets during test failover and therefore it is not possible to assign them to a device pool before the test. It is possible, however, to use Symmetrix Authorizations covered later in this chapter.
Dell SRDF Adapter acts as a proxy for SRM and performs a number of storage array-related operations. These include:
- Discovery of the storage arrays attached to the VMware ESXi hosts.
- Discovery of replicated devices and the state of the replication on the storage arrays connected to the VMware ESXi hosts.
- Creation of copies of replicated devices at the recovery site for testing and other activities.
- Failing over from the protection site to the recovery site in case of a planned or unplanned event.
The Symmetrix Access Controls configuration has to be applied such that all of the operations listed above here can be performed on the appropriate set of devices and storage arrays.
This example takes advantage of the alternate access ID method with client/server mode enabled. This means that the alternate access ID of the Solutions Enabler instance local to the SRM server is the ID used to create the ACLs.
The relevant example environment information is shown below:
- Protected Site:
- Solutions Enabler client unique identifier: 2C590AA6-544084C0-9C3F7478
- VMAX array serial number 194900281
- Recovery Site:
- Solutions Enabler client unique identifier: 2C5C06A6-54488CC0-9C3F747B
- VMAX array serial number 192603603
The following process demonstrates how to configure ACLs for the SRDF SRA:
- Create the Access Groups. Before access rules can be created access groups have to be configured. Access group must be created on all PowerMax arrays that are configured to use SYMACLs. PowerMax access groups contain user-defined server names and associated unique identifiers of the Solutions Enabler clients. Users can either create two separate groups, one for each Solutions Enabler instance or put both client IDs in the same group. Putting both clients in the same group is simpler as one group is easier to manage then two, but the granularity of control is diminished as both Solutions Enabler clients are forced to have the same access permissions. The decision to use a shared access group or separate ones depends entirely on the configuration of individual environments. Figure 186 shows the process to create an access group with Unisphere for VMAX. The figure shows an access group called “SRMGRP” being created on a VMAX array that contains both the local and remote Solutions Enabler client IDs.
Figure 186. Creating SYMACL access group in Unisphere for VMAX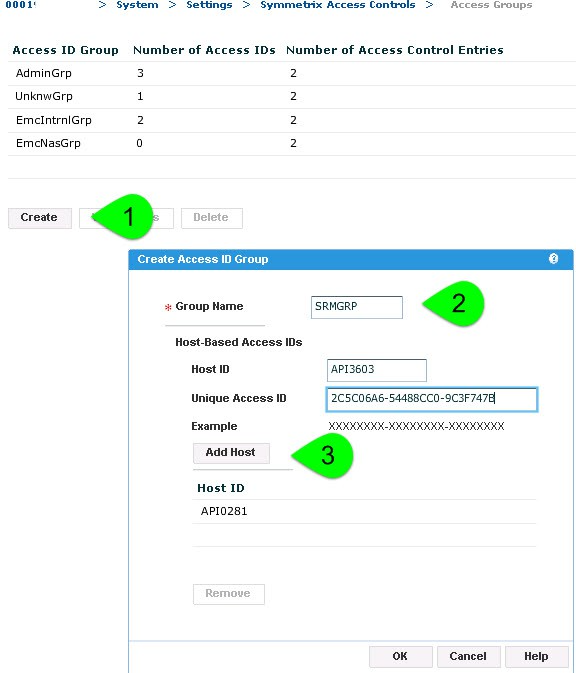
Figure 186 also shows the access group definitions on the protection site VMAX array. It can be seen from the figure that the group definitions include the unique IDs for the Solutions Enabler clients on the protection and recovery sites. This process should be repeated for all arrays using SYMACLs until every array involved in a SRM protection group has a group that includes the identifier for both the remote and local Solutions Enabler clients.
2. Create device pools. The second step of the process is to create a device pool. For each array, a pool must be created that includes all of the devices that will be used by SRM and the SRA. This includes SRDF replication devices (R1, R2, R21 etc...) and TimeFinder replication devices (BCVs, VDEVs or Clone targets). Examining masking records can help assist with finding the appropriate devices to include in the device pool. It is important to note that gold copy devices may not be presented to the VMware environment so other methods might be required to identify devices targeted for use in that capacity. Figure 187 shows the creation of a device pool called “SRMPOOL”.
Figure 187. Display of devices in the device pool utilized by the Solutions Enabler server - Unisphere for VMAX

3. Create the access control entries. Associate the access groups with access pools and assigning that association privileges. Both Solutions Enabler servers needs the following privileges on each array:
- “BASE” access for all devices on the PowerMax. “BASE” access to all devices is required for the SRDF SRA to be able to discover the array.
- “BASECTRL” and “RDF” access for only the SRM-related devices is required for basic functionality of the SRDF SRA. “BASECTRL” access allows for the SRA to manipulate device/composite groups and “RDF” access allows for the RDF control operations required for failover.
- “BCV” (Optional) If test failover/gold copy functionality with TimeFinder/Clone or VP Snap technologies is desired, “BCV” access for only the SRM-related devices is necessary.
- “VLOGIX” (Optional) If the user has configured the SRDF SRA to be able to mask/unmask devices during test recovery or recovery “VLOGIX” access is required for all devices on the PowerMax, not just the SRM-related ones.
Since “BASE” and “VLOGIX” control is required for all devices and the other permissions only require access to the SRM-related subset of devices, two different access control entries are required.
By default, there is a device pool (named ALL_DEVS) that is pre-created which automatically contains all of the devices on the PowerMax array. This is the device pool that should be associated with “BASE” control and optionally “VLOGIX” for the Solutions Enabler clients. Figure 188 shows the ACEs for an example environment.
Figure 188. Access control entries necessary for the SRDF SRA - Unisphere for VMAX
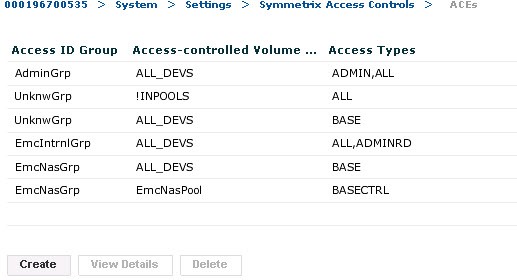
Note that two separate ACLs are required, one with “BASE” and “VLOGIX” access for all devices and a second with “RDF”, “BASECTRL”, “BCV” and “SNAP” permissions for the devices in the pool which was previously created called “SRMPOOL”. These two ACLs should be created on each VMAX array to allow for the proper access for both Solutions Enabler clients.
3-site SRDF (Star and Non-Star) and SYMACLs
For environments implementing 3-site SRDF the requirements for the protected and recovery site PowerMax array ACLs are no different than 2-site ACL requirements. However, in addition, the local and remote Solutions Enabler clients must be granted access to the tertiary array at the bunker site (for SRDF/Star this could be the Asynchronous or Synchronous site, for Non-Star SRDF this will always be the Synchronous site). Even though the SRA will not recover the workload on the bunker array, the Solutions Enabler clients need “RDF” and “BASECTRL” access to the devices on the tertiary array. Similar to the other arrays, the local and remote Solutions Enabler clients also require a second ACE on the tertiary array that allows them “BASE” access to device pool “ALL_DEVS”. Since the SRA also cannot execute a test failover, manipulate masking or create gold copies on the bunker site, “SNAP”, “BCV” or “VLOGIX” access is not needed by the SRDF SRA on the bunker array.
A quick evaluation of the ACEs discussed in the preceding paragraphs clearly shows that the Solutions Enabler clients used by the Dell SRDF Adapter have no authority over and above of which is required for support of the four operations listed in the introduction to this section. Therefore, Symmetrix Access Controls can be used effectively to address security concerns that are raised by the use of Solutions Enabler with SRM and the SRA
