Home > Data Protection > PowerProtect Data Manager > PowerProtect Cloud Snapshot Manager: Application Consistent Snapshots > Prerequisites
Prerequisites
-
This section describes the prerequisites for application consistent snapshots in CSM - VSS enabled snapshots and custom scripts based on AWS SSM documents.
Make sure that the EC2 instances you want to protect with application consistent snapshots meet all the following requirements:Amazon EC2 Windows instance requirements
Verify that your EC2 instances meet the Systems Manager requirements.
In addition, VSS-enabled EBS snapshots are supported for instances running Windows Server 2008 R2 or later.
SSM
Make sure that your instances are SSM managed and run the minimal required SSM agent version, which should be 2.2.58.0 or later. If you are using an older version of SSM Agent, you can update it by using Run Command.
For more information, see Installing and Configuring SSM agents.
In the AWS management console, from the Systems Manager service, select the Managed Instances page. In the Managed Instances page, if your instances are listed, it means they are SSM managed. You can check the version of the SSM agent in the page as shown in the following figure:
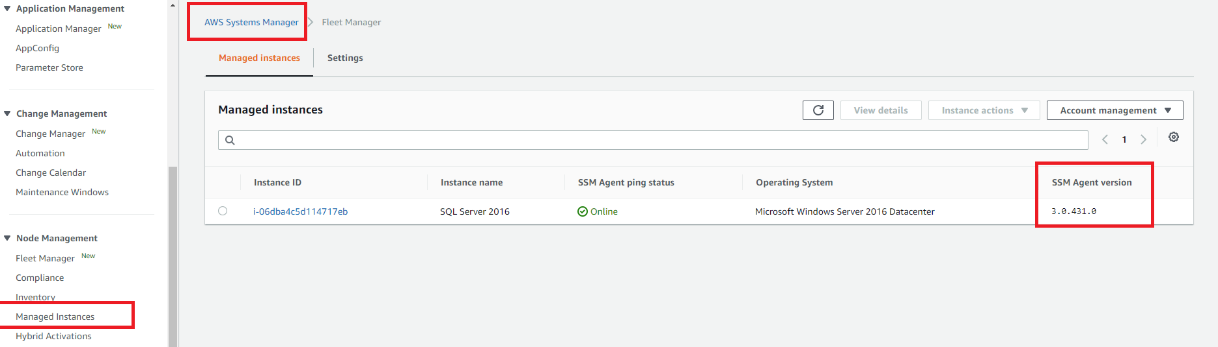
Note that it might take a few minutes for new instances to appear in this page, and they must be in “running” state.
Instances have the required permissions
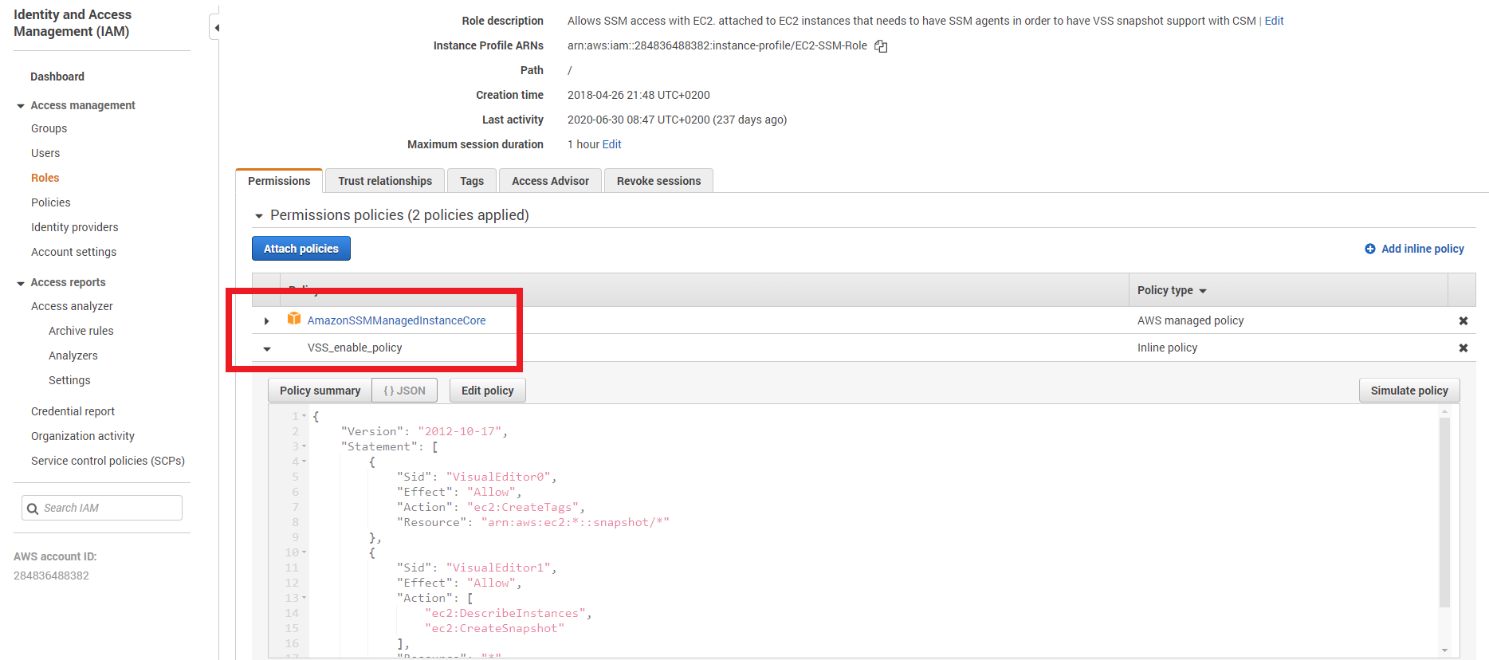
You need to create an IAM Role (the role should be attached to EC2 instances you want to protect) that contains the following policies:
- AmazonSSMManagedInstanceCore—Amazon managed policy which is required to run SSM documents (for custom pre-scripts and post-scripts, file-level recovery auto attach restored volumes)
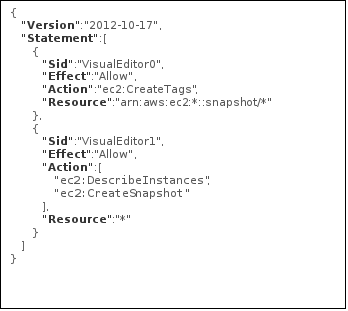
- A policy that includes the actions: DescribeInstances, CreateTags, CreateSnapshot. These actions are required to take VSS enabled snapshots. The following JSON describes the required policy:
The following figure shows a Role creation permission details and the two policies; the AmazonSSMManagedInstanceCore policy, and an inline (or a pre-created) policy. The inline policy includes the JSON format of DescribeInstances, CreateTags, CreateSnapshot:
Make sure that the Role is attached to your instances. The following figure is provided as an example:
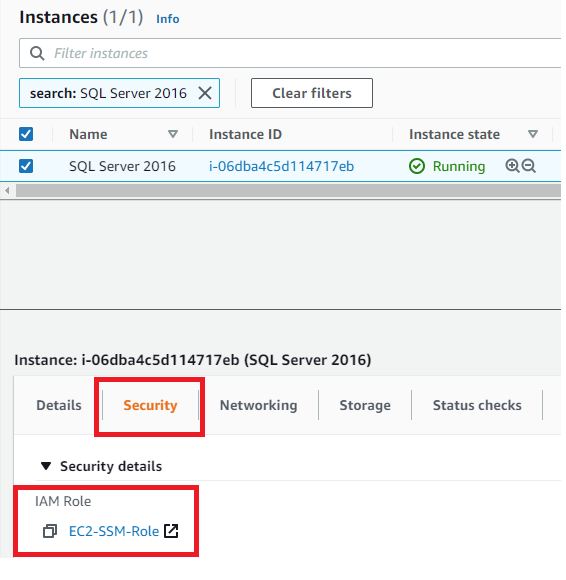
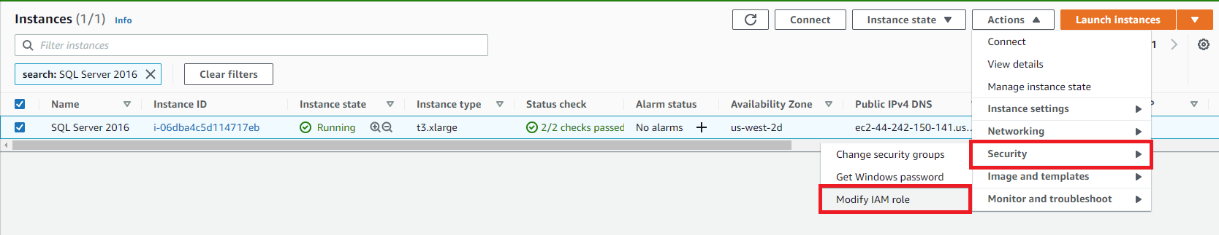
To attach this Role to an existing instance, select your instance then click Actions > Security > Modify IAM role as shown in the following figures:
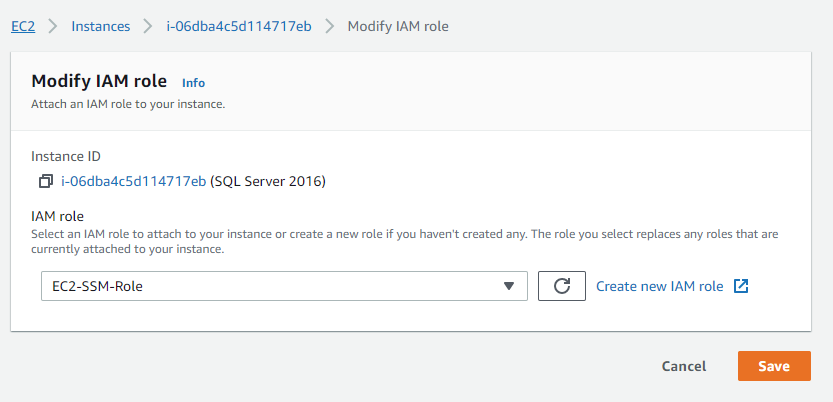
If the instance already has another role attached to it, make sure to add the permissions to the attached Role.
VSS components
The AWS VSS components package must be installed on the instances to enable the creation of VSS snapshots. Make sure that your instance has an SSM agent installed and that it appears in the Managed Instances page.
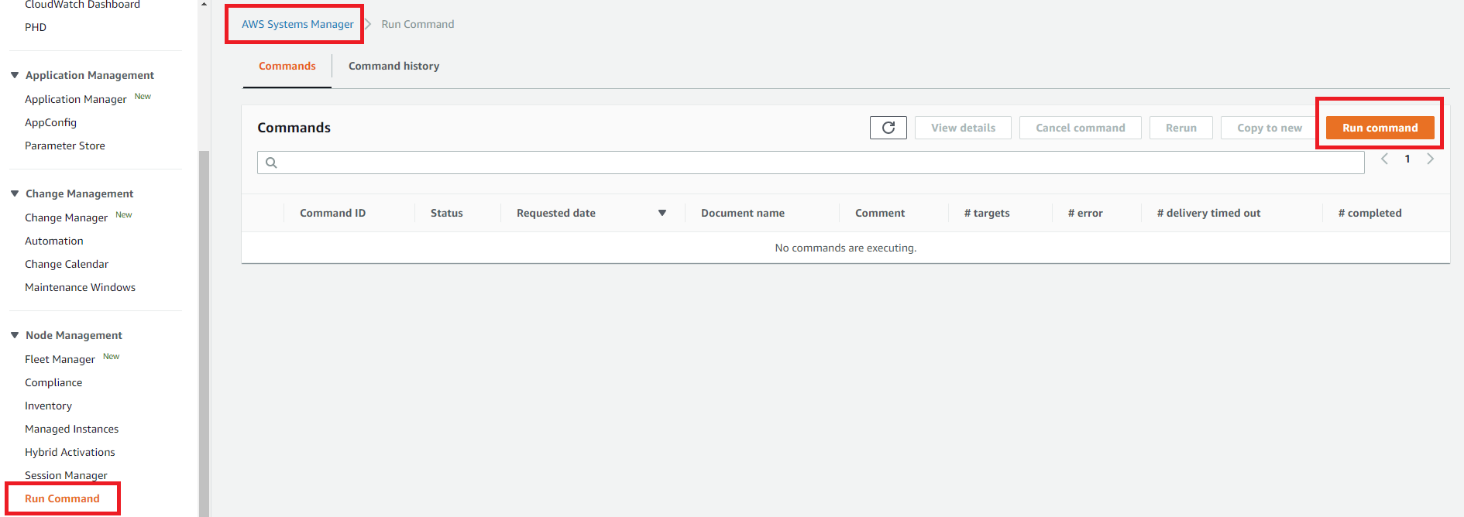
To install the VSS components using the AWS management console, complete the following steps:
- Use the Systems Manager service, select the Run Command page, and click the Run command button to create a new one, as shown in the following figure:
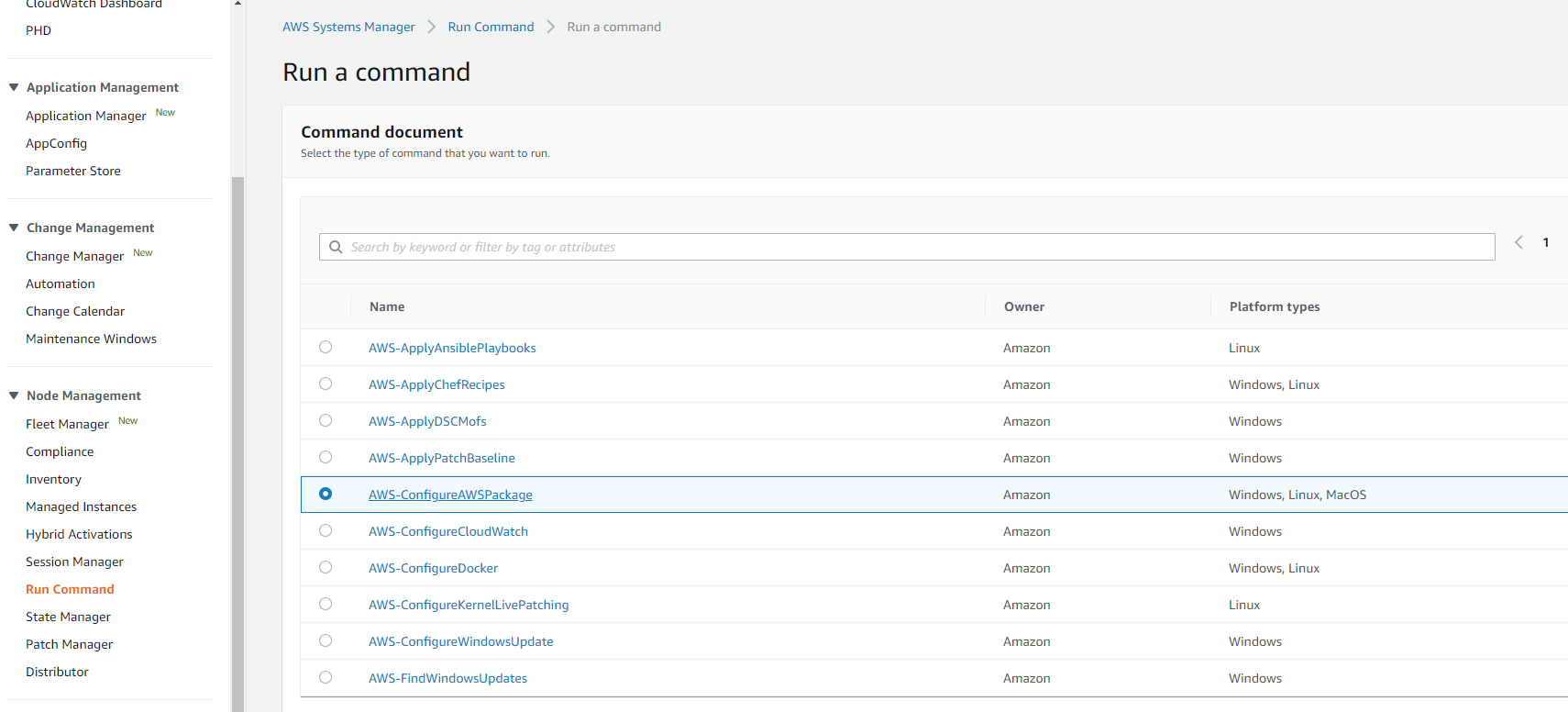
- Select the AWS-ConfigureAWSPackage command document as shown in the following figure:
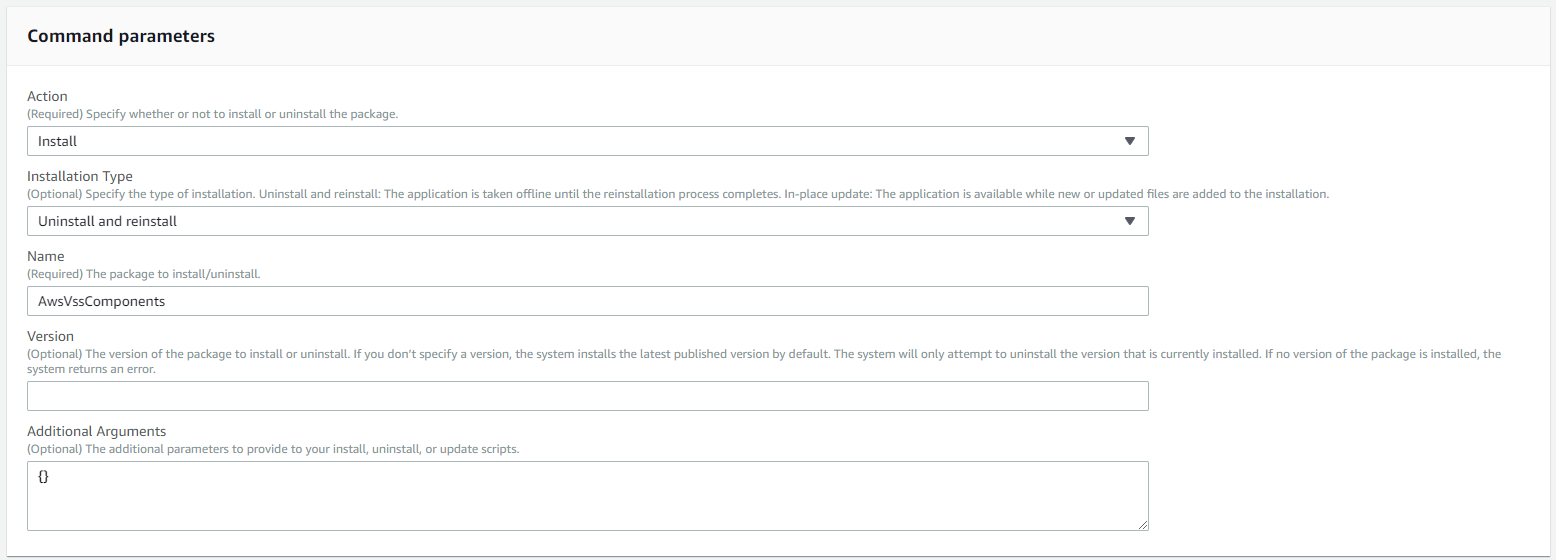
- Select the Install Action and specify AwsVssComponents in the Name field. Use the defaults for other fields:
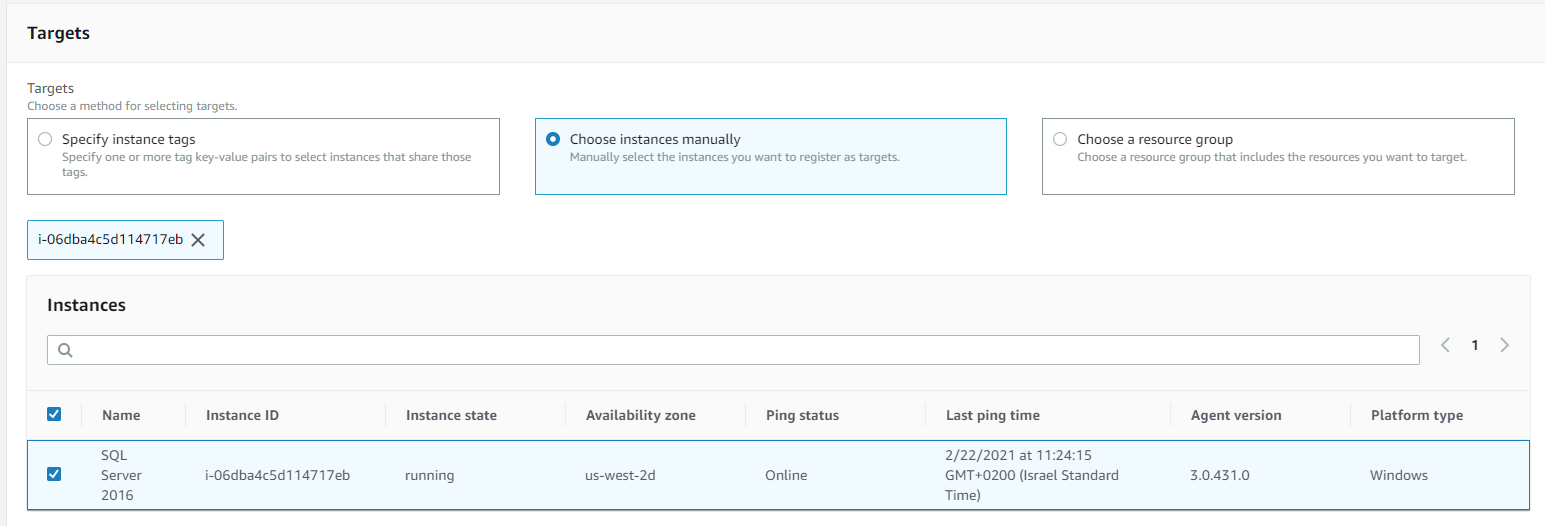
- Select the target instances:
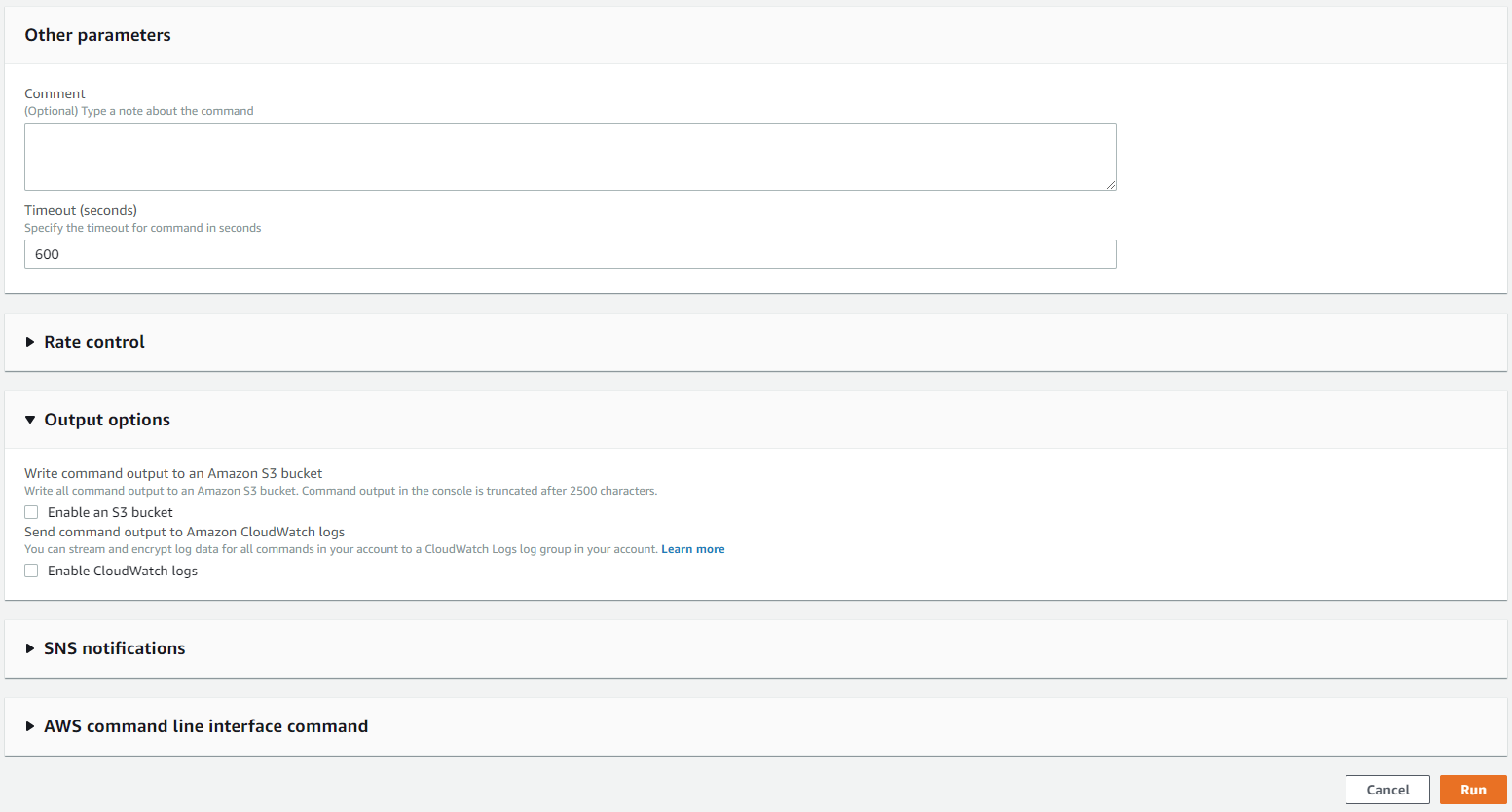
- Change the other options as you see fit or use the defaults, then Click Run as shown in the following figure:
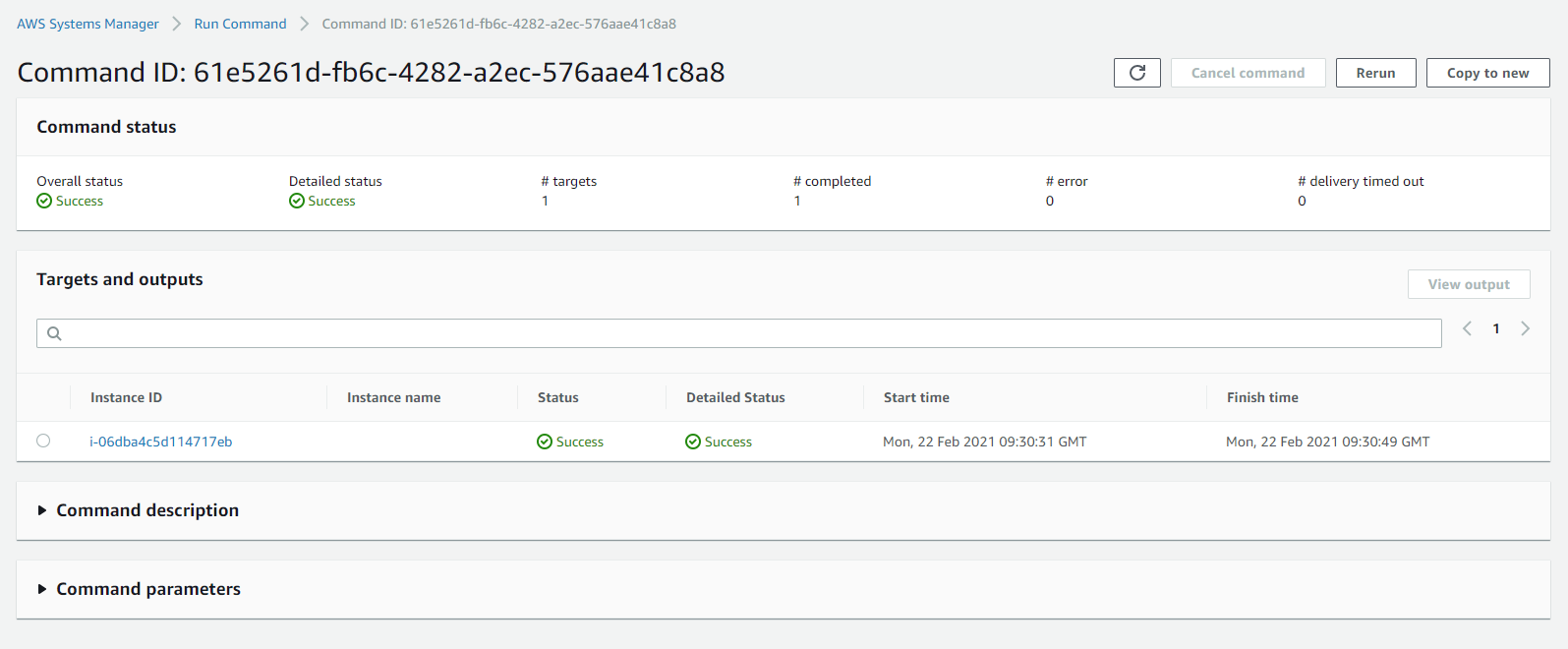
The results will be displayed in the Run command page. The “Success” status indicates that the VSS components package has been installed successfully:
After installing the SSM agent and the VSS components on the instances that you want to protect, you can create application consistent snapshots using VSS with CSM.
Permissions of the CSM IAM User/Role to run custom scripts
In addition to the SSM agent and Role attached to the instances, to run custom scripts, the IAM User or the IAM Role used by Cloud Snapshot Manager must have the required permissions to the SSM documents that it can run:
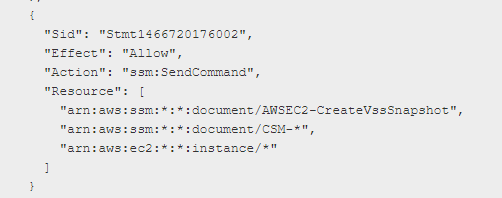
The above section defines the name prefix required for SSM documents so that CSM could run them. By default, the minimal required permissions that CSM requires allow it to run all documents that their name starts with “CSM-“. Make sure to add this prefix to your SSM documents when you create them. You can also edit the permissions of your IAM User or IAM Role to include the documents that you want CSM to run.
For more information, see CSM Prerequisites for application consistency in the CSM online help.
