Home > Data Protection > PowerProtect Cyber Recovery > Dell PowerProtect Cyber Recovery: Reference Architecture > Cyber Recovery features
Cyber Recovery features
-
The Cyber Recovery solution key features include:
- Secure data in an isolated network with an automated operational air gap
- Policy-based secure copy creation, management, and scheduling
- Integration with Index Engine CyberSense software to detect if the backup data has been compromised
- Robust REST API framework that enables analytics with artificial intelligence (AI) and machine learning (ML) for malware (including ransomware). Cyber Recovery REST API availability on Dell Marketplace and Stoplight
- Recovery assistance and the ability to export data to a recovery host easily
- Automated recovery options for the NetWorker and PowerProtect Data Manager applications
- Optional multifactor authentication enabled from the UI or command-line interface (CLI) to provide added protection for the Cyber Recovery software and its resources
- Informative dashboards that show system alerts, the state of the Cyber Recovery vault, and critical details
- Ability to transmit alerts through SMTP outside the Cyber Recovery vault
- Support for high availability (HA) on DD series in the Cyber Recovery vault
- Replication window enforcement that stops a sync operation if it runs longer than the replication window
- Automatic retention locking feature that allows setting of retention lock with no additional operation. Cyber Recovery deployments running DDOS 7.8 support replicating a Retention Lock Compliance replication on the production system to the Cyber Recovery vault
- Ability to create a Cyber Recovery policy by selecting multiple MTree replication contexts (multiple MTrees are only supported for a PowerProtect Data Manager policy)
- Cyber Recovery supports subscription licensing model along with evaluation or proof-of-concept license that is valid for 90 days
- Sheltered Harbor endorsement for achieving compliance with financial institution data vaulting standards and certification, planning for operational resilience and recovery, and protecting financial critical data
- On-demand cleanup from the Cyber Recovery UI by clicking the Maintenance tab under the gear icon in the masthead navigation
- A maximum of three simultaneous login sessions for the Security Office (crso) for enhanced security
- Notification if a user's email address is modified or if multifactor authentication is disabled
- Option to add a virtual Ethernet adapter to configure a separate IP address for SMTP communication from the Cyber Recovery vault if the Postfix mail transfer agent is used
- Support for recovery of PowerProtect Data Manager with Oracle, SQL, and file system workloads
- Option to provide the location of the latest bootstrap backup for a faster automated NetWorker recovery
- Support for the Cyber Recovery vault on Amazon Web Services (AWS), available from Amazon Marketplace using custom pricing
- Support for the Cyber Recovery software on a supported Linux operating system in a Microsoft Hyper-V environment
- Support for the analyze operation for PowerProtect Data Manager backups (Filesystem, VMware, and Oracle) is enabled
- Addition of REST API V6, which is backwards compatible with REST API V5 and V4. REST API V3 and earlier versions are no longer supported
- The “crsetup.sh” script to perform a readiness check before upgrading the Cyber Recovery software
- Support for multiple DDVE appliances for the Cyber Recovery vault on AWS—up to 5 DDVEs are supported
- CyberSense analysis report can be sent to additional email addresses
- Cyber Recovery telemetry feature sends telemetry information using one-way email to Dell Technologies for troubleshooting purposes. Telemetry can be run on demand using CRCLI or scheduled to run with frequency of minimum of one day and maximum of 30 days
- Cyber Recovery custom certificate support: users can generate a Certificate Signed Request (CSR), submit the CSR to Certificate Authority (CA) to apply for a CA signed certificate, and can add it to the Cyber Recovery system
- Secure reset option to regenerate the Cyber Recovery certificates – Starting with Cyber Recovery version 19.11, the crsetup.sh script includes an option that allows you to reset the Cyber Recovery root certificates and encryption keys when your deployment is compromised.
- From CRCLI and API, users have the option to:
- Include or exclude files and file path from the analyze action
- The content format of the MTree to be analyzed can be specified optionally, which is included as part of the CyberSense report for informational purposes
- Password expiration is set to 90 days by default; the value can be changed to a minimum of 30 days and a maximum of 180 days for all UI users
- Cyber Recovery UI support menu - Cyber Recovery 19.10 provides a new support menu for users in Cyber Recovery UI. Users can generate and download the support bundle from Cyber Recovery UI.
- CyberSense host information in copy details - Cyber Recovery provides information about the analysis host which analyzed the copy in the copy details. This information helps users to identify the Cyber Sense details for environments with more than one CyberSense host
- Policy network interfaces - Users can use eth V1 for analysis or for Cyber Recovery policy but cannot use both at the same time. For example, only ethV0 is listed in the following figure because ethV1 is being used for the Cyber Recovery policy.
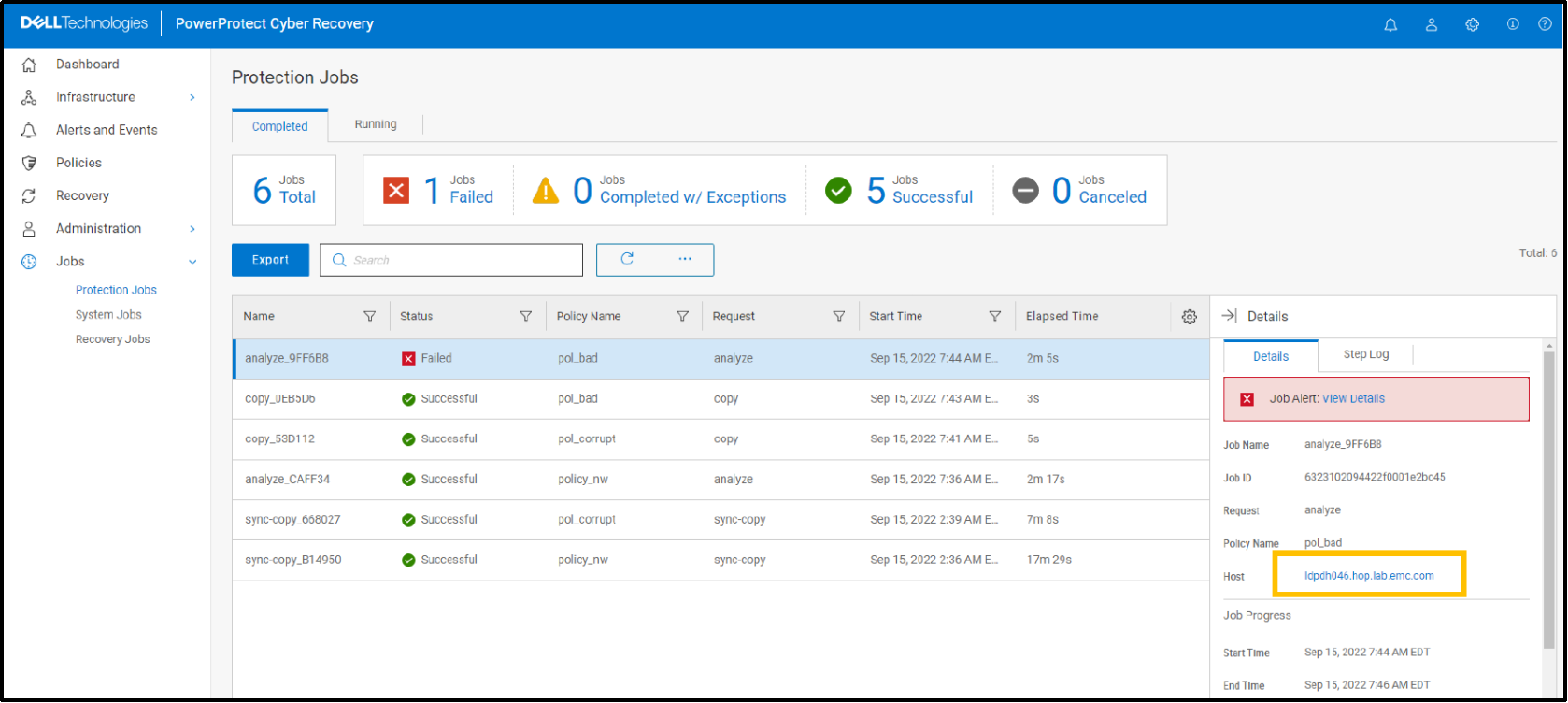
- CyberSense analyze dashboard link from Cyber Recovery jobs - Starting with Cyber Recovery version 19.12, the job details section and policies/copies section have links that open the CyberSense analyze dashboard when a copy is found to be suspicious.
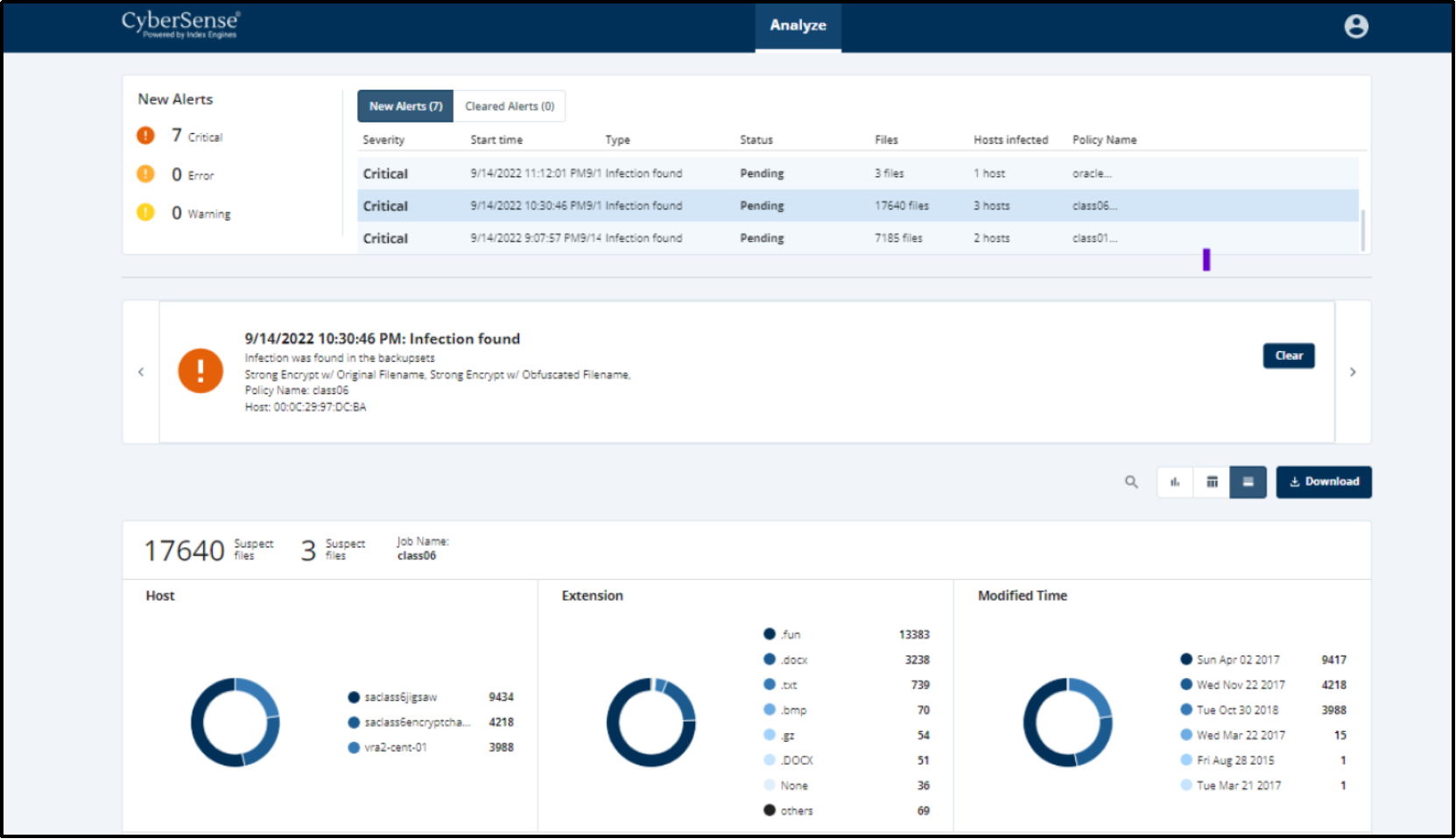
- CyberSense analyze dashboard - CyberSense analyze dashboard is a UI that was designed specifically for CyberSense workflow. It provides the ability to scope and analyze a potential attack in a single dashboard.
- Cyber Recovery users and access management - Multiple security officer roles: Starting with Cyber Recovery version 19.12, the Cyber Recovery security officer (crso) can create multiple security officer roles and manage those accounts. The security officer has the same permissions as the crso but cannot manage the crso account.
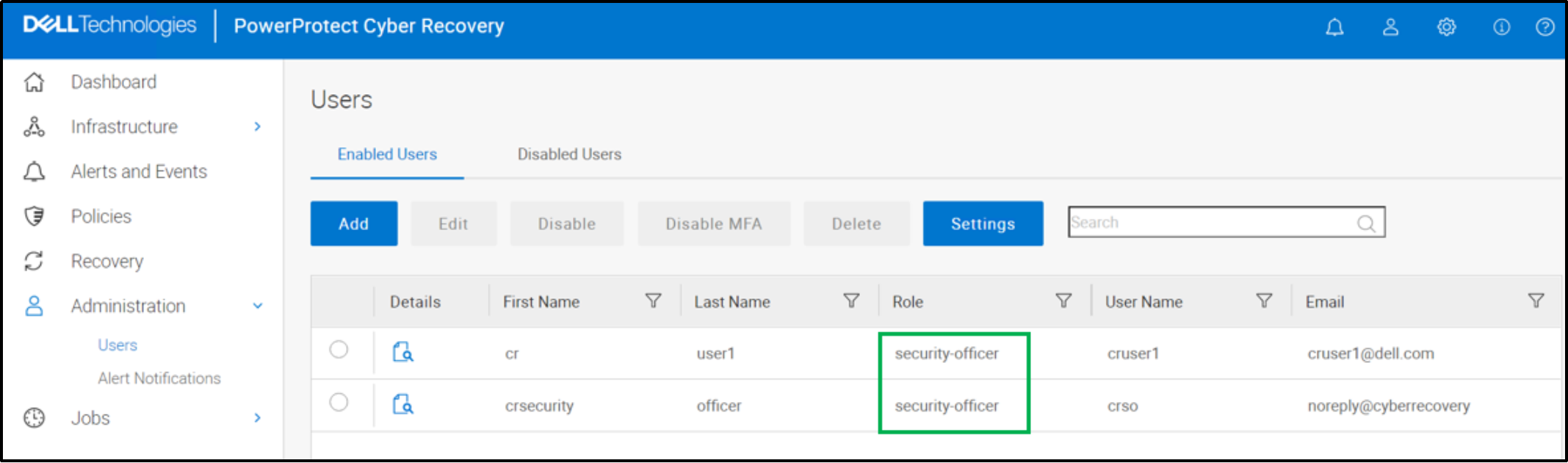
Note: Security officer users can create other security officer users. The “Admin” role can no longer create users.
Deletion of users: Starting with Cyber Recovery version 19.12, the crso and security officer can delete security officer, admin, and dashboard users from the Cyber Recovery UI.
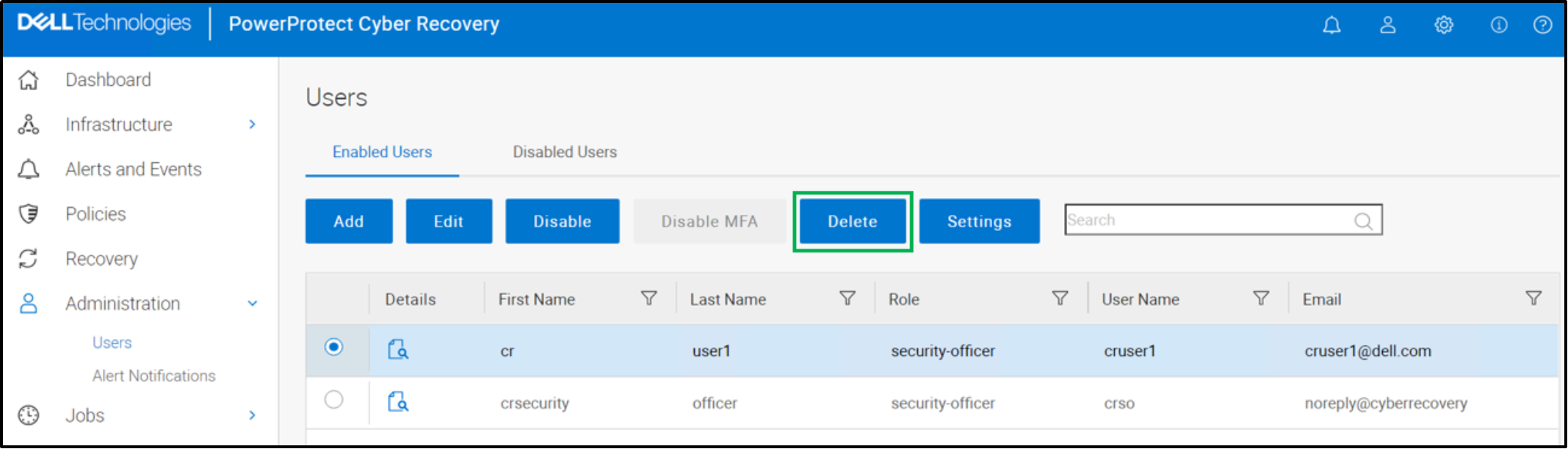
Note: One cannot add a user with the same username of a previously deleted user. Instead, add a user that has a different username.
- Cyber Recovery alert services
- DD series capacity alert
Cyber Recovery notifies a user if the Secure Copy/Sync operation fails due to space issues in Vault Data Domain. If the DD system in the Cyber Recovery vault generates a capacity alert, the Cyber Recovery software displays it as warning or critical alert on the dashboard and on the Alerts tab. The threshold capacity can be set on the DD system.
- Alert when one or more DD series is down:
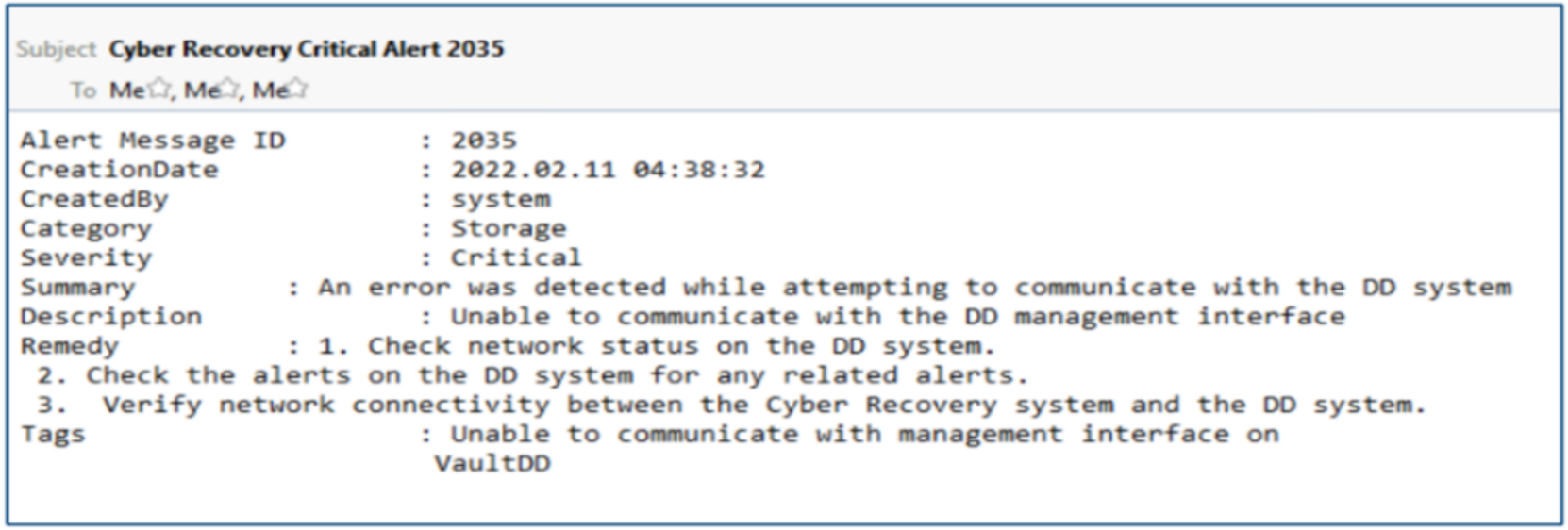
When a DD series in the Cyber Recovery vault is down, the Cyber Recovery software generates a critical alert that is displayed on the dashboard and on the Alerts tab. It also sends an email message to user accounts that are configured to receive email messages. The vault status is displayed as Degraded (orange icon) until the DD system is up and running again.
- Monitor Cyber Recovery services
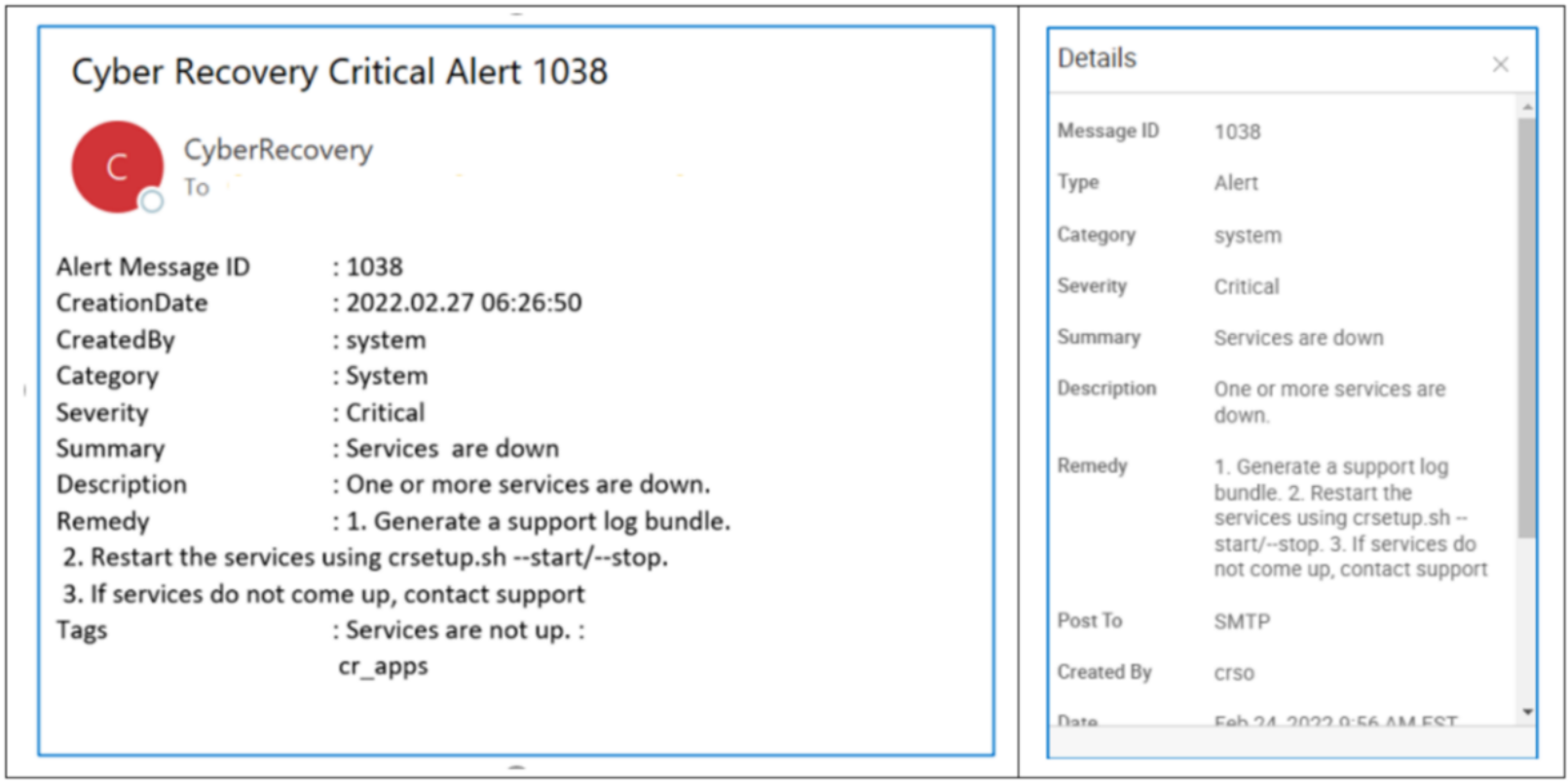
Cyber Recovery 19.10 monitors its services in the background and alerts every hour after initial critical alert if one or more Cyber Recovery service is down. If a Cyber Recovery service stops, the Cyber Recovery software displays a critical alert on the dashboard and the Alerts tab. Use the crsetup.sh script to restart the service.
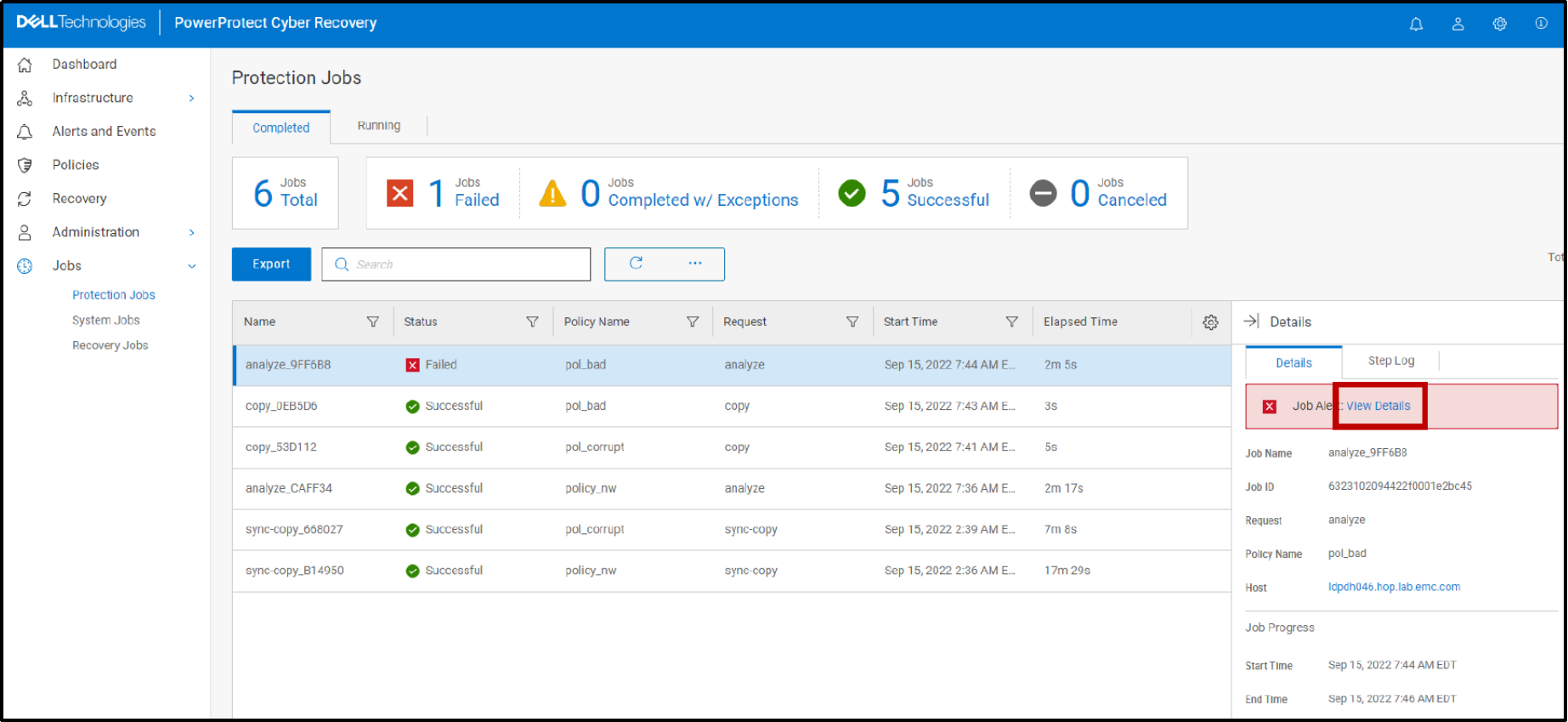
- Links to the Alerts and Events page
Starting with Cyber Recovery version 19.12, any failed jobs that generated alerts have links to the “Alerts and Events” page and show the alert details.
- Configuring and managing multiple links for CyberSense
Starting with Cyber Recovery version 19.13, you can define multiple links between a CyberSense host and one or more PowerProtect DD systems from the Cyber Recovery UI. CyberSense version 8.2 with Cyber Recovery version 19.13 provides the ability to configure links between network interfaces on the PowerProtect DD and network interfaces on the CyberSense host to improve network performance. The multilink feature provides significant performance improvements for all workloads. With Cyber Recovery version 19.13 and CyberSense version 8.2, you must configure the network interface links for each CyberSense host before you can analyze copies.
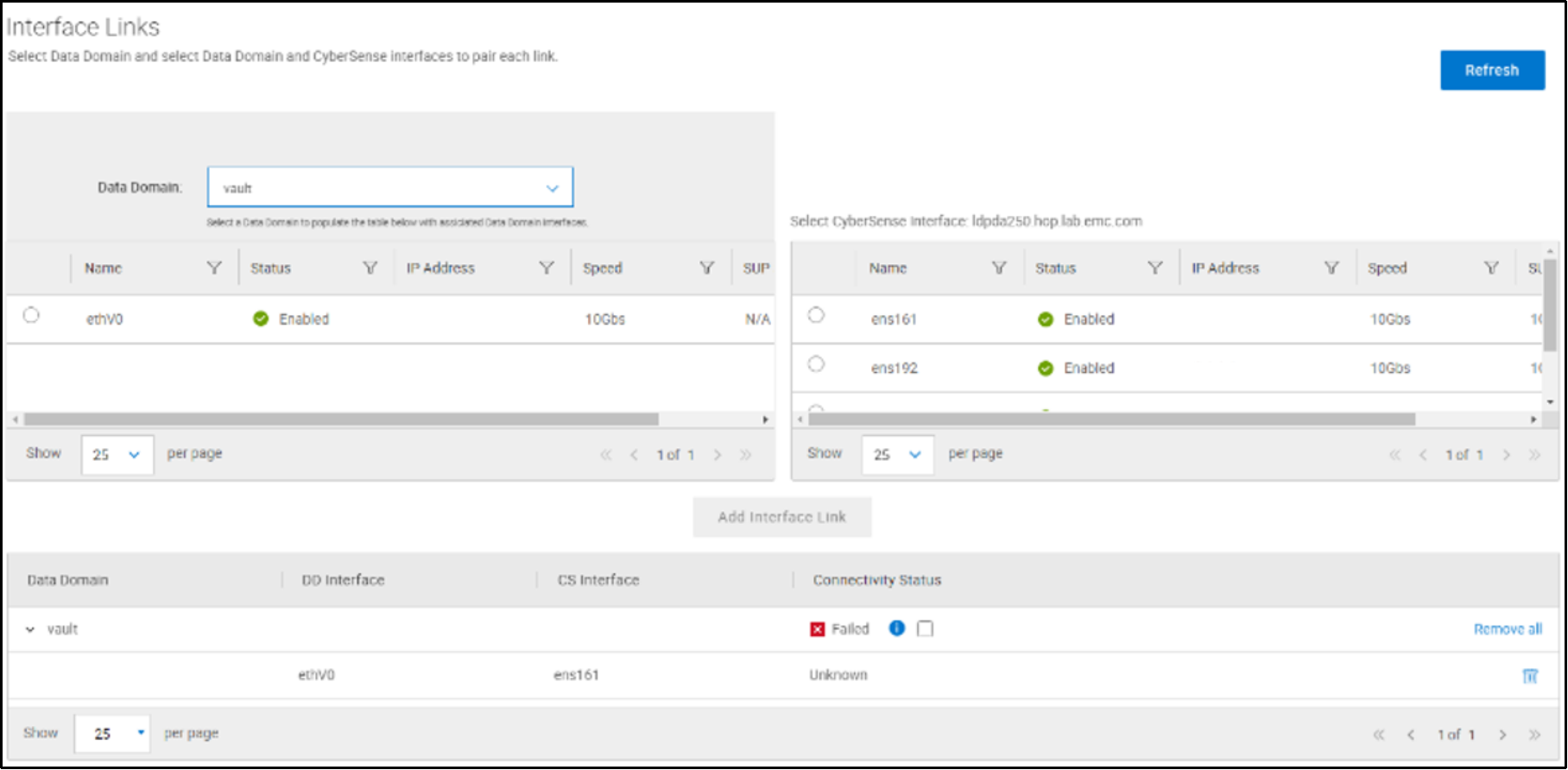
Note: You can use CyberSense versions earlier than version 8.2 with Cyber Recovery version 19.13; however, you cannot configure multiple links.
The multilink feature enables you to take advantage of multiple Ethernet interfaces on the CyberSense host and the PowerProtect DD systems. CyberSense Analyze operations read data from the PowerProtect DD system using both the NFS and DD Boost protocols. A multilink configuration improves performance for both NFS and DD Boost read operations by load-balancing traffic across all available links.
For more details about configuring multiple links, see the Dell PowerProtect Cyber Recovery Product Guide.
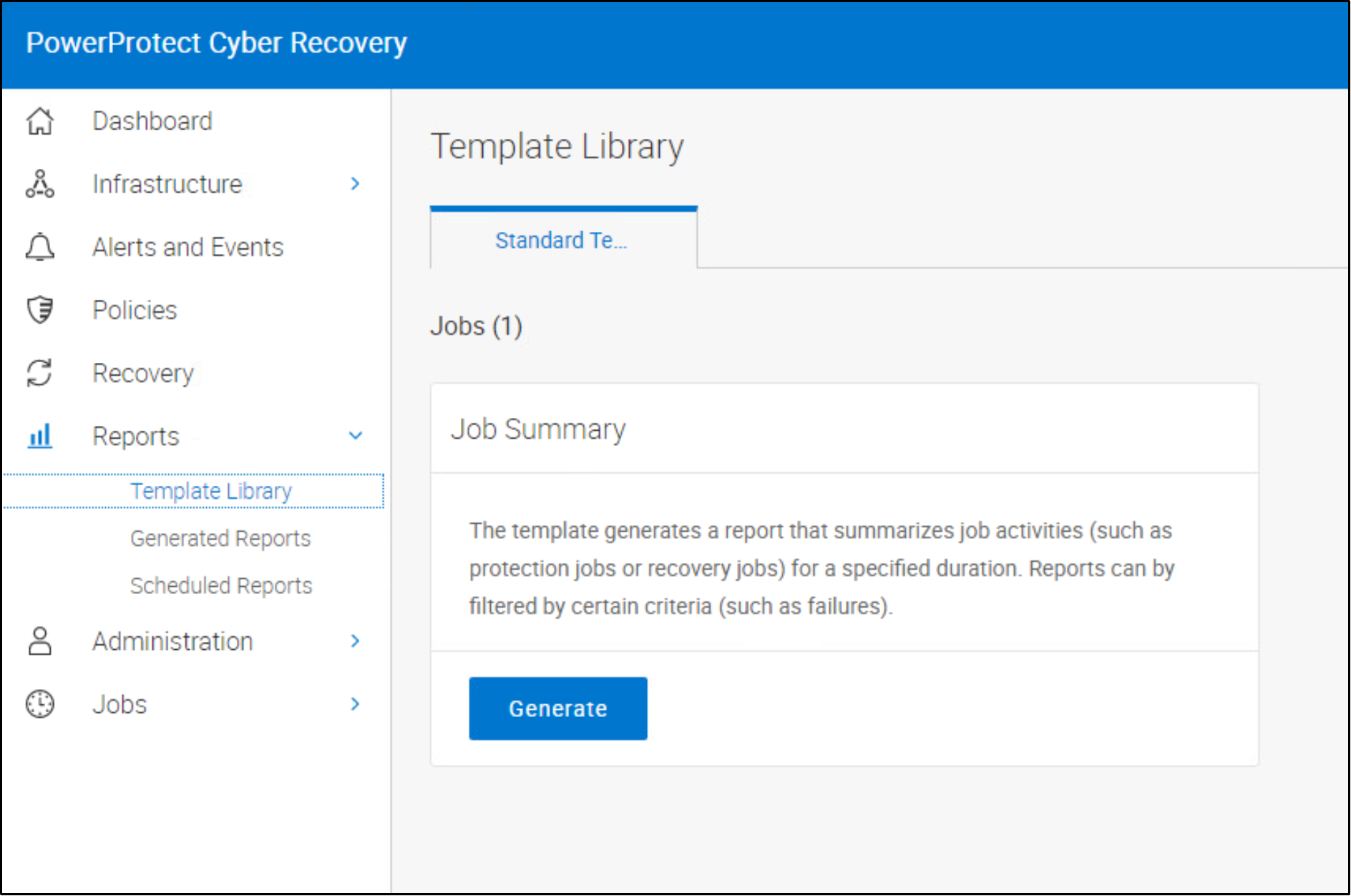
- Cyber Recovery reporting
The Cyber Recovery reporting feature in the Cyber Recovery UI enables you to create, run, and schedule reports that summarize job activities. The reporting feature includes a built-in job summary report template. A wizard provides access to a template library that contains predefined standard templates for various reporting categories. The wizard guides you through the template to create a report. Security officers and admin users can create report schedules or on-demand reports that provide information about Cyber Recovery activities. Scheduled reports are emailed, and on-demand reports can be downloaded and emailed.
For more details about Cyber Recovery reporting, see the Dell PowerProtect Cyber Recovery Product Guide.
- Starting with Cyber Recovery version 19.13, an Alternate Recovery option is available in the Cyber Recovery UI.
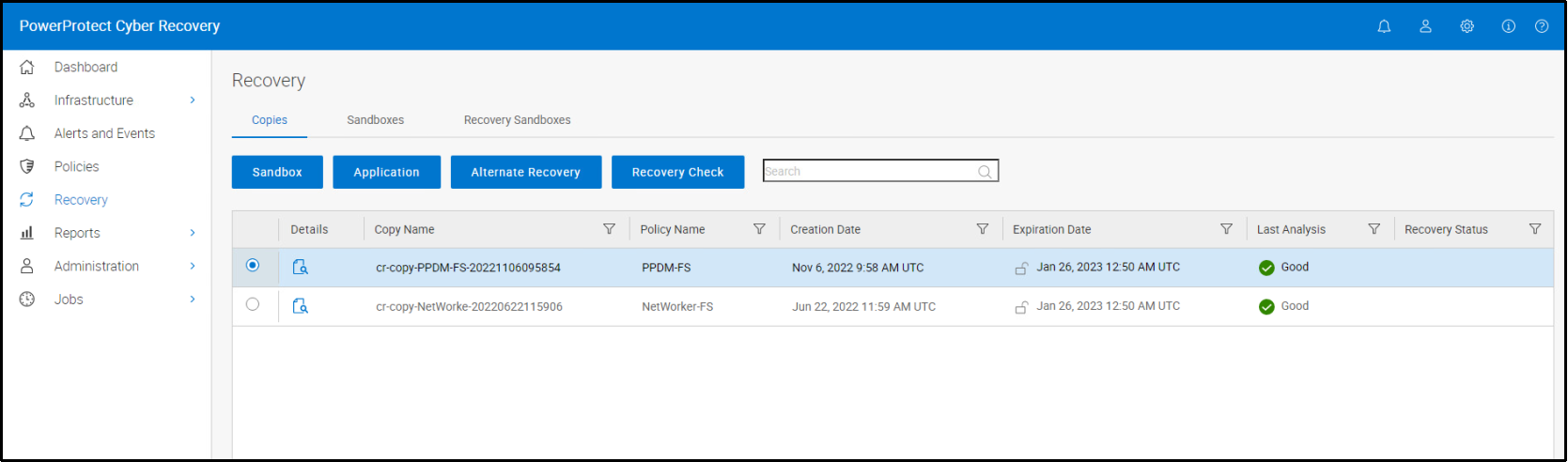
For more details about recovering data to an alternate DD series, see the Dell PowerProtect Cyber Recovery Product Guide.
Cyber Recovery support matrix
For details about compatibility, see the Dell PowerProtect Cyber Recovery Simple Support Matrix.
