Home > Data Protection > PowerProtect DD Series Appliances > Dell EMC PowerProtect DD Virtual Edition on Google Cloud > Architecture overview
Architecture overview
-
The following diagram shows the architecture of DDVE on Google Cloud.
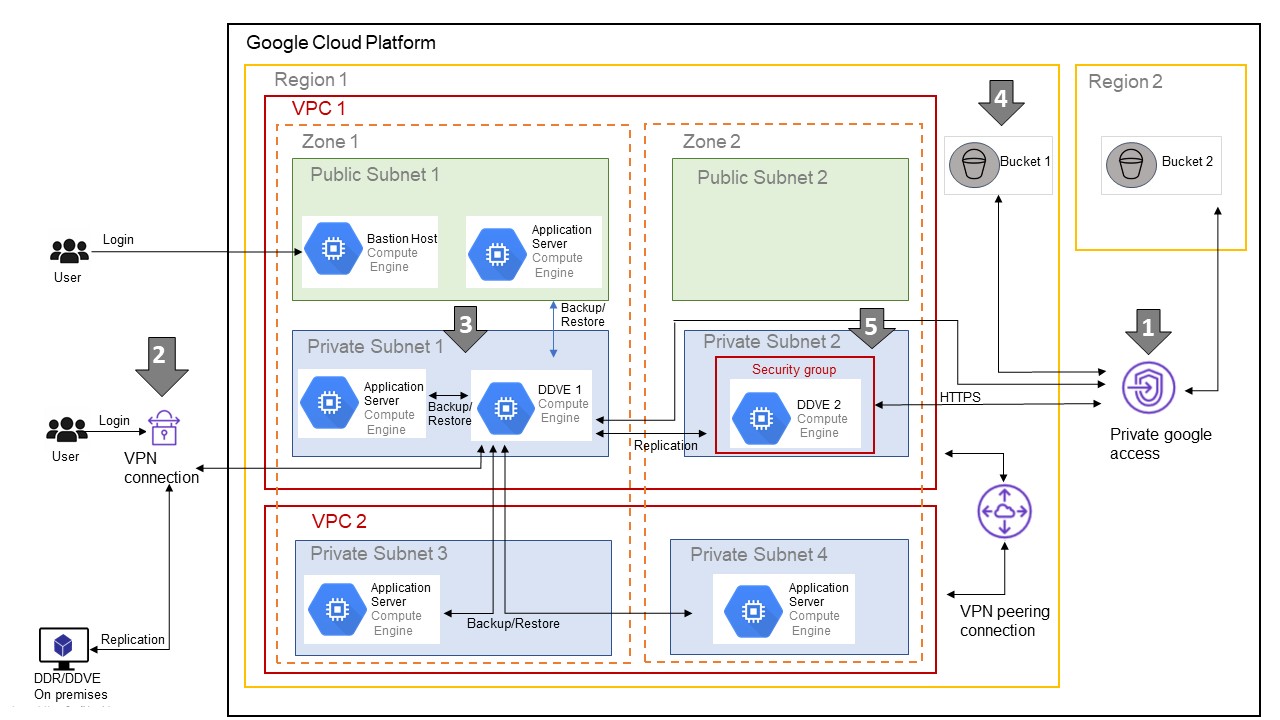
- To keep data traffic between DDVE and the bucket within the Google Cloud infrastructure, it is recommended to create Private Google Access. This configuration keeps DDVE from depending on a NAT Gateway or Public IP address to access the bucket.
- To keep data transfers secure, Dell Technologies recommends a VPN connection to replicate data from an on-premises host to DDVE in the cloud, or from DDVE in the cloud to an on-premises host.
- DDVE is categorized as a backend server. It must be kept in a private subnet with a private address. Never set a public IP address for DDVE.
- Dell Technologies recommends creating the bucket in the region where the DDVE instance is running. A multiregional bucket is also supported and should be used if the user is in a location where no data center is available as a regional location. A separate bucket for each DDVE is required.
- All DDVE instances must be secured with the appropriate security group entries.
Note:
- Typically, SSH (Port 22) or HTTPS (Port 443) is used for DDVE inbound access.
- HTTPS (443) must be allowed for outbound bucket access for DDVE.
- TCP ports 2049 and 2051 are used for DD Boost and replication purposes.
