Home > Communication Service Provider Solutions > Telecom Multicloud Foundation > Open Telecom Ecosystem > Guides > Certified Solution of SUSE Rancher 2.6.3, K3s 1.21.7 and SUSE Linux Enterprise Micro 5.1 on PowerEdge Servers > SUSE Rancher
SUSE Rancher
-
For the SUSE Rancher software installation, start with the installation of an enterprise-grade Linux operating system such as SUSE Linux Enterprise Micro as the base software layer.
Preparation(s)
- For the respective node’s firewall service, either
- Enable and configure the necessary inbound ports (https://rancher.com/docs/
rancher/v2.6/en/installation/requirements/ports/) or
- Stop and completely disable the firewall service.
- Determine the desired SSL configuration (https://rancher.com/docs/rancher/v2.6/en/installation/install-rancher-on-k8s/for TLS termination
- Rancher-generated TLS certificate
Note: This is the easiest way of installing SUSE Rancher with self-signed certificates.
- Let’s Encrypt
- Bring your own certificate
- Obtain a Helm (https://helm.sh/docs/intro/install/) binary matching the respective Kubernetes version for this SUSE Rancher implementation.
#Obtain helm binary https://raw.githubusercontent.com/helm/helm/main/scripts/get-helm-3 | bash
Note: Enable the respective kubeconfig setting for kubectl , K3s - /etc/rancher/k3s/k3s.yml, to be leveraged by helm command. (Example: chmod 600 /etc/rancher/k3s/k3s.yaml, export KUBECONFIG=/etc/rancher/k3s/k3s.yaml)
Prerequisites
To meet the solution stack requirements, verify that the SUSE Linux Enterprise Micro operating system is installed and configured for the node to use:
- Domain Name Service (DNS): An external network-accessible service to map IP Addresses to hostnames.
- Network Time Protocol (NTP): an external network-accessible service to obtain and synchronize system times to aid in timestamp consistency.
- Software Update Service: access to a network-based repository for software update packages. This repository can be accessed directly from each node using registration to any of the following:
- The general, internet-based SUSE Customer Center (SCC) portal
- An organization’s SUSE Manager infrastructure
- A local server running an instance of the Repository Mirroring Tool (RMT)
Note: When installing the node, you can point it to the respective update service. This can also be accomplished after the installation is complete using the SUSEConnect command-line tool.
Deployment process
While logged into the node, as root or with some privileges, perform the following steps to install SUSE Rancher:
- Create the Helm Chart custom resource for cert-manager.
- Set the following variable with the wanted version of cert-manager (for example, CERT_MANAGER_VERSION="v1.5.1").
CERT_MANAGER_VERSION=""
Note: The currently supported version of cert-manager is v1.5.1.
- Create the cert-manager CRDs and apply the Helm Chart resource manifest:
kubectl apply --validate=false -f https://github.com/jetstack/cert-manager/releases/download/${CERT_MANAGER_VERSION}/cert-manager.crds.yaml
# Add the Jetstack Helm repository
helm repo add jetstack https://charts.jetstack.io
# Update your local Helm chart repository cache
helm repo update
# Install the cert-manager Helm chart
helm install cert-manager jetstack/cert-manager \
--namespace cert-manager \
--create-namespace \
--version ${CERT_MANAGER_VERSION}
- Check the progress of the installation, looking for all pods to be in running status:
kubectl get pods --namespace cert-manager
- Enter this command to monitor the progress of the installation.
watch -c "kubectl get deployments -A"
The deployment is complete all the deployments (cert-manager, cert-manager-cainjector, and cert-manager-webhook) show at least one as AVAILABLE.- After confirming that all the pods are running, press Ctrl+C to exit the watch loop.
- Add the SUSE Rancher helm chart repository.
helm repo add rancher-stable https://releases.rancher.com/server-charts/stable
- Create a namespace for SUSE Rancher
kubectl create namespace cattle-system
- Prepare to use the Helm Chart for SUSE Rancher:
- Set the following variable to the hostname of the SUSE Rancher server instance (for example, HOSTNAME=" rancherxr11.dsp.lab”):
HOSTNAME=""
Note: This hostname should be resolvable to an IP address of the K3s host or a load balancer/proxy server that supports this installation of SUSE Rancher.
- Set the following variable to the number of deployed K3s nodes planned to host the SUSE Rancher service (for example, REPLICAS="1"):
REPLICAS=""
- Set the following variable to the desired version of SUSE Rancher server instance (for example, RANCHER_VERSION="2.6.3"):
RANCHER_VERSION=""
- Install the SUSE Rancher Helm Chart
helm install rancher rancher-stable/rancher \
--namespace cattle-system \
--set hostname=${HOSTNAME} \
--set version=${RANCHER_VERSION} \
--set replicas=${REPLICAS}
- Enter this command to monitor the progress of the installation.
kubectl -n cattle-system rollout status deploy/rancher
watch -c "kubectl get deployments -A"
kubectl get all -A
The deployment is complete all the pods have a status of Completed or Running with the number of READY pods being 1/1, 2/2, and so on.
- After confirming that all the pods are running, press Ctrl+C to exit the watch loop.
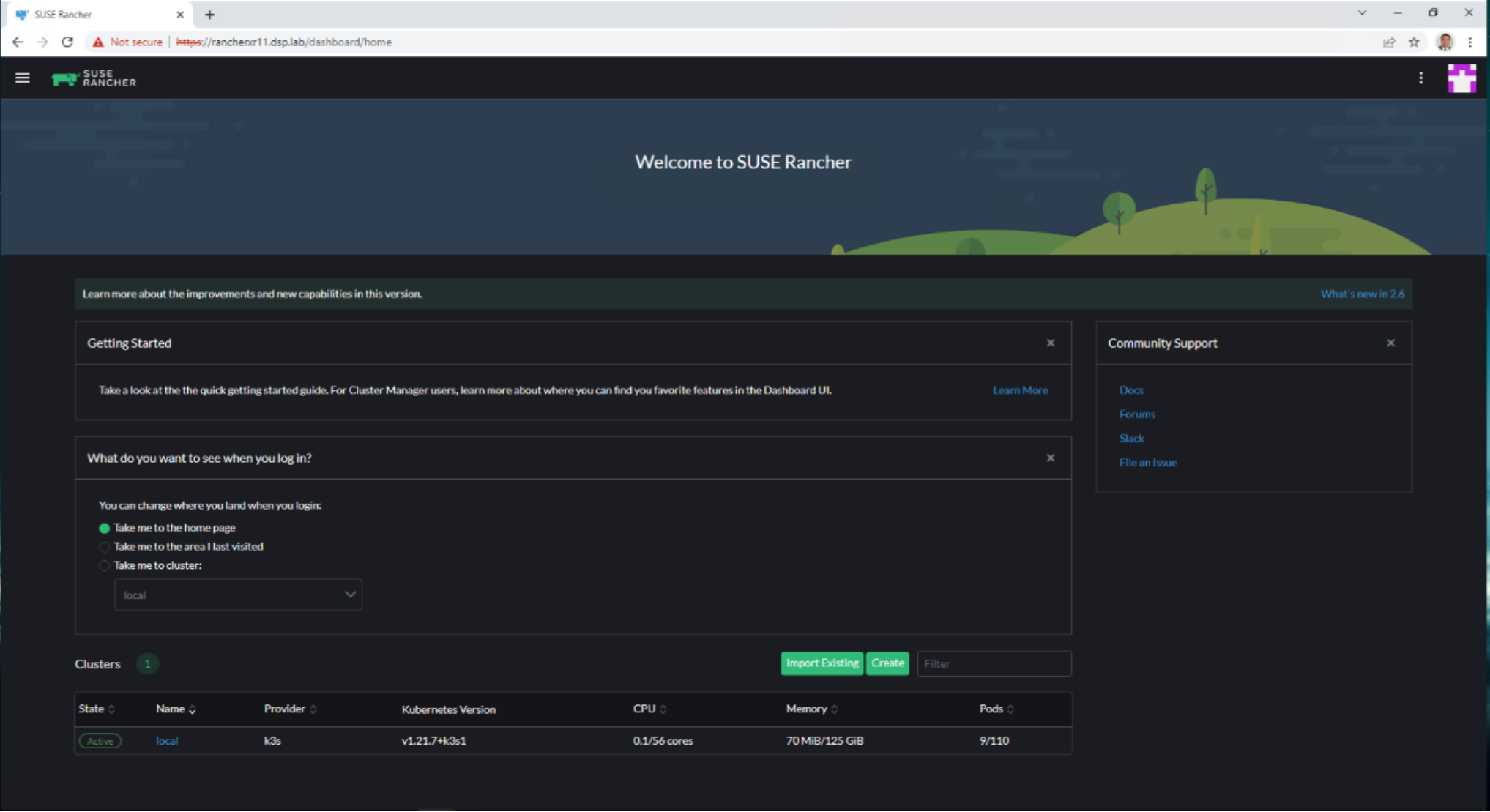
- Connect to Rancher User Interface via https (for example, https://rancherxr11.dsp.lab/dashboard/home)
As an option, you can create an SSH tunnel to access SUSE Rancher.
Note: This optional step is useful in cases where NAT routers or firewalls prevent the client web browser from reaching the exposed SUSE Rancher server IP address, port, or both. This step requires that a Linux host is accessible through SSH from the client system and that the Linux host can reach the exposed SUSE Rancher service. The SUSE Rancher hostname should be resolvable to the appropriate IP address by the local workstation.
To an SSH tunnel through the Linux host to the IP address of the SUSE Rancher server on the NodePort:
- Enter the following command:
ssh -N -D 8080 user@Linux-host
- From the local workstation web browser, change the SOCKS Host settings to 127.0.0.1 and the port to 8080.
CAUTION: This configuration routes all traffic from the web browser through the remote Linux host. When you are finished, ensure that you close the tunnel and restore the previous SOCKS Host settings.
- Connect to the SUSE Rancher web UI and configure SUSE Rancher:
- On the client system, use a web browser to connect to the SUSE Rancher service.
- Enter a new Admin password in the field provided.
CAUTION: On the second configuration page, verify that the Rancher Server URL is set to the hostname specified when creating the SUSE Rancher Helm Chart custom resource, and that the port is set to 443. For example, rancherxr11.dsp.lab:443.
To further optimize deployment factors, leverage the following practices:
- Availability: In instances where a load balancer is used to access a K3s cluster, deploying two additional K3s cluster nodes, for a total of three, will automatically make SUSE Rancher highly available.
- Security: The basic deployment steps described in the preceding section are for the deployment of SUSE Rancher with automatically generated, self-signed security certificates. Other options are to have SUSE Rancher create public certificates using the Let’s Encrypt application that is associated with a publicly resolvable hostname for the SUSE Rancher server, or to provide preconfigured, private certificates. See the SUSE Rancher Choose your SSL Configuration section for more information.
- Integrity: This deployment of SUSE Rancher uses the K3s etcd key/value store to persist its data and configuration, which offers several advantages. With a multinode cluster and this resiliency through replication, having to provide highly available storage is not needed. In addition, backing up the K3s etcd store protects the cluster and the installation of SUSE Rancher and permits restoration of a given state.
After the successful deployment of the SUSE Rancher solution, review the SUSE Rancher product documentation for information about how downstream Kubernetes clusters can be deployed, imported, managed, and accessed.
Setting up K3S downstream clusters in Rancher
Rancher simplifies the creation of K3S Kubernetes clusters by allowing you to create them through the Rancher UI rather than more complex alternatives. Rancher provides multiple options for launching a cluster. Use the option that best fits your use case.
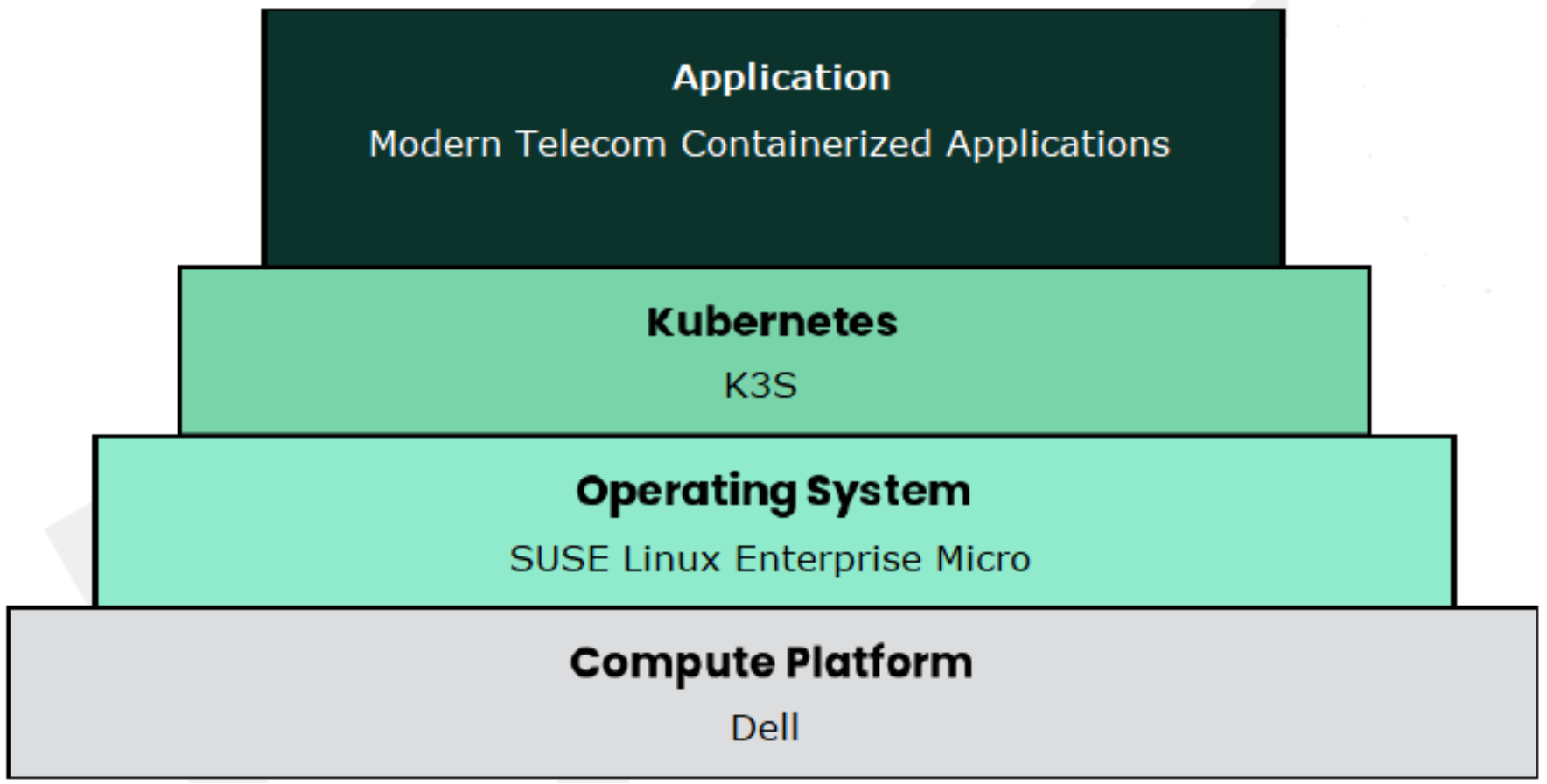
Figure 7. Modern telecom containerized applications stack
Note: For more information, see the Setting up Kubernetes Clusters in Rancher page.
To create a downstream custom cluster using the Rancher user interface, perform the following steps:
- Click Cluster Management, then click Create.
- Select RKE2/K3S then select Custom.
- Add a Cluster Name in the required field.
- From the Cluster Configuration section, select the Basics tab, then select the version of Kubernetes from the drop-down provided.
- Click to select the System Services options that you want to include, then click Create.
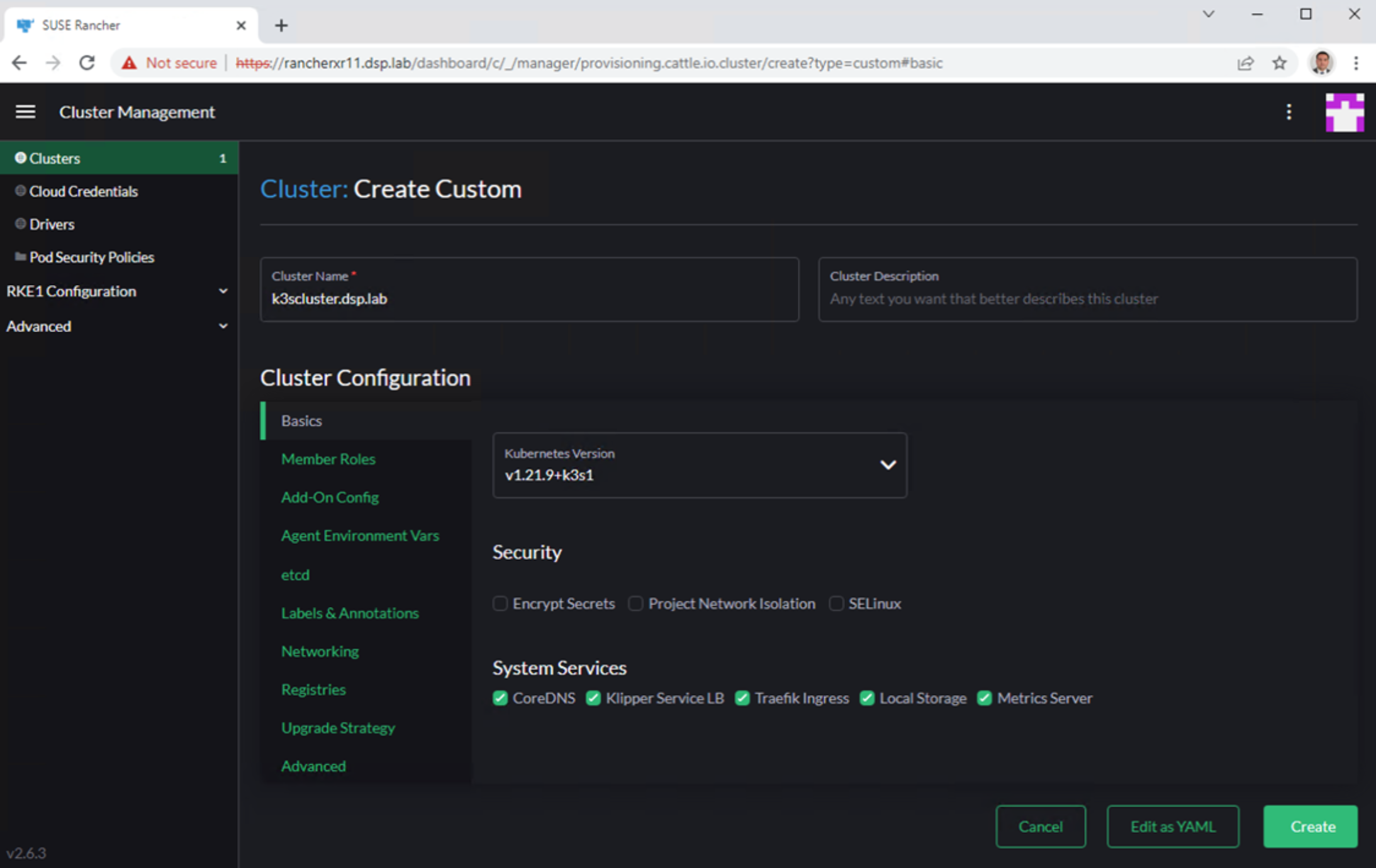
Figure 8. SUSE Rancher creating a custom cluster
There are 2 ways to configure the K3S cluster:
- High Availability (HA)
- Standalone
Setting up K3S high availability cluster
To set up the K3S server, perform the following steps:
- From the Cluster Management screen, click the Clusters link in the left navigation panel.
- Click to select the cluster to configure.
- Click the Registration tab.
- From the Step 1 section, click to place a check in the etcd and Control Plane boxes.
- From the Step 2 section, copy all the text in the Registration Command box as shown in the figure below.
- Run the information from the Registration Command section in each of the existing Linux systems you want to register.

Figure 9. Creation of K3S server HA custom cluster in SUSE Rancher
To set up the K3S agents, perform the following steps:
- From the Cluster Management screen, click the Clusters link in the left navigation panel.
- Click to select the cluster to configure.
- Click the Registration tab.
- From the Step 1 section, click to place a check in the Worker box.
- From the Step 2 section, copy all the text in the Registration Command box as shown in the figure below.
- Run the information from the Registration Command section in each of the existing nodes you want to register.
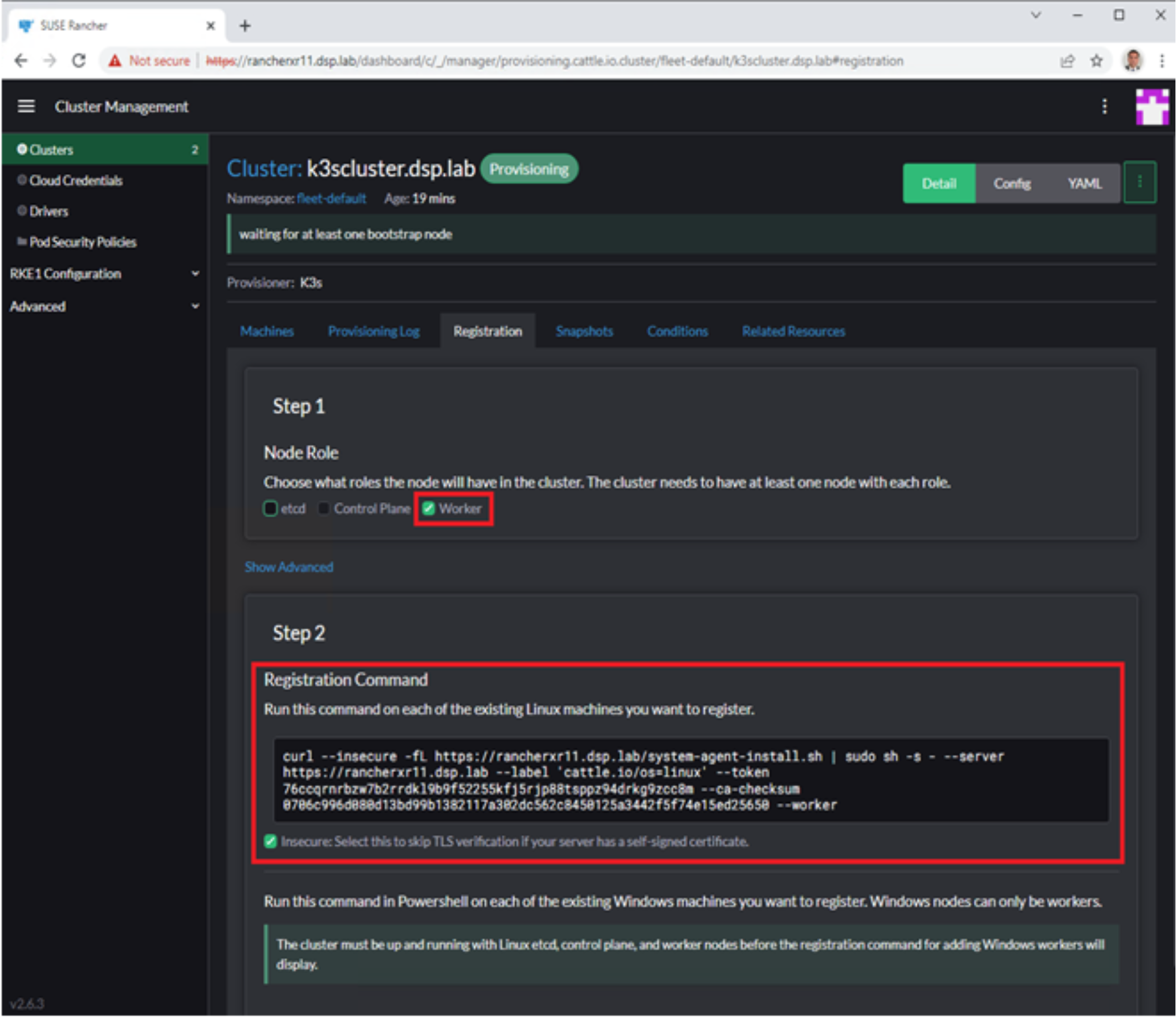
Figure 10. Creation of K3S agent HA custom cluster in SUSE Rancher
All K3S servers and agents join the K3S HA cluster and display in Cluster Management after they are registered.
Setting up K3S standalone cluster
To set up a K3S standalone cluster, perform the following steps:
- From the Cluster Management screen, click the Clusters link in the left navigation panel.
- Click to select the cluster to configure.
- Click the Registration tab.
- From the Step 1 section, click to place a check in the etcd, Control Plane, and Worker boxes.
- From the Step 2 section, copy all the text in the Registration Command box as shown in the figure below.
- Run the information from the Registration Command section in each of the existing nodes you want to register.
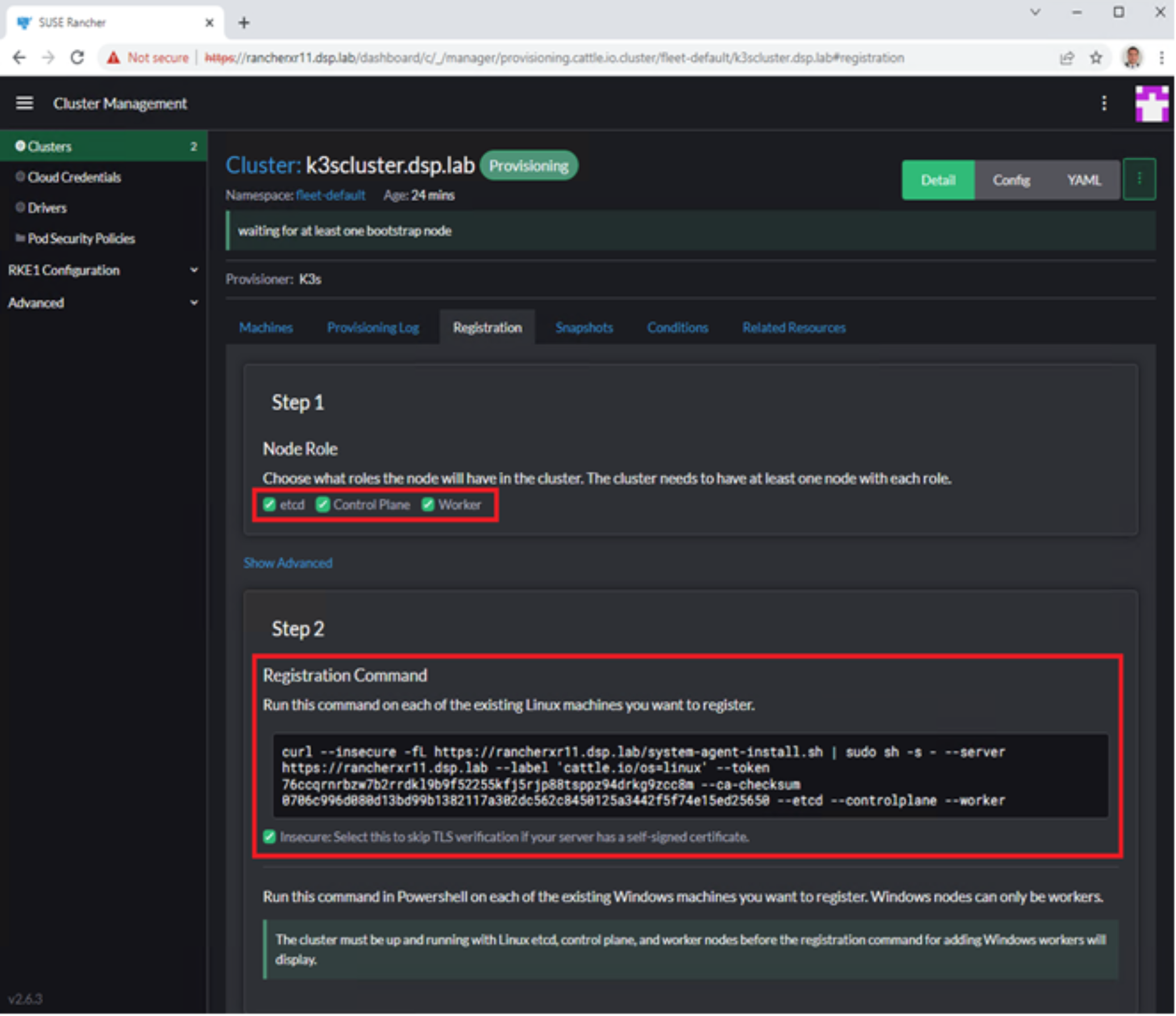
Figure 11. Creation of K3S standalone custom cluster
The K3S standalone cluster displays in Cluster Management after it is registered.
Continuous delivery
Rancher Continuous Delivery is powered by Fleet, which comes preinstalled with Rancher. Fleet is GitOps at scale, designed to manage up to a million clusters. and is lightweight enough that is works great for a single cluster. Fleet shows its true performance capabilities when used with many clusters, deployments, or teams in a single organization.
Fleet can manage git deployments of raw Kubernetes YAML, Helm charts, Kustomize, or any combination of the three. Regardless of the source, all resources are dynamically turned into Helm charts and used as the engine to deploy everything in the cluster. This gives you a high degree of control, consistency, and auditability. Fleet focuses not only on the ability to scale but provides a high degree of control and visibility to exactly what is installed on the cluster. To access Fleet, click the Continuous Delivery option in the Rancher UI. For more information, see the Fleet website.
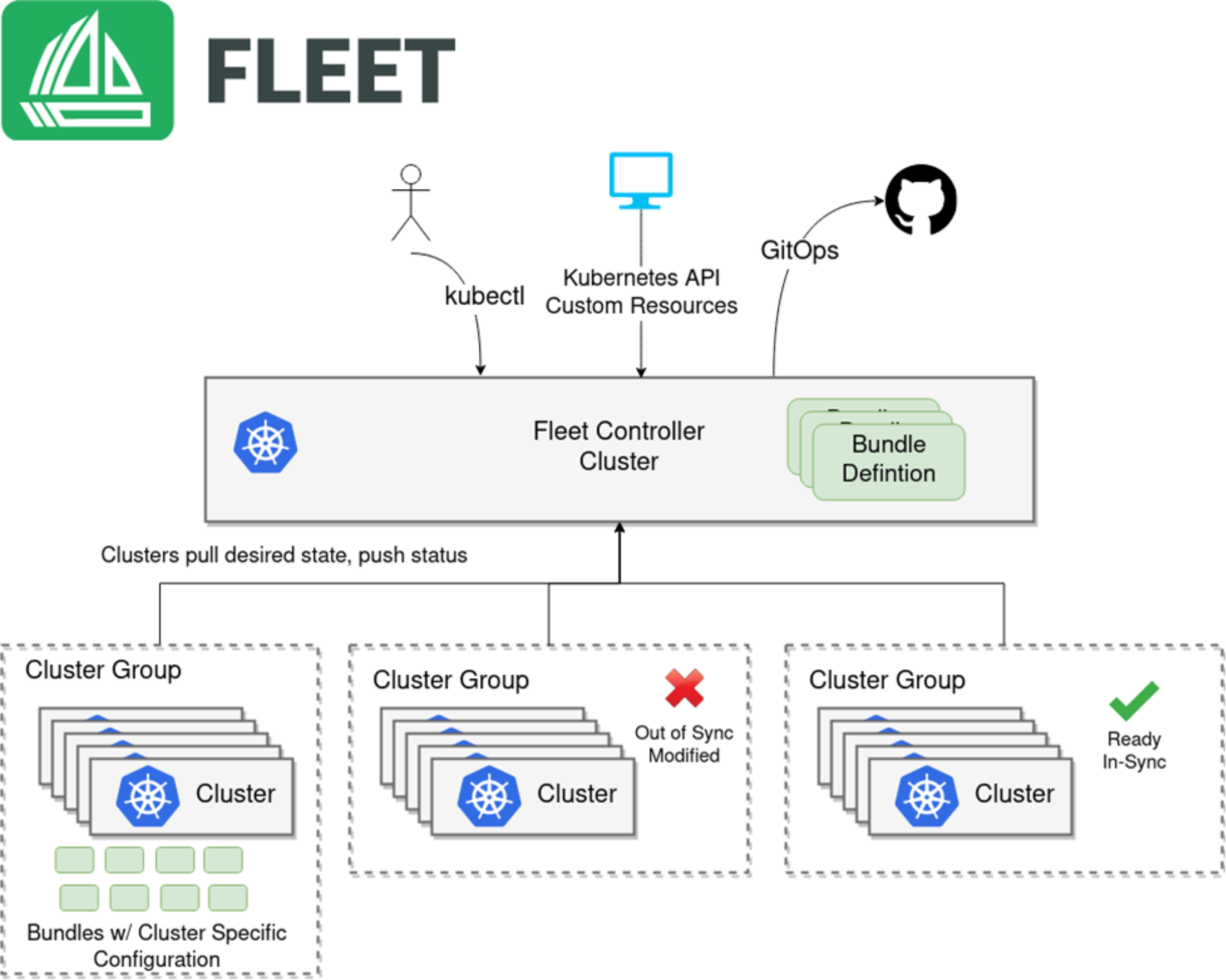
Figure 12. SUSE Rancher Fleet
