Home > APEX > Cyber & Data Protection > White Papers > Introduction to Dell APEX Backup Services > Overview of services and features
Overview of services and features
-
The following figure shows the services and features with APEX Backup Services.
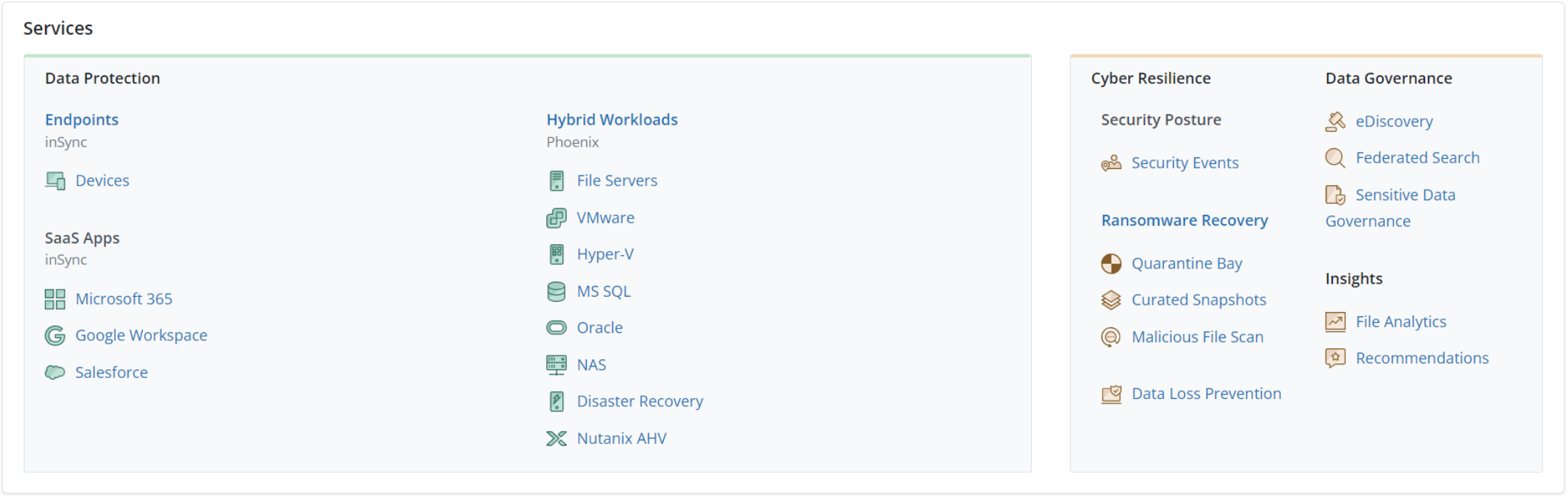
Figure 17. Overview section lists services and features
APEX Backup Services are categorized as:
- Data Protection
- Endpoints
- SaaS Apps
- Hybrid Workloads
- Data Governance
- eDiscovery
- Federated Search
- Sensitive Data Governance
- Cyber Resilience
- Security Posture
- Ransomware Recovery
- Insights
- File Analytics
- Recommendations
Data Governance
Legal Hold (eDiscovery)
With Legal Hold, you can preserve user backup data and avoid data deletion. When you keep a user on Legal Hold, the backup data for that user is excluded from compaction.
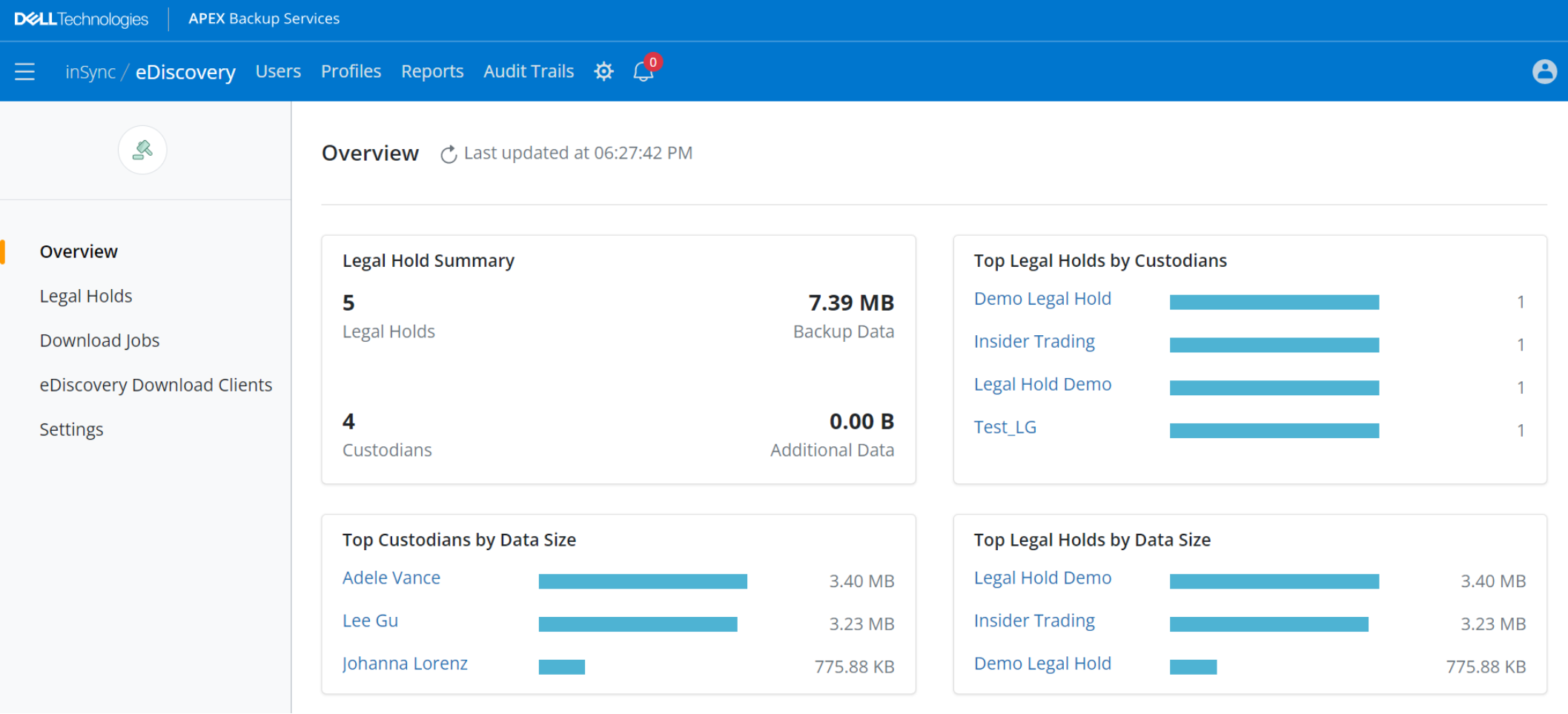
Figure 18. eDiscovery dashboard
APEX Backup Services does not delete the data that the user backs up from any endpoint device. Administrators can analyze user data by using eDiscovery tools.
When you put a user on Legal Hold, the user data from endpoints such as laptops and mobile, and from cloud applications is preserved.
Federated Search for backed up data
APEX Backup Services has a unique capability that allows you to centrally perform a global-federated-metadata search across all users and workloads in the backup, from a single pane of glass. Federated Search extends the keyword-based search with metadata search to enhance investigative capabilities for security, legal, and forensic teams. Federated Search also supports of search of files and email messages using the different parameters available for files and email messages.
Note: Federated Search is only applicable to endpoints and SaaS apps.
Federated search is valuable across multiple use cases including:
- eDiscovery and forensic investigations: Locate relevant files to the investigation
- Security investigations: Find and delete malicious data in source and backup
- Compliance: Find and delete sensitive files in source and backup
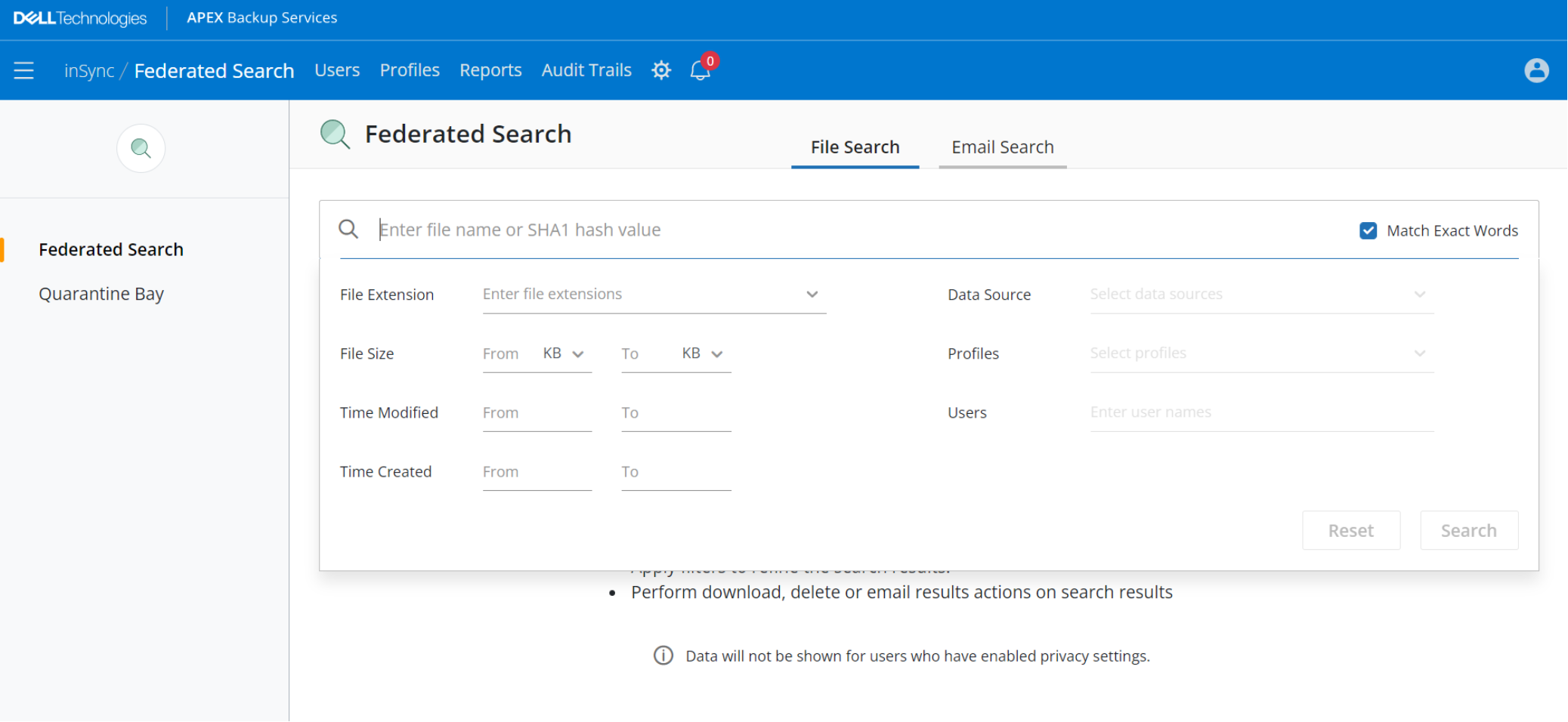
Figure 19. Federated Search > File Search
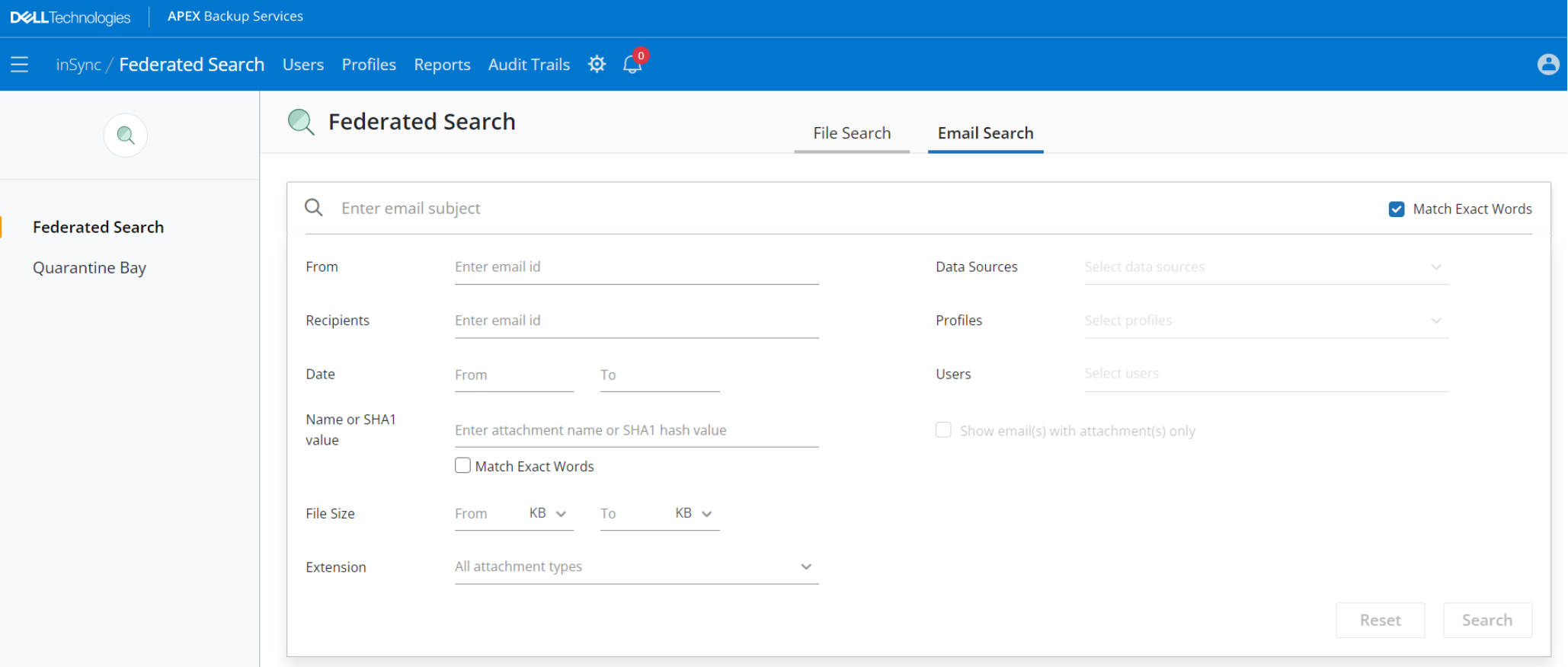
Figure 20. Federated Search > Email Search
Sensitive Data Governance
Sensitive Data Governance provides visibility of compliance breaches associated with end-user data in your organization. Sensitive Data Governance lets you proactively track, monitor, and get notified for data compliance risks in your organization.
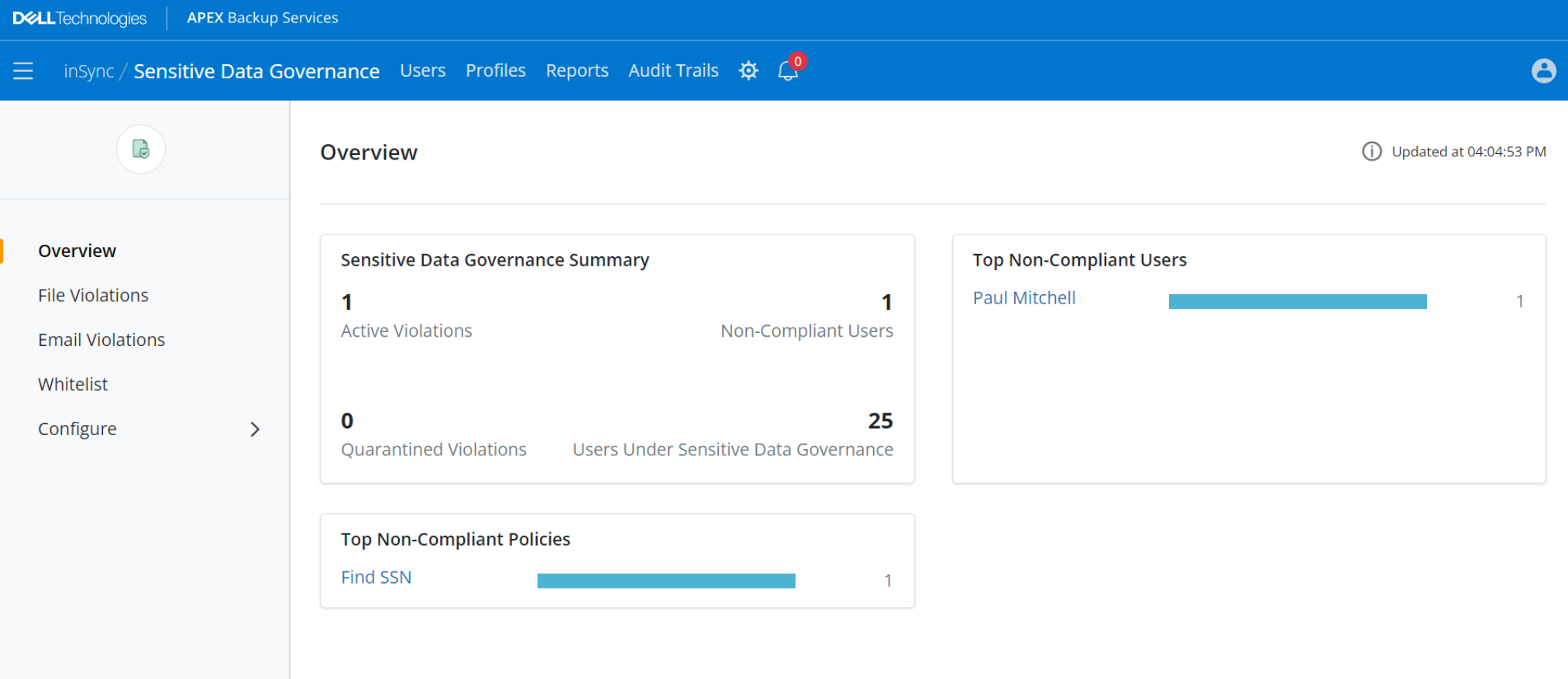
Figure 21. Sensitive Data Governance dashboard
The end-user data can be across any of the following data sources:
- Endpoints such as laptops, desktops, iOS, and Android devices
- OneDrive from Microsoft 365 services
- Emails that are backed up from Gmail, MAPI, and Exchange Online
- Google Drive
Sensitive Data Governance reports compliance violations for sensitive data that occurs in the email body, subject, and attachments. APEX Backup Services displays email messages with sensitive data on the Sensitive Data Governance Dashboard and allows administrators to download email messages in the EML file format.
Once enabled, Sensitive Data Governance:
- Enables defining sensitive data and scanning user data for compliance violations or risks of violations
- Allows you to locate end-user data that has violated a compliance policy
- Lets you generate a non-compliance report and view the visual representation to indicate adherence to compliance regulations in your company
Cyber Resilience
Ransomware Recovery
With APEX Backup Services, you have data protection with backup data isolated in a cloud platform and away from the customers’ infrastructure, providing immutable protection. Our cloud-native architecture prevents ransomware from encrypting your clean backup copies, and enables you to:
- Provide immutable data protection
- Identify and automate data protection for key business assets
- Isolate backup data from the data center network
- Secure data in flight and at rest
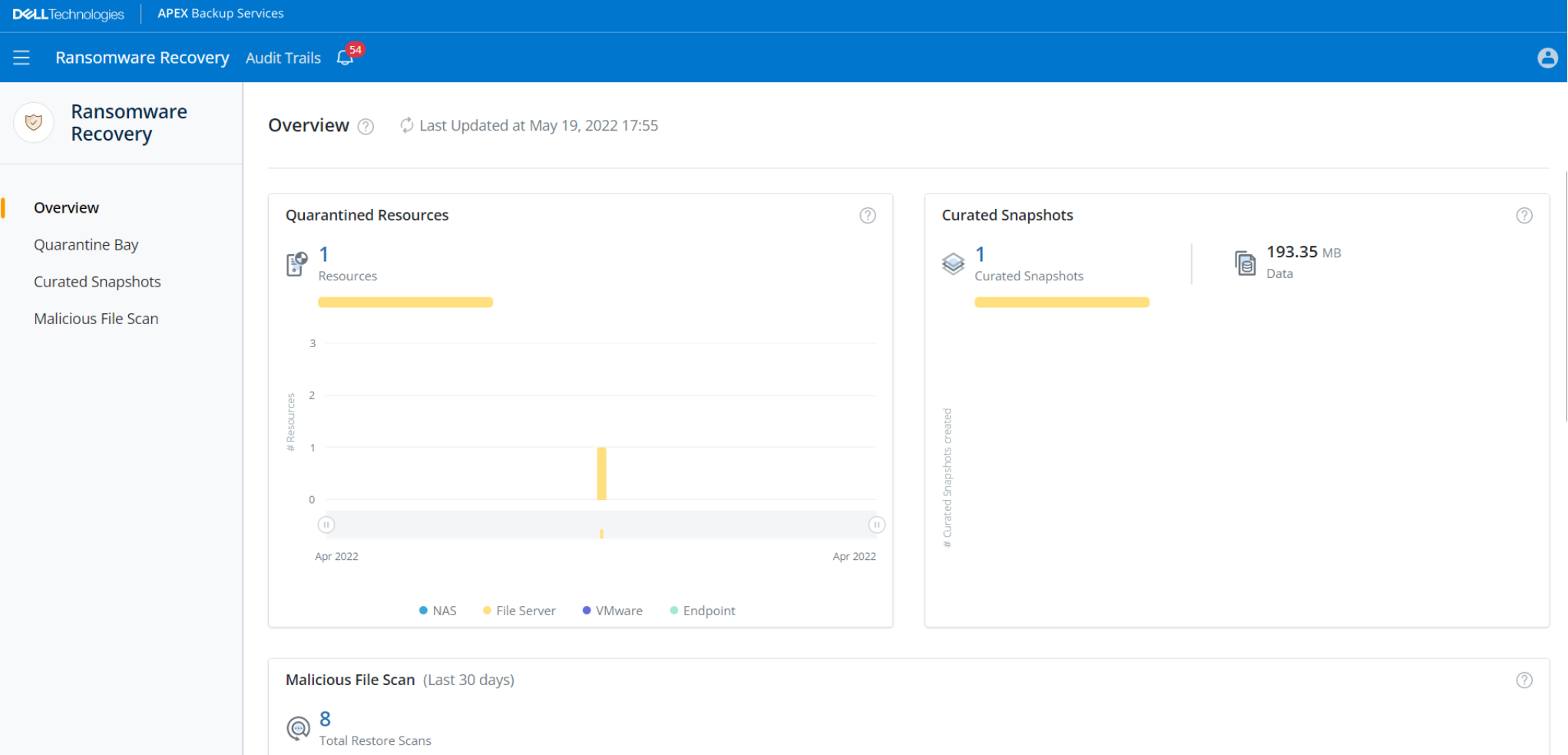
Figure 22. Ransomware Recovery dashboard
Data Loss Prevention
APEX Backup Services offers data loss prevention (DLP) features. These features enable IT administrators to maintain secure control over sensitive data on endpoint devices and respond to potential data loss events quickly if endpoint devices are lost or stolen. DLP is an effective solution that reduces the total economic impact of a lost or stolen laptop or mobile device for enterprises.
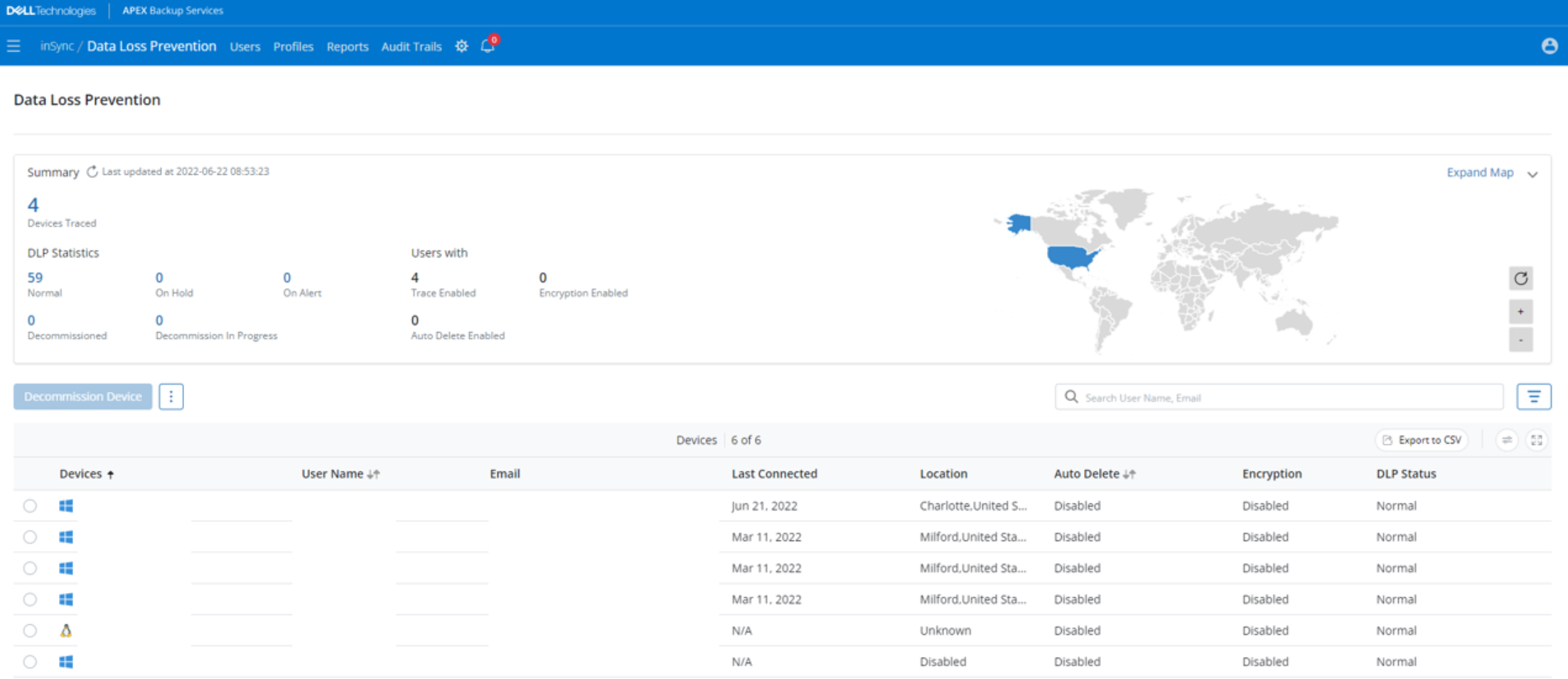
Figure 23. Data Loss Prevention dashboard
DLP provides powerful, multi-layered protection of critical data residing in your organization’s devices such as:
- Remote device encryption and sanitization capabilities to prevent data breach
- Geolocation capabilities to aid in device recovery
- Geofencing that can restrict access to data from specific IP addresses or locations
Insights
File Analytics
File Analytics provides you detailed insights which you can turn into a source of discovery to:
- Understand the type of data protected in your organization
- Understand the data growth trend and its impact on your storage consumption
- Visualize, manage, and plan for your storage requirements in the future
For an organization, the data that is generated can be classified as critical data, essential for running the business, and noncritical data, which may not be required to function a business. While it is essential to protect and preserve the critical data, noncritical data can be deleted or excluded from backup to eliminate the cost of protecting it.
Protecting the right information has the following benefits like:
- Reduces overhead of managing and maintaining the data for operational requirements
- Reduces compliance risks in accordance with the government-imposed data protection acts
- Saves storage cost
File Analytics provides dashboard using which administrators can determine the type of data that is being backed up in the organization, identify whether the data under protection is critical or noncritical, and which datasets are driving up the storage costs.
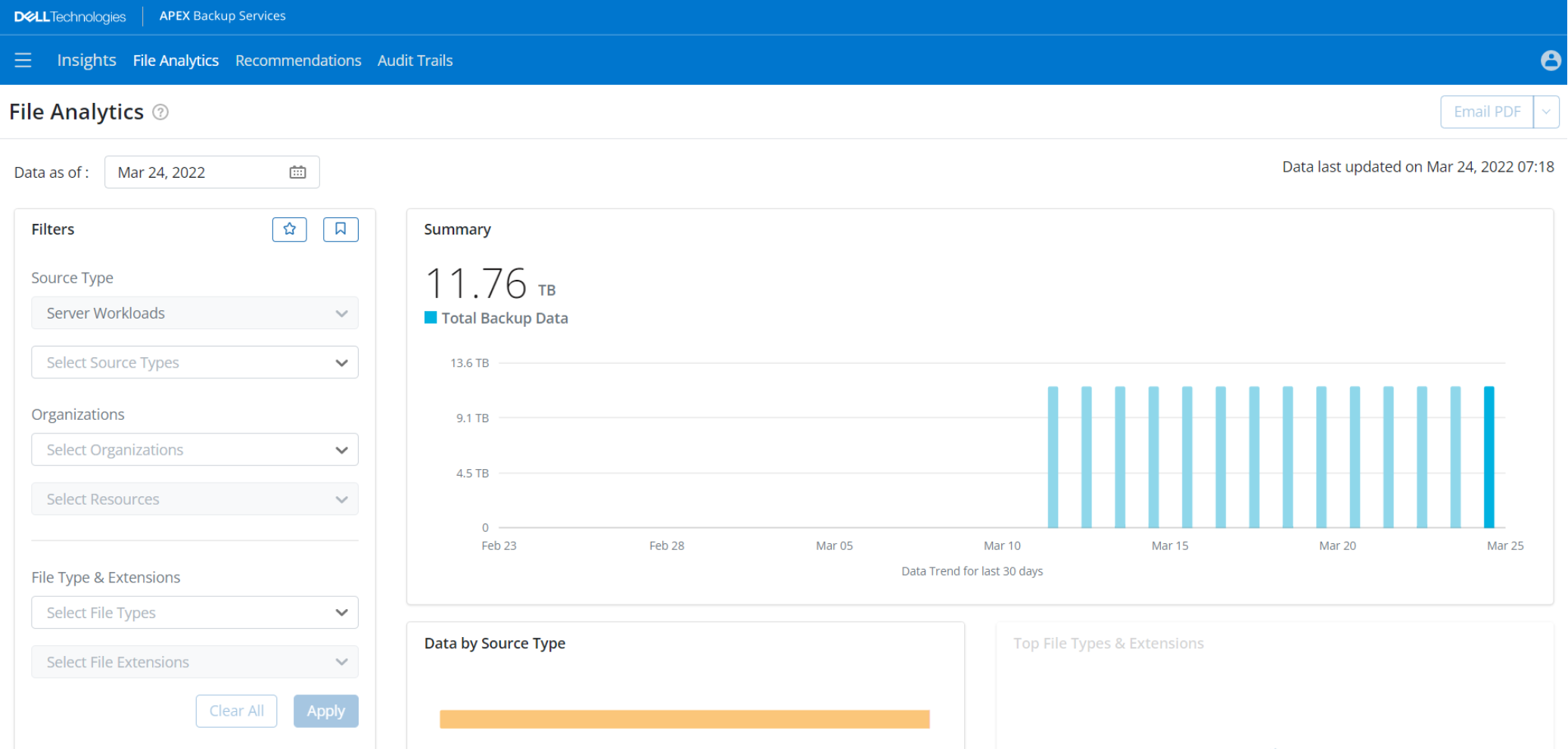
Figure 24. File Analytics dashboard
In parallel, you can use Recommendations, a smart service that automatically scans the data under protection and identifies the noncritical data and its total size in each of the backup set.
Recommendations
Recommendations is a smart service designed to identify and proactively inform administrators about the backup spends on the noncritical business data under protection and recommend necessary action to exclude it from backup and save costs.
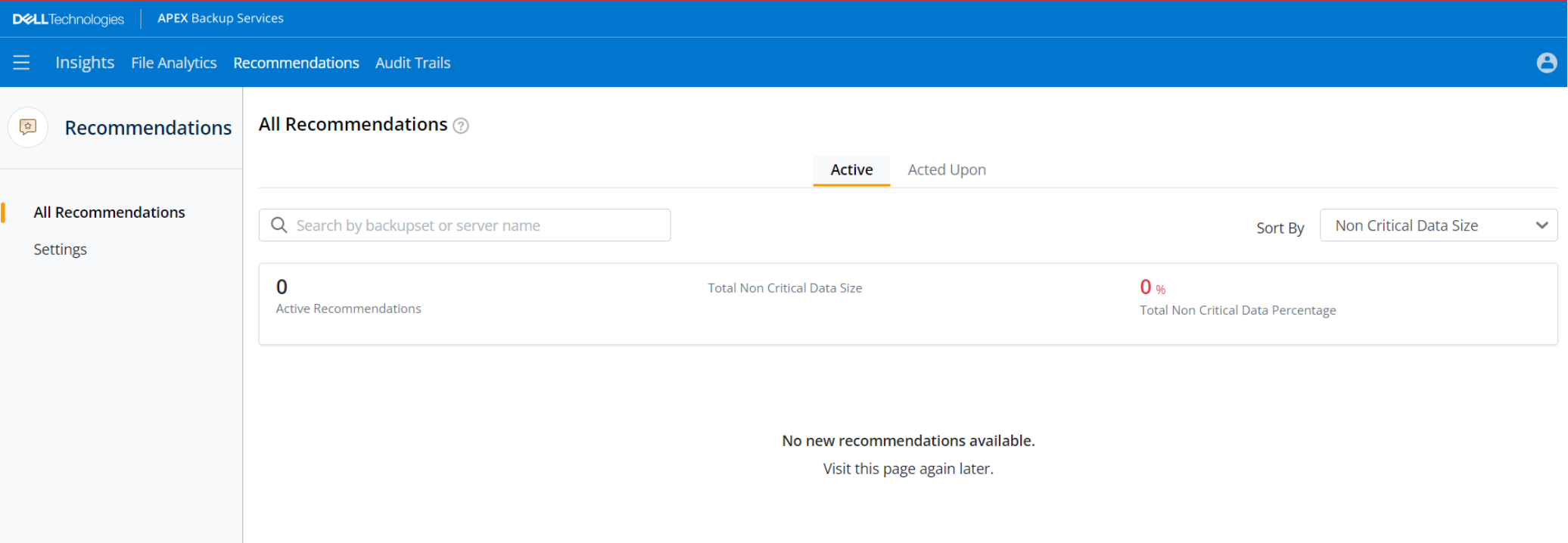
Figure 25. Recommendations console
Recommendations sits on top of File Analytics. File Analytics provide administrators detailed insights and enable them to identify whether the data under protection is critical or noncritical. Eliminating noncritical data requires effort. Even if administrators or users decide to eliminate the noncritical data on their own, it can be an overwhelming task to get rid of all the noncritical data.
Recommendations enable faster detection of noncritical files and save costs. They enable administrators to:
- Monitor activity and take real-time actions to stop the noncritical business data from being backed up
- Get unprecedented visibility into the storage and analyze the type of data under protection
- Save the storage costs by improving the content rules and backup policies
