Home > Workload Solutions > SAP > Guides > Dell Validated Design for High Availability for SAP with VMware and Red Hat on Dell PowerEdge Servers > Installing SAP
Installing SAP
-
Prerequisites
When installing SAP, ensure that:
- Operating systems are already installed on the servers
- Hostnames and IP addresses are configured
For fault tolerance at the network level, Dell Technologies recommends using active/passive network bonding devices. See Chapter 14. Configuring network bonding Red Hat Enterprise Linux 8 | Red Hat Customer Portal.
Installation tasks overview
Install the SAP components in the following order:
- ASCS instance
- Database instance and clustering
- Primary application server
- Additional application servers (at least one)
Prepare the file systems
On all the servers, run the following commands:
# mkdir -p {/sapmnt,/sapinst,/usr/sap/TR1/SYS}
# mount <nfsServerIP>:/sapmnt /sapmnt
# mount <nfsServerIP>:/sapinst /sapinst
# mount <nfsServerIP>:/sapsys /usr/sap/TR1/SYSInstall the ASCS instance on nwascs
Assign the cluster IP to the first node where the ASCS instance is running initially:
nwacsc01# cd /sapinst/SWPM
nwacsc01# ./sapinst SAPINST_USE_HOSTNAME=nwascs01Use the SWPM interface
Download the Software Provisioning Manager (SWPM). Choose the appropriate instance based on the following SAP NetWeaver version and architecture:
- ASCS instance
- Database instance and clustering
- Primary application server
- Additional application servers (at least one)
Install SAP NetWeaver 7.5
- Under SID id TR1:
- Use instance number 00.
- Clear the Using FQDN option.
- For all passwords, use <yourSecurePwd>.
- During the parameter review, confirm that the nwascs01 virtual name is used.
- Ensure that the user IDs that are specified in Table 11 are used.
- If a permissions error appears, change the ownership of the ASCS directory by running the following command:
chown -R tr1adm:sapsys /usr/sap/TR1/ASCS00
Post-installation tasks for ASCS and ERS
Install SAP HANA on the hana01 and hana02 servers
Ensure that:
- The three required file systems for the SAP HANA database (/hana/data, /hana/log, and /hana/shared) are already configured on the system.
- The system is fast enough to support the wanted workload.
Start by installing the empty database on both hosts so that you can use the latest SAP HANA patch release.
Note: While SWPM assumes that the installation media is used, it is recommended to install the latest SAP HANA patch packages instead of installing the base version first and then updating to the latest patch release.
- To add the SAP HANA cluster IP to the hana01 server, run the following command:
hana01# ip addr add 10.14.20.19/24 dev bond0
- On both servers (hana01 and hana02), run the following command:
# cd /sapinst/SAP_HANA_DATABASE/
# ./hdblcm –ignore=check_signature_file
Note:
Use the ignore parameter only if an SAP HANA database patch release is installed without creating a signature with SAPcar during the extraction.
Enter the values that are specified in Table 6 and Table 7.
Ensure that you enter the correct value for the sapsys group. Do not use the SAP HANA default value of 79.Import the SAP HANA database
On hana01, run the following command:
hana01 # cd /sapinst/SWPM
./sapinst SAPINST_USE_HOSTNAME=hana-ha
Install the primary application server on nwwrk01
In the SWPM interface:
- Run the following commands:
nwwrk01 # cd /sapinst/SWPM/
nwwrk01 # ./sapinst SAPINST_USE_HOSTNAME=nwwrk01
- Select Installing SAP NetWeaver 7.5 > SAP HANA Database > Installation > Application Server ABAP > High-Availability System > Primary Application Server Instance (PAS).
- Apply the following settings:
- Instance number 21.
- Clear the Using FQDN option.
- Other required parameters for the environment (such as SLD).
Install the additional application server on nwwrk02
- Run the following commands:
nwwrk02 # cd /sapinst/SWPM/
nwwrk02 # ./sapinst SAPINST_USE_HOSTNAME=nwwrk02
- In the SWPM interface, select Installing SAP NetWeaver 7.5 > SAP HANA Database > Installation > Application Server ABAP > High-Availability System > Primary Application Server Instance (PAS).
- Apply the following settings:
- Select instance number 22.
- Clear the Using FQDN option.
Cluster configuration
Install and set up a cluster quorum service
Red Hat strongly recommends using a quorum server for an SAP HANA failover cluster to prevent a “split brain” scenario when a network failure occurs. A “split brain” is when two databases in a cluster act as a primary database without specifying which one should be active. As a result, valid transaction requests could reach two databases, which would require a manual intervention to resolve after the network is back online. Otherwise, you would have to discard transactions on one side and accept data loss.
The quorum service itself is lightweight and can be run on any system on top of the normal workload of an existing server. The service can be installed in the following locations, ordered from most efficient to least efficient:
- On a physical or virtual server outside the VMware cluster that runs the SAP workload (like a central DNS server)
- On a virtual server on the VMware cluster that runs the SAP workload***
- Not installed at all
Note: The first option is better than having no quorum, because VMware uses SAN-based cluster communication in addition to network communication. Therefore, the quorum VM will not be started a second time when only a network outage happens.
- Install the required software on the quorum host:
sapquorum:# dnf -y install pcs corosync-qnetd
- Start the software:
sapquorum:# systemctl start pcsd.service
sapquorum:# systemctl enable pcsd.service
- Configure the quorum service:
sapquorum:# pcs qdevice setup model net --enable –start
- Verify that everything is running:
sapquorum:# pcs qdevice status net –full
- (Optional) If needed, allow the quorum service in the firewall:
sapquorum:# firewall-cmd --permanent --add-service=high-availability
sapquorum:# firewall-cmd --add-service=high-availability
Note: For more information about how to set up and use quorum servers, see the official Red Hat document: Configuring quorum devices Red Hat Enterprise Linux 8.
Configure the SAP HANA replication
Before configuring the SAP HANA replication, set up the hdbuser-store for a backup user. This design guide uses “backup” as the username.
On both hosts, run the following commands:
# su – th0adm
# hdbuserstore -i add backup localhost:30013@SYSTEMDB systemNote: For data protection reasons, create a backup user with the appropriate permissions on your databases. The SYSTEM user permissions can also be used.
To configure the replication:
- On the first node (which will become the primary database), create a backup, and then enable system replication by running the following commands:
hana01:# su – th0adm
# hdbsql -i 00 -U backup -d SYSTEMDB "BACKUP DATA USING FILE ('/tmp/foo')"# hdbsql -i 00 -U backup -d SYSTEMDB "BACKUP DATA FOR TH0 USING FILE ('/tmp/foo2')"
Note: Ensure that the backup file destination has enough free available space and is writable for the th0adm user.
- After running the backups, prepare the primary node for system replication:
th0adm@hana01:# hdbnsutil -sr_enable --name=Node1
- Add the second database server to the replication by running:
hana02:# scale unit – th0adm
th0adm@hana02:# HDB stop- Copy the security keys from the first server to the second server:
hana02:# scp root@hana01:/usr/sap/TH0/SYS/global/security/rsecssfs/key/SSFS_TH0.KEY/usr/sap/TH0/SYS/global/security/rsecssfs/key/SSFS_TH0.KEY
hana02:# scp root@hana01:/usr/sap/TH0/SYS/global/security/rsecssfs/data/SSFS_TH0.DAT /usr/sap/TH0/SYS/global/security/rsecssfs/data/SSFS_TH0.DAT
- Register the second node by running:
hana02:# su – th0adm
th0adm@hana02:# hdbnsutil -sr_register --remoteHost=hana01 --remoteInstance=00 --replicationMode=syncmem --name=Node2- Start the database on the second node by running:
hana02:# su – th0adm
th0adm@hana02:# HDB start- (Optional) Verify the status of the replication by running the following commands on the first node:
hana01:# su – th0adm
th0adm@hana01:# cdpy
th0adm@hana01:# python systemReplicationStatus.py
The following code snippet shows the output of a successful replication command:
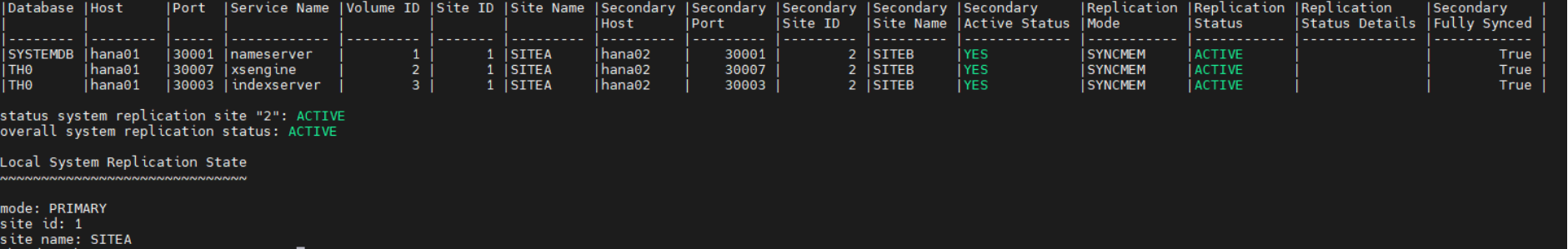
Figure 3. Replication status
Configure Pacemaker
To configure Pacemaker:
- Install the required packages on both SAP HANA nodes:
# dnf -y install pcs pacemaker resource-agents-sap-hana corosync-qdevice
# passwd hacluster
[enter a password for the user hacluster]
# systemctl enable pcsd.service; systemctl start pcsd.service
- Create the cluster with no cluster resources defined (run these commands on one host only):
# pcs host auth hana1 hana2
# pcs cluster setup clhana hana01 hana02
# pcs cluster start –all
- Add the quorum server into the cluster (run these commands on one host only):
# pcs host auth sapquorum
# pcs quorum device add model net host=sapquorum algorithm=ffsplit
- Verify that the quorum configuration succeeded:
# pcs quorum config
Options:
Device:
votes: 1
Model: net
algorithm: ffsplit
host: sapquorum
- For information about the scenarios in which fencing is required, see Using the Pacemaker cluster to automate startup on failure.
- For the configuration steps, see Configuring fencing in a Red Hat High Availability cluster Red Hat Enterprise Linux 8.
Red Hat supports two fencing mechanisms: power fence agents and I/O fence agents. For more information, see Fencing in a Red Hat High Availability Cluster - Red Hat Customer Portal.
Dell SAP engineering used VMware fencing, as described in: How do I configure a stonith device using agent fence_vmware_soap in a Red Hat High Availability cluster with pacemaker? - Red Hat Customer Portal.
- Configure the srConnectionChanged hooks on both cluster nodes:
- Stop the database instances:
hana01:# su – th0adm
th0adm@hana01:# HDB stophana02:# su – th0adm
th0adm@hana02:# HDB stop- Copy the files on both nodes:
[root]# mkdir -p /hana/shared/myHooks
[root]# cp /usr/share/SAPHanaSR/srHook/SAPHanaSR.py /hana/shared/myHooks
[root]# chown -R th0adm:sapsys /hana/shared/myHooks
- On both database nodes, modify the configuration file by editing the /hana/shared/TH0/global/hdb/custom/config/global.ini file as follows:
[ha_dr_provider_SAPHanaSR]
provider = SAPHanaSR
path = /hana/shared/myHooks
execution_order = 1
[trace]
ha_dr_saphanasr = info
- Create the /etc/sudoers.d/20-saphana file with the following content:
Note:
Adjust the values for th0 with your lowercase SAP SID of your database.
Adjust Node1 and Node2 with the database names given during replication setup.Cmnd_Alias Node1_SOK = /usr/sbin/crm_attribute -n hana_th0_site_srHook_Node1 -v SOK -t crm_config -s SAPHanaSR
Cmnd_Alias Node1_SFAIL = /usr/sbin/crm_attribute -n hana_th0_site_srHook_Node1 -v SFAIL -t crm_config -s SAPHanaSR
Cmnd_Alias Node2_SOK = /usr/sbin/crm_attribute -n hana_th0_site_srHook_Node2 -v SOK -t crm_config -s SAPHanaSR
Cmnd_Alias Node_SFAIL = /usr/sbin/crm_attribute -n hana_th0_site_srHook_Node2 -v SFAIL -t crm_config -s SAPHanaSR
th0adm ALL=(ALL) NOPASSWD: Node1_SOK, Node1_SFAIL, Node2_SOK, Node2_SFAIL
Defaults!Node1_SOK, Node1_SFAIL, Node2_SOK, Node2_SFAIL !requiretty
- Start the databases again:
hana01:# su – th0adm
th0adm@hana01:# HDB starthana02:# su – th0adm
th0adm@hana02:# HDB start- Configure the cluster resources:
- Enable the cluster maintenance mode. This ensures that the cluster software does not try to make any changes to the SAP HANA database replication until the configuration of the failover cluster is complete.
hana01# pcs property set maintenance-mode=true
- Define global parameters for all cluster resources:
# pcs resource defaults update resource-stickiness=1000
# pcs resource defaults update migration-threshold=5000
- Add the configuration for the SAP host resource:
# pcs resource create SAPHanaTopology_TH0_00 SAPHanaTopology SID=TH0 InstanceNumber=00 \
op start timeout=600 \
op stop timeout=300 \
op monitor interval=10 timeout=600 \
clone clone-max=2 clone-node-max=1 interleave=true
- Add the resource configuration for the active-passive SAP HANA database:
# pcs resource create SAPHana_TH0_00 SAPHana SID=TH0 InstanceNumber=00 \
PREFER_SITE_TAKEOVER=true DUPLICATE_PRIMARY_TIMEOUT=7200 AUTOMATED_REGISTER=true \
op start timeout=3600 \
op stop timeout=3600 \
op monitor interval=61 role="Slave" timeout=700 \
op monitor interval=59 role="Master" timeout=700 \
op promote timeout=3600 \
op demote timeout=3600 \
promotable notify=true clone-max=2 clone-node-max=1 interleave=true
- Add the virtual IP as a cluster resource:
# pcs resource create vip_TH0_00 IPaddr2 ip="10.14.20.10"
- Add resource constraints so that the different cluster resources run on the nodes where they belong respectively, such as the virtual IP address on the node with the writable primary database:
# pcs constraint order SAPHanaTopology_TH0_00-clone then SAPHana_TH0_00-clone symmetrical=false
# pcs constraint colocation add vip_TH0_00 with master SAPHana_TH0_00-clone 2000
- Disable maintenance mode on the cluster. (All the resources are now configured properly.)
pcs property set maintenance-mode=false
- Verify that the cluster is installed on hana01 by running:
hana01:~ # crm_mon -r1
The following output is displayed:
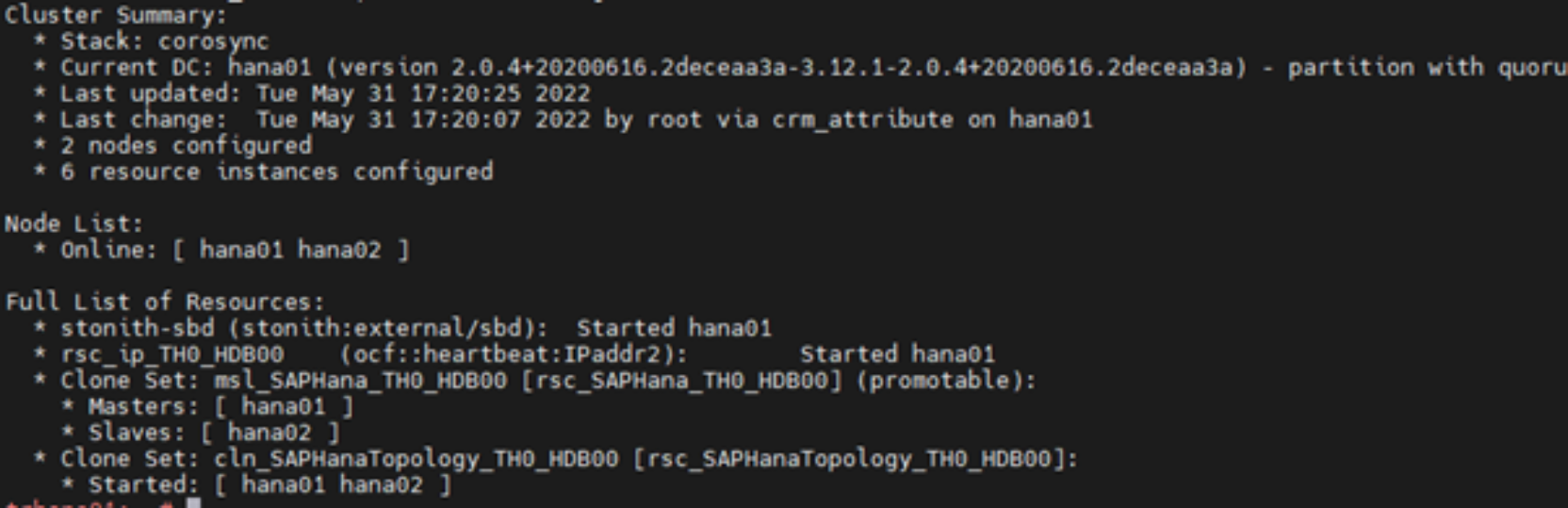
Figure 4. Checking the cluster installation status
- Verify the status of the replication by running:
trhana01:# su – th0adm
th0adm@hana01:# cdpy
th0adm@hana01:# python systemReplicationStatus.py
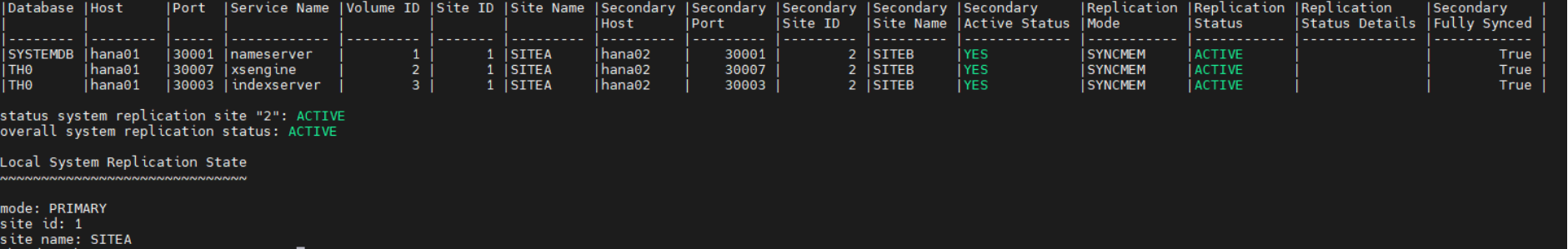
Figure 5. Checking the replication status
Configure VMware Fault Tolerance for the ASCS instance
To configure fault tolerance for the ASCS instance:
- Right-click the ASCS virtual server in the vCenter and select the option to enable Fault Tolerance, as shown in the following figure:
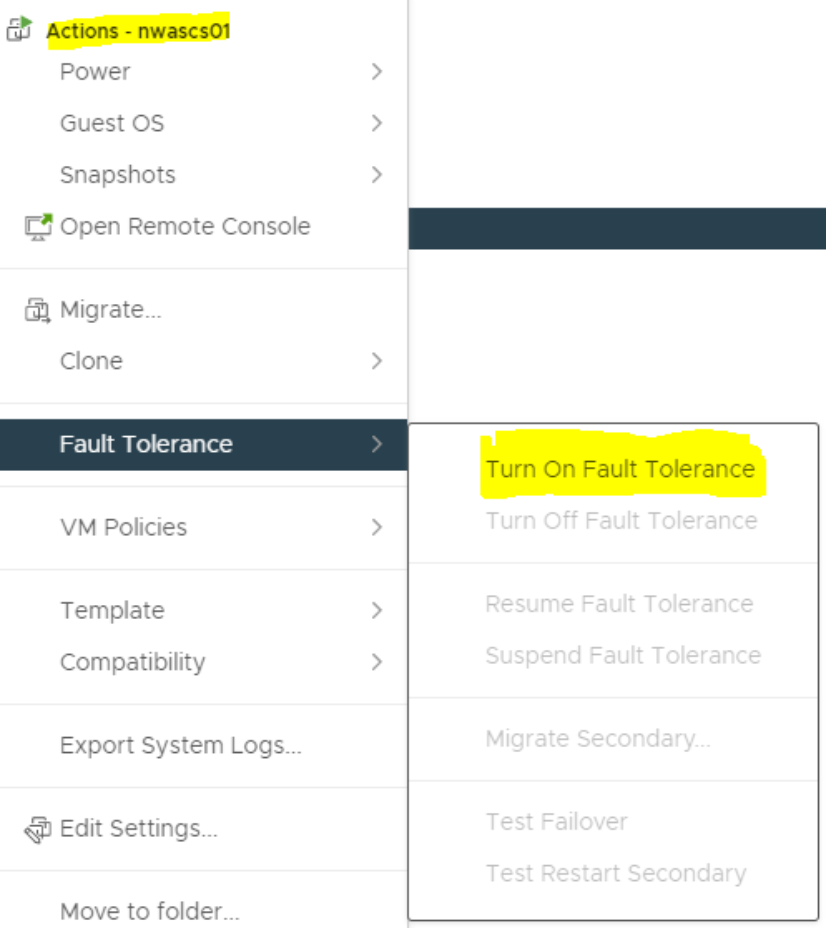
Figure 6. Turning on VMware Fault Tolerance
- Specify the datastore and ESXi host on which the secondary VM should reside.
The VM is turned on automatically after approximately one minute.
Defining host and VM groups to keep the virtual servers distributed on the ESXi servers
This example assumes that the VMware cluster is evenly spanned over two data centers. Automate the placement of the virtual servers through VM and host rules so that each data center has at least one SAP HANA database and one SAP application server.
Define the host groups on the Configuration tab of the vSphere cluster object.
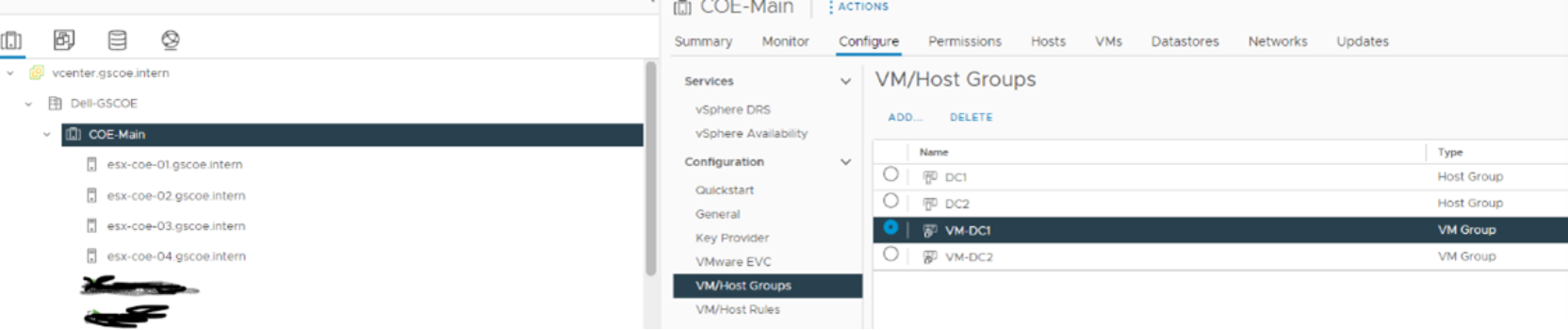
Figure 7. Configuring the vSphere cluster
Host Group 1: (DC1)
Contains all the hosts that are residing in the first data center.
Host Group 2: (DC2)
Contains all the hosts that are residing in the second data center.
VM Group 1: (VM-DC1)
Contains the virtual servers: hana01, nwascs01, and nwwrk01.
VM Group 2: (VM-DC2)
Contains the virtual servers: hana02, nwascs02.
Creating affinity rules.
Creating affinity rules keeps VMs in the correct data center by telling the vSphere dynamic resource scheduler (DRS) which virtual servers should run on which host group.
To create affinity rules:
- Select should run on hosts in group, as shown in the following figure:
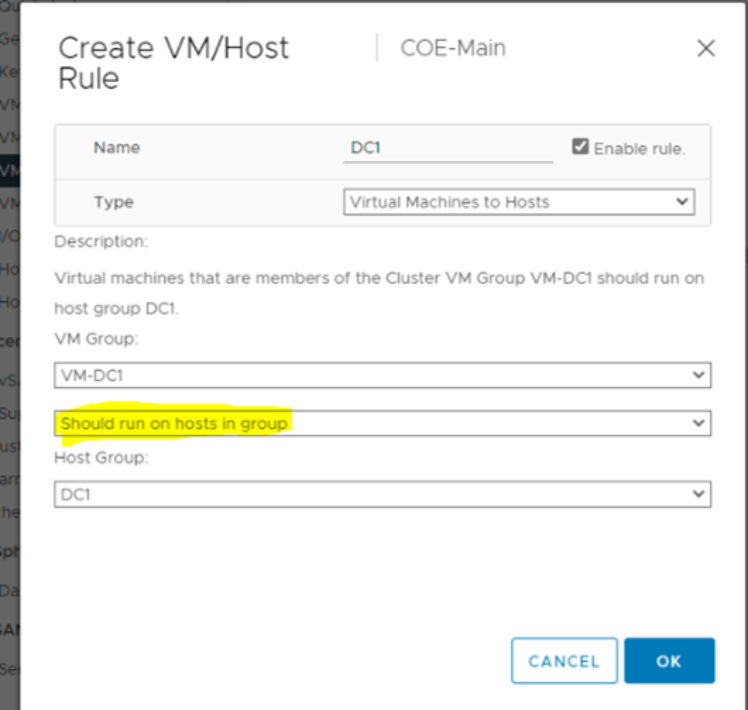
Figure 8. Creating affinity rules
This rule ensures that the virtual servers can be restarted in the second data center if the first data center is completely offline.
- Create a second rule for the DC2 hosts and VM-DC2s.
This step is similar to the preceding step, but using VM-DC2 and DC2 as parameters.
If it is necessary to manually place the secondary VM in the correct data center, use the fault tolerance menu of the primary VM, as shown in the following figure:
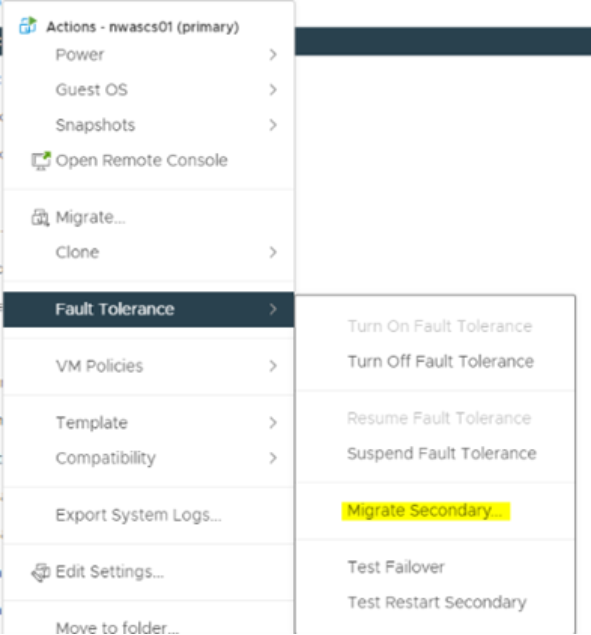
Figure 9. Positioning the second VM
