Home > Networking Solutions > Other Networking Solutions > uCPE Solutions > Guides > Virtual Edge Platform, SD-WAN, and uCPE Solutions Architecture Guide > Versa
Versa
-
Versa Networks Solution is made of three software components:
- Versa FlexVNF
- Versa Director
- Versa Analytics
Versa FlexVNF
At the heart of Versa Networks SD-WAN solution is the Versa FlexVNF. This is a highly available distributed virtual network services appliance that is built for multi-tenancy, dynamic elasticity, high-availability, and service chaining capabilities.
Versa FlexVNF is configured and managed through Versa Director which provides REST based API for integration with existing third-party management applications in the network. FlexVNF also exports a rich variety of security, NAT, SD-WAN, and audit logs for compliance and analytics derivation for the services running in the network to Versa Analytics. Versa Analytics can generate appropriate reports on a per tenant basis.
Versa FlexVNF is a software instance that allows users to seamlessly configure and manage Layer 4 through Layer 7 network services. Versa FlexVNF can be installed on Bare Metal using VEP4600 or VEP1400 platforms, or as a virtual machine on KVM or ESXi hypervisors.
Versa FlexVNF is a single software image that can be configured for the following functions:
- Branch Router or CPE
- Hub Router
- SD-WAN Gateway
- SD-WAN Controllers
Versa FlexVNF provides the following network services:
- Routing Services: L3 CPE (L3 customer-premises equipment), Route Reflector, Provider Edge, Carrier Grade NAT.
- Security Services: L3/L4 Firewall, Next Generation Firewall, Intrusion Detection and Prevention (IDP/IPS), Zero Day Attack Prevention, Network anti-virus and anti-malware, URL filtering, DDoS protection, DNS filtering, application detection and control, and several others.
- VPN Services: Site to Site IPsec VPN
- Network Services: DHCP Server and Relay, QoS, VRRP, BFD, and Ethernet OAM
- Software-Defined WAN (SD-WAN) with Link SLA Monitoring
- Application Delivery Controller – L3/L4 Load-Balancer
Versa Director
For service activation, Versa Director leverages the concept of service template and workflows. If multiple sites, branches or FlexVNF instances use a similar set of configurations, templates can be used to build a generic configuration that can be applied to one or more FlexVNF instances. Altering configurations across many software instances or nodes can be tedious and time-consuming, and templates save time by applying the necessary configurations and ensuring consistency across sites.
Versa Director also automates the discovery of a new branch deployment and configuration using pre-provisioned templates. High level interfaces between Director, FlexVNF and Analytics are depicted in Figure 8.
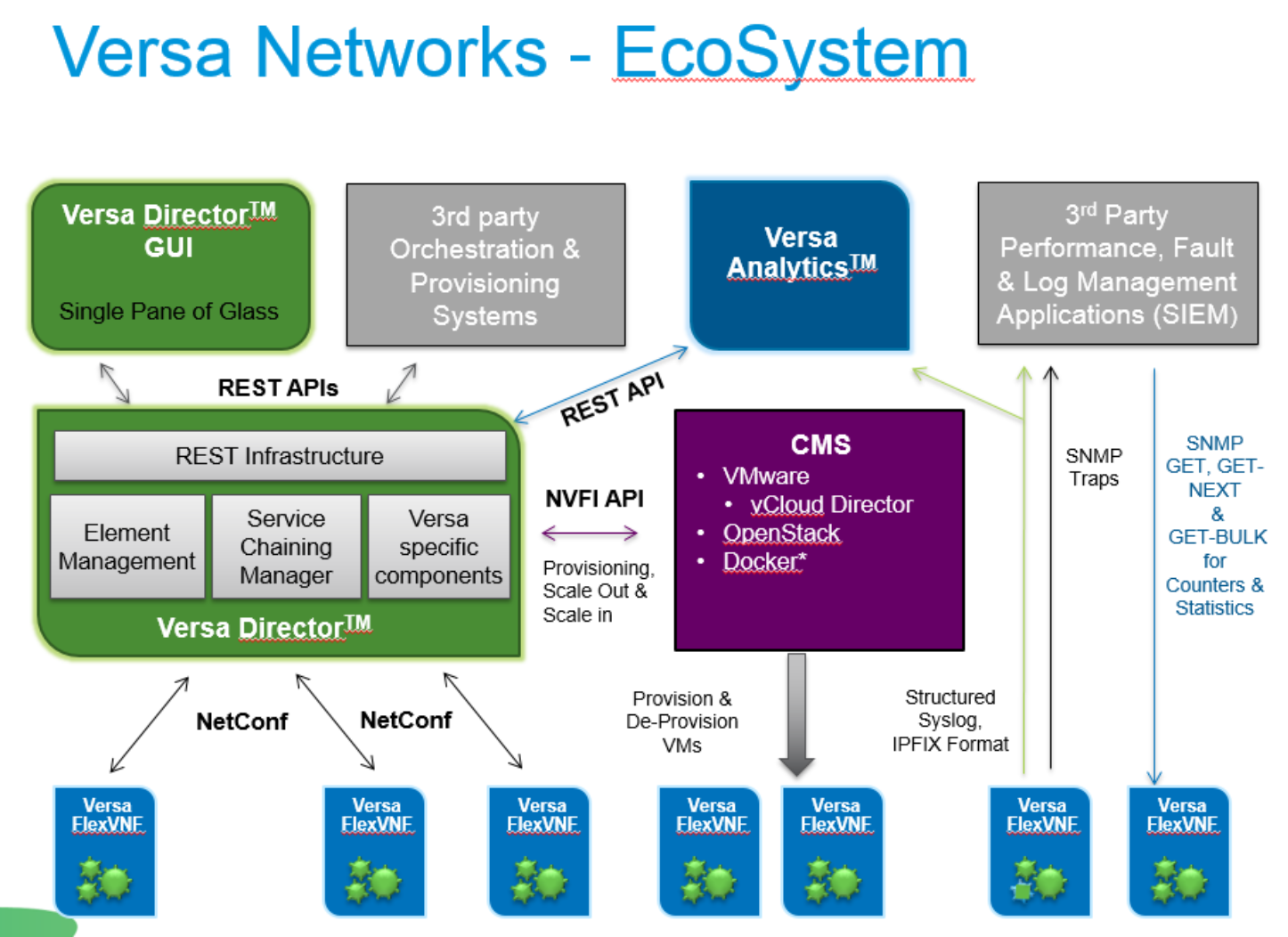
Figure 12. Interfaces connecting primary components of the Versa Solution
Versa Analytics
The Versa Networks solution also supports an Analytics Framework. Versa Analytics (VAN) is a multi-tenant carrier-class analytics engine that runs either on bare-metal or in a virtualized environment.
Versa Analytics assists administrators to perform tasks such as network planning, traffic/application analysis, network security analytics and behavior anomaly detection.
This provides a complete view into what is happening in the network, which applications are running, and what those applications are doing—in addition to insights about threat detection. Vera Analytics can provide description of the application or threat, the applications key features and behavioral characteristics, details on the users who are using that application, and the details about those who may be affected by a threat.
It also includes:
- Real time network security event monitoring
- Internal and external threat monitoring
- Zero day anomaly detection
- SD-WAN topology and SLA monitoring
The Versa Analytics Engine is a 360-degree view in to the activity on your network and help you analyze events from a current and historical perspective.
Solution architecture
The Versa Networks SD-WAN solution is composed of the high-level components that are depicted in Figure 9.
Figure 13. Versa SD-WAN Solution Components
Role of Versa FlexVNF in SD-WAN
Some of the features relating to connectivity which are supported on FlexVNF include:
- Secured Connectivity
- Segmentation: Support for multiple tenants and multiple VRFs
- Intelligent load-sharing of traffic over various access circuits
- Zero touch provisioning
- In band and out of band SLA measurement
- Centralized configuration, management, and policy enforcement
- Support for generalized templates
- Multiple Layer-3 protocols: Multi-protocol BGP, OSPF, Static, VRRP
- Multiple layer-2 protocols: Link Aggregation Control Protocol, Connectivity Fault Management.
- Hierarchical QoS including Adaptive Shaping
- Passive and Active monitoring for SaaS Applications
- Support for High Availability
- IPV6 support
The following list describes the features relating to network services that are supported on FlexVNF:
- Support for versatile service-chaining
- Support for Direct Internet Access
- Avoids sprawl of appliances with support for multiple services
- Support for High Availability with Stateful Replication
- IPV6 Support
Different features of FlexVNF are exercised depending on which role FlexVNF performs as branch CPE, SD-WAN gateway, or SD-WAN controller.
Versa SD-WAN Controller
The Versa SD-WAN Controller plays a key role in the solution and serves as a primary attachment point to the Virtual Private Network. The SD-WAN Controller provides a central control-plane entry point for the zero-touch deployment of branches. The Controller authenticates the branch FlexVNF instances using PKI certificates as part of an IKE exchange. The secure channel that is established using IKE provides a transport-channel between a branch node and the SD-WAN Controller for transport of routes, policy, and configuration. A single SD-WAN Controller can serve as the attachment point for VPNs belonging to several different customers.
The SD-WAN Controllers can be deployed in a cluster for redundancy and scale.
Versa Staging Sever (Optional for Bootstrapping and Secure Connectivity)
Versa Staging Server is a registration and staging entity for the deployment of all Branch-FlexVNF. This is an optional component which is required for a deterministic handoff of the Versa FlexVNF from Versa Networks to the appropriate administrator within the company deploying the Virtual Private Network (VPN). This is accomplished by a multi-factor authentication scheme consisting of the email-address and SMS number of the branch-administrator.
Staging is only necessary once during branch bootstrapping and no further communication is required to the staging server after the initial Attach procedure.
The same Versa Director can serve both as a Staging-Server and a VNF-Manager.
Multi tenant Versa analytics
The Versa Analytics is a big data based solution that analyses logs, events, and provides powerful reports, analytics, and feedback loop to the Versa Director. It natively integrates with third-party data reporting and existing SIEM products. Multiple FlexVNF at various branch-sites continuously provide monitoring information relating to link, network-path, and services to the Versa Analytics servers. Additionally, every service on the FlexVNF such as NextGen Security module and URL Filtering module generate flow-level and aggregate log messages which are consumed by the analytics platform. This information can be leveraged for functions such as capacity planning and security forensics.
For SD-WAN implementations, the Versa Analytics supports historical and real time data reporting.
Feedback information that is received from the Versa Analytics can be passed to the Versa Director for consumption. Each Versa FlexVNF at a remote branch site continuously provides monitoring information for link and services towards the Versa Analytics server.
The control plane in the architecture is implemented by
- Versa Director
- Versa Analytics
- Staging Server
- Versa SD-WAN Controller
The data plane is implemented by
- Versa FlexVNF
- SD-WAN Gateway
Versa Networks SD-WAN Secure Control and Data Overlay Tunnel solution
Versa Networks SD-WAN concepts relies on secure overlay tunnels (IPsec tunnels) for both Control plane and forwarding plane. The following section provides a description of the different tunnels encapsulation methods which can implemented between SD-WAN CPEs and controllers and among CPEs.
However, the way PKI framework differs between Control plane (CPEs to Controllers) and Forwarding Plane (CPEs to CPEs).
Using overlay technologies helps provide both traffic separation, isolation, and privacy.
To establish a secure Control plane, Versa Networks SD-WAN solution leverages regular IPSec /IKE with PKI framework if required.
Figure 14 provides a representation of key management call flow between branches for secure forwarding overlay tunnel establishment. Branch to Branch key exchanges is accomplished using MP-BGP which is tunneled through the secure Control channel that each CPE establishes with the SD-WAN Controllers. In this diagram, the Control channel is already encrypted using standard IPSec/IKE processes, making it impossible to see branch-to-branch key exchanges.

Figure 14. Call flow of branches for secure forwarding overlay tunnel establishment
Versa Networks SD-WAN routing framework
The Versa Networks SD-WAN solution relies on MP-BGP for route distribution. This is achieved through the Controllers acting as Route Reflectors through the secure overlay control channel that each CPE maintains on a per tenant basis with SD-WAN Controllers.
Versa Networks SD-WAN solution does not need IGP protocols for MP-BGP next-hop resolution since each CPE are directly connected to each other using secure overlay forwarding tunnels.
The main features of the Versa Networks SD-WAN routing solution are listed below:
- Multiple MPBGP instances each configured within a routing-instance or global hierarchy
- Each MPBGP instance corresponds to a tenant and can support multiple VRFs per tenant
- SD-WAN Controller (Route reflector) reflects the routes to other branches and send to other controllers as well (Route Reflector meshing)
- The route reflector can be different than Controllers where required
- Various topologies supported on a per VRF basis:
- Hub and spoke
- Partial-mesh
- Full-mesh
Although the default Versa SD-WAN model provisions a full forwarding mesh through IP Prefix advertisement in MP-BGP, an operator can configure other VPN topologies using the Versa Director.
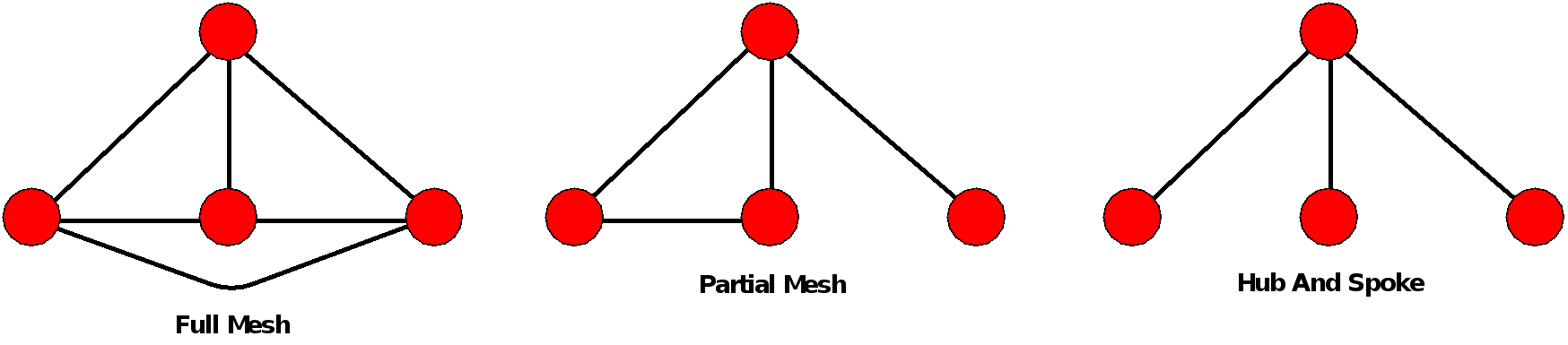
Figure 15. IP Forwarding topology Models.
The Versa SD-WAN Controller acts as a MP-BGP Route Reflector. Topology/connectivity is created through the exchange of BGP NLRI/Community. In addition to traditional information like routes and next hops, Versa Networks has enhanced and extended MP-BGP to exchange information relating to Key Management, Access Circuit State, and other state relating to SD-WAN.
The extension to MP-BGP relating to Key Management obviates the need to setup IKE based IPSec tunnels between various branch sites.
Support for overlapping Private IP Addresses is supported in the Versa Networks SD-WAN framework. The solution leverages overlay tunnels thus hiding end-users IP address schemes.
An existing private IP address space in use over an existing MPLS VPN architecture can be ported over the SD-WAN architecture. Overlapping private IP addresses among customers as used will remain the same.

