This section outlines the security best practices that help maintain confidentiality, integrity, and availability. It is a starting point when designing for security.
Home > Edge > Retail Edge > Guides > Dell Validated Design for Retail Edge with Deep North - Design Guide > Best practices and recommendations
Best practices and recommendations
-
Authentication, authorization, and accounting
Authentication, authorization, and accounting (AAA) is a framework or security principal that focuses on the concepts of identification, authentication, authorization, auditing, and accounting. Following this framework leads to a more effective security design.
Identification uniquely identifies the authenticating entity, for example, using a unique username or user ID number.
Authentication is the process of proving the identity of the entity that was provided. This is an example of providing the username and then the password to prove that the subject is the claimed identity, since they know the password.
Authorization is the process of verifying the access and privileges of the authenticated entity. This determines if the user has access to write to certain files.
Auditing is the process of tracking the actions of an entity throughout the system and creating a record of it through mechanisms like logging. Auditing supports accountability if logs are effectively created, stored, and secured to show what each unique entity has done on the system.
Applying these security principals is recommended when planning the implementation of this DVD.
A specific example is to ensure that the Ubuntu OS enforces users and services to always be uniquely identified and authenticated. Privileges should be defined for each type of account or role, and the OS is configured to audit user and services actions. Ideally, logs are centralized in a solution like a SIEM for secure and centralized storage with added benefits such as event correlation. The IEEE 802.1X standard supports port-based authentication for connecting devices over Ethernet. Implementing 802.1X is recommended for devices connecting to the network in the LAN, such as IP cameras if supported.
At a high level, IEEE 802.1X supports the AAA framework by identifying, authenticating, and then authorizing the device to connect to the Local Area Network (LAN). RADIUS is a protocol that supports 802.1X and the AAA framework. RADIUS also supports the logging of important events, such as connection requests. Open source and commercial implementations of RADIUS are available to support this functionality. Organizations can also investigate a more secure implementation of RADIUS, such as Diameter.
Defense in depth
Defense in depth is a principal of applying security in layers, as the following figure shows. It is about applying security controls from the physical level all the way to the application level. An example of this is to have physical defenses such as security guards, CCTV, and proximity cards to control access to the server room.
Additionally, security should be applied at the data layer by employing methods like encrypting data at rest. Another layer of security can be added by applying system-wide logging and monitoring. This principle makes it so that when an adversary breaks through one layer of defense—for example, by breaking into the server room—they are delayed or prevented from further data disclosure because the data on those hard drives is encrypted.
Figure 21. Defense in depth 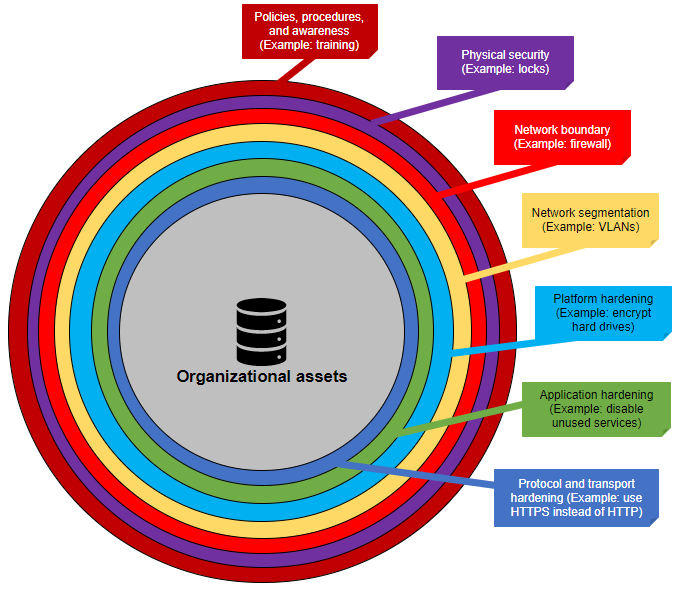
The DVD employs the principal of defense in depth by recommending best practices and validating security settings at the different deployment layers. A direct example is to apply host firewall rules on the Ubuntu host to prevent the ingress or egress of unauthorized traffic. However, if the host firewall rules are somehow circumvented and centralized auditing is configured on the host, then the organization can be warned of suspicious activity on the host.
Principal of least privilege
The principal of least privilege states that subjects, such as users, are only given the minimum necessary number of privileges to carry out their assigned job role and tasks. This applies to both executing tasks and assigning access privileges to data, including files.
The principal is an effective way to protect the integrity and confidentiality of data. An example is assigning only the required privileges to the Deep North user account on the Ubuntu OS. This user account should only have the privileges and access necessary to execute the tasks to successfully run the software.
Another example is not giving regular users excessive administrator privileges, since a compromised administrator account can cause more damage than an account with fewer privileges. Preventing regular users from being able to change IP configuration settings or other network-related settings is an example of this.
Zero trust
Zero trust is the security principal that nothing within the local area network (LAN) and or trusted network is automatically trusted. Another way to visualize zero trust is to assume that there is currently a threat within the LAN/trusted network. To follow the zero trust principal, implement security controls, such as segmenting the internal network into further microsegments and inspecting traffic between these segments. Other security control examples include using multifactor authentication, leveraging identity and access management solutions, and continuously monitoring and logging network activities.
When implementing and designing for this solution, consider all of the components (cameras, servers, and network equipment), how they connect, and how they communicate with each other.
Additional ways to apply this principal include:
- Validate the identity and connectivity from users and devices.
- Segment internal networks (such as using different VLANs or subnets) between the devices.
- Leverage VMware security settings for further segmentation and control.
High availability
Part of security is ensuring the availability of systems. Any downtime can cause significant harm to the organization.
High availability is a concept that ensures a certain uptime (or availability) of systems or system components. Goals of high availability include eliminating single points of failure, reducing the impact of faults, and employing the use of redundancy. Further details on high availability can be found in the High Availability chapter.
