This section covers the overall system design for Forescout. This software platform supplies cybersecurity functionality, allowing visibility to assets and vulnerabilities of the assets in a substation. Forescout provides other applications which can be integrated with each other. Forescout eyeInspect was the focus of this validation. Topics include the overall functionality of this product, how to design and implement Forescout deployments, as well as functional use cases validated for eyeInspect.
Forescout eyeInspect
The primary objective of eyeInspect is to offer comprehensive visibility into the substation, which provides a holistic understanding of the substation network. Visibility is key as any oversight regarding assets or network segments could result in the failure to detect potential vulnerabilities or malicious activities.
Once eyeInspect has full visibility of assets and networks, the system can proactively address potential vulnerabilities, risks, alerts, threats, network communication mappings, baselines, process values, and more. Moreover, eyeInspect offers users valuable dashboards, highlighting assets with the most critical vulnerabilities and risks. This aids in prioritizing and addressing the most important issues, which is beneficial when dealing with a large number of potential risks and vulnerabilities.
Network deployment considerations
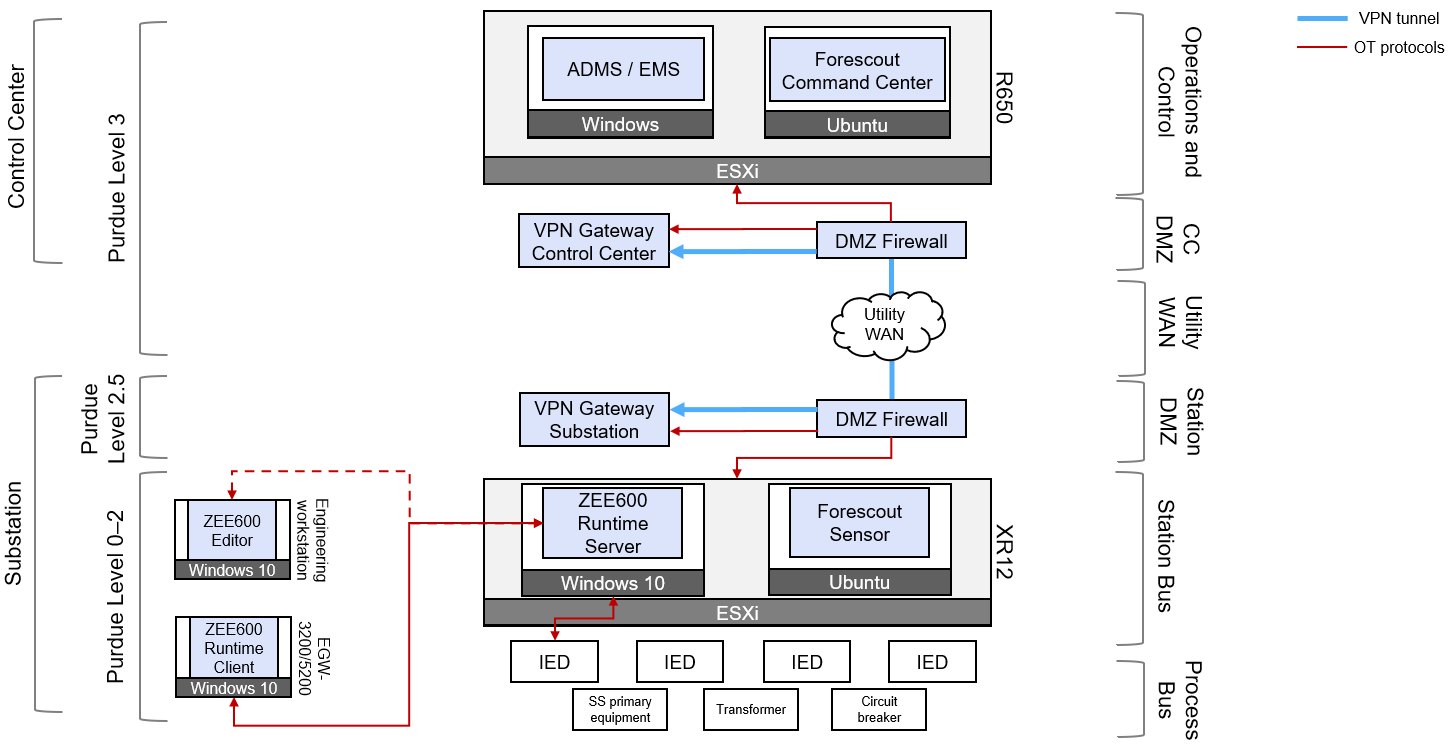
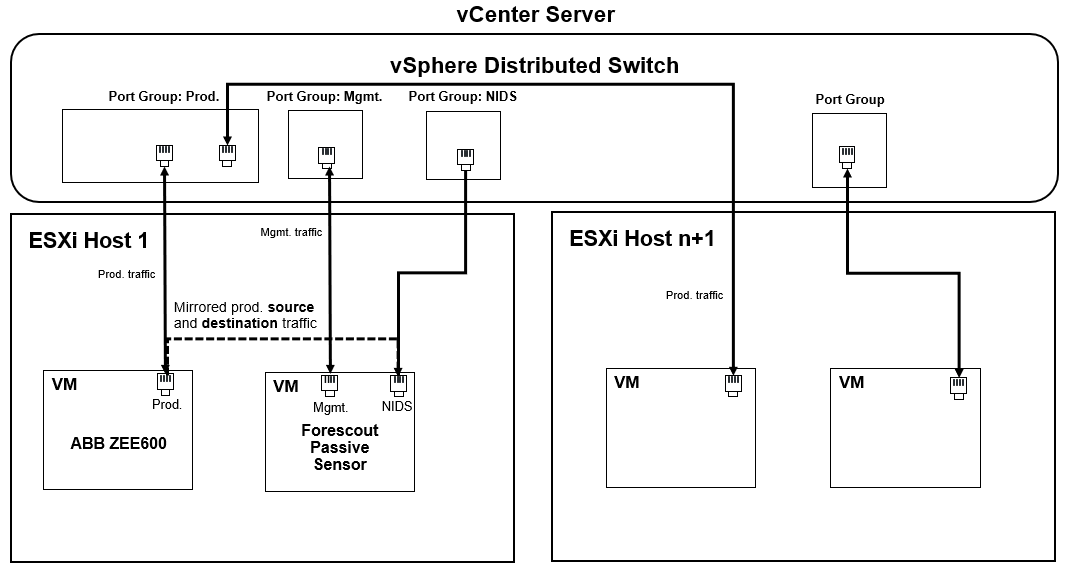
eyeInspect uses passive network monitoring as its primary method for gathering network and asset information. This validation was conducted for the use of eyeInspect's Passive Sensor strategically located at the substation. The sensor can be configured to ingest mirrored network traffic through methods such as the Switch Port Analyzer (SPAN) protocol. In the following figure, the sensor is shown to ingest SPAN data into its data interface while the sensor is managed and connected to the Command Center through its management (Mgmt.) interface.
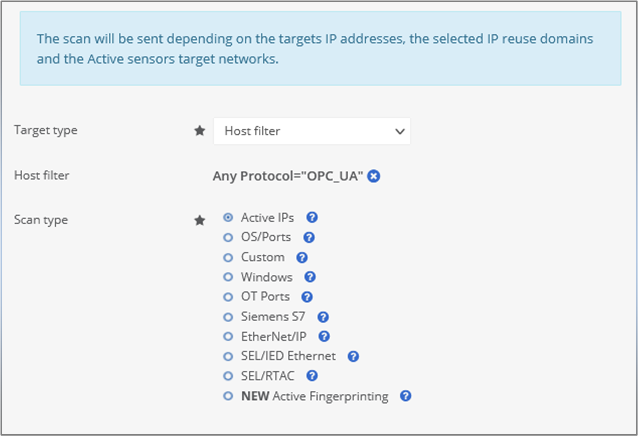
eyeInspect can also ingest data through its Active Sensor which can be configured for various devices, including industrial-type devices like programmable logic controllers (PLCs) and workstations. The Active Sensor conducts safe scans to avoid potential disruptions to industrial devices, as they may not be equipped to handle traditional IT scanning methods. By doing so, eyeInspect ensures that critical industrial systems remain secure and stable, while simultaneously offering valuable insights into their security and performance.

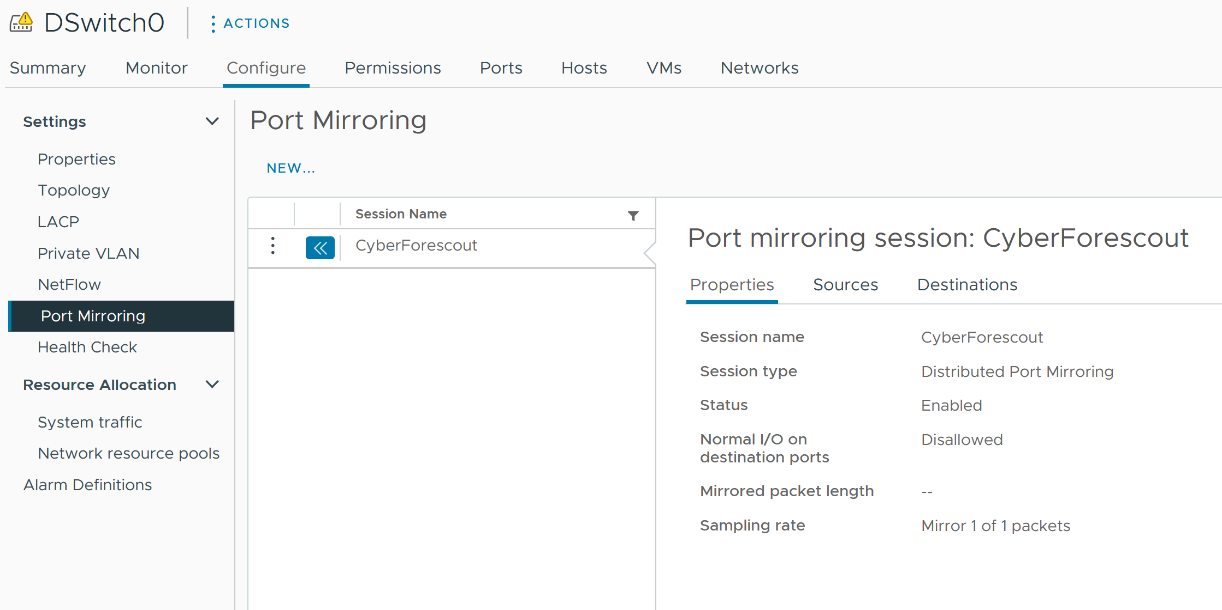
vCenter cluster networking considerations
There are some key considerations when deploying the sensor on a vCenter cluster. In a vCenter deployment, there is a virtual distributed switch (vDS) which acts as the main switch between all ESXi hosts in the cluster. For the sensor to passively ingest network traffic on a vCenter cluster, distributed port mirroring must be configured on the vDS. Overall, the user chooses the source of traffic to collect based on the virtual network port. The user then selects the destination port to send the traffic to. Users should be aware that there is a limitation where traffic cannot be mirrored across hosts, meaning from one ESXi host in the cluster to another. Follow the guidance in the subsequent sections for workarounds to this limitation.
PowerEdge XR12 deployment consideration
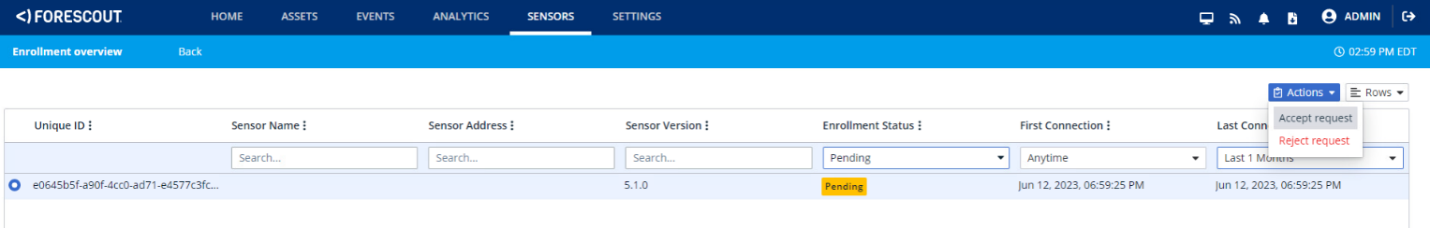
In certain scenarios, deploying eyeInspect software directly on a gateway can prove more efficient. This is advisable when the eyeInspect Sensor is in a separate network segment, distant from the Command Center server. As of the current date, the Dell PowerEdge XR12 has undergone validation to run the eyeInspect Sensor v5.1.0. For further details, see Platform hardening.
Test cases
Asset discovery
Forescout eyeInspect offers multiple methods to discover assets on the networks, such as passive and active sensors. The following test cases demonstrate the effectiveness of these features in allowing the utilities industry to gain insight into their network assets and reveal the underlying structure of the existing substation network.
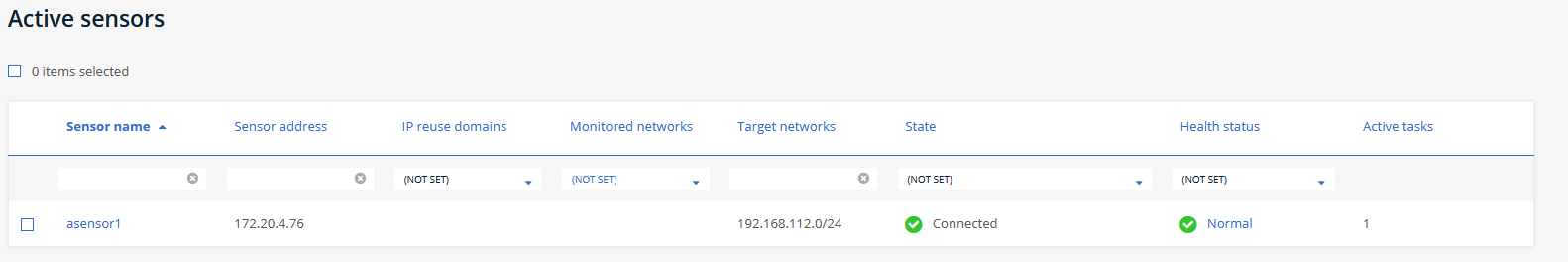
Asset Passive Monitoring
Passive monitoring is the primary way data is ingested in Forescout eyeInspect. This is done by configuring Switch Port Analyzer Protocol (SPAN) on one of the Network adapters of the Passive Sensor and connecting it to switches at the substation. It is best to deploy on a core switch because if most traffic is traversing this switch, it is most efficient to collect data from one source. The sensor is deployed according to Forescout guidelines and then it is configured to connect to the Command Center. For the verification steps in Command Center, see Monitor passive asset in the Forescout tasks section.
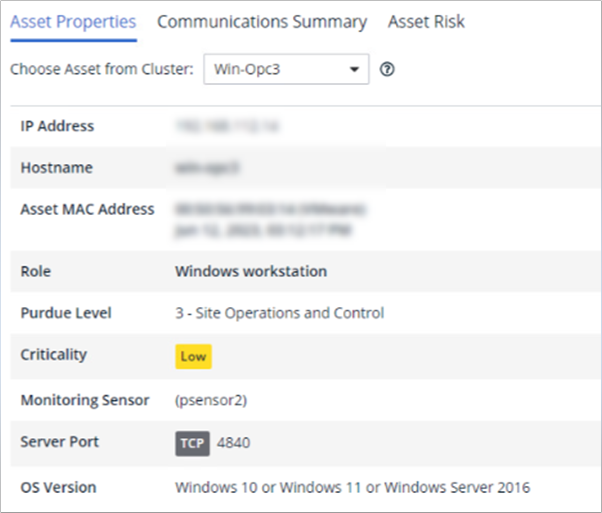
The eyeInspect Passive Sensor offers Asset Details on each individual device and displays an asset map that shows asset locations on the Purdue model. It also provides a communication flow to highlight inbound and outbound traffic from the asset. Users can access asset properties such as IP, OS, and MAC address, along with the corresponding asset risk information.
Asset Active Scanning
The primary role of Active Sensors is to collect data that cannot be easily accessed through passive monitoring. This can lead to the discovery of additional information about known assets, or identify assets that are not actively communicating or reside in networks that are not monitored by passive sensors. Active Sensors play a crucial role in providing a more thorough view of the network, complementing the insights obtained from passive monitoring. The sensor is deployed according to Forescout guidelines, then it is configured to connect to the Command Center. For the verification steps in Command Center, see Scan active asset in the Forescout tasks section.
The eyeInspect Active Sensor conducts scans on one or multiple hosts to identify active IP addresses, thereby discovering new assets within the network. It assesses the operating system, identifies open ports that may pose risks to an asset, and recognizes open OT-specific ports to ascertain the historical communication protocols of an asset. Additionally, the Active Sensor captures details like IED hardware and firmware information, among other relevant data points.
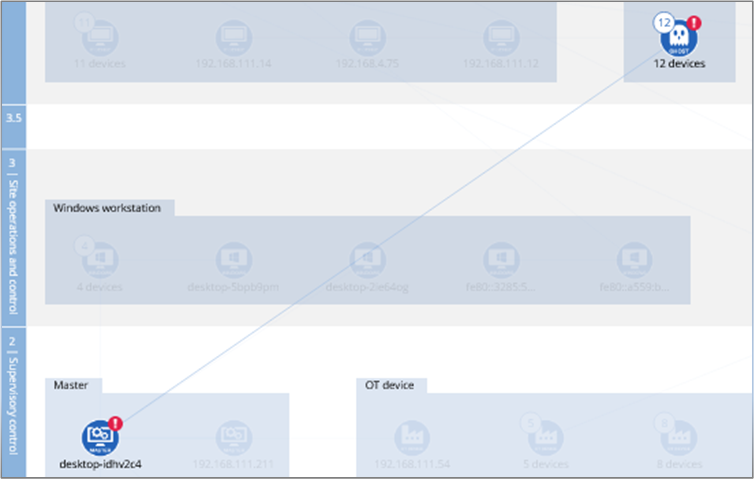
Network visibility and architecture
Having a clear understanding of an organization's network architecture and topology is essential in locating and identifying network issues. It is crucial to ensure that devices adhere to standardized models, such as the Purdue Model for substations. Having this sort of visibility can validate that assets are logically in the proper location, and unauthorized devices are not jumping operational levels to communicate with other devices, which can pose security risks.
By gaining visibility into the network architecture, organizations can anticipate potential threat scenarios and align their architecture models with standardized business practices for enhanced security and operational efficiency.
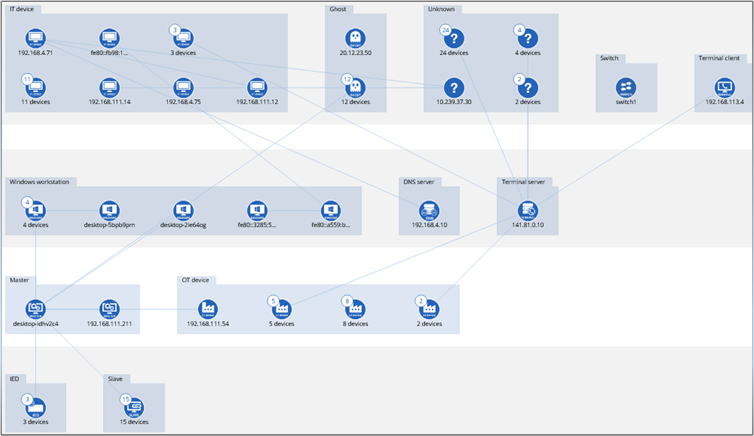
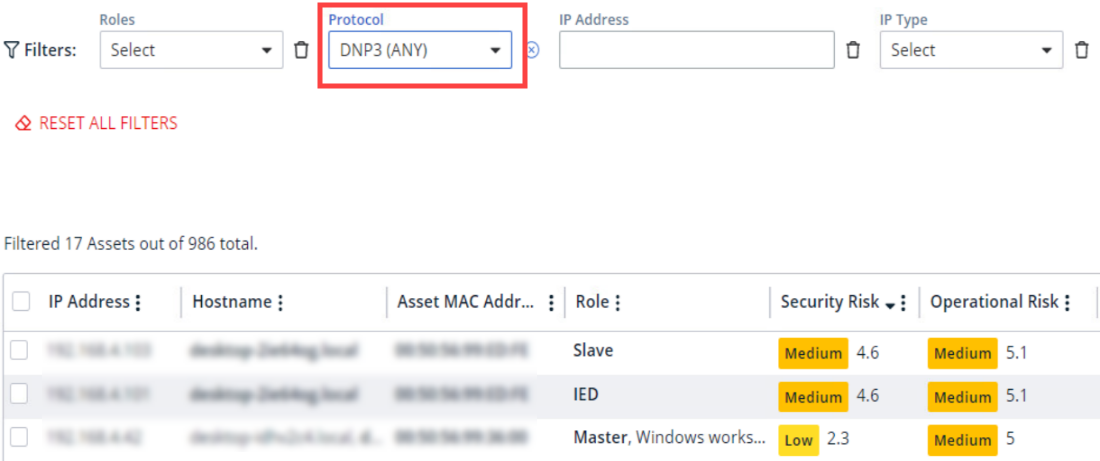
Asset visibility customization
Substations often consist of numerous assets, and there may be instances where the focus needs to be narrowed down to a specific type of asset. EyeInspect offers the flexibility to customize dashboards in the Assets tab, enabling users to access detailed information about specific types of assets.
This capability enhances the user's ability to obtain purposeful insights and effectively monitor the wanted assets. This allows for well-informed decision-making for asset management.
Investigation and detection
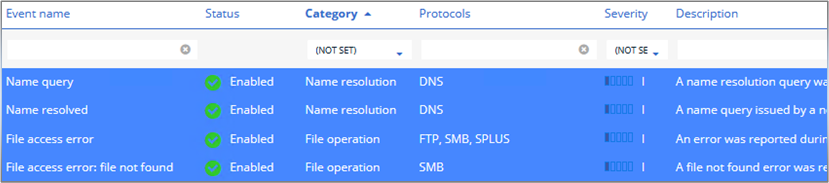
Detecting network communications can be effective in applying configuration management. Capturing and correctly identifying network communication establishes a baseline and helps to also detect any anomalous or suspicious behavior.
Detect network communications
Gaining insight into the network communications of the substation plays a crucial role in identifying suspicious requests and transfers. The Passive Sensors are equipped with Event Logging modules, which require activation. Once activated, these modules search for specific actions on network communication protocols.
Enabling all these features ensures that eyeInspect maximizes its capability to capture and detect rogue events, bolstering the network's security and effectively mitigating potential threats.
Risk and vulnerabilities
Forescout sensors offer valuable insights into the assets present at your substation, which include vulnerabilities and risks. In conventional terms, a vulnerability represents a weakness, while a risk refers to the probability of that vulnerability being exploited. This section demonstrates how eyeInspect can reveal vulnerabilities and risks to the cybersecurity of the substation network and provide a comprehensive means to view and effectively manage risks that are present.
Detecting vulnerabilities
Within its monitored network, eyeInspect incorporates a network intelligence framework with detection engines that monitor and alert for scenarios that are related to security, networking, and operations. The Passive Sensor is equipped with an Industrial Threat Library (ITL) which examines assets for weaknesses and outputs vulnerabilities specific to each asset type in the Assets Details tab. The ITL aligns with common vulnerabilities and exposures (CVEs) tailored to the substation, ensuring operators receive relevant vulnerability information, avoiding unnecessary alerts unrelated to their operations.
This targeted approach streamlines security monitoring and allows operators to prioritize focus on critical issues.
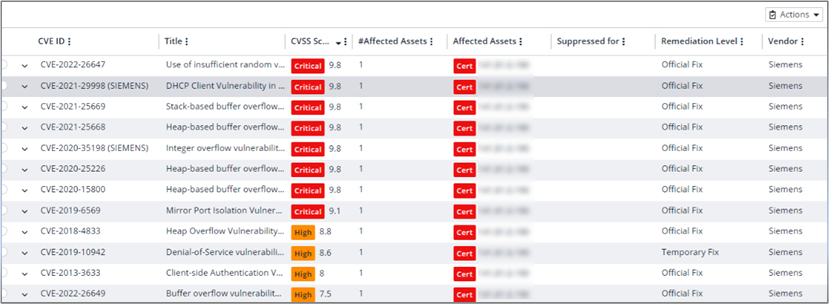
Generating insight of risks
eyeInspect offers a quantified approach to assessing asset vulnerabilities by assigning risk scores for both operational and security risks. These risk scores can be configured to be continuously updated through periodic polling, enabling real-time risk evaluation in fast-paced operational environments.
This dynamic capability fortifies the system's ability to proactively identify and address potential risks, providing valuable insights for effective risk management and informed decision making.
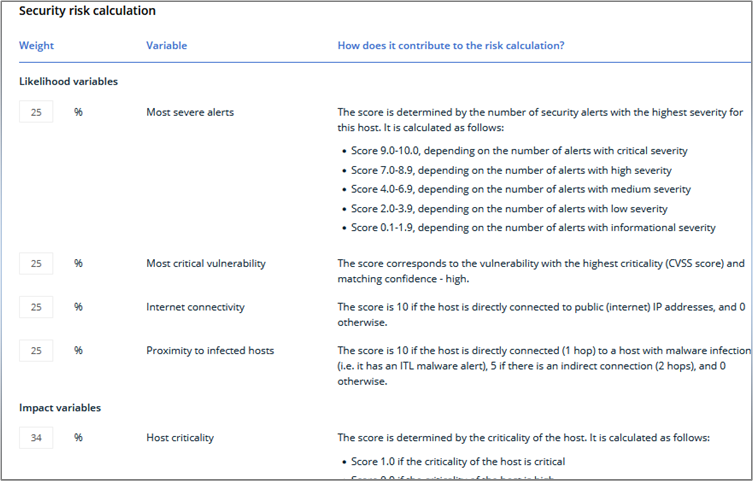
Risk calculation
eyeInspect incorporates a robust integrated risk calculation method, developed through years of experience and extensive research on substation threats. Since each substation is unique, operators and administrators have the flexibility to customize risk calculations, prioritizing attributes that contribute to the risk score as percentages.
This tailored approach empowers organizations to adapt to their specific security needs, enhancing the effectiveness of risk assessment and management that is closely aligned to their security posture.
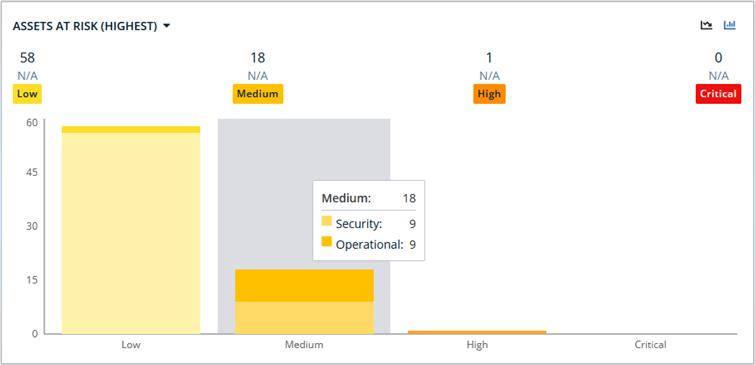
Risk visualization
By representing risks in a visual format, administrators can quickly identify critical areas that require immediate attention and prioritize their efforts accordingly. This visual representation enables better decision making, facilitates effective risk mitigation strategies, and enhances overall cybersecurity measures. Forescout eyeInspect provides dashboards on the home landing page for visualizing assets at higher risk at-a-glance, and further customization is possible in the Analytics tab, allowing operators to create graphs depicting assets and their risk levels (operational or security) in relation to other variables.
Visualizing risks helps administrators identify, communicate, and track the security status of the substation in a more intuitive and accessible manner, allowing for a better understanding and support for security initiatives.
Threat detection
Forescout sensors also provide useful insight into potential threats to a substation. Conventionally, a threat is an event or scenario that can cause data to be damaged, leaked, stolen, or disrupted. eyeInspect can enable visibility into substation network security threats and allow end customers to evaluate threats they are concerned about.
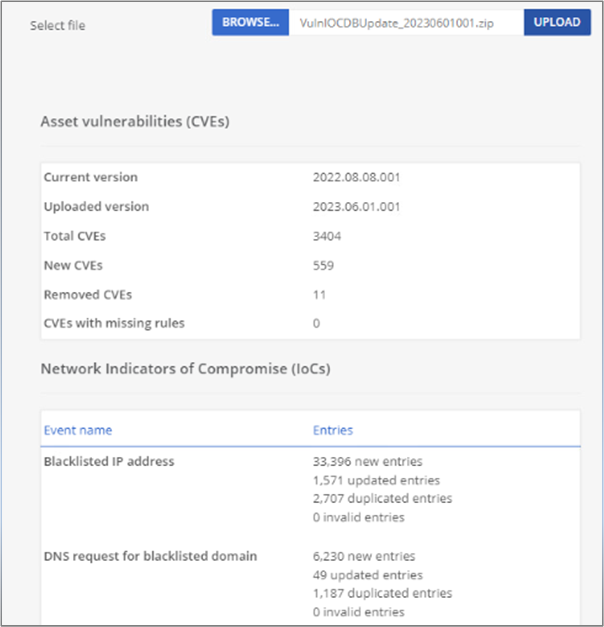
Threat definition updates
eyeInspect's Command Center (CC) offers the capability to update CVEs and indicators of compromise (IoCs) tailored for substation environments. This feature is vital, as threats are consistently detected and require regular updates. Forescout regularly provides CVEs that specifically target the substation through its Partner Portal. Administrators have the option to manually upload the new threat definitions that are provided by Forescout to the CC and are encouraged to download updates frequently. By going to Events > Network Logs > IoC Scan Page, you can upload the updated files that contain the new CVEs and IoC definition.
This proactive approach enhances the ability of the system to stay current with emerging threats, bolstering the cybersecurity posture of substations, and ensuring effective threat mitigation.
Threat monitoring and discovery
eyeInspect incorporates an Industrial Threat Library, which enables the identification of asset actions as potential threats. A list of all potential threats along with general alerts can be found in the Events > Alerts tab. When an event is identified as a threat, an in-depth alert summary is presented, featuring the communicating assets, associated sensors, and a brief description. Additional tabs offer more detailed information such as ports, protocols, and timestamps for the event.
The CC also provides ICS adversarial tactics, techniques, and common knowledge (ATT&CK) category matches for the events, explaining the tactics and techniques used by attackers for the matched threat. This valuable information helps organizations to understand attack patterns and helps them take appropriate measures to counter potential threats. Lastly, the discovered threat outputs the sensor's trigger details, providing the lowest level of information about the event.
This multifaceted approach ensures a comprehensive and granular understanding of detected threats, facilitating efficient threat management and response.
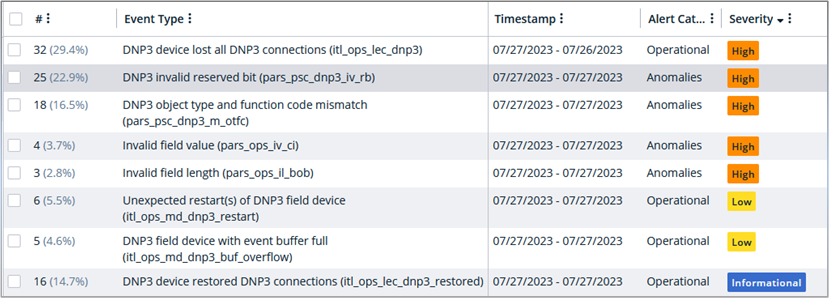
Threat visibility customization
Just as with creating dashboards for assets with specific attributes, eyeInspect enables the creation of dashboards for events that pose potential threats to substations while reviewing related Alerts. This functionality empowers operators to monitor and analyze events more effectively, ensuring timely responses to potential security risks and enhancing the overall threat detection capabilities of the system. For example, if there is a threat that coincides with assets communicating through the DNP3 protocol, you can create a dashboard to filter the alerts of L7 Protocol: DNP3.
Cases
In eyeInspect, operators have the capability to create Cases in the Events > Alerts tab. This feature groups related alerts and instructs the system to automatically assign new instances of those alerts to the designated case. This can help segment alerts related to an ongoing investigation or process. This functionality can also help to streamline threat monitoring, allowing operators to concentrate on new threats emerging on the network while efficiently managing and analyzing existing issues within designated cases.
Alert cases improve operational efficiency by providing a structured approach to handle and prioritize security incidents in real time.
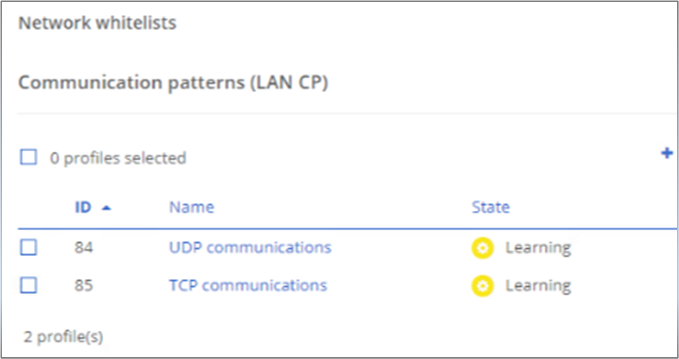
Baselining and deviation
In OT environments, uptime and reliability are often prioritized, leaving minimal time to address system security. The Passive Sensors can be equipped with the Local Area Network Connection Profiler (LAN CP), which tracks and analyzes TCP and UDP communication patterns among network devices. Regular communication patterns are recorded in an editable safelist. The LAN CP can be set to Learning mode to establish a baseline of communication traffic. Once configured, the profiler switches to Detecting mode, alerting on unfamiliar communications to identify potential rogue devices or anomalies on the network.
This proactive approach aids in enhancing the security posture of OT environments and mitigating potential risks effectively. LAN CP can be toggled between Learning and Detecting mode to establish a new baseline if needed; however, this privilege should be restricted to administrators to allow for proper change management.
Incidence response and alerting
Forescout eyeInspect primarily functions as an intrusion detection system, providing incident response for network access concerns through alerting. It seamlessly integrates with security information and event management (SIEM) for log forwarding and can generate incident reports for forensics without disrupting Forescout operations. Moreover, eyeInspect harmoniously integrates with other Forescout applications, thereby creating a robust cybersecurity ecosystem that elevates threat detection and response capabilities.
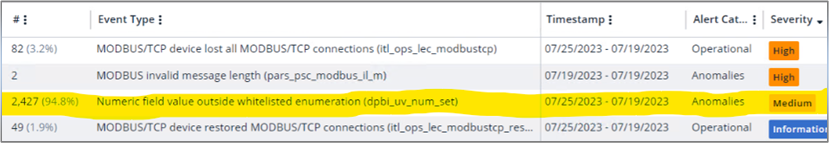
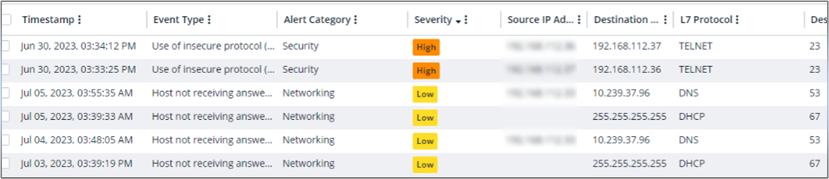
Viewing alerts
eyeInspect generates alerts when it detects suspicious events in the network traffic. These alerts are assigned severity levels, allowing administrators to prioritize their response. Alerts can be triggered by:
- Network communications
- Anomalies when eyeInspect observes deviations from a set baseline
- Security and operational events when potential threats or disruptions are matched to tactics and techniques of known threats
- Informational alerts that notify of nonthreatening events in the system
All alerts can be conveniently viewed in the Events > Alerts tab, providing administrators with real-time insights to effectively manage and respond to security incidents.
Generating reports
eyeInspect offers the capability to export host information and alert details to an editable .docx document. Users can create management reports that provide an overview of assets and identified threats on the network. Additionally, eyeInspect allows for generating detailed reports for offline analysis and mitigation purposes.

In eyeInspect's Command Center, every tab offers the capability to generate and export CSV files. Whether it is a comprehensive list of assets and their essential details or specific assets with vulnerabilities, this feature ensures convenient data export for various purposes.
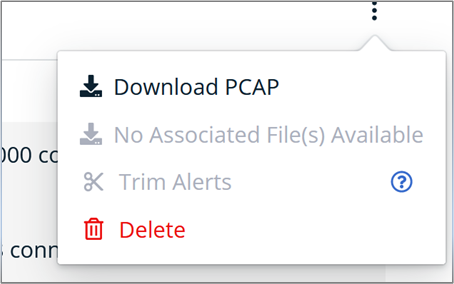
Within the Events > Alerts tab, when selecting a specific alert, locate the three vertical dots on the right. There is submenu item Download PCAP which presents the opportunity to retrieve a packet capture (PCAP) file encompassing the unprocessed network traffic that is linked to the alert. This feature empowers analysts to conduct an investigation into the origins and outcomes of the identified anomalous behavior. The PCAP file further serves as a resource for forensic analysis.
Integrating with SIEM
Forescout eyeInspect specializes in incident response by alerting for events and potential threats. Its sister software, eyeSight, seamlessly integrates with external products like ServiceNow, streamlining incident response workflows. eyeInspect can automatically take action to resolve incidents by connecting to eyeSight. Additionally, it can integrate with SIEM solutions using the syslog protocol, enhancing security threat detection, analysis, and response for organizations. Forescout can forward alerts, network logs, active scans, and Command Center's health status to the SIEM.
Forescout's integrations strengthen its ecosystem's security posture and incident response abilities, providing a more complete approach to security management.
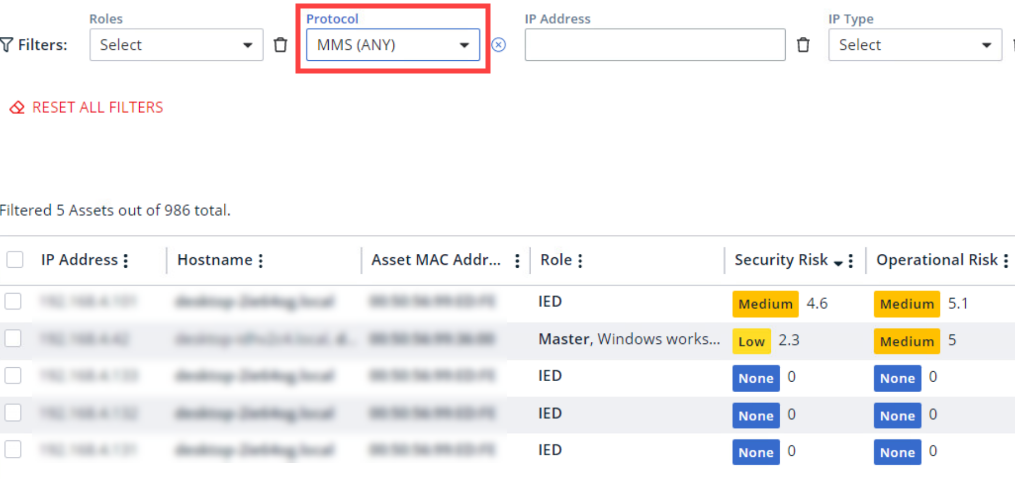
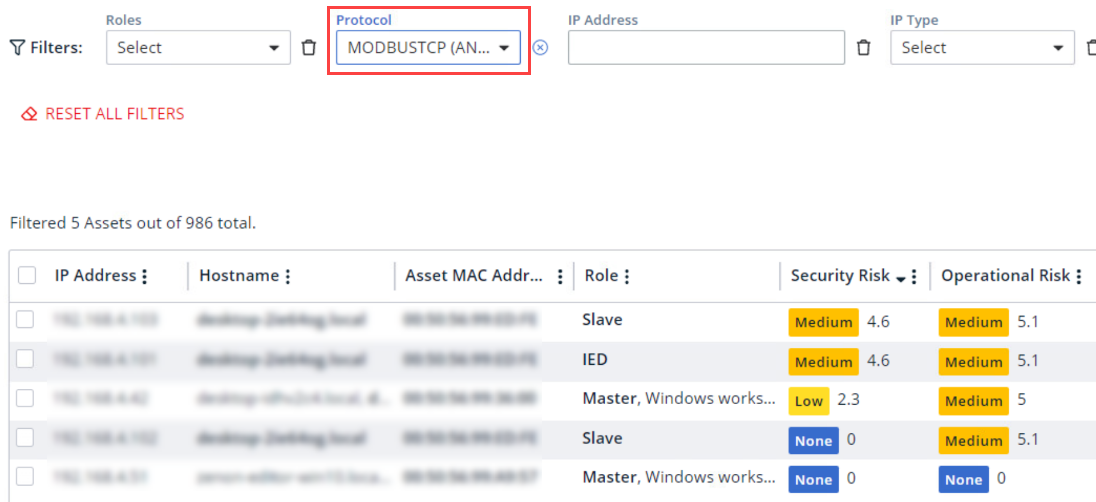
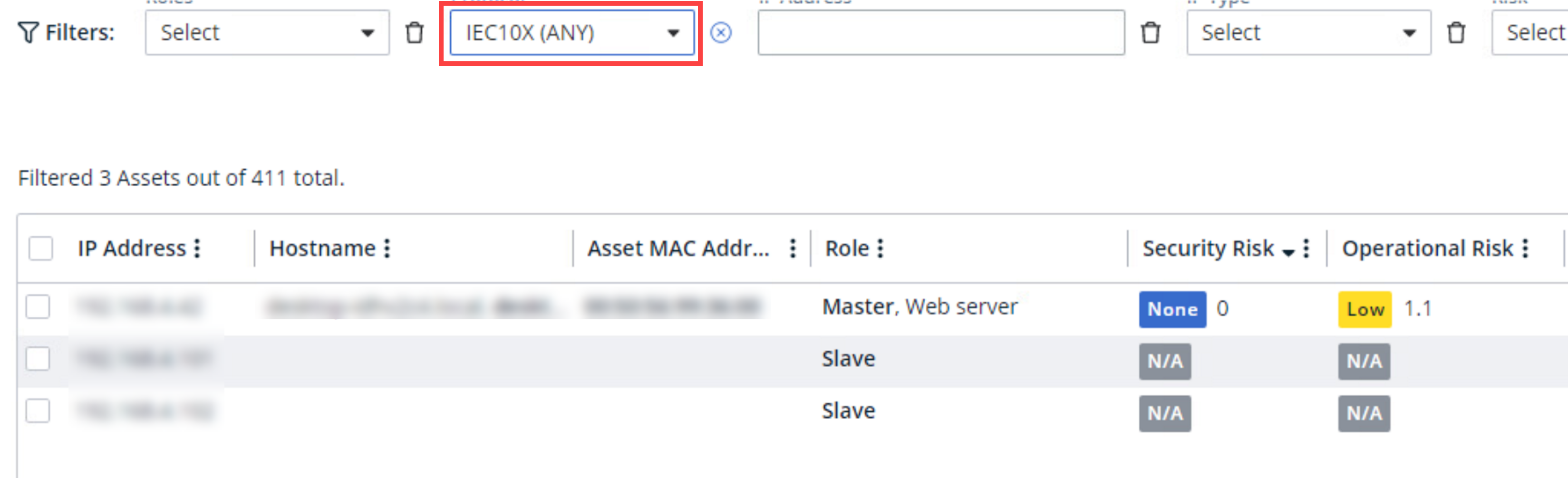
Detect and read OT process values in a unified architecture
eyeInspect was validated along with ABB ZEE600 following the architecture that is displayed in the Validated architecture for secure communication in a substation and Control Center figure. Utilizing a few of the more common substation protocols, the integration of Forescout eyeInspect provided valuable insights into assets engaged in protocol-based communication. Upon asset detection, eyeInspect conducted a risk assessment and established its logical architectural position. The following figures show a few of the protocols that were used and eyeInspect's discovery and representation of them.
eyeInspect's passive sensor has a feature similar to the Local Area Network Connection Profiler (LAN CP) feature, Deep Packet Behavior Inspection (DPBI) to learn the normal range of protocol behavior/values per asset. After the protocol behavior had been observed and recorded, the DPBI monitor was set to detect mode, promptly alerting on any values outside the range of values learned from the device output.
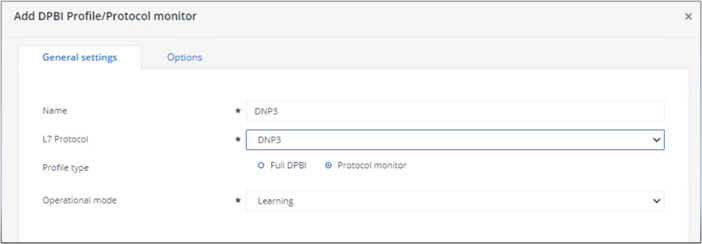
Unforeseen variations such as voltage fluctuations can disrupt operational continuity within substations. Detecting when values deviate from the anticipated range proves invaluable in the forensic analysis of trends. In the event of such incidents, eyeInspect promptly alerts and designates the numerical anomalies as Anomalies, aiding in timely response and resolution.