Home > Data Protection > PowerProtect Data Manager > White Papers > Dell PowerProtect Cloud Snapshot Manager: Architecture and Security > Overall CSM Architecture
Overall CSM Architecture
-
CSM leverages the cloud providers’ (AWS, Azure, and GCP) existing snapshot technology to protect workloads in the cloud. More enterprises want to use native snapshots for data protection over traditional backups because it provides faster backups and restores. While snapshot capabilities exist in the cloud, they are not automated and need to be manually managed. As a result, they are typically managed and run using scripts and homegrown tools.
The lack of snapshot automation and management results in snapshot proliferation, which quickly becomes expensive and cumbersome to manage. It also adds complexity to the recovery process because users find it difficult to identify the “right” snapshot to recover, among so many snapshots. These challenges exist in single cloud instances, and when an organization goes multi-cloud it exacerbates the problems.
CSM solves this problem by orchestrating and managing snapshot creation and deletion per policy across multiple clouds, multiple accounts and regions through a single pane of glass.
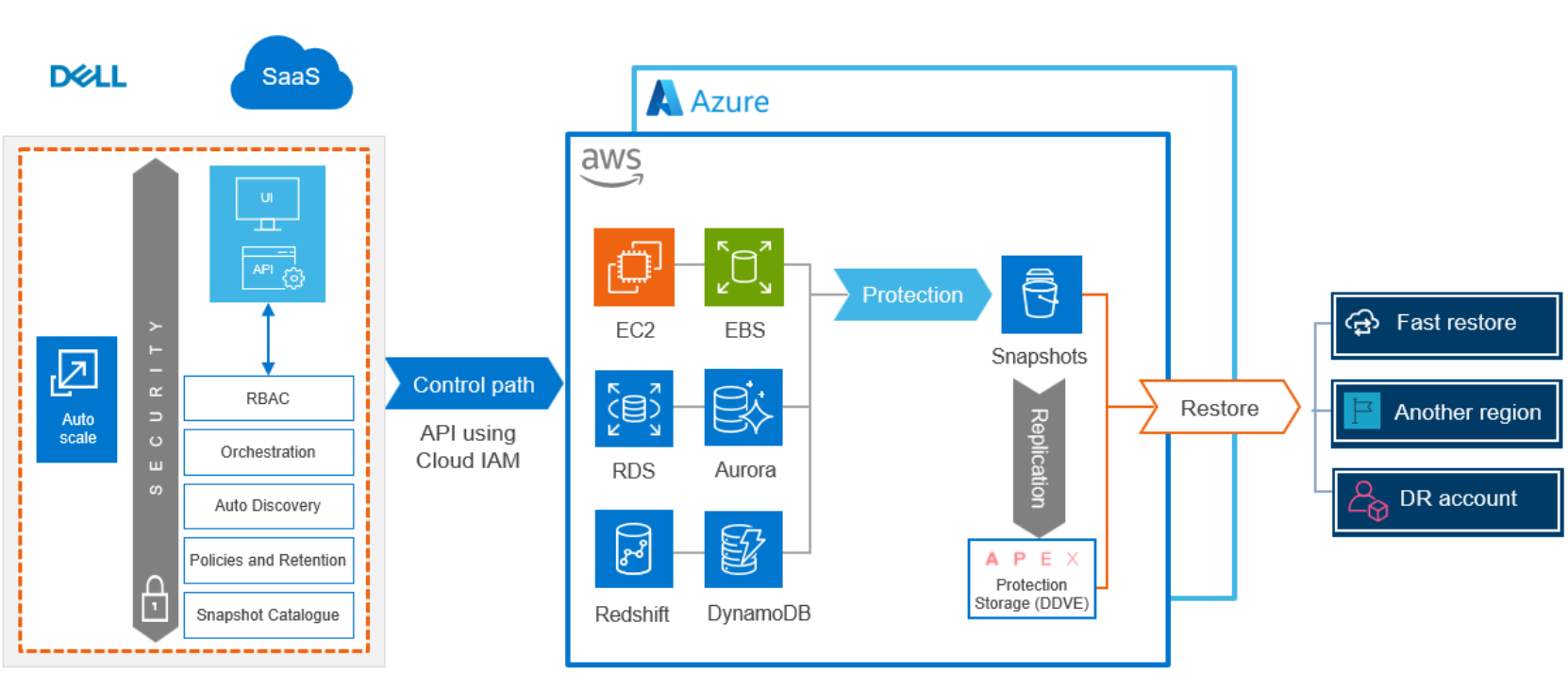
Figure 1. Cloud Snapshot Management for AWS
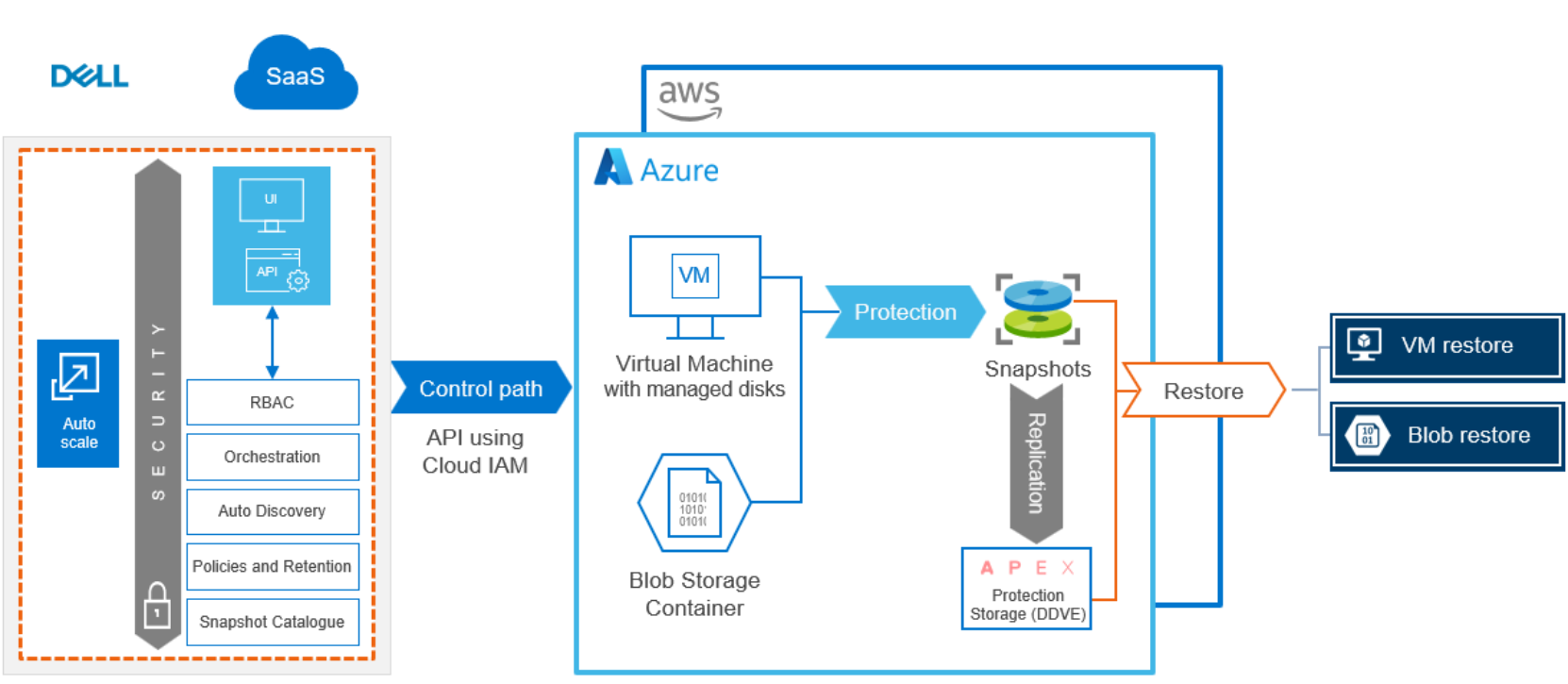
Figure 2. Cloud Snapshot Management for Azure
CSM uses the REST APIs provided by the cloud providers to accomplish tasks like instance discovery, creation, deletion and restoration of snapshots. CSM automates the creation of snapshots through Protection Policies. When the protection policy is run, snapshot creation is triggered for the cloud resources attached to the policy. AWS creates the snapshot of the specified EC2 instance, EBS volumes, and RDS databases, and stores these snapshots in a special snapshot bucket in S3. This helps separate the copy of the protected data from the primary data. Azure creates snapshots of the Managed Disks and stores the snapshot in the low cost Locally Redundant Storage (LRS).
For AWS, CSM allows copying of snapshots to a different region or a different account other than the region or account where the cloud resources are located for disaster recovery. If the original region snapshot is encrypted, the copied snapshot is encrypted with the AWS default encryption key for the targeted remote region. CSM also enables the users to configure custom encryption keys instead of using the default encryption key.
CSM also helps protect VMs against security attacks and breaches in customer AWS accounts. CSM provides disaster recovery by enabling snapshots to be copied to a restricted account in AWS. Snapshots copied across accounts are full backups and therefore, can be restored to the original account or a different AWS account.
For Azure, CSM allows copying snapshots to remote or cross-regions, therefore enabling the quick recovery of protected VMs in other regions. CSM supports the use of both disk-level encryption (Managed Disk Server-Side Encryption with Customer Managed Keys) and operating system-level encryption (Azure Disk Encryption (ADE)) for copying and restoring snapshots across regions.
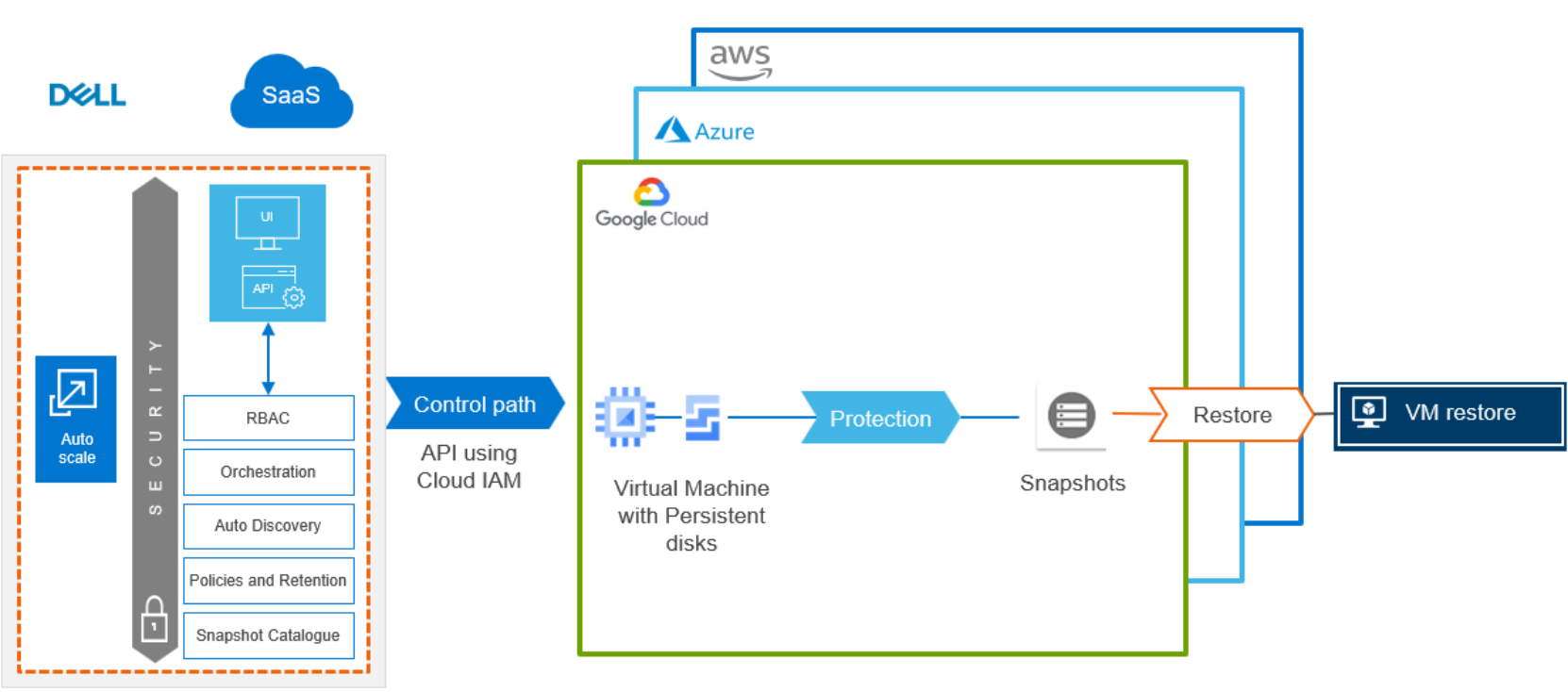
Figure 3. Cloud Snapshot Management for GCP
For GCP, CSM supports the protection of data in the GCP environment. It offers quick and easy onboarding/integration of GCP with CSM. VM instances running in compute engine in GCP are protected by CSM using snapshot technology. CSM offers tag-based and resource-based protection plans.
