

Talking CloudIQ: Cybersecurity
Mon, 20 Feb 2023 21:08:34 -0000
|Read Time: 0 minutes
Introduction
This is the fourth in a series of blogs discussing CloudIQ. Previous blogs provide an overview of CloudIQ and discuss proactive health scores and capacity monitoring and planning. This blog discusses the cybersecurity feature in CloudIQ. Cyber-attacks have become a significant issue for all companies across all industries. The immediate economic consequences, combined with the longer-term impact of the loss of organizational reputation, can have both immediate and lasting effects.
Reduce risk
Misconfigurations of infrastructure systems can open your organization to cyber intrusion and is a leading threat to data security. The CloudIQ cybersecurity feature proactively monitors infrastructure security configurations for Dell PowerStore and PowerMax storage systems and PowerEdge servers, and notifies users of security risks. A risk level is assigned to each system, placing the system into one of four categories, depending on the number and severity of the issues: Normal, Low, Medium, or High.
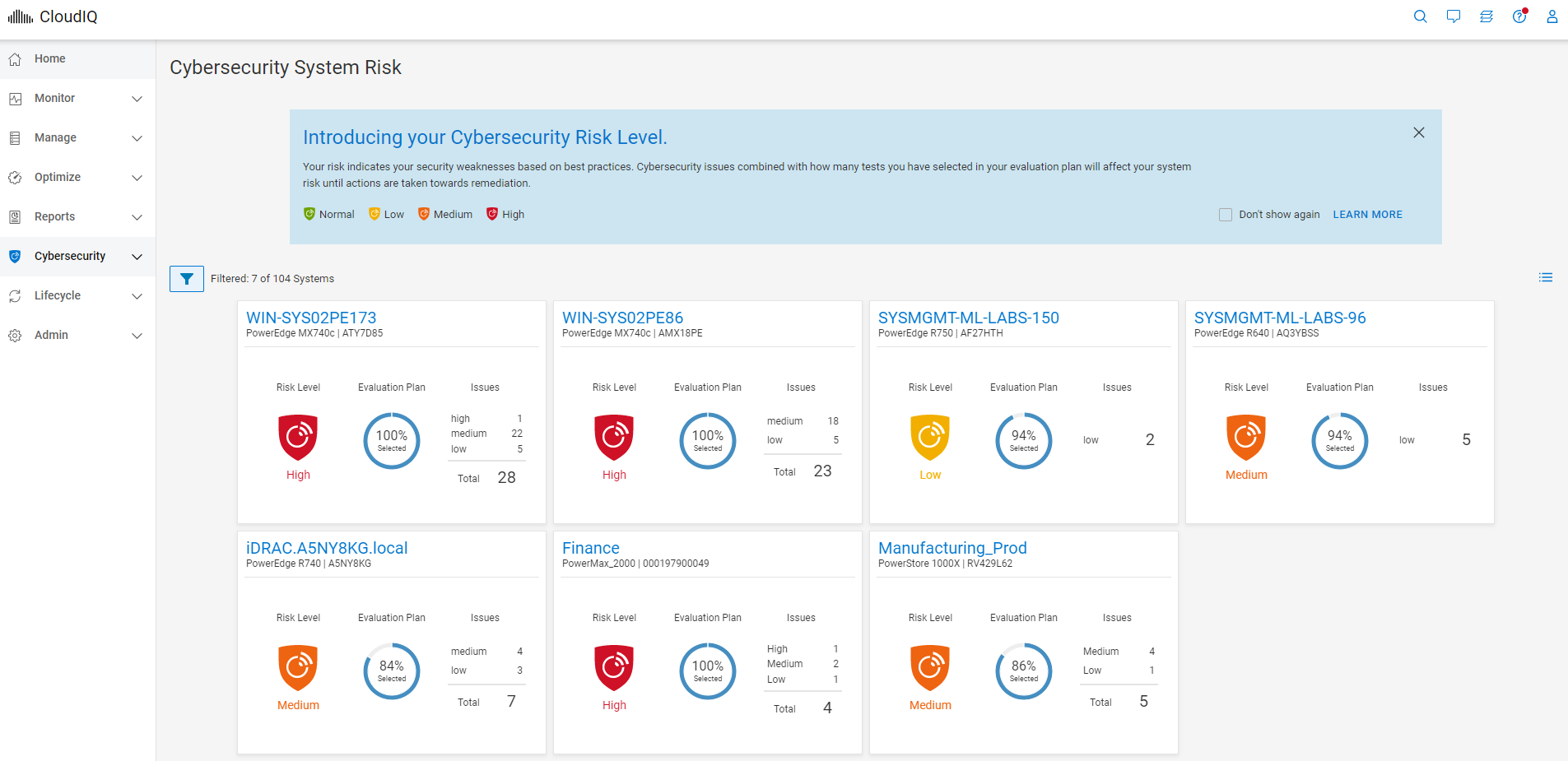
Figure 1. Cybersecurity system risk levels
When a security risk is found, remediation instructions are provided to help you address the issue as quickly as possible.
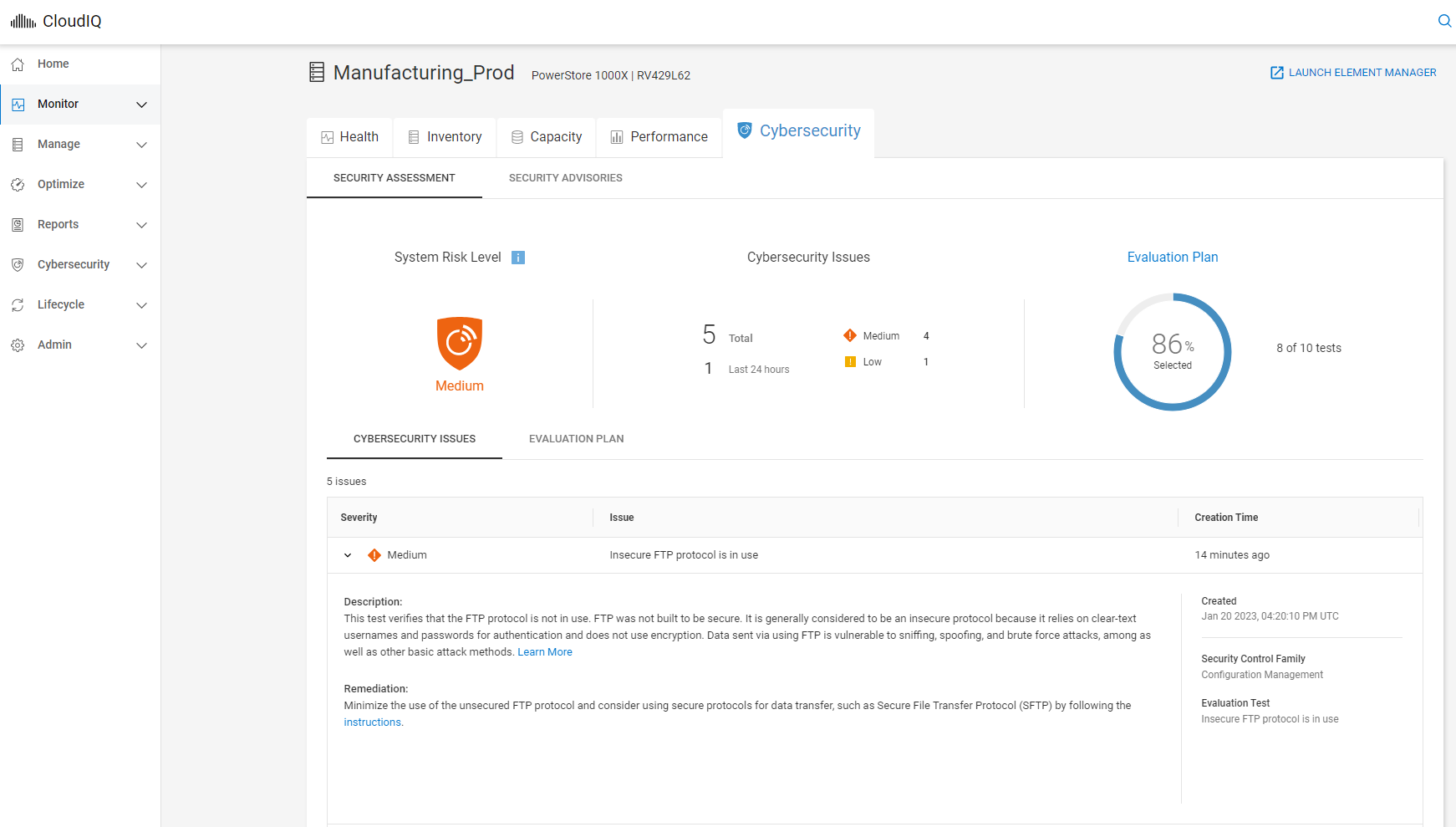
Figure 2. Cybersecurity details with remediation
Security Advisory integration
CloudIQ evaluates outgoing Dell Security Advisories (DSAs) and intelligently notifies users when those advisories are applicable to their specific Dell system models with specific system software and firmware versions. This eliminates the need for users to investigate if a Security Advisory applies to their systems and allows them to immediately focus on remediation.
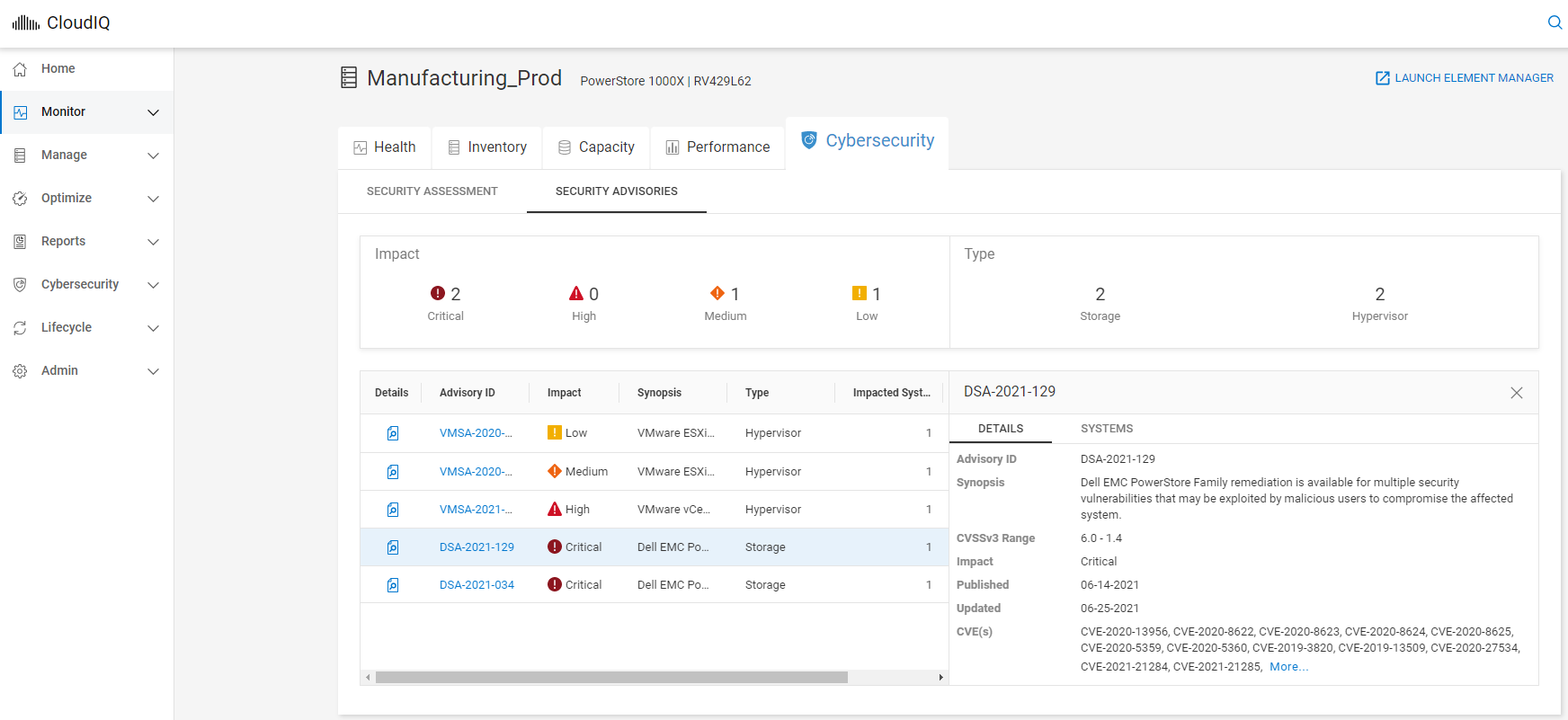
Figure 3. Dell Security Advisory listing
Manage policy
By using CloudIQ Cybersecurity policy templates, users can quickly set up security configuration evaluation tests and assign them to large numbers of systems with just a few clicks. Once assigned, the test plan is evaluated against each associated system, and the system administrator is notified in minutes of any unwanted configuration settings.
Testing has shown that it takes less than 3 minutes to set policies and automate security configuration checking for 1 to 1,000 systems. That’s a dramatic time savings versus the 6 minutes that it would take to manually check each individual system’s security configuration.1
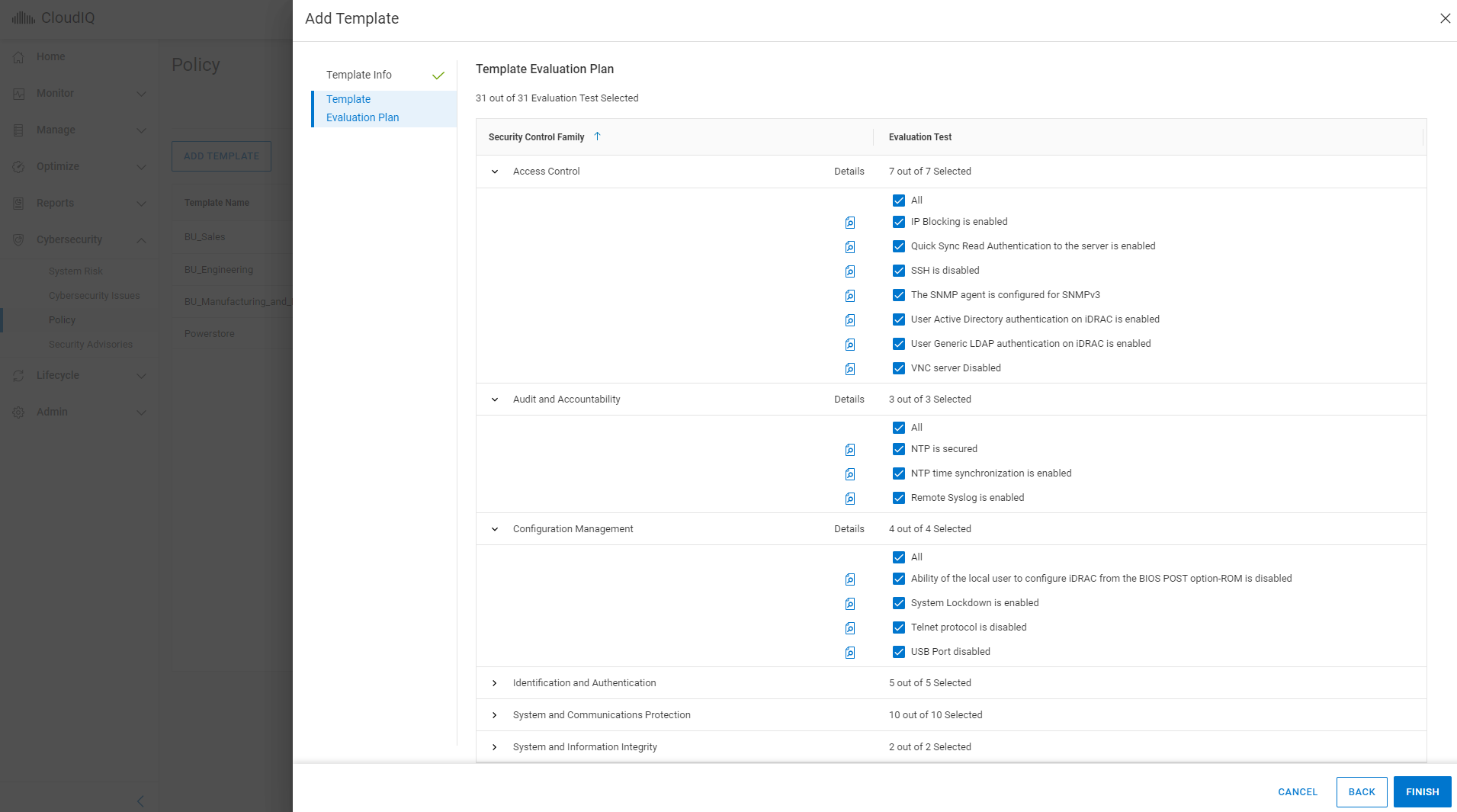
Figure 4. Evaluation plan templates
Conclusion
Cybersecurity has clearly become a challenge and priority for companies of all sizes. With the large and growing number of systems distributed across core and edge locations, it is impractical for any IT organization to manually check those systems for misconfigurations. Dell CloudIQ eliminates manual checking by automating it and recommending how to quickly mitigate misconfiguration risks that can lead to unwanted intrusions threatening data security. With the intelligent evaluation of Dell Security Advisories, CloudIQ identifies applicable DSAs, further saving time and expediting remediation.
Resources
For additional cybersecurity related information, see the following documents:
- Dell PowerStore: Cybersecurity
- Dell PowerMax: Cybersecurity
- Dell PowerMax: Cybersecurity for Mainframe Storage
- Dell CloudIQ Cybersecurity for PowerEdge: The Benefits of Automation
How do you become more familiar with Dell Technologies and CloudIQ? The Dell Technologies Info Hub provides expertise that helps to ensure customer success with Dell platforms. We have CloudIQ demos, white papers, and videos available at the Dell Technologies CloudIQ page. Also, you can refer to the CloudIQ: A Detailed Review white paper, which provides in-depth summary of CloudIQ.
Author: Derek Barboza, Senior Principal Engineering Technologist
1Dell CloudIQ Cybersecurity for PowerEdge: The Benefits of Automation



