Home > Storage > PowerFlex > White Papers > Ransomware Protection:Secure data on Dell APEX Block Storage for Public Cloud with PowerProtect Cyber Recovery > Solution Architecture
None
-
This section describes how Dell PowerProtect Cyber Recovery is deployed in AWS and replicates data from the production system that is deployed on a two-layer Dell APEX Block Storage for Public Cloud.
The following diagram represents the architecture of Dell PowerProtect Cyber Recovery and the Dell APEX Block Storage that is deployed across multiple AZs in a single AWS region.
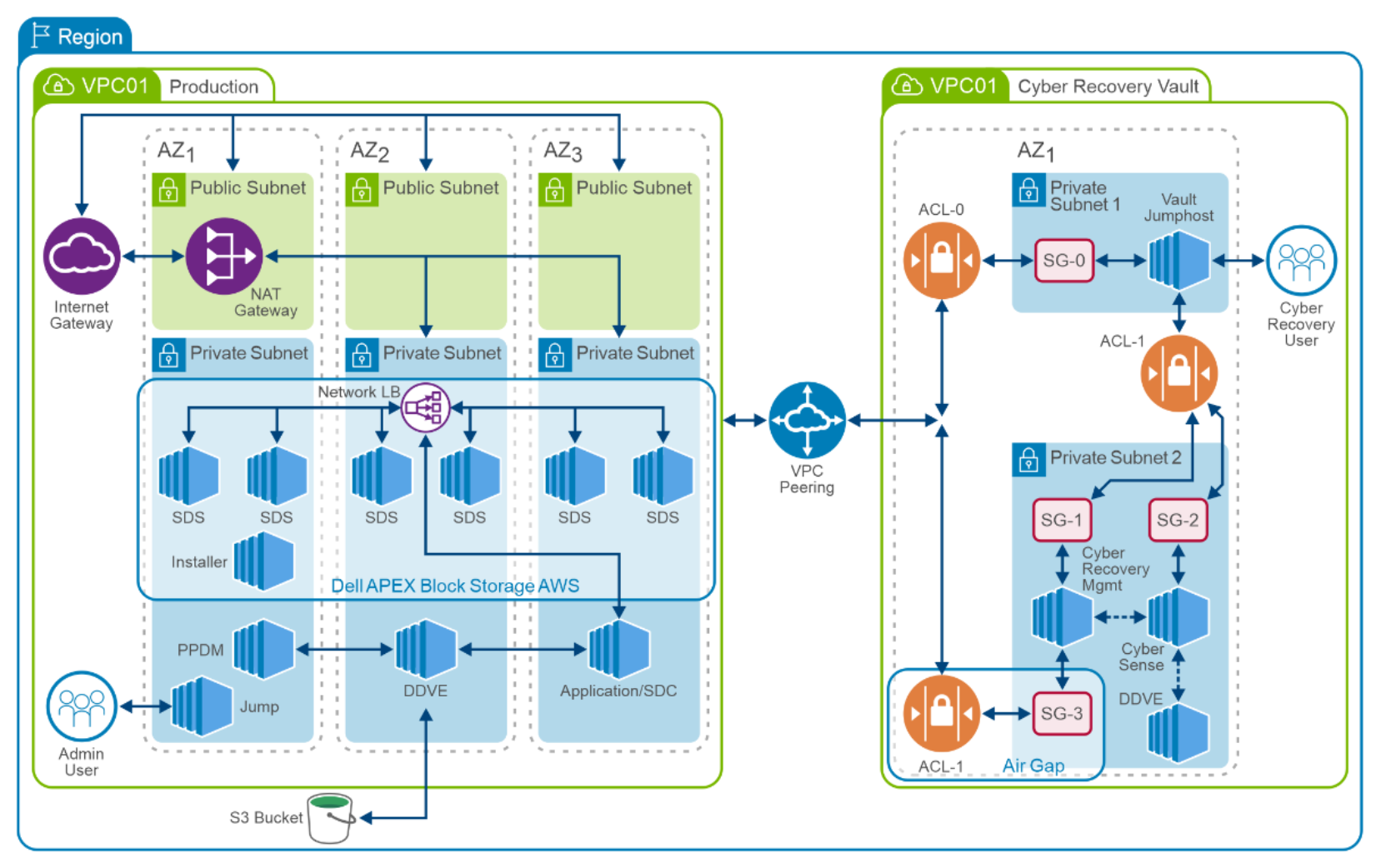
Figure 4. Dell APEX Block Storage for Public Cloud in AWS with Dell PowerProtect Cyber Recovery architecture
Production environment : In this deployment, Dell APEX Block Storage for Public Cloud in AWS is deployed with one VPC (virtual private cloud) across three availability zones within the same AWS region for resiliency. For each availability zone, a separate private and public subnet is created to provide connectivity and routing across different availability zones. The public subnet contains resources that are accessible over the Internet and the private subnet contains the compute, storage, and data protection resources.
A network address translation (NAT) gateway is configured in the public routing table to enable access to the Amazon EC2 instances in public subnet over the Internet. Security groups are created for Amazon EC2 instances to provide an additional layer of security and control over inbound and outbound traffic at the subnet level.
In each AZ, two SDS are installed on c5n.4xlarge Amazon EC2 instance with the Red Hat Enterprise Linux AMI. The Amazon EC2 instances that are deployed by Dell APEX Block Storage for Public Cloud are backed by SSD drives. The SSDs are locally attached at the Instance level. The natively attached SSD drives are persistent storage. There are six SDS instances that are configured into a single protection domain. A single storage pool is created, using all the storage devices available within the protection domain.
Dell APEX Block Storage for Public Cloud in AWS maintains the user data in a mesh mirrored layout such that each piece of data has two copies (primary and secondary) stored on two different storage optimized Amazon EC2 instances (SDS). The copies are evenly distributed across the SDS instances, which enable the system to maintain data availability and high-performance if there is a failure of a storage device or Amazon EC2 storage optimized instance.
The Dell APEX Block Storage volumes that are created from the Dell APEX Block Storage pool are mapped to Amazon EC2 compute instances running Dell APEX Block Storage SDC services. The Dell APEX Block Storage volumes mapped to instances are used to create the file system to host the databases.
PPDM and DDVE instances are deployed in existing availability zones separately within the same AWS region to backup the data on Dell APEX Block Storage. Dedicated S3 buckets are created for DDVE to store backup data securely.
Vault environment : The Cyber Recovery solution on AWS is deployed with another Virtual Private Cloud (VPC) within the same AWS region. It involves a single Availability Zone (AZ) and the creation of two private subnets, each with its dedicated routing tables.
For more information, see Cyber Recovery Solution Architecture.
- Jump Host Access:
The first private subnet, along with its associated security groups and network access lists, is configured for accessing the jump host.
- Cyber Recovery Management:
The second private subnet, along with its corresponding security groups and network access lists, facilitates access to the Cyber Recovery management host, DDVE (Dell Data Domain Virtual Edition), and CyberSense.
- Backup Data Storage:
Dedicated S3 buckets are created for DDVE to store backup data securely.
- VPC Peering:
A VPC peering connection is established between the two VPCs, enabling private routing of traffic between the production environment and the Vault environment.
