Home > Storage > PowerFlex > White Papers > Ransomware Protection:Secure data on Dell APEX Block Storage for Public Cloud with PowerProtect Cyber Recovery > Data Analysis using CyberSense
None
-
Using the CyberSense feature in the Dell PowerProtect Cyber Recovery vault, you can analyze a point-in-time (PIT) copy for indicators of compromise, suspicious files, or potential malware.
For more information and detailed instructions on analyzing a data copy, see Dell PowerProtect Cyber Recovery Product Guide.
- Login to Dell PowerProtect Cyber Recovery UI and go to Policies > Copies.
- Select the latest copy and click Analyze. From the Application Host list box, select the application nickname for the CyberSense feature.

Figure 14. CyberSense as an application in Dell PowerProtect Cyber Recovery
- When the analysis is complete, return to the list of copies under Policies > Copies and click in the row of a copy. The Last Analysis column shows the results as Suspicious, Good as shown in the following figures:
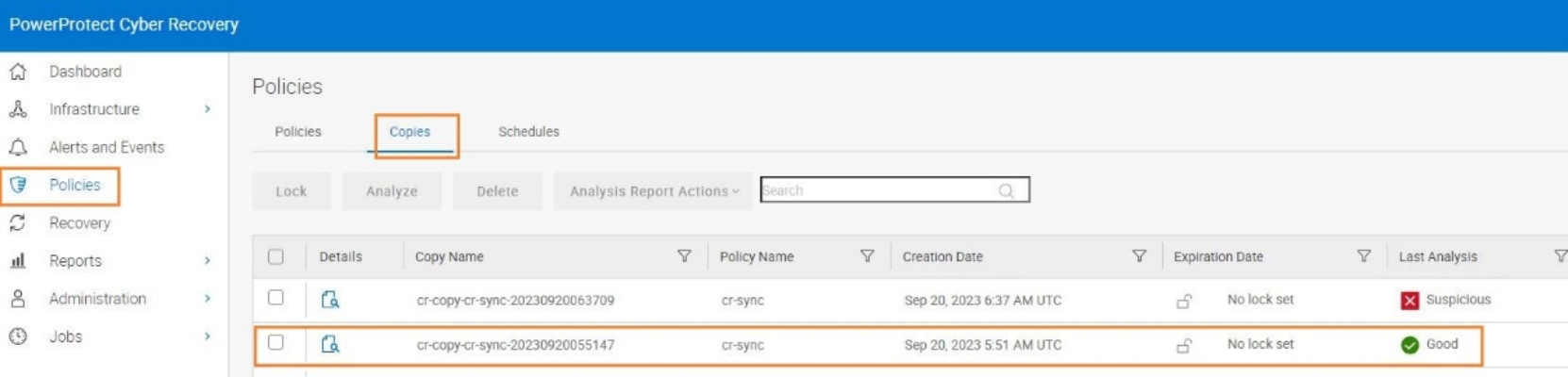
Figure 15. Analyze the good test data operation status
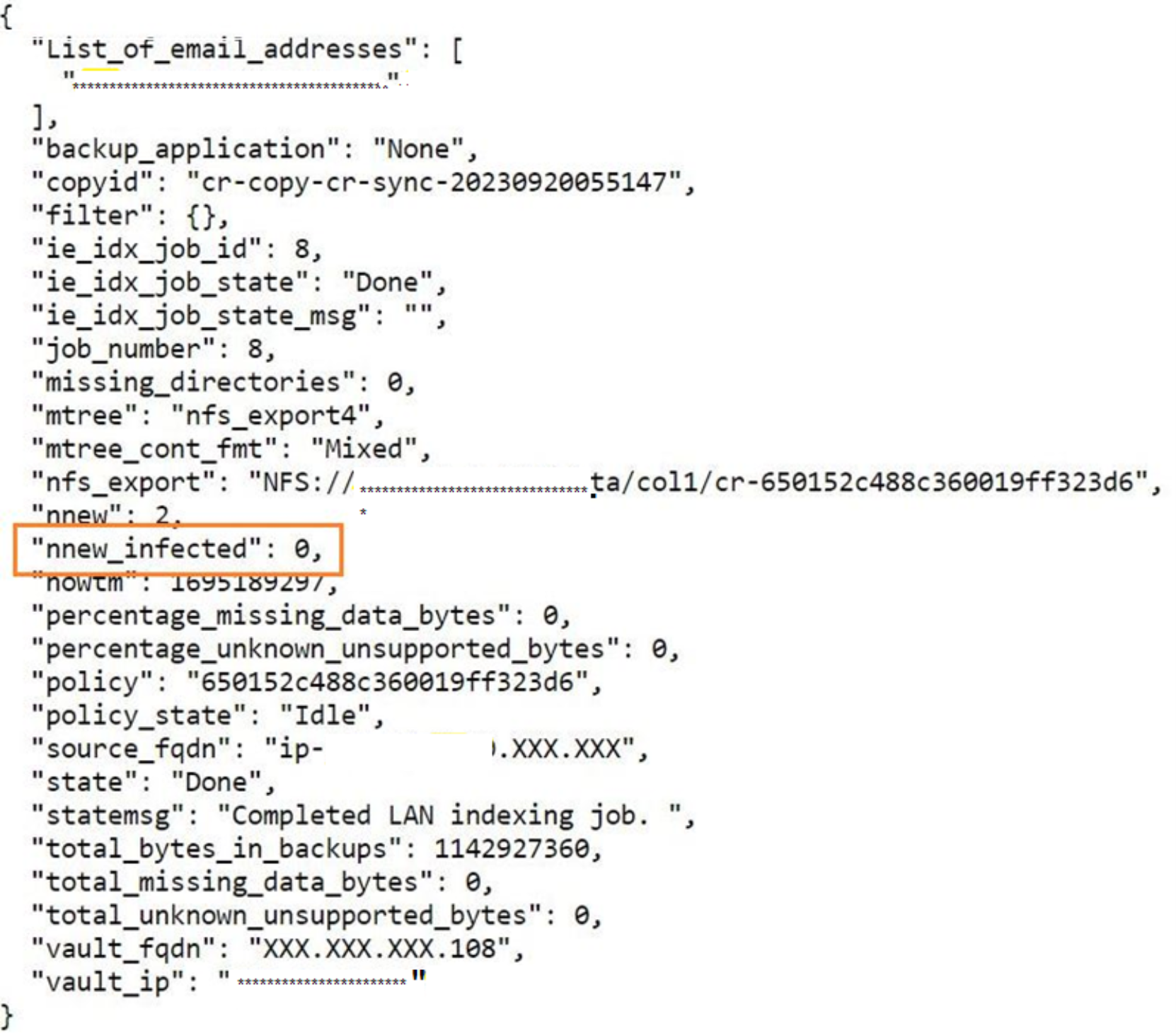
Figure 16. Output for good test data – CyberSense
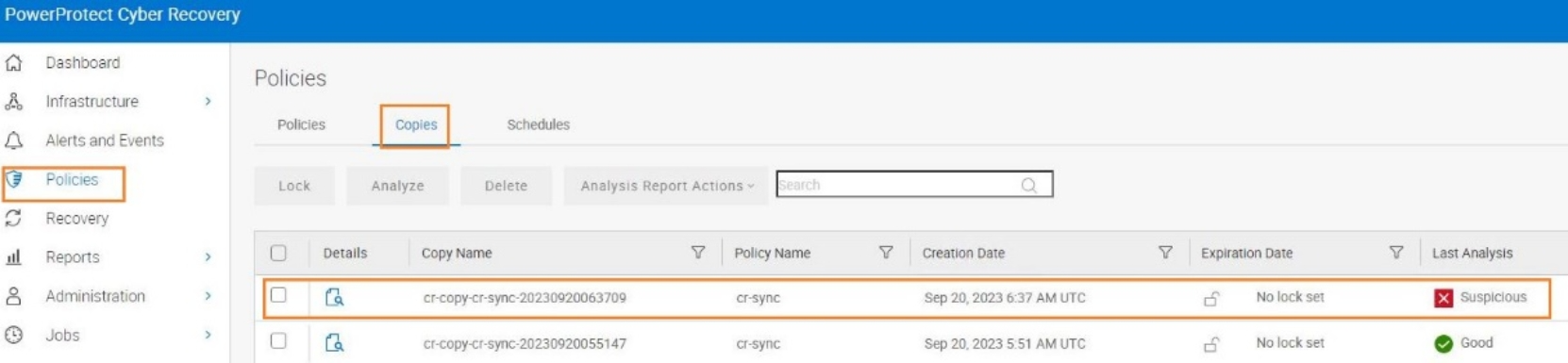
Figure 17. Analyze the suspicious data operation status

Figure 18. Output for suspicious test data – CyberSense
- To retrieve a detailed analysis report (copy-name.csv) about a completed analysis, select the analyzed copy, click Analysis Report Actions, and do one of the following from the drop-down list as shown in the following figure:
- Click Download Analysis Report to download an analysis report for a specified copy to the location configured for download in the browser.
- Click Email Analysis Report to send an analysis report for a specified copy in an email message. In the drop-down list, enter at least one valid email address. You can then specify multiple email addresses. Click Apply.
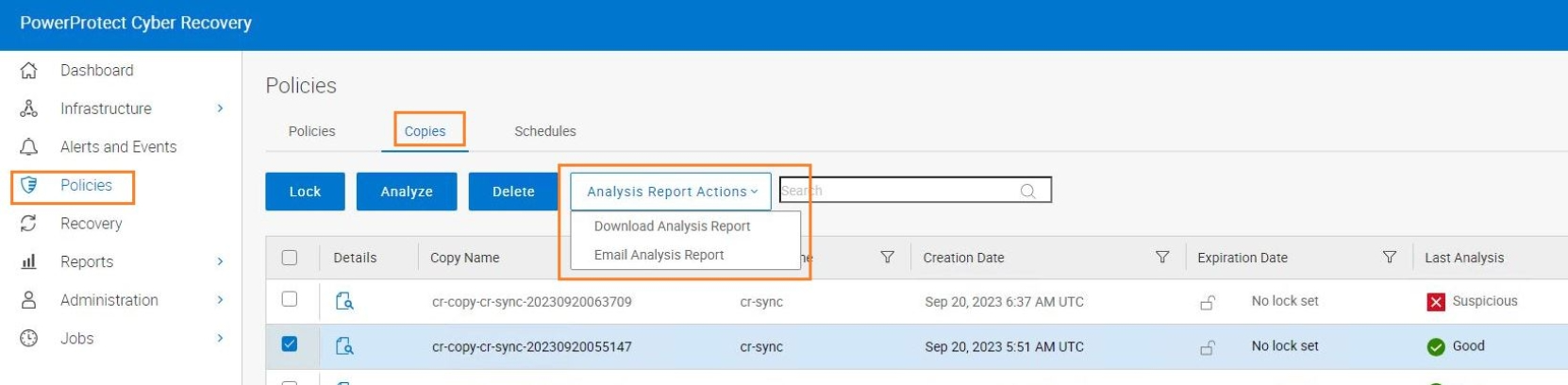
Figure 19. Analysis report download options
