Integrating Rancher Prime-managed Kubernetes cluster with PowerProtect Data Manager
Home > Workload Solutions > Container Platforms > SUSE Containers as a Service > White Papers > Rancher Prime and RKE2 Kubernetes Cluster in APEX Private Cloud with PowerProtect Data Manager > Integrating Rancher Prime-managed Kubernetes cluster with PowerProtect Data Manager
Integrating Rancher Prime-managed Kubernetes cluster with PowerProtect Data Manager
-
PowerProtect Data Manager is integrated with a Rancher Prime managed Kubernetes cluster for data protection in the following ways:
- By directly connecting to the RKE2 downstream single node with controlplane and etcd roles
- Through a load balancer, when there are multiple RKE2 nodes with controlplane and etcd roles in an RKE2 downstream cluster
The following diagram shows the Rancher Prime-managed RKE2 downstream cluster with three RKE2 nodes:
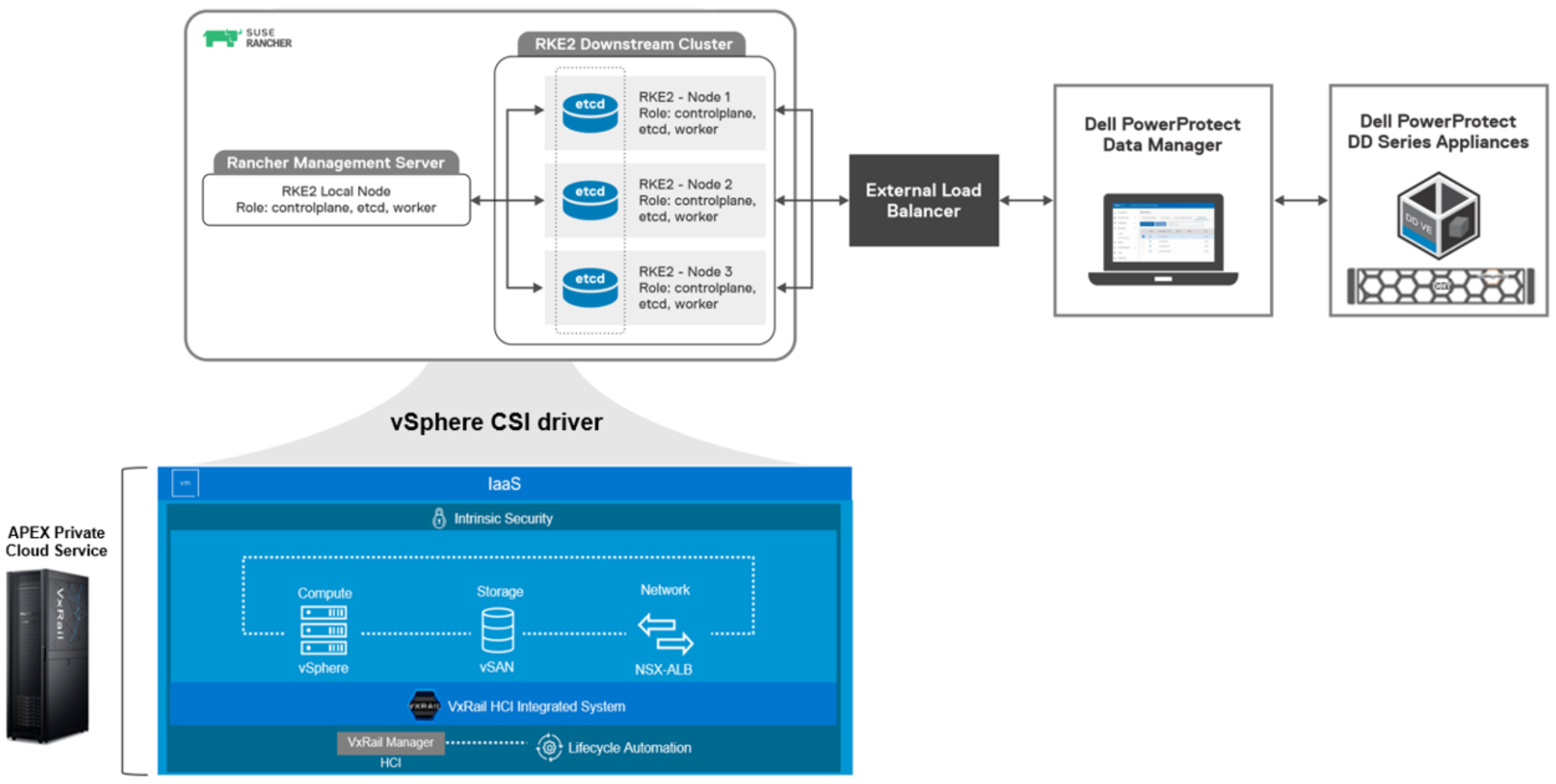
Figure 6. High-level integration overview of RKE2 downstream cluster with PowerProtect Data Manager
Note: Figure 6 is the high-level integration architecture for this white paper. Use Figure 5 as a best practice reference architecture.
Each RKE2 node holds all roles, such as controlplane, etcd, and worker, that are managed by the Rancher management server. APEX Cloud Private Service is equipped with the Dell VxRail HCI integrated system. On top of the infrastructure, PowerProtect Data Manager and DDVE appliances are deployed. A VMware vSphere datastore is used as the persistent storage for the Kubernetes cluster workloads that are integrated through the vSphere CSI driver. An external load balancer is configured as the front-end cluster endpoint for the RKE2 nodes. PowerProtect Data Manager accesses the RKE2 downstream cluster assets for data protection by using the load balancer Virtual IP.
RKE2 supports x509 authentication strategy. A list of SANs can also be defined to add to the Kubernetes API Server PKI certificates. The optional load balancer configuration is done when there are multiple RKE2 nodes available with controlplane and etcd in an RKE2 downstream cluster.
For example, you can connect to a Kubernetes cluster API server through a load balancer instead of a single RKE2 node.
Prerequisites
Before integrating the RKE2 downstream cluster with PowerProtect Data Manager, perform the following required configuration procedures.
Load balancer authentication
Add the load balancer details to the RKE2 downstream cluster:
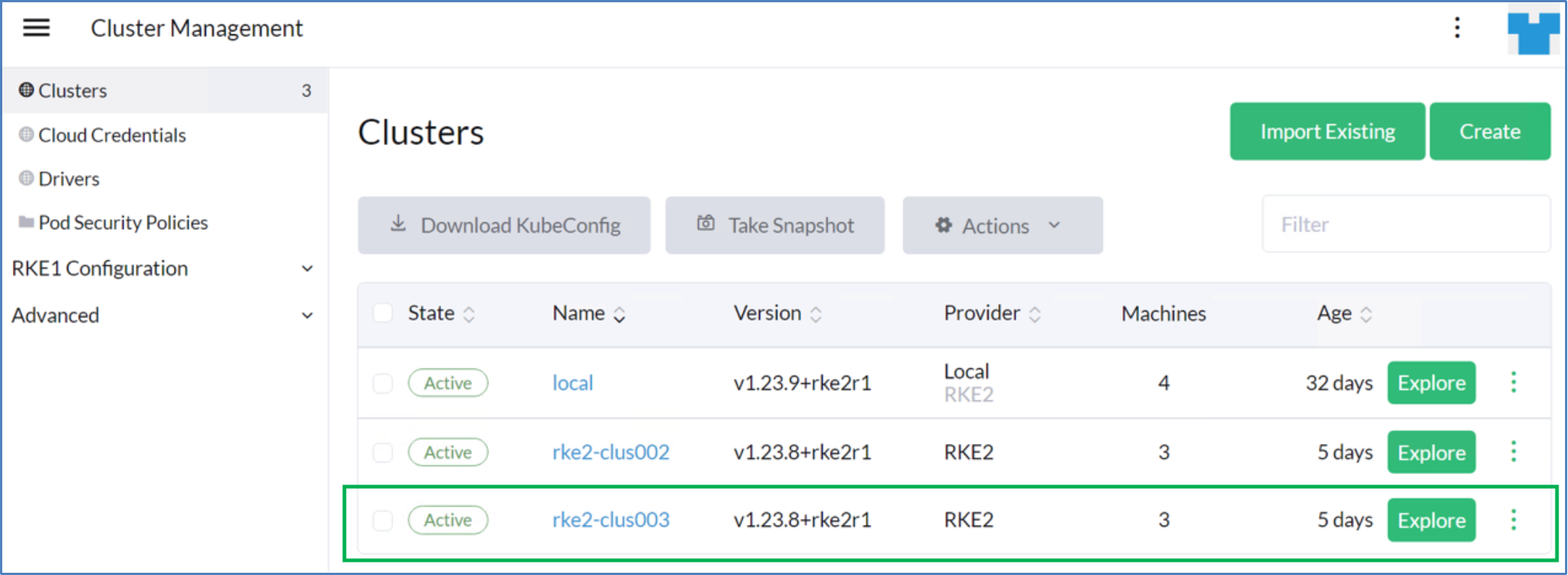
- From the Rancher management server UI, click the hamburger menu (
 ) and select Cluster Management.
) and select Cluster Management.

- Select the custom RKE2 cluster and click Explore.
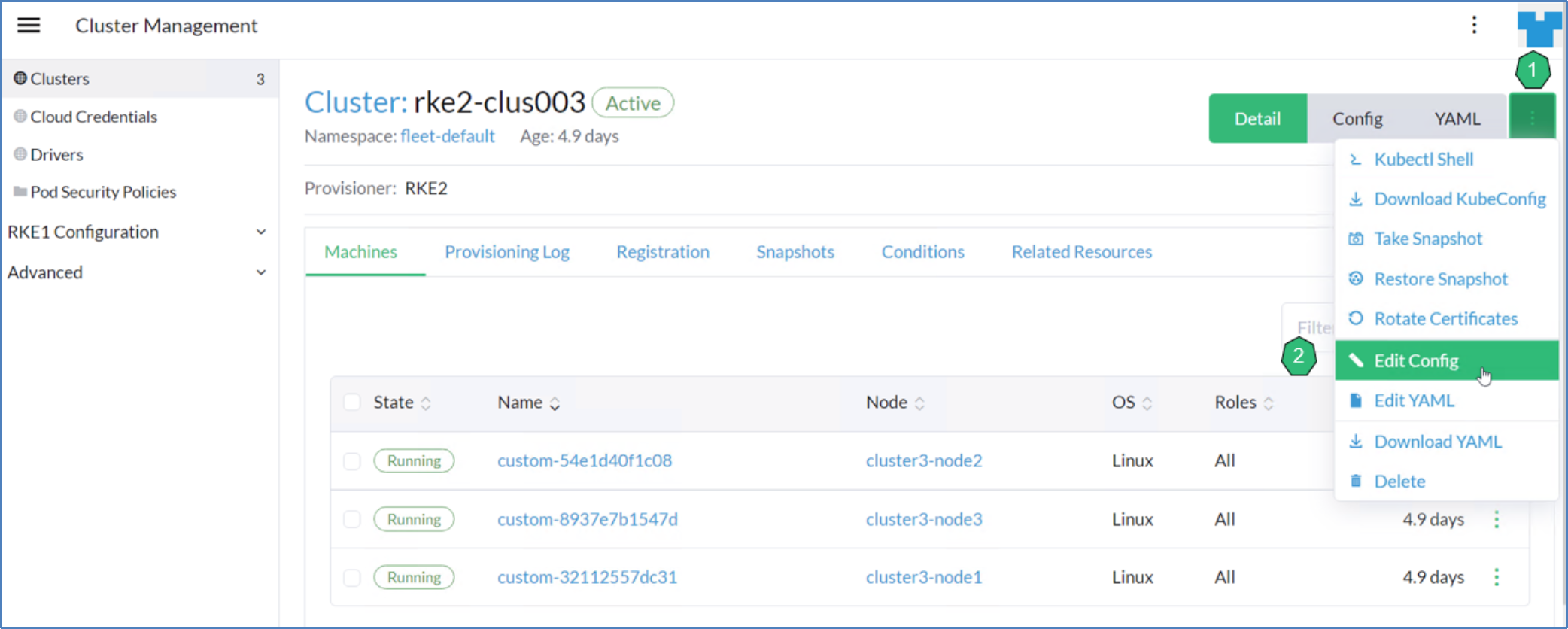
- From the custom cluster dashboard, select the kebab menu (
 ) and select Edit Config.
) and select Edit Config.
- Select Networking, click Add under TLS Alternate Names, and enter the load balancer IP or FQDN.
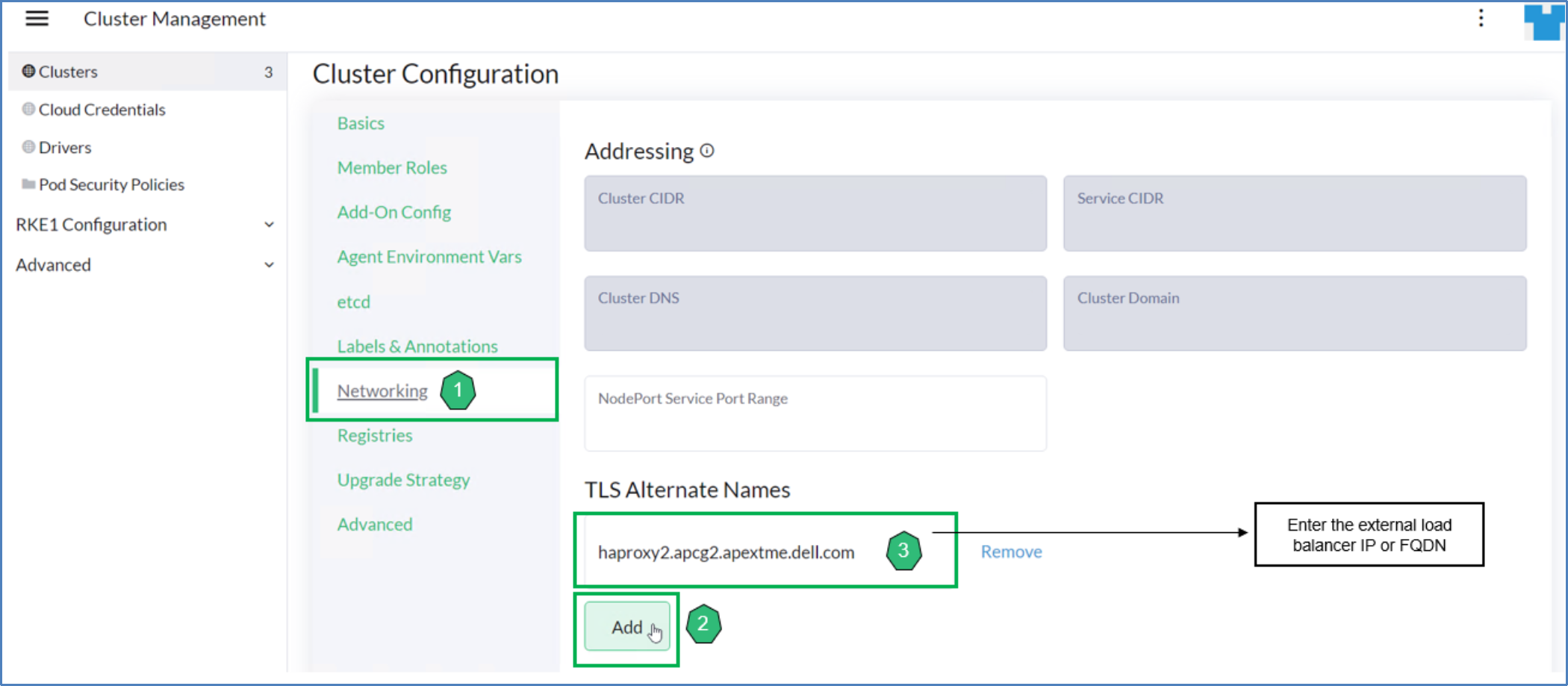
- Click Save to save the configuration file.
The cluster takes a few minutes to update the configuration.
The following figure shows that the sample YAML cluster configuration file after the load balancer IP address has been added in the tls-san section.

Service account token for the Rancher Kubernetes cluster
The service account must have the following privileges:
- Get, Create, Update, and List for CustomResourceDefinitions
- Get, Create, and Update ClusterRoleBinding for the cluster-admin role
- Create and Update for the PowerProtect namespace
- Get, List, Create, Update, Delete, and List
- Get, List, Create, Update, and Delete for all resources inside the PowerProtect namespace
- Get, List, and Watch for all the namespaces in the cluster and PV, PVC, storageclass, deployments, and pods in all the namespaces
Note: The admin-user service account in the kube-system namespace contains all the privileges. You can use the token of this account or an existing similar service account. Alternatively, you can create a service account that is bound to a cluster role that contains these privileges and provide the token of this service account. For more information, see the PowerProtect Data Manager Kubernetes User Guide.
- Run the following commands to create a service account for registering the Kubernetes cluster with PowerProtect Data Manager:
kubectl create serviceaccount admin1 -n kube-system
kubectl create clusterrolebinding admin1-admin -n kube-system --clusterrole=cluster-admin --serviceaccount=default:admin1
- Run the following command to obtain the service account token:
kubectl get secret $(kubectl get serviceaccount admin1 -o jsonpath="{.secrets[0].name}") -o jsonpath="{.data.token}" | base64 –decode
Enable the asset source
Use the PowerProtect Data Manager UI to enable the Kubernetes asset source before adding and registering the asset source for the protection of assets.
Enable the asset source as follows:
- From the PowerProtect Data Manager UI, go to Infrastructure > Asset Sources, and click the + icon to display the New Asset Source tab.
- In the New Asset Source window, click Enable Source in the Kubernetes section.
Adding RKE2 downstream cluster with PowerProtect Data Manger as an asset source
To protect the Kubernetes environment with PowerProtect Data Manager, add an RKE2 downstream cluster that is managed by the Rancher Prime as an asset source. Namespaces are then automatically discovered as assets for data protection operations.
Specify the Kubernetes cluster attributes as follows:
- Name: Kubernetes cluster name to be displayed in asset sources list
- Address: FQDN or IP address of the Kubernetes API server or load balancer
- Port: Port to use for communication when the default port, 443, is not used
Note: The use of any port other than 443 or 6443 requires opening the port on PowerProtect Data Manager.
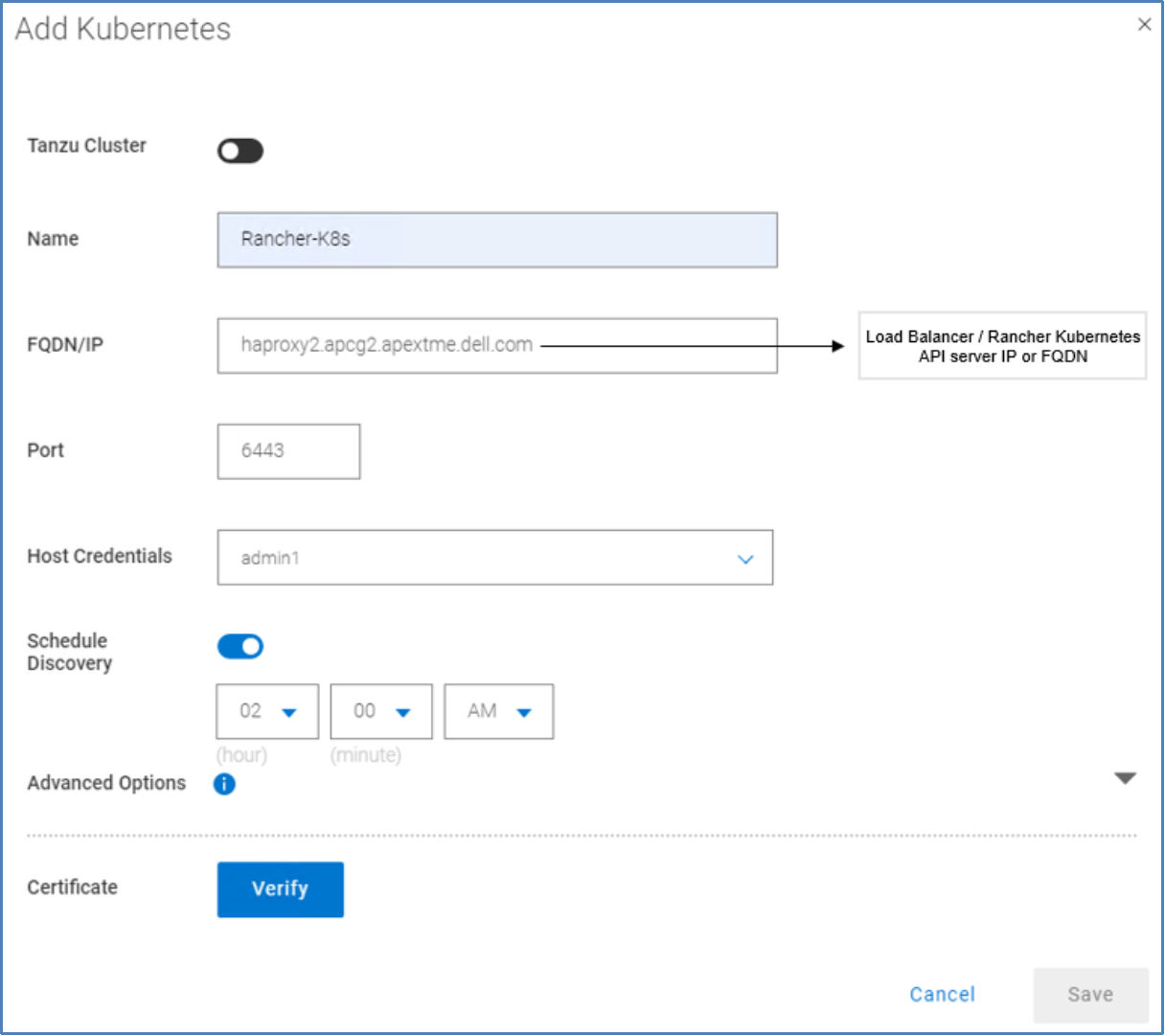
Figure 7. Kubernetes cluster attributes
When you add an RKE2 downstream cluster, the cluster information appears in the table, and automatic discovery of the namespace assets is initiated.
When the discovery is successful, the namespace assets appear as assets in the Kubernetes tab in the Assets window.
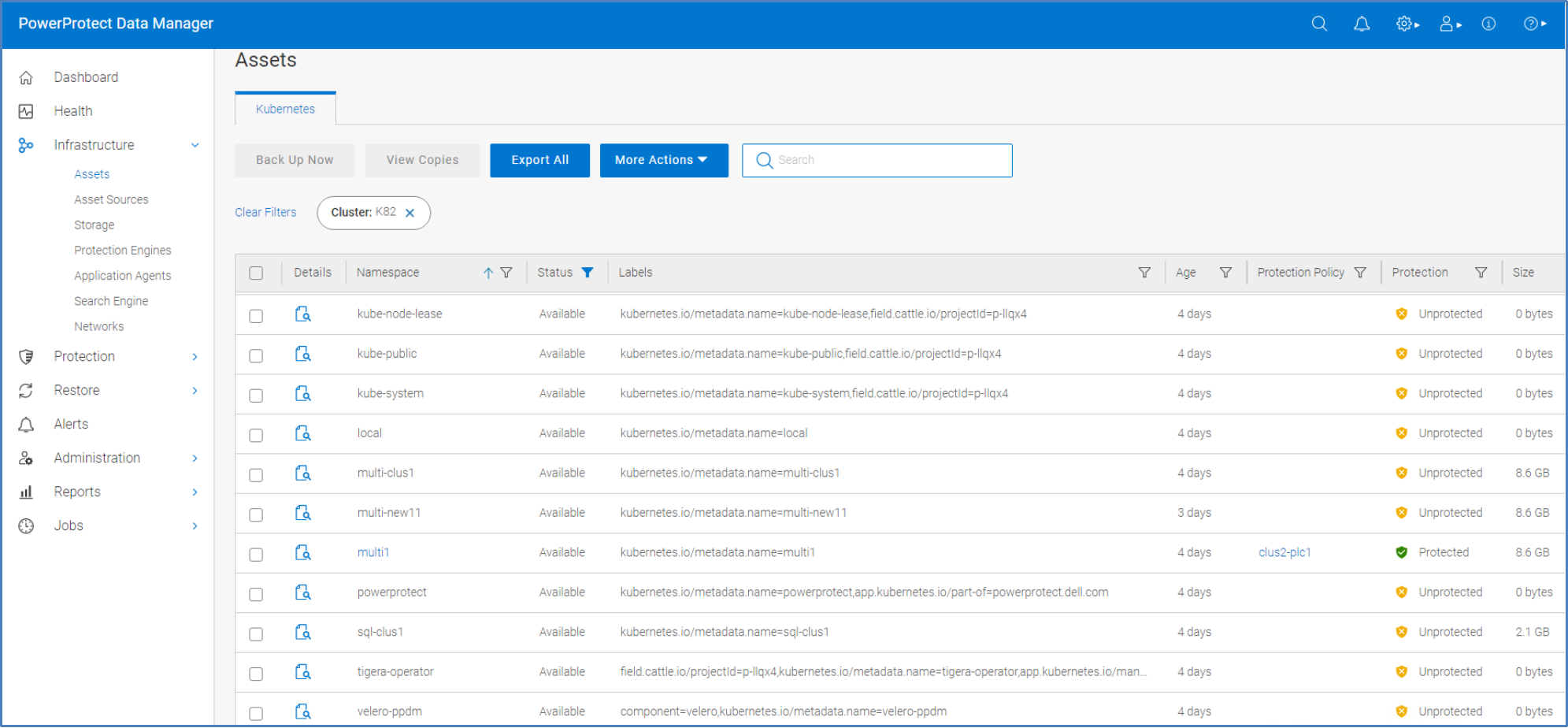
Figure 8. Kubernetes assets window
Creating a protection policy for namespaces and PVCs on the Rancher Kubernetes cluster
Protection policies define sets of objectives that apply to specific time periods. These objectives drive configuration, active protection, and copy-data-management operations that satisfy the business requirements for the specified data. Each plan type has its own set of user objectives. Users with the system admin role can create protection policies.
PowerProtect Data Manager provides the following options when you create a Kubernetes cluster protection policy:
- Crash Consistent: Select this option for point-in-time backup of namespaces.
- Exclusion: Select this option if there are assets within the protection policy to be excluded from data protection operations.
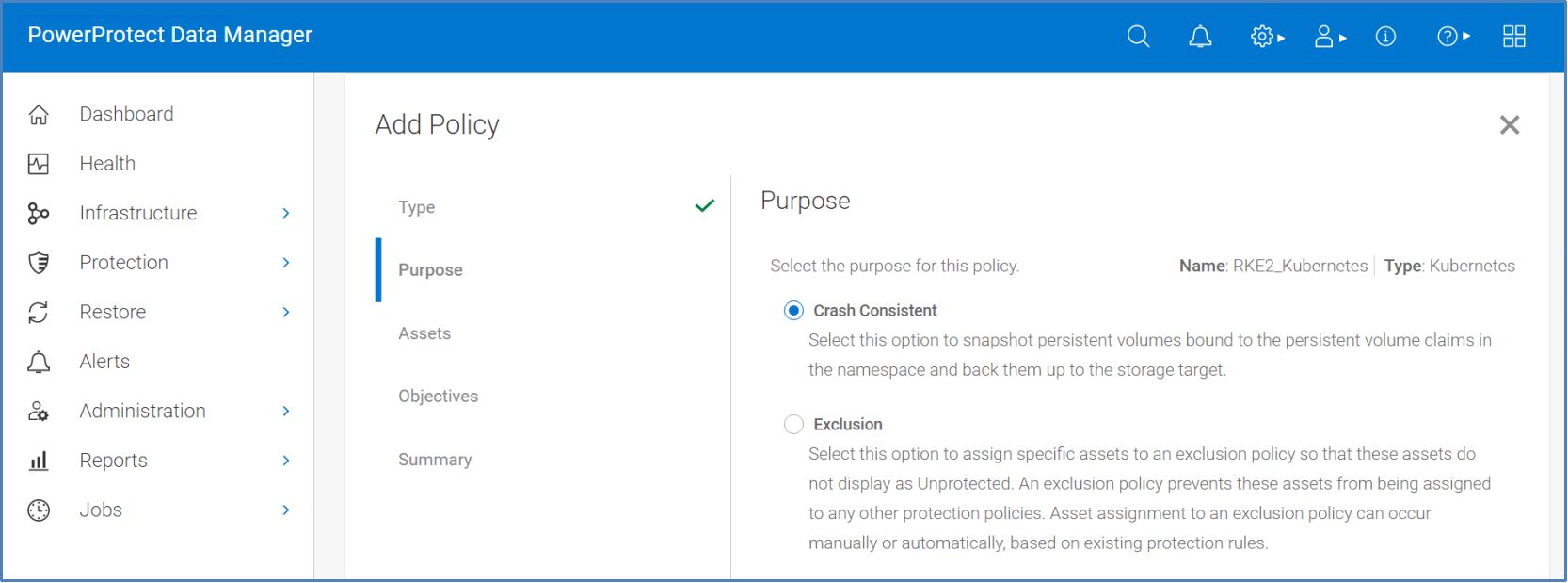
Figure 9. PowerProtect Data Manager policy configuration window—Specifying policy purpose
You can also select namespaces and associated PVCs statically or dynamically for inclusion or exclusion in protection policies, along with schedules, retention, and other protection operations.
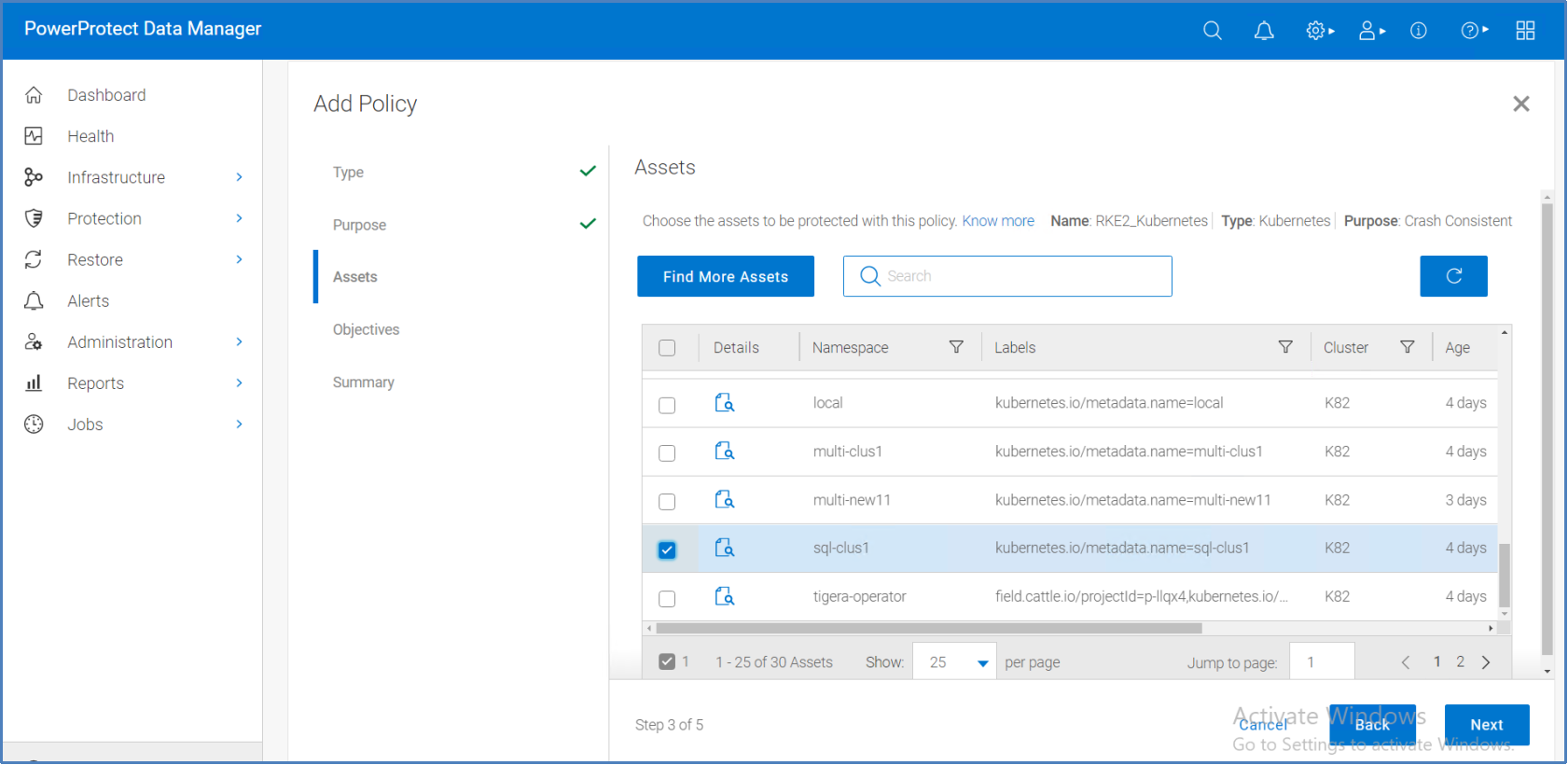
Figure 10. PowerProtect Data Manager policy configuration window—Specifying assets to be protected
For more information about creating a protection policy for Kubernetes namespace protection, see the PowerProtect Data Manager Kubernetes User Guide.
Performing backup of namespaces and PVCs on a Rancher Kubernetes cluster
Apart from the scheduled backup option, PowerProtect Data Manager supports the option to perform manual backups.
For example, a sample mysql application is deployed on the Rancher Kubernetes cluster with the namespace sql-clus1. The namespace is composed of a MySQL pod, as shown in the following figure:
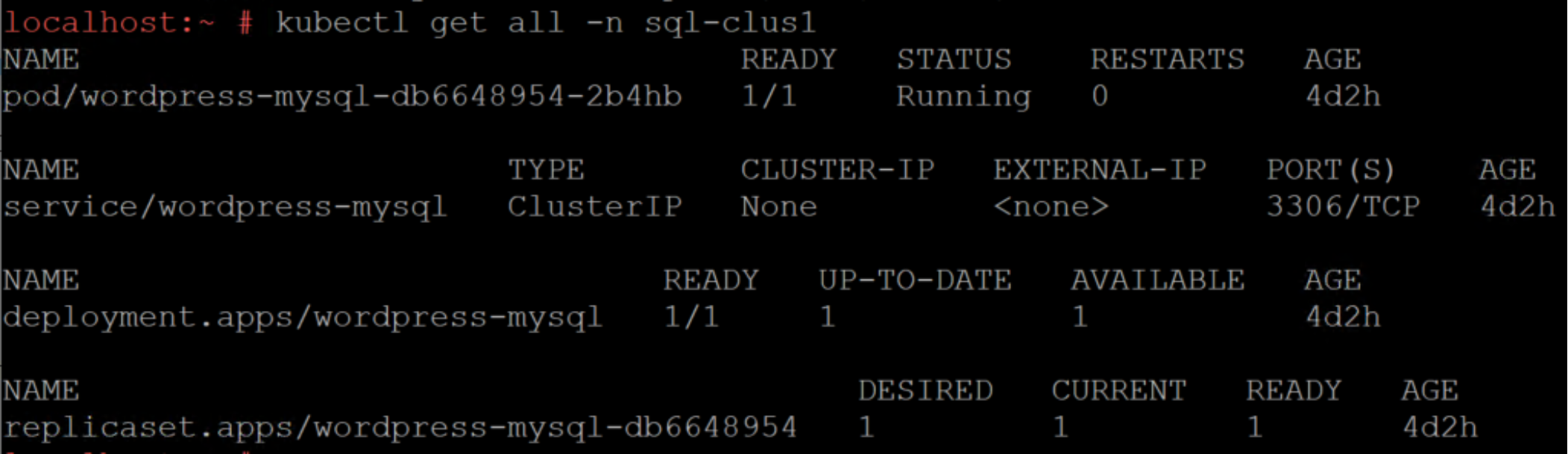
Figure 11. MySQL application pod in sql-clus1 namespace
The following Rancher UI shows that the MySQL application pod is in the namespace sql-clus1:
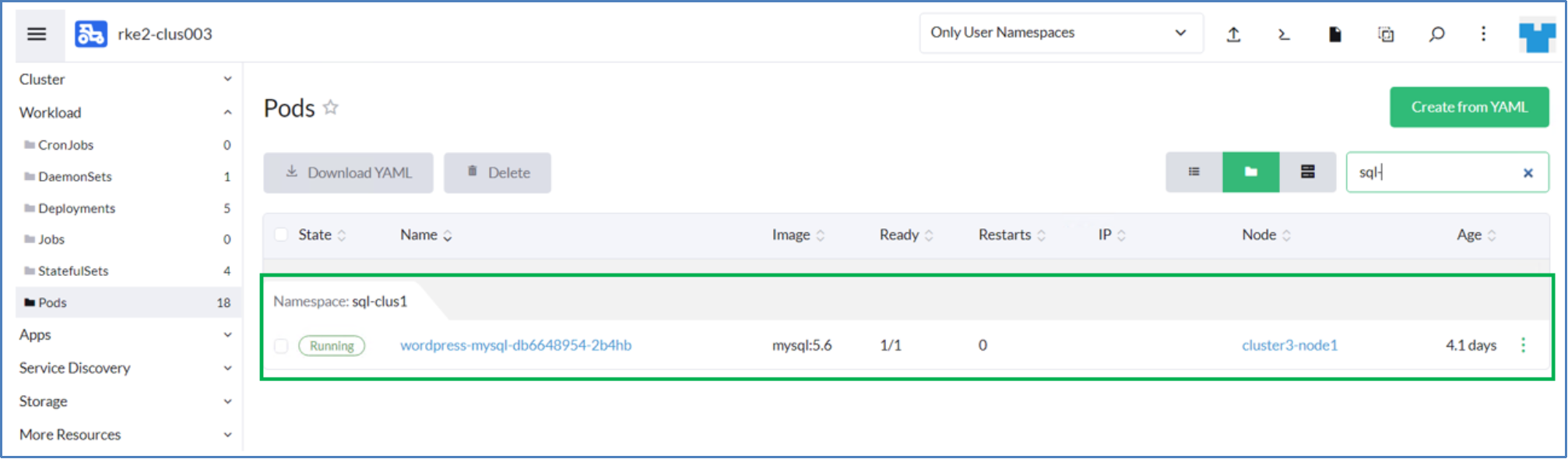
Figure 12. MySQL application pod in sql-clus1 namespace from Rancher UI
A sample database students_details and a respective table has been created on the MySQL application pod belonging to namespace sql-clus1, as shown in the following figure:
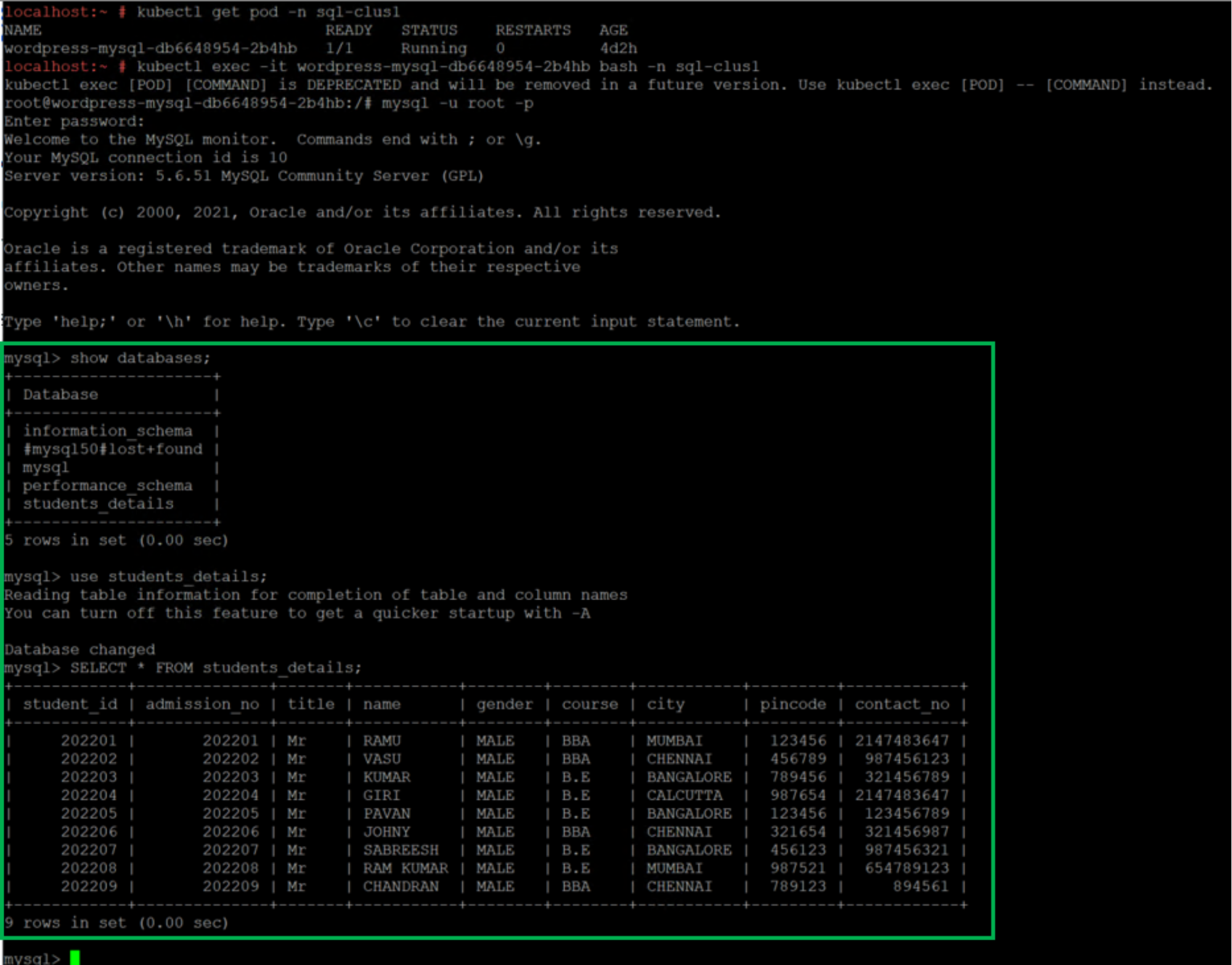
Figure 13. Sample database and table created on the MySQL application pod belongs to namespace sql-clus1
We will now back up the namespace sql-clus1 and the respective PVCs with PowerProtect Data Manager.
The following figure shows the protection job that is completed successfully for the sql-clus1 namespace:
Figure 14. PowerProtect Data Manager protection job summary
The following figure shows the protection copy available for the namespace sql-clus1:
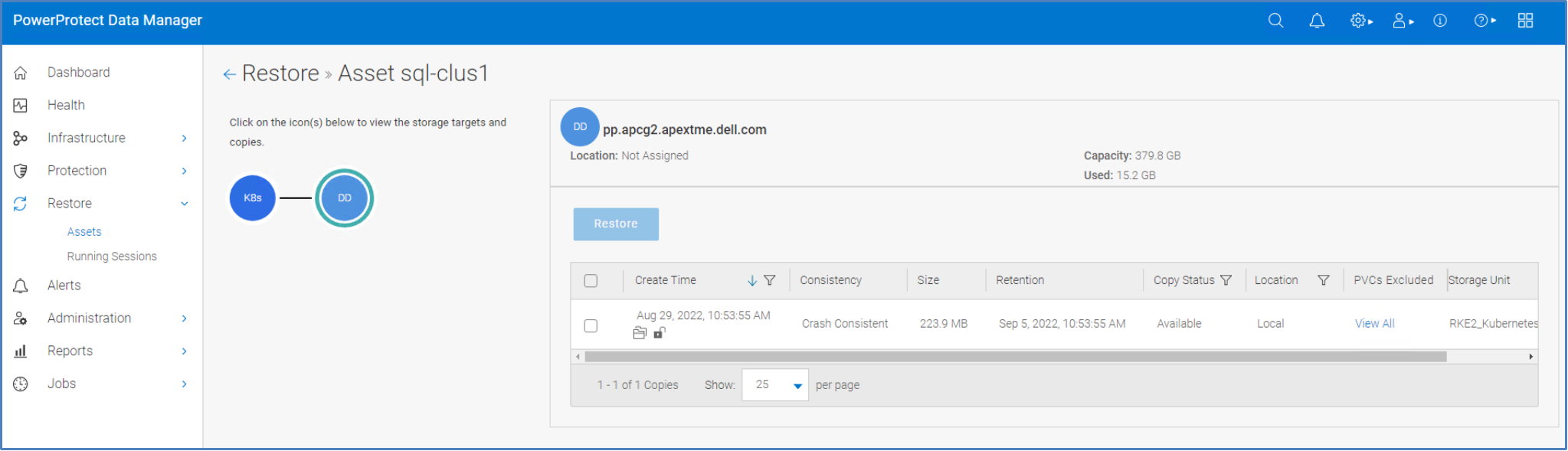
Figure 15. PowerProtect Data Manager asset window displaying the available protection copy
For more information about backing up and recovering Kubernetes workloads using PowerProtect Data Manager, see the PowerProtect Data Manager Kubernetes User Guide.
Restoring the namespaces and PVCs to a Rancher Kubernetes cluster
After assets are protected under the Kubernetes cluster protection policy, a restore of namespace and PVCs can be done from individual namespace backups.
Use the following recovery options:
- Restore to original namespace: Restore to the original namespace on the original cluster.
- Restore to new namespace: Create a namespace and restore to this location on the original cluster or a different cluster.
- Restore to existing namespace: Restore to an existing namespace in the original cluster or a different cluster.
In the following sample restore, the PVCs that are backed up within the namespace sql-clus1 are restored to the new namespace sql-clus1-restore:

Figure 16. Restore Type window
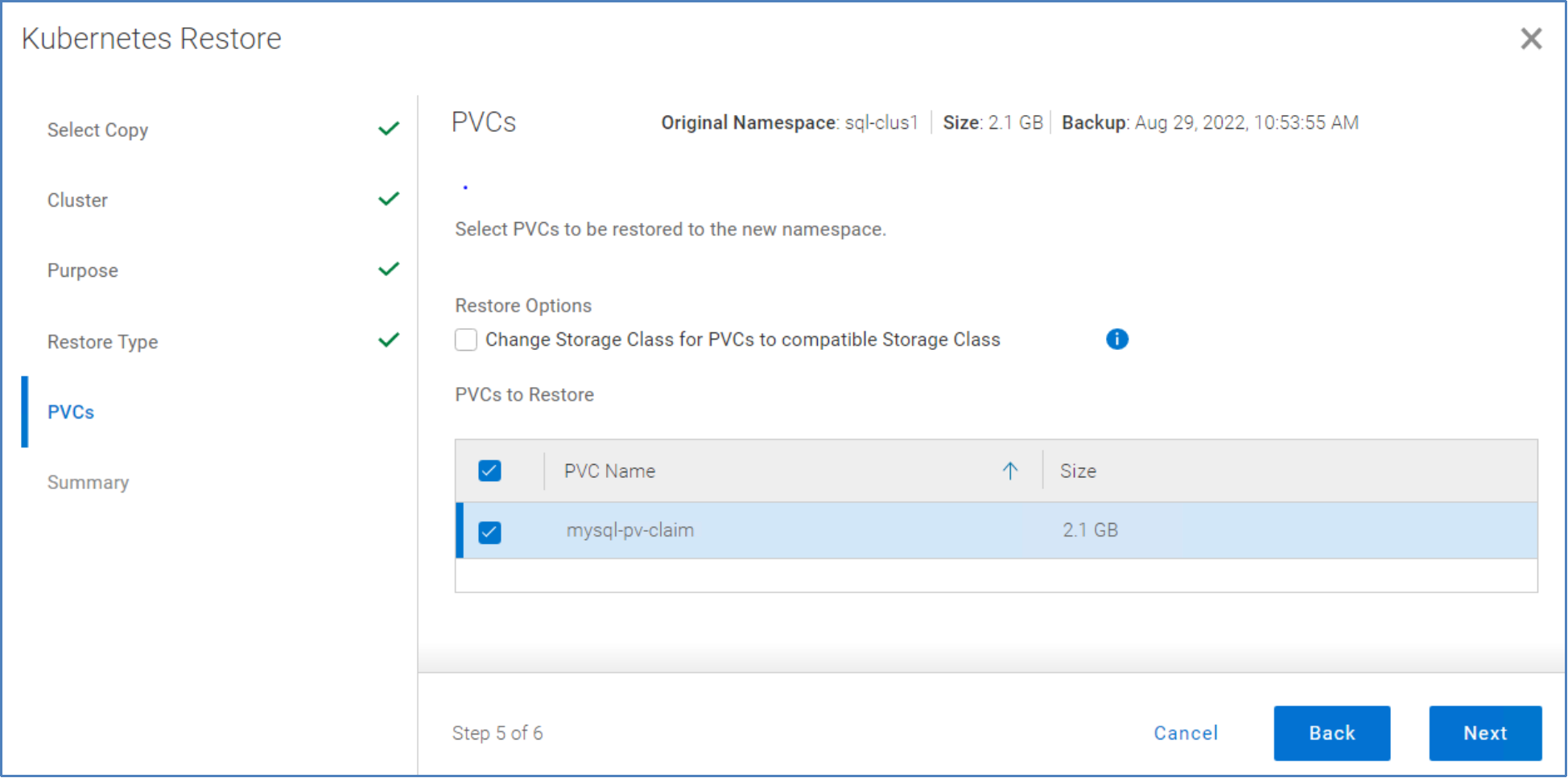
Figure 17. Selecting PVCs for restore
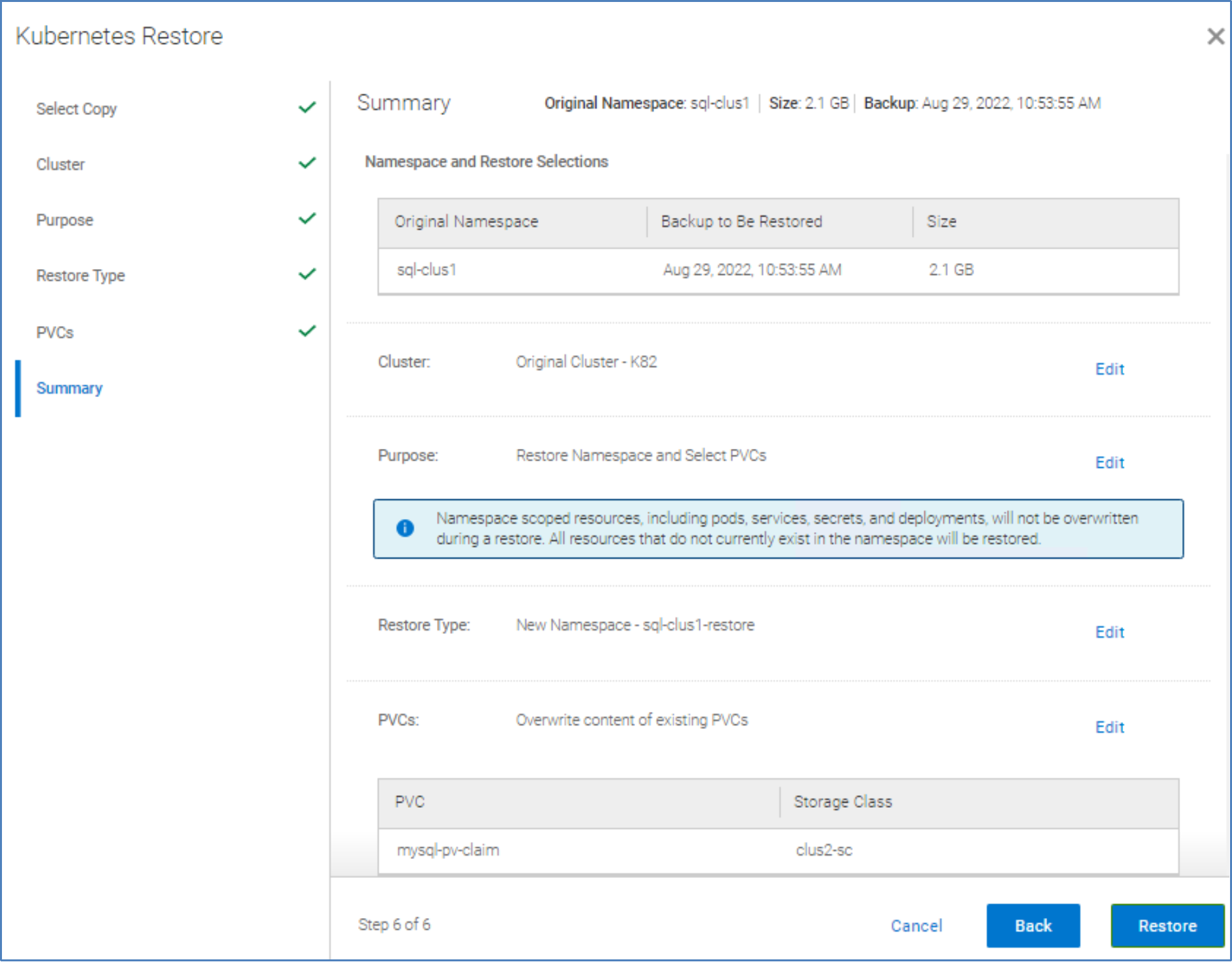
Figure 18. Restore summary
The following image shows that the restore job was completed successfully.

Figure 19. PowerProtect Data Manager restore job summary
The following figure shows that the new namespace sql-clus1-restore was created successfully on the RKE2 downstream cluster during the restore.
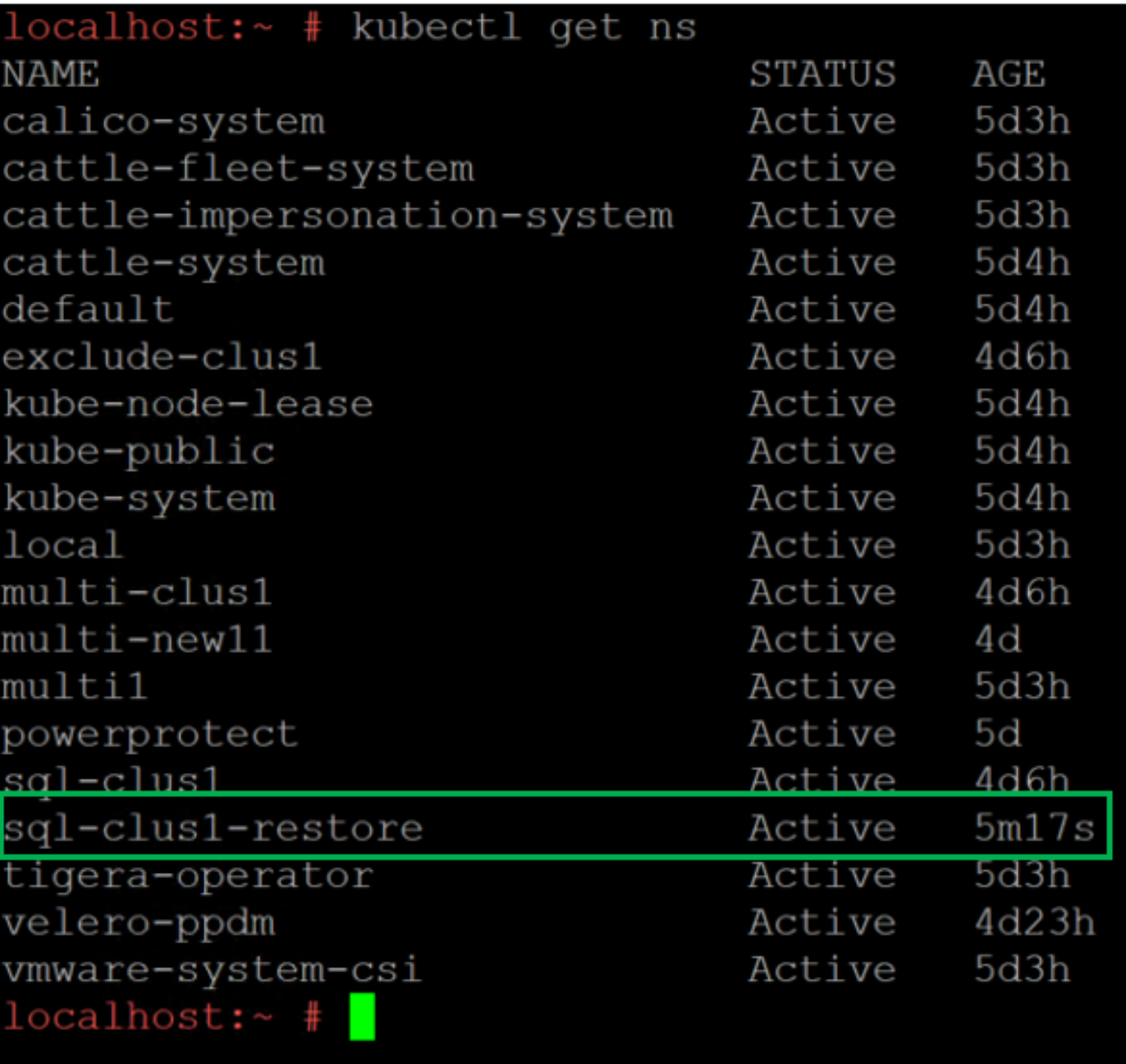
Figure 20. New namespace sql-clus1-restore created on cluster
The following figure shows that the MySQL application pod has been successfully restored to the new namespace sql-clus1-restore.
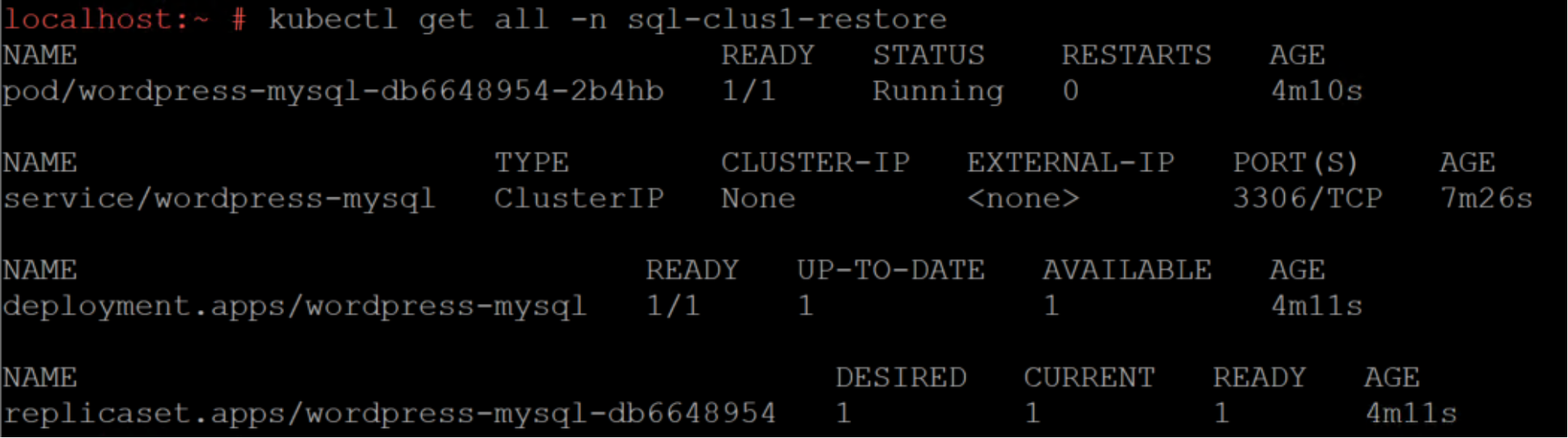
Figure 21. Restored namespace sql-clus1-restore details
The restored MySQL application in the namespace sql-clus1-restore is displayed in the Rancher management UI:
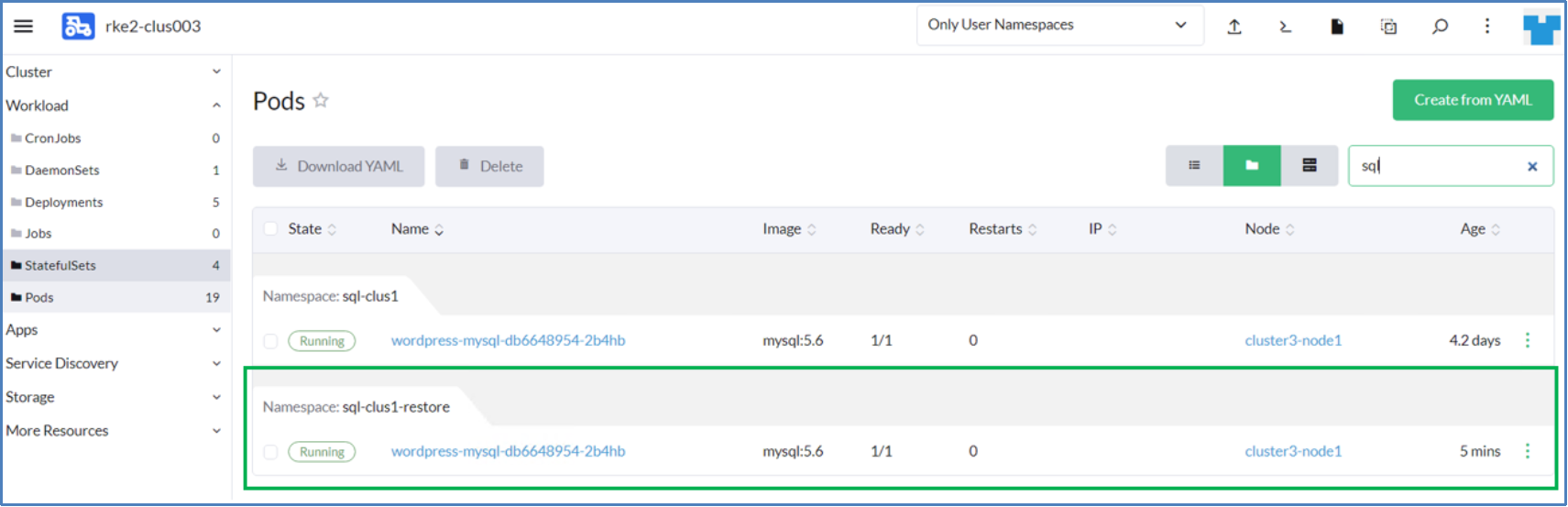
Figure 22. MySQL application pods in mysql-clus2-restore namespace from Rancher UI
The database students_details and its respective table that was created on the MySQL application pod belonging to namespace sql-clus1 are now available with the restored namespace sql-clus1-restore.
The following figure shows confirmation of the successful backup and recovery of namespaces and PVCs that are available in the RKE2 downstream cluster using PowerProtect Data Manager.
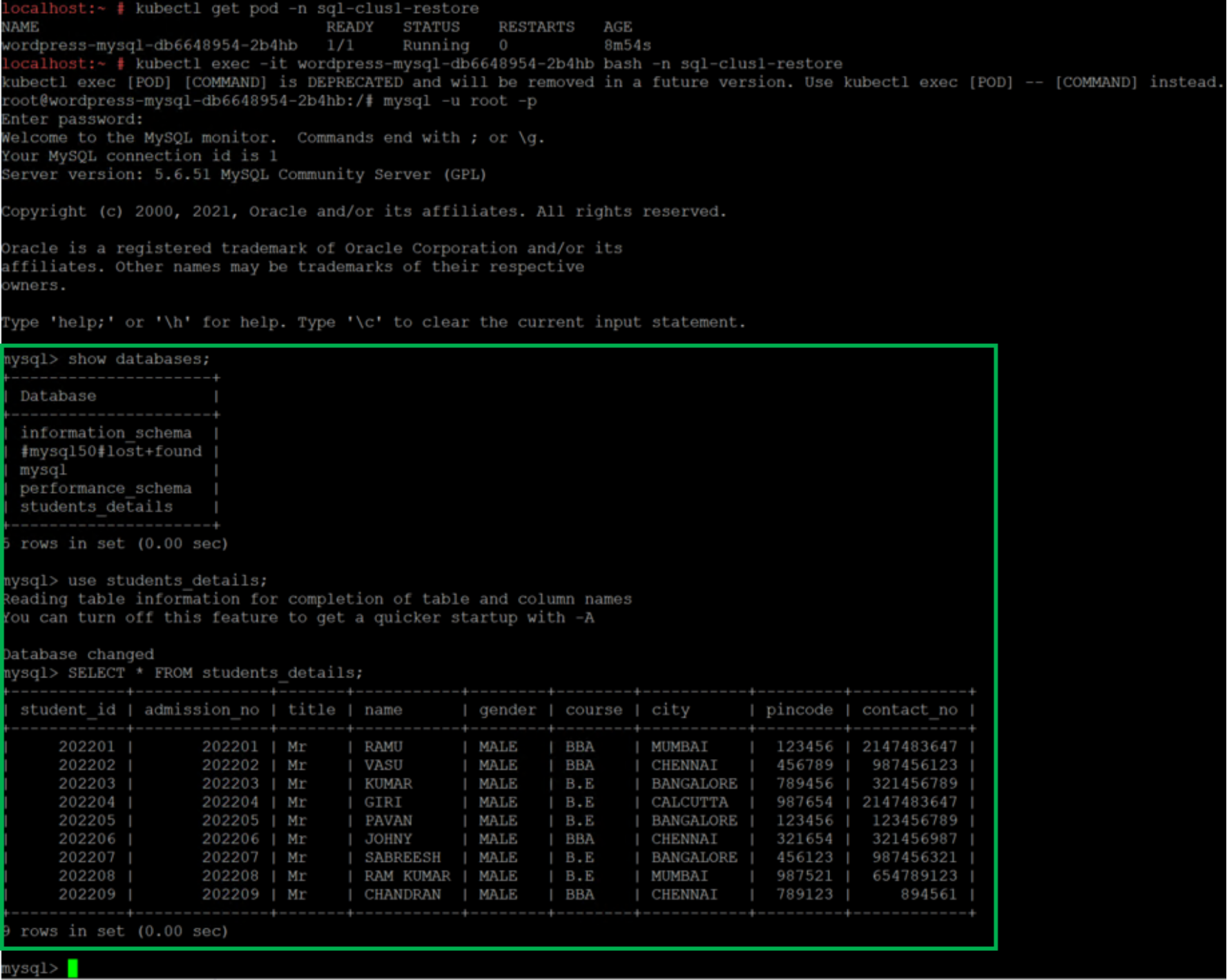
Figure 23. WordPress post available on the restored namespace
For more information about backing up and recovering Kubernetes workloads using PowerProtect Data Manager, see the PowerProtect Data Manager Kubernetes User Guide.
