Home > Storage > PowerScale (Isilon) > Product Documentation > Management and Migration > PowerScale OneFS User Mapping: Mapping Identities Across Authentication Providers > Fields and options
Fields and options
-
Rules can include options that target the fields of an access token. A field represents a section of an access token, such as the primary UID and primary user SID from a user that you select. When you create a rule, you can add an option to manipulate how OneFS combines sections of two identities into a single token. For example, an option can force OneFS to append only the supplement groups to a token.
A token includes the following fields that you can manipulate with user mapping rules:
- username
- unix_name
- primary_uid
- primary_user_sid
- primary_gid
- primary_group_sid
- additional_ids (includes supplemental groups)
The options for appending a field from a user are illustrated in the following figure:
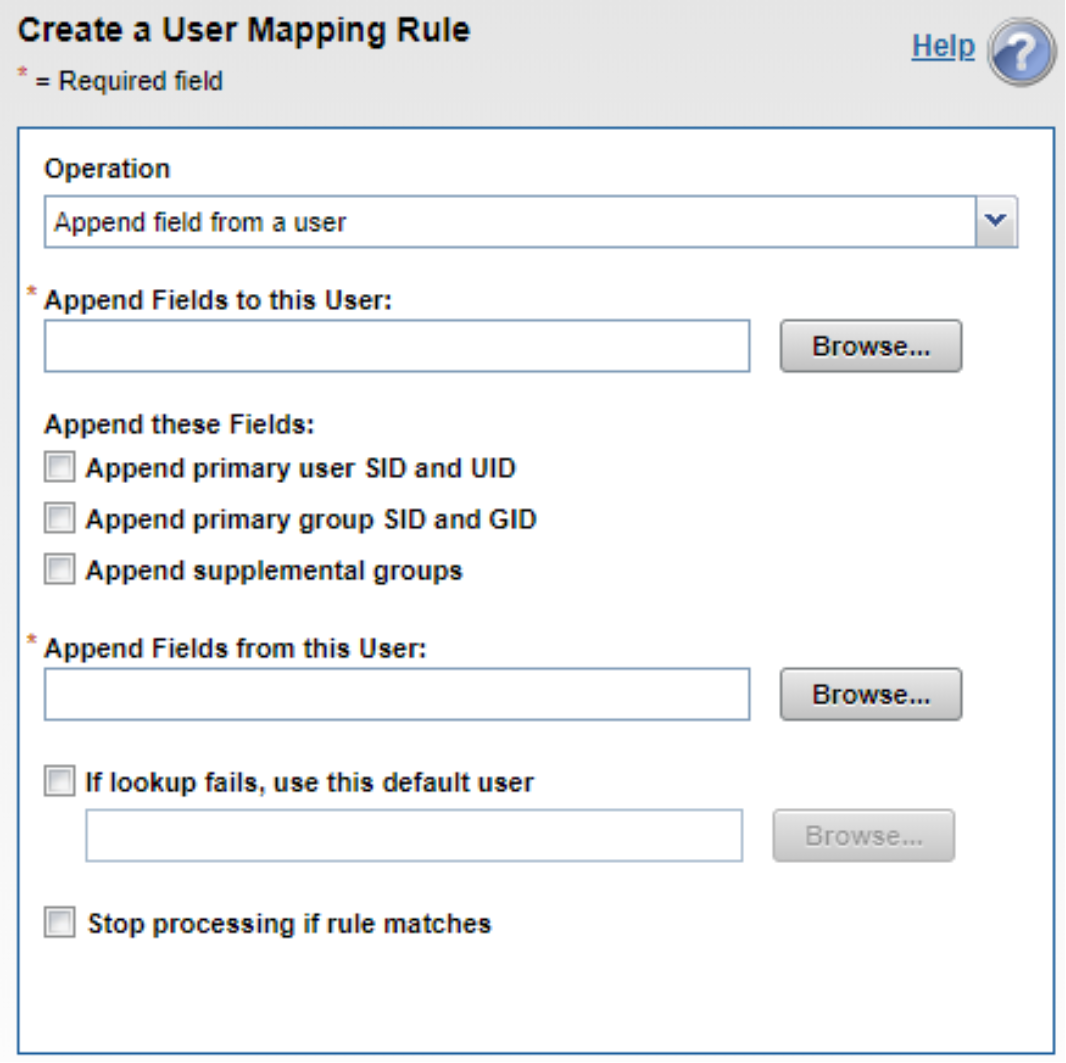
Figure 2. Append field from a user
You can also see the fields in an OneFS access token:
isi auth mapping token --user york\\stand
User
Name: YORK\stand
UID: 100000
SID: S-1-5-21-1195855716-1269722693-1240286574-591111
On Disk: S-1-5-21-1195855716-1269722693-1240286574-591111
ZID: 1
Zone: System
Privileges: -
Primary Group
Name: YORK\york_sh_udg
GID: 1000000
SID: S-1-5-21-1195855716-1269722693-1240286574-66133
Supplemental Identities
Name: YORK\sd-york space group
GID: 1000002
SID: S-1-5-21-1195855716-1269722693-1240286574-579109
The primary username
The primary UID
The primary user SID
The primary GID
The primary group SID
The additional IDs are the supplemental groups that appear under the Supplemental Identities heading
The primary UID and the primary user SID always correspond to the same user; they can, however, differ from the user listed in the username field, as later examples will show. The primary GID and primary group SID always correspond to the same group.
Options
The options control how a rule combines identity information in a token. The break option is the exception: it stops OneFS from processing additional rules.
Although several options can apply to a rule, not all options apply to all operators. The following table describes the effect of each option and the operators that they work with.
Table 2. Mapping rule options
Option
Description
User
The user option works with the insert and append operators. It copies the primary UID and primary user SID to the token.
Group
The group option works with the insert and append operators. It copies the primary GID and primary group SID to the token.
Groups
The groups option works with the insert and append operators. It copies all the additional identifiers to the token. (The additional identifiers exclude the primary UID, the primary GID, the primary user SID, and the primary group SID.)
Default_user
The default user option works with all the operators except remove groups. If the mapping service fails to find the second user in a rule, the service tries to find the username of the default user. The name of the default user cannot include wildcards. When you set the option for the default user in a rule with the command-line interface, you must set it with an underscore: default_user
Break
The break option works with all the operators. The break option stops the mapping service from applying rules that follow the insertion point of the break option. The mapping service generates the final token at the point of the break.
Default UNIX user parameters if UIDs and GIDs are not available
A global option that applies to all user mapping is available for setting the default UNIX user parameters if UIDs and GIDs are not available. This option specifies how default UNIX user parameters are generated if UIDs or GIDs are not available, as illustrated in the following figure:
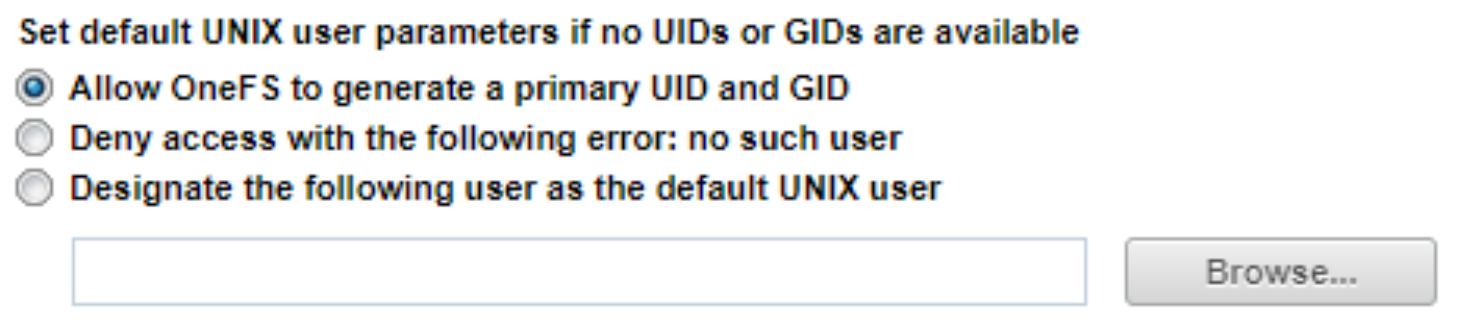
Figure 3. Default UNIX user parameters

Figure 4. Default user option
To summarize, the default UNIX user parameter specifies an option if UIDs and GIDs are not available after OneFS applies all the rules in the zone. The option for the default user selects a user to include in a token when the lookup of a username in a rule fails.
Append operator example
Here is an example of how a rule with the append operator and the user option affects a token. The user option appends the primary UID and primary user SID to the token.
Consider the following access token for a user from Active Directory named user_9449:
isi auth mapping token YORK\\user_9449
User
Name: YORK\user_9449
UID: 1000000
SID: S-1-5-21-1195855716-1269722693-1240286574-11556
ZID: 1
Zone: System
Privileges: -
Primary Group
Name: YORK\domain users
GID: 1000000
SID: S-1-5-21-1195855716-1269722693-1240286574-513
Supplemental Identities
Name: Users
GID: 1545
SID: S-1-5-32-545The following rule contains the append operator with the user option to append the LDAP user’s primary UID and the primary SID to the token of the Active Directory user:
isi zone zones modify System --user-mapping-rules="YORK\\user_9449 ++ lduser_010 [user]"
After setting the rule, you can view it with the following command. The output is abridged to focus on the rule:
isi zone zones view System
Name: System
...
User Mapping Rules: YORK\user_9449 ++ lduser_010 [user]
The rule produces the following access token. The user option adds the LDAP user’s primary UID and primary GID, highlighted in bold, to the Supplemental Identities section of the token:
isi auth mapping token YORK\\user_9449
User
Name: YORK\user_9449
UID: 1000000
SID: S-1-5-21-1195855716-1269722693-1240286574-11556
ZID: 1
Zone: System
Privileges: -
Primary Group
Name: YORK\domain users
GID: 1000000
SID: S-1-5-21-1195855716-1269722693-1240286574-513
Supplemental Identities
Name: Users
GID: 1545
SID: S-1-5-32-545
Name: lduser_010
UID: 10010
SID: S-1-22-1-10010
